RedRum Ransomware Targets Education and Software SMEs
First seen in the wild in December 2019, RedRum ransomware has been used in highly targeted campaigns, the latest of which seem to have education and software small to medium enterprises (SME) in its crosshairs. Further, according to analysis conducted by researchers at BlackBerry and security analysts with KPMG, the ransomware is capable of targeting not only Windows machines but Linux as well. The gang operating the ransomware has adopted several unique tactics, some not seen before in ransomware distribution, to better turn targets into victims.
The ransomware called Tycoon by BlackBerry and KPMG is written in Java, which is rare in itself, but this requires the ransomware to be run in a Java Runtime Environment (JRE) to infect and encrypt targeted data. To that effect, the ransomware operators make use of a trojanized JRE to run the ransomware which is further leveraged inside an obscure Java image format in order to invade detections. So confident are the gang in their evasion techniques that the code itself is not obfuscated in any way. The use of Java and other lesser-known languages including GoLang has been noted by researchers to be an increasing trend. By using Java and the weaponized Java image format the attackers hope to avoid detection without the need to obfuscate code.
Before the ransomware can make use of these techniques alluded to above it needs to be successfully delivered onto the target’s machine. Here the gang does not look to reinvent well but searches for Internet-facing RDP ports. Increasingly ransomware operators are looking to gain a foothold onto a target network via badly configured RDP ports. Even though this tactic is used often, RedRum’s operators still look to remain undetected for a relatively long period. Once a suitable target is found and the initial foothold is achieved via a badly configured RDP port the attacker will silently look to gain administrator credentials.
Once credentials are gained the attacker disables anti-virus software and leaves a backdoor into the machine's network. From there the attacker will connect to the RDP server, this is done to spread laterally across the network and target network assets. Connections are made to other devices be they machines or server assets via compromised RDP connections. Once this is done the attacker can disable anti-virus software across the network. Now the network is primed to be infected with RedRum. This process takes several days to achieve, all the while stealth is the priority.
This has been seen before in numerous other attacks but even the RDP compromise has some unique tactics that deserve to be mentioned. In order to achieve persistence once the foothold is gained the attackers use a technique called Image File Execution Options (IFEO) injection. IFEO settings are stored in the Windows registry. These settings give developers an option to debug their software through the attachment of a debugging application during the execution of a target application. Under the guise of a debugger, the attacker is able to execute arbitrary code. While mostly used to maintain persistence on a victim’s machine the technique can be used to monitor the system for the launch of specific programs and can launch other programs upon the closing of other programs.
JIMAGE
Once infection can begin the ransomware is delivered via a ZIP archive which contains the trojanized JRE with the malware itself compiled into a Java image file (JIMAGE). JIMAGE is defined by the researchers as,
“JIMAGE is a special file format that stores custom JRE images which is designed to be used by the Java Virtual Machine (JVM) at runtime. It encompasses resources and class files of all Java modules that support the specific JRE build. The format was first introduced in Java version 9 and is sparsely documented. Unlike the popular Java Archive format (JAR), JIMAGE is mostly internal to the JDK and rarely used by developers,”
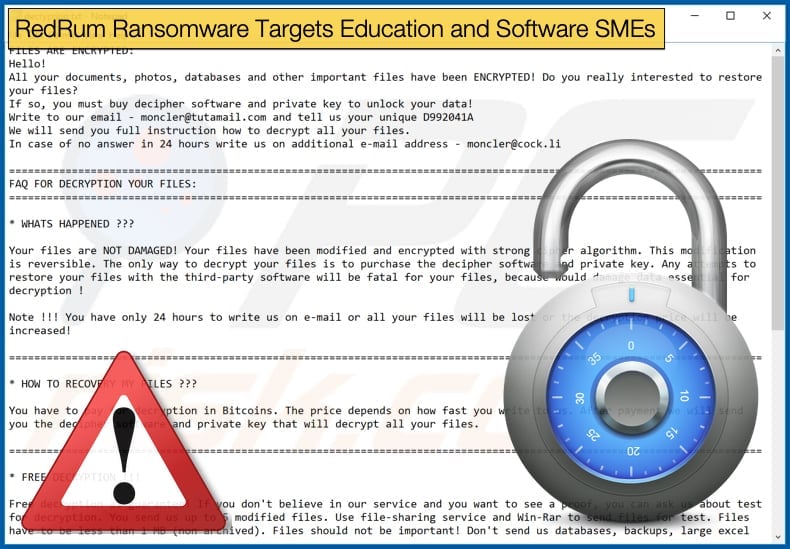
The file format is rarely used, even by developers, and its use further assists in keeping the malware undetected till the moment it encrypts data and drops the ransom note. At this point stealth is irrelevant and all that remains is getting paid by the victim. The gang’s tactics are in line with the targeted approach of finding and making victims. By only targeting a relatively small number of victims from specific sectors, this campaign has seen SMEs in education and software been the primary targets, and using obscure file formats to hide the malware in the gang is doing everything it can in successfully turning potential victims to victims. In concluding, researchers shared a similar view in that the adoption of these tactics is done with a very specific purpose, stating,
“Malware writers are constantly seeking new ways of flying under the radar. They are slowly moving away from conventional obfuscation and shifting towards uncommon programming languages and obscure data formats. We have already seen a substantial increase in ransomware written in languages such as Java and Go. This is the first sample we've encountered that specifically abuses the Java JIMAGE format to create a custom malicious JRE build…Tycoon has been in the wild for at least six months, but there seems to be a limited number of victims. This suggests the malware may be highly targeted. It may also be a part of a wider campaign using several different ransomware solutions, depending on what is perceived more successful in specific environments…The overlap in some of the email addresses, as well as the text of the ransom note and the naming convention used for encrypted files, suggests a connection between Tycoon and Dharma/CrySIS ransomware.”
Some Hope, not much though
It is too early to link RedRum, or Tycoon, to the Dharma and CrySIS ransomware family, however, if this is the case it is indeed worrying as Dharma is one of the most prolific ransomware variants on the current threat landscape and has been for some time. There is some hope for some victims to get away without paying the ransom. Earlier versions of the ransomware which can be determined by the use of .redrum as the file extension added to encrypted files used a public RSA key which in turn was posted on a Bleeping Computer forum enabled the creation of a decryptor. That is where the hope ends in that since .redrum has been used later campaigns have used .thanos and .grinch and currently no decryptor exists for the updated variants.
Despite a decryptor existing for earlier infections, it can be safely assumed that the campaign has been successful as it is still ongoing. Further, by updating the ransomware it is clear that the gang is far from giving up on the project. So far, only Windows machines have been targeted, however, the code contains modules designed specifically to target and carry out encryption on Linux machines. The inclusion of these modules may be an indication of campaigns to come which target sectors known for using Linux. Despite this and its unique use of Java and JIMAGE being infected with RedRum is preventable. As the ransomware relies on abusing poorly configured Internet-facing RDP ports the ransomware can be stopped in its tracks by following best practices.
These best practices include avoid having RDP connections facing the Internet unless absolutely necessary. Organizations should also make sure that accounts that do need access to these ports aren't using default credentials or weak passwords that can easily be guessed as a means of breaking in. Applying security patches when released can also prevent many ransomware attacks, this stops ransomware gangs from exploiting known vulnerabilities to gain access to machines. Organizations should also ensure they regularly backup their network, and that the backup is reliable. While this does not prevent falling victim to a ransomware strain, if it does happen then the organization can restore the network, and importantly operations can continue, without giving in to the ransom demands and hope the cybercriminals live up to their end of the bargain.
Despite being a threat faced by everyone who uses the Internet for over ten years, ransomware continues to be a threat. This is due to a number of reasons, notwithstanding the rapid adoption of new tactics which makes fighting the threat harder, ransomware, and other malware variants still rely on distribution and execution tactics that can be prevented by adopting simple measures. Moving forward education may be the best defense against cybercrime.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion