Joker’s Stash Hobbled
In recent memory, a collaboration between Windows and several other security firms attempted to take out TrickBots infrastructure. Cooler heads warned that this was not the end of TrickBot, and those behind would be back. This was proved to be true but the attempt to take down TrickBot’s infrastructure did achieve one important goal, to prevent the botnet known for distributing ransomware from having any discernible impact on the recent US elections. TrickBot’s return mirrors recent attempts by the US Federal Bureau of Investigation and Interpol taking down Joker’s Stash servers.
Joker’s Stash has developed a reputation over the years for being the biggest marketplace for buying and selling stolen cards. According to ZDNet both the FBI and Interpol sent out a joint email stating that a small number of Joker’s Stash servers were seized disrupting the illegal platforms business operations at least temporarily. The operation was still described as ongoing and more servers have been targeted for seizure. Seizure banners appeared on four Joker's Stash sites, at jstash.bazar, jstash.lib, jstash.emc, and jstash.coin.
The websites where the seizure banner appeared are recognized as top-level domains (TLD), which represent the top level of the hierarchical order the Internet applies to the Domain Name System. Those in question are managed by Emercoin, a blockchain company. Records for these domains are stored inside a blockchain and cannot be transferred to anyone else without the domain owner's cryptographic signature.
While the operation is still ongoing, Joker’s Stash operations were disrupted. Completely removing the marketplace from the Internet will prove to be far harder than seizing a few servers, unfortunately. Those behind Joker’s Stash maintain several versions of the website, including Blockhain domains. Some of the domains used include .bazar, .lib, .emc, and coin, as well as two .onion. Initially when the news broke several users on the popular Russian-speaking cybercriminal forum XSS believed that the entire infrastructure was taken down.
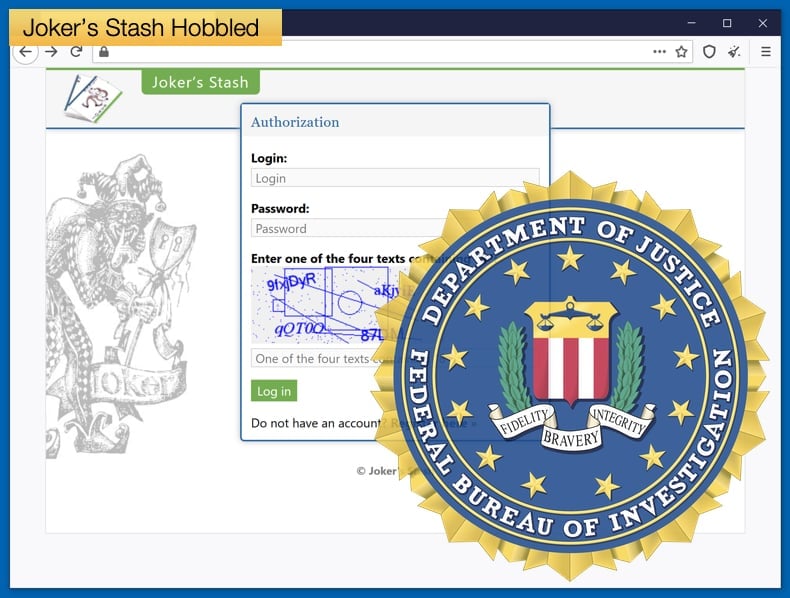
Not long after a representative for Joker’s Stash took to another cybercriminal forum Club2CRD with a focus on various types of credit card fraud created a dedicated forum discussing events. In one post by the representative stated that only the .bazar site seemed to be affected as the .bazar domain’s external proxy server had been “busted.” The representative further noted that the server contained none of the shop data and the marketplace would be up and running in a matter of days. Lastly, the post also stated that the .onion sites were unaffected and customers should use those until the Blockchain domains had recovered from the takedown attempt.
Impact of Seizures
Two security firms have been tracking the seizure and subsequent recovery efforts by those behind Joker’s Stash. Both Intel471 and Digital Shadows agree that the seizure would not have a lasting impact on the marketplace. The Digital Shadows team noted,
“The seizure of the .bazar domain likely will not do much to disrupt Joker's Stash, especially since the team behind Joker's Stash maintain several versions of the site and the site's Tor-based links are still working normally,”
Given that the marketplace has a following on underground forums, the marketplace can easily be moved to other Blockchain domains and this information can be easily conveyed to other visitors to the forum. It might be an inconvenience but the likelihood of crippling the operation as it stands is slim. The Digital Shadows team discussed other ramifications for the marketplace, speculating that,
“Law enforcement disruption may impact Joker’s Stash’s reputation within the cybercriminal community. Still, as the Tor versions of the site are still accessible and with Joker’s Stash’s standing as a credible marketplace, cybercriminals will likely continue to utilize the site. In the future, additional AVC sites could be the target of takedown operations by law enforcement in an attempt to deter cybercriminals. Unfortunately, when one site or operation is taken down, cybercrime finds a way through other platforms with cybercriminals ready to fill the void.”
In the past, we have seen marketplaces and forums taken down, often with seizure notifications be published where the site would have been. Such actions often create confusion and no small amount of concern for the cybercriminals who use them. These forums are often used as marketing tools, selling malware, or data stolen from a well-known data breach. It is not always law enforcement that attaches the seizure banner, but sometimes pranksters looking to sow no small amount of chaos will attach a banner once an administrator takes the forum down. This was likely the case in 2018 when the KickAss forum was taken down by administrators, possibly in an attempt to cash out. A seizure banner was posted but no law enforcement agencies confirmed the seizure, suggesting that the banner was added by a third-party.
There is one way to check if law enforcement took down the site and that is the duration that the seizure banner is up, other announcements made through official channels. In the case of Joker’s Stash, the seizure banner is likely to be up for an extended period. The team at Digital Shadows believes this is the case as law enforcement agencies will want to show that even Blockchain domains can be successfully taken down, even if the operation is likely to survive a few of their servers being seized.
Blockchain DNS Abuse
Joker’s Stash is regarded as one of the original criminal organizations who looked to use Blockchain DNS technology to their advantage. Well one of the first adopters, security firms have noticed an increase in hacker marketplaces moving some of their infrastructures to Blockchain domains. Commenting on why this is so researchers noted,
“Blockchain DNS technology is a decentralized system for top-level domains, and it brings significant security advantages―think bulletproof-hosted platforms and obscured malicious activity. It’s also much harder for security services to target blockchain DNS sites because they’re not regulated by a central authority in the way conventional DNS sites are. You can read more on how cybercriminals use blockchain DNS here. Typically, blockchain DNS sites are accessed via Chrome, with a browser extension that enables access to sites with certain URL suffixes. In July 2017, the Joker’s Stash began using blockchain DNS alongside its established Tor domain. Users wanting to access the .bazar version of the site needed to install a blockchain DNS browser extension or add-on.”
Before the development of Blockchain DNS technology, how Internet traffic was handles boiled down to the user typing an address in their browser of choice. The computer will then query a DNS server for an IP address. So, once the address is typed, say somewebsite[.]com Internet protocols will look for the IP address associated with the website address which is a series of numbers that might look something like this – 54.334.146.91. Once that is complete the website is served to the computer that requested it. The final part of the domain (.com, .de, .uk, .org) is known as a Top-Level Domain (TLD) and is controlled by a central authority such as Internet Corporation for Assigned Names and Numbers (ICANN), Nominet or DENIC.
A Blockchain DNS has no central authority like ICANN and it handles queries differently. DNS lookup tables are shared over a peer-to-peer network and use a different technology from traditional DNS requests. This is what makes shutting down a Blockchain domain like .bazar more difficult as no central authority can provide the exact IP address. The increased level of anonymity is what cybercriminals might find most appealing. However, technology does have advantages for those not looking to profit from illegal activities.
For instance, those who reside in regions defined by excessive government censorship or control over ISPs can use a Blockchain domain to counter such censorship. In terms of security Blockchain domains can help prevent DNS spoofing, this is when an attacker inserts corrupt DNS data so that the name server returns an incorrect IP address and redirects traffic to a site under the attacker's control.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion