Costs Associated with Ransomware Infections Skyrocket
Combatting malware infections is often a hard and thankless task made increasingly difficult by hackers. This task is made harder when attackers change tactics. When the costs associated with infections, such as data recovery, increase more stress is placed on organizations and those that defend the organizations. The latest report by Coveware shows that ransom amounts demanded in ransomware incidents has risen approximately 90%. Not only will departments responsible for cybersecurity curse the news but financial managers as well.
Coveware's Ransomware Marketplace Report involved analysis of recent ransomware cases the security firm has investigated. Figures from the investigation showed that the average ransom organizations paid per incident during the first quarter of this year stands at 12,762 USD, compared to 6,733 USD in the final quarter of 2018. This shows that the ransom cost associated with ransomware infections has almost doubled. According to Coveware, this increase can be accredited to the emergence of more expensive and more hands-on forms of ransomware like Ryuk, Bitpaymer and Dharma. These new hands-on, termed hands-on as the attackers actively target victims, ransomware variants no longer use the spray and pray technique of sending out massed spam emails but are far more targeted in approach. This approach has placed companies and organizations in their crosshairs in order to try to extort a much larger ransom.
In order to successfully infect large organizations, hackers use a combination of abusing remote desktop protocols (RDP) and stolen credentials to gain access to networks. Towards the latter half of 2018, the US Federal Bureau of Investigation issued an alert concerning the abuse of RDP. These protocols are a proprietary technology developed by Microsoft in the 90s that allows a user to log into a remote computer and interact with its OS via a visual interface that includes mouse and keyboard input. RDP access is rarely enabled on home computers, however, it is often turned on for workstations in enterprise networks or for computers located in remote locations, where system administrators need access to, but can't get to in person. While a convenient solution for admins far from the troublesome desktop it has opened an avenue for hackers to abuse.
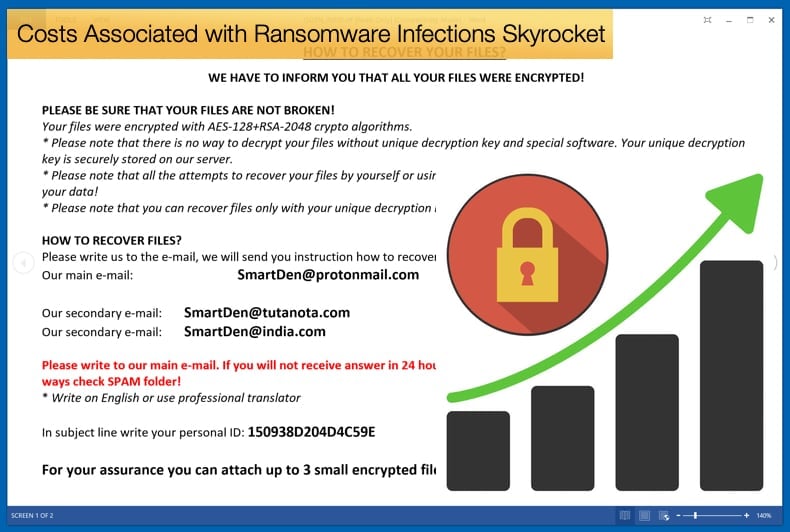
This new approach, when combined with newer ransomware variants, has emboldened hackers to charge more for the data they ransom. In some cases, hackers are demanding six-figure sums as seen in the case of when Jackson County in Georgia was struck by a ransomware incident. The largest ransom demands are associated with Ryuk ransomware, which targets large organizations with a low tolerance for downtime. Coveware's figures suggest the average payment in Ryuk attacks is 286,557 USD. It is not only the cost of the ransom that needs to be considered but also the length of time the incident takes up, according to Coveware the average number of days a ransomware incident lasts amounts to just over a week at 7.3 days, up from 6.2 days in 2018. This increase can be attributed to the better encryption methods used in newer ransomware variants that are harder to decrypt.
The Difficult Decision
It is generally advised that victims do not pay the ransom for a variety of reasons. Primarily these reasons lie in the rationale that paying the ransom funds criminal activities and there is no guarantee that the encrypted data can be decrypted by the hackers in the first place. Another reason recently discussed not to pay is that the payment may violate US sanctions according to legal opinion and whether the funds are determined to land up in country already sanctioned. Despite this, organizations often feel they do not have a choice and pay the ransom with many business leaders feeling it is a no-win situation but still need that data to operate.
The figures put forward by Coveware suggest that 96 percent of the time, paying the ransom results in the victim receiving the decryption tool, with around 93 percent of data recovered. However, the data recovered depends on the type of ransomware. Ryuk has a relatively low data recovery rate of 80 percent, while GandCrab, one of the most common forms of ransomware is close to 100 percent. One would expect this high decryption rate to go against public perception of hackers only looking to scam people out of money. The research suggests that this is not the case with hackers targeting organizations as they adopt approaches more akin to business by ensuring a reputation for the ability to decrypt data. If the group’s reputation is solid, organizations would be more inclined to pay the ransom, rather than a group known for not been able to decrypt files they illegally encrypted. Thus if the group wishes to make money in the long term it is in their interest to be able to decrypt data.
Another reason not to pay the ransom relates to perception. If a company pays the ransom they might be perceived as a soft target, this, in turn, might invite the same attacker or other attackers to continue to target the organization in question. This further results in the perception that ransomware works and hackers will then continue to use it. Fortunately, there are relatively simple ways to combat and importantly prevent ransomware infections. For starters ensuring that RDP ports can't be accessed by default credentials is one, and ensuring that the company is running security software which can protect against malware dropped in phishing attacks is another. Another important counter is ensuring the company follows a backup plan in the event of infection. These measures are shouted from the InfoSec rooftops daily, it is time such measures were adopted universally.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion