EssentialModule Adware (Mac)
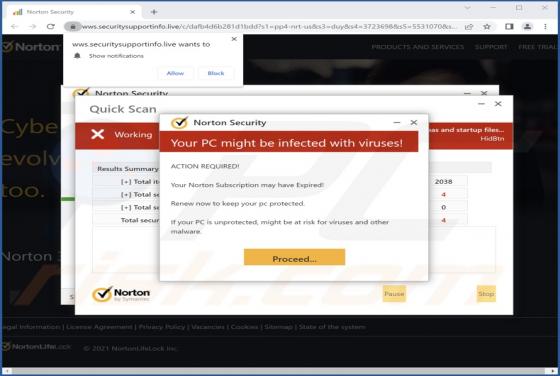
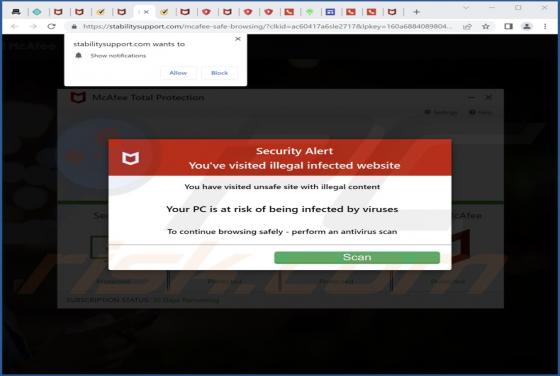
While surfing deceptive pages, we discovered an application called EssentialModule. Our team tested this app and found that it displays annoying advertisements. Thus, we classified EssentialModule as adware. It is worth mentioning that users do not normally download and install adware knowingly.