Looking into Darkside’s 90 million dollars in Earnings
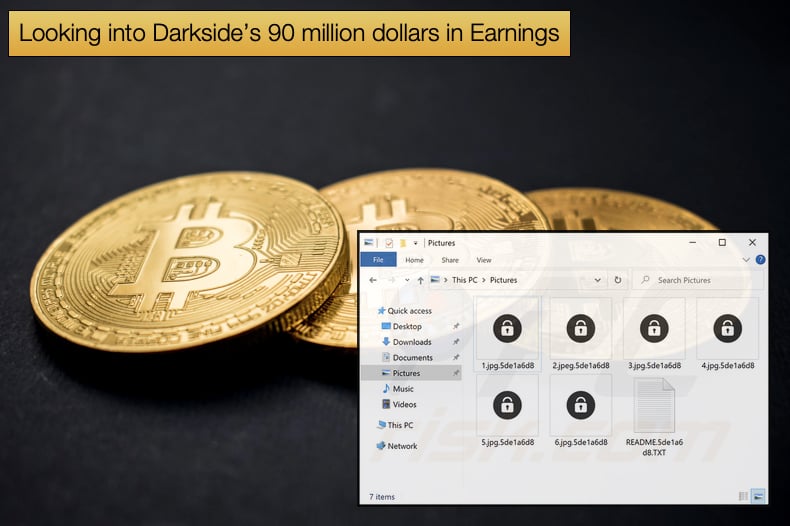
The ransomware gang behind the DarkSide who attacked the Colonial Pipeline has only been operational for approximately nine months. Due to the incident, they are best known for, they have reached a level of notoriety cybercriminals tend to want to avoid. This has prompted some to research how much money the gang has made. Recently, Elliptic has dug into the murky depths of cryptocurrency blockchains to figure out how much the gang has made in those nine months. In Bitcoin, the ransomware’s developers and affiliates have netted a total of over 90 million USD.
In a blog article published by Elliptic, researchers gave us another interesting insight into how the gang managed their ransom payments. Much of the work involved tracking down the wallets used by the gang to facilitate payments. More payments may be uncovered in the future given the level of anonymity afforded to Bitcoin transactions, but it is important to note that Bitcoin transactions are not 100% anonymous and can be traced to a certain degree. According to Elliptic’s research 99 organizations have suffered a DarkSide infection with approximately 47% of the victims paying the ransom.
As DarkSide operates as a ransomware-as-a-service the extorted amounts are split between affiliates and the malware’s developers. The affiliates can be responsible for finding victims, gaining initial access to victim networks, and then initializing the ransomware. Researchers found that,
“Any ransom payment made by a victim is then split between the affiliate and the developer. In the case of DarkSide, the developer reportedly takes 25% for ransoms less than $500,000, but this decreases to 10% for ransoms greater than $5 million. This split of the ransom payment is very clear to see on the blockchain, with the different shares going to separate Bitcoin wallets controlled by the affiliate and developer. In total, the DarkSide developer has received bitcoins worth $15.5 million (17%), with the remaining $74.7 million (83%) going to the various affiliates.”
One question that begs to be asked is how they get away with laundering the money from Bitcoin to fiat currency. This has been answered by several other research firms as best as can be done given the level of secrecy criminal organizations prefer to operate with. In summary, while many cryptocurrency exchanges are required by law to implement Know Your Customer (KYC) legislation to prevent money laundering and fraud, these rules are not equally applied across all jurisdictions.
This opens up the possibility for unregulated or even poorly regulated, exchanges to act as a safe haven for cybercriminals and organized crime. These exchanges are just one step in the laundering process which often involves several parties including money mauls, who will draw cash or use their bank accounts to receive funds to be handed over to another party.
Colonial Pipeline Pays
Last week when the ramifications of the Colonial Pipeline incident rumors from unnamed sources were saying that the company paid the 5 million USD ransom. Other publications reported that the ransom was indeed paid. Ondrej Krehel, chief executive officer and founder of digital forensics firm LIFARS and a former cyber expert at Loews Corp, said,
“They had to pay, this is a cyber cancer. You want to die or you want to live? It’s not a situation where you can wait.”
Government agencies and law enforcement will argue with this point of view and still advise that victims do not pay the ransom as it supports criminal activity. While, much of whether Colonial Pipeline actually paid or not remained speculative at best, research conducted by Elliptic seems to confirm that the company did pay. According to Elliptic,
“Elliptic has identified the Bitcoin wallet used by the DarkSide ransomware group to receive ransom payments from its victims, based on our intelligence collection and analysis of blockchain transactions. This wallet received the 75 BTC payment made by Colonial Pipeline on May 8, following the crippling cyberattack on its operations - leading to widespread fuel shortages in the US…Our analysis shows that the wallet has been active since 4th March 2021 and has received 57 payments from 21 different wallets. Some of these payments directly match ransoms known to have been paid to DarkSide by other victims, such as 78.29 BTC (worth $4.4 million) sent by chemical distribution company Brenntag on May 11.”
It was also shown that the affiliate's share was sent to the same wallet address involved in both the Colonial Pipeline incident and Brenntag incident. During this period there was a lot of activity regarding known DarkSide affiliated wallets, understandably given the scope of the Colonial Pipeline incident. The wallet that received the 5 million USD was soon emptied leading some to believe that the US Government had managed to seize the wallet in question.
The speculation may be proved to be false as analysis revealed that most of the Bitcoin was moved out of the wallet on May 9. Further analysis revealed that 18% of the Bitcoin was sent to a small group of exchanges and an additional 4% of the wallet's contents was sent to Hydra, the world’s largest darknet marketplace, servicing customers in Russia and neighboring countries. Hydra offers cash-out services alongside narcotics, hacking tools, and fake IDs. These allow Bitcoin to be converted into gift vouchers, prepaid debit cards, or cash Rubles.
DarkSide Shuts Down Operations
When it was rumored that the US Government had seized assets and funds in the possession of DarkSide operators it also emerged that the gang was shutting down operations. A message was shared on an underground hacker forum by someone going by UNKN, possibly a contraction of the unknown, who is regarded as a direct competitor to the Sodinokibi ransomware gang. The post stated,
“Since the first version, we have promised to speak honestly and openly about problems. A few hours ago, we lost access to the public part of our infrastructure, namely : Blog, Payment server, DOS servers. Now these servers are unavailable via SSH, the hosting panels are blocked. Hosting support, apart from information ‘at the request of law enforcement agencies’.”
Journalists discovered that websites controlled by DarkSide were indeed down. However, Bleeping Computer confirmed that the Tor payment site was still accessible. It may be that the gang was feeling the heat from law enforcement and decided to pull the plug and may have gone into early retirement. It is also possible that the group may shift operations and emerge as another gang with modified ransomware. It does appear that the affiliate program run by the ransomware’s creators is now closed. Intel 471, managed to get access to a message sent to affiliates. The translated message reads as follows,
“Starting from version one, we promised to speak about problems honestly and openly. A couple of hours ago, we lost access to the public part of our infrastructure, in particular to the blog, payment server, CDN servers. At the moment, these servers cannot be accessed via SSH, and the hosting panels have been blocked. The hosting support service doesn't provide any information except "at the request of law enforcement authorities." In addition, a couple of hours after the seizure, funds from the payment server (belonging to us and our clients) were withdrawn to an unknown account. The following actions will be taken to solve the current issue: You will be given decryption tools for all the companies that haven't paid yet. After that, you will be free to communicate with them wherever you want in any way you want. Contact the support service. We will withdraw the deposit to resolve the issues with all the affected users. The approximate date of compensation is May 23 (due to the fact that the deposit is to be put on hold for 10 days on XSS). In view of the above and due to the pressure from the US, the affiliate program is closed. Stay safe and good luck. The landing page, servers, and other resources will be taken down within 48 hours.”
The message sent to affiliates confirms statements made on the underground hacker forum. Given the stir the Colonial Pipeline incident caused, which prompted US President Joe Biden to sign an executive order aimed at strengthening both government and private cybersecurity measures, shutting down operations may be a prudent step. However, the damage is done and by shutting down operations law enforcement is unlikely to stop pursuing those they believe are involved. At the time of writing, no statement by law enforcement could be found confirming Bitcoin or asset seizures.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion