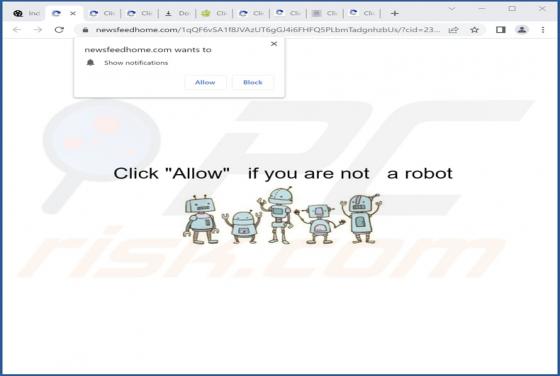
Newsfeedhome.com Ads
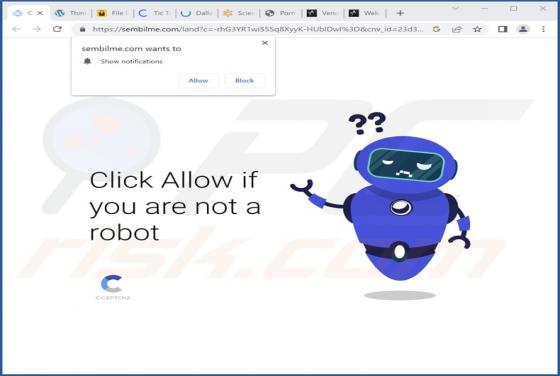
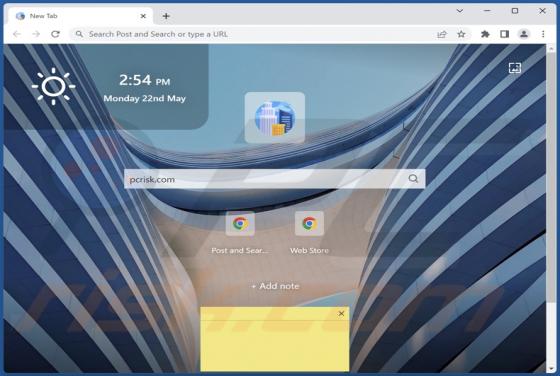
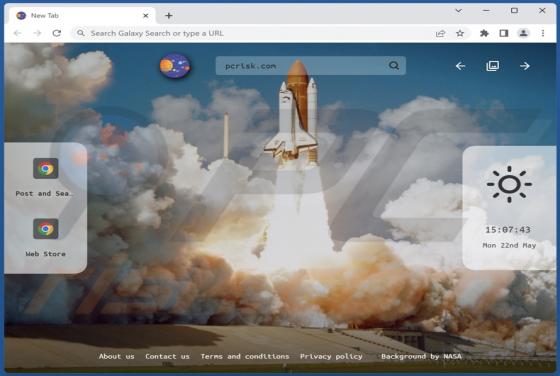
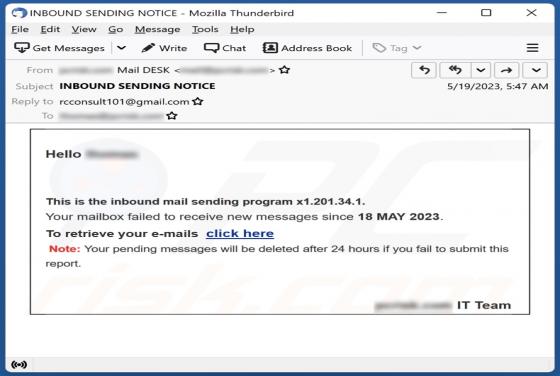
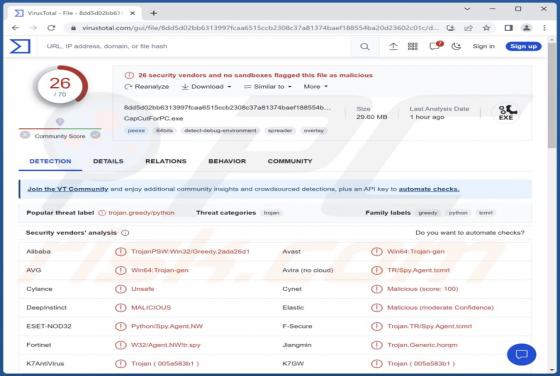
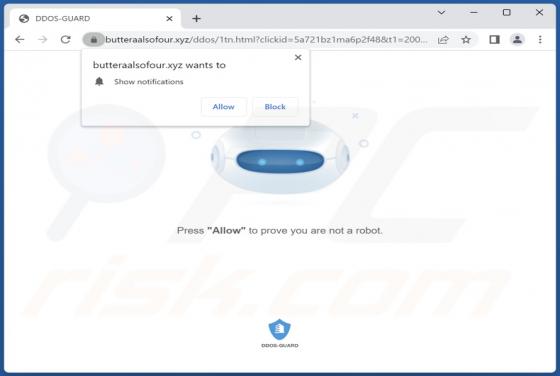
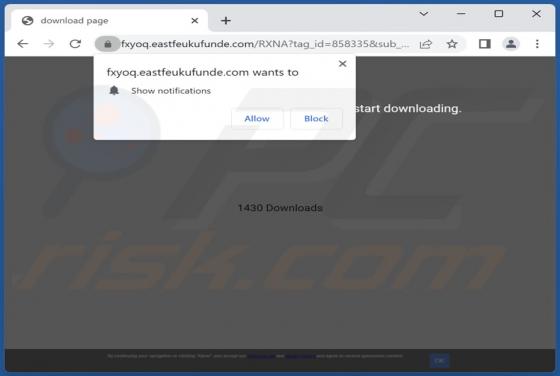
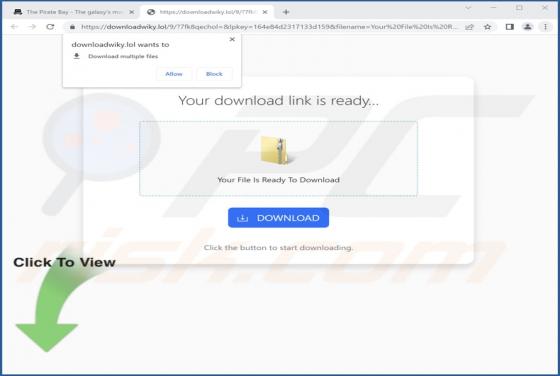
After analyzing newsfeedhome[.]com, our team discovered that the website employs a deceptive tactic by displaying a misleading message to manipulate visitors into granting permission for notifications. Additionally, newsfeedhome[.]com redirects users to other websites that employ clickbait techniq