Stolen Healthcare Data For Sale on the Deep Web
The Deep Web is that part of the internet where hackers sell exploit kits and stolen data. Such sites are often hard to find. Many require an invitation from someone else to join. Some, like AlphaBay, hide behind the Tor network.
TrendLabs Security reports that data stolen from US hospitals is showing up on markets there. Prices range from $1 for a patient profile to $500,000 for a complete database.
This data has value on several fronts. This data has lasting value because it includes Social Security numbers, which, unlike credit card numbers, is something that people cannot change. It is also harder to obtain since retailer databases do not store those. Thieves can sometimes use prescription information to obtain controlled substances dispensed using the mails. But more valuable is the personally identifiable information (PII) which can be used for identity theft. This includes making fake tax returns and then applying for a refund from the government under that person’s name. They can also make fake claims to an insurance company for reimbursement. And they can create identities for criminals on the run, terrorists, or whoever by using the data of people who are deceased. That is called a farmed identity and sells for about $1,000.
In can take the victim a long time and very much trouble to remove the blemishes on their record such fraud leaves behind.
TrendLabs says that the medical industry is the 3rd most attacked industry. Numbers 1 and 2 are government and retail.
There is no one overriding insurance system in the USA. The positive side to that is there is no one system that hackers could attack to get all medical records on all Americans. (There are some private efforts to provide a place for medical records, like Microsoft’s HeathVault.)
Medical Insurance is handled by hundreds of companies in the USA, each of which have their own system. Plus hospitals and labs use in-house and cloud software. Some of that has been attacked. For example, 300,000 medical records were stolen from PrognoCIS in 2015. The same year Medical Informatics Engineering lost data on 3.9 million patients.
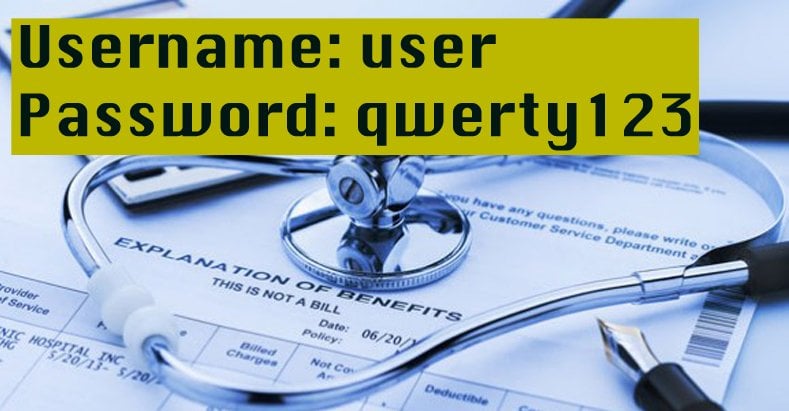
TrendLabs says there are several problems here. First, they used the Shodan search engine to list thousands of devices, like MRI machines, that are attached to the internet with no authentication required or have outdated software that can be exploited. Second, hospitals and doctors offices do not always have the right kind of IT people trained in cybersecurity. And they do not always deploy such common-sense, easy-to-implement ideas like two factor authentication. Hackers can then consult lists like this site listing default passwords to try different passwords to login.
Hackers can take advantage of, for example, the Universal Plug and Play Protocol (UPnP) to access the network by exploiting that exposed via a printer with a public IP address. Since the device is connected to the hospital’s network, the hacker can access its configuration page to gain information about the internal network, like subnet and gateways. That would help them move laterally across that. For example, here is one admin screen for a Ricoh printer system that we found using a simple Shodan search and here is an HP printer configuration page.
Remote desktops are exposed as well. Here for example you can see the login screen of different Windows computers by querying Shodan for devices listening on port 3389.
Some medical devices, like patient monitoring devices, need to have a public IP address in order to communicate with the healthcare provider. If a hacker hacked a patient on a heart monitor, for example, that would obviously cause fatal harm.
This kind of hacking is not strictly just in the USA either. The largest number of exposed hospitals are in Canada. And on the Deep Web you can find UK insurance cards for sale.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion