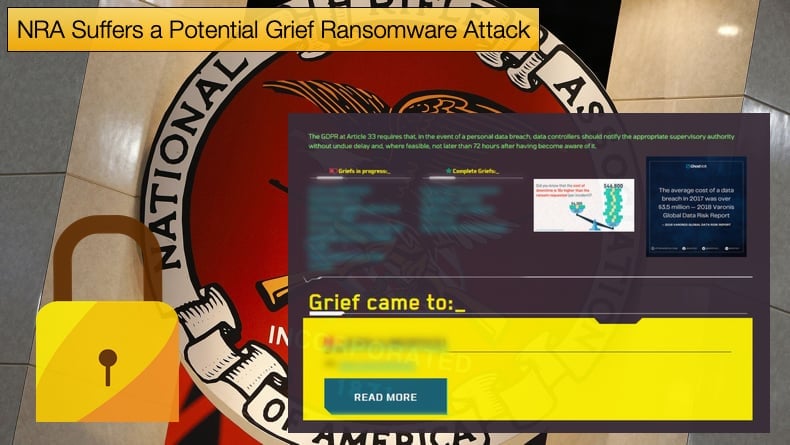
NRA Suffers a Potential Grief Ransomware Attack
According to the threat actors behind the Grief ransomware strain, they have successfully compromised the National Rifle Association (NRA) network, stolen data, and encrypted their data. Bleeping Computer reports that the ransomware group posted the announcement to their leak site along with data stolen from the NRA. The site now boasts images of Excel spreadsheets containing tax and investment information allegedly belonging to the NRA. Further, the group leaked a zip file, “National Grants.zip”, which is reported to contain information relating to grant applications done by the NRA.
Bleeping Computer has attempted to contact the NRA on several occasions with no response from the organization best known for promoting American Gun Rights as well as training programs for responsible gun use.
The organization has also been involved in several controversies in recent memory with reports suggesting the NRA is in financial trouble resulting from dwindling memberships. Is this incident another one of the instances of bad press to add to the growing pile? It might be following a statement made by Andrew Arulanandam, managing director of the NRA’s Public Affairs department. The statement notes,
“NRA does not discuss matters relating to its physical or electronic security. However, the NRA takes extraordinary measures to protect information regarding its members, donors, and operations – and is vigilant in doing so.”
This can be a dangerous line to take, as if it is proven that indeed the NRA has fallen victim to the threat group behind the ransomware, strongly believed to be Evil Corp. There will be more difficult questions to answer as to why they were not upfront about the attack and why the “...extraordinary measures to protect information…” failed.
The attack on the NRA by affiliates of Evil Corp. is also interesting in the sense that the organization is believed to be struggling both economically and maintaining a sense of relevance to the perceived values of American life. Given the financial state, the NRA is in the likelihood of being paid the ransom might drop off significantly. If this is the case then there is sure to be press attention for the financially motivated threat group, as this article proves.
However, press attention does not automatically translate into financial rewards. The recent retirement of Sodinokibi, again, from the treat landscape illustrates the fundamental importance of being paid for your efforts, no matter their illegality.
DoppelPaymer to Grief
In May of this year, DoppelPaymer ransomware activity effectively dropped off a cliff with no new announcements of victims via the leak site. Interestingly, DoppelPaymer is believed to be a fork of BitPaymer with developers of the latter believed to have parted ways over a difference in opinion.
When DoppelPaymer activity dropped off a new ransomware strain emerged called Grief. Researchers discovered that both DoppelPaymer and Grief shared the same encryption routine. More importantly, they were both distributed via the same infrastructure, namely the Dridex botnet.
Dridex started life out as a banking trojan designed to steal banking information and credentials. It was the piece of Malware that enabled the group that was to become known as Evil Corp to make a splash on the threat landscape. Once credentials are harvested they are either sold off or are used to commit several kinds of banking and wire fraud. Over the years the malware has evolved to become a delivery network for other malware strains with ransomware being the most popular recently.
These bits of information suggest strongly that Evil Corp is behind not only DoppelPaymer but the emergence of Grief. It is not clear if Grief is a fork, similar to the BitPaymer DoppelPaymer split or a complete pivot by the same development team to help avoid the prying eye of law enforcement, something Evil Corp is keen to avoid following several US Indictments. Commenting on the rise of Grief security firm ZScaler notes,
“In early May 2021, DoppelPaymer ransomware activity dropped significantly. Although the DoppelPaymer leak site still remains online, there has not been a new victim post since May 6, 2021. In addition, no victim posts have been updated since the end of June. This lull is likely a reaction to the Colonial Pipeline ransomware attack which occurred on May 7, 2021. However, the apparent break is due to the threat group behind DoppelPaymer rebranding the ransomware under the name Grief (aka Pay OR Grief). An early Grief ransomware (aka Pay or Grief) sample was compiled on May 17, 2021. This sample is particularly interesting because it contains the Grief ransomware code and ransom note, but the link in the ransom note points to the DoppelPaymer ransom portal. This suggests that the malware author may have still been in the process of developing the Grief ransom portal. Ransomware threat groups often rebrand the name of the malware as a diversion.”
ZScaler researchers also noted that the code differences between DoppelPaymer and Grief are minimal. It was noted that Grief still retains the code to decrypt data from the binary’s .sdata section and that the Grief string encryption algorithm is similar to DoppelPaymer, bar the RC4 key was increased from a length of 40 bytes to 48 bytes.
Further, the vast majority of the two codebases are very similar with identical encryption algorithms, 2048-bit RSA and 256-bit AES, import hashing, and how the entry point offset is calculated. At the time researchers concluded,
“Grief ransomware is the latest version of DoppelPaymer ransomware with minor code changes and a new cosmetic theme. The threat group has been very active since the release of Grief in the middle of May 2021. However, they have been successful in maintaining a low profile so far. This is in light of recent high-profile attacks including the Colonial Pipeline hack by Darkside ransomware and the Kaseya supply-chain attack by REvil (Sodinokibi).”
Since then those behind Grief have threatened to wipe decryption keys if the victims hire ransomware negotiators. With the now ransomware gang stating,
“We wanna play a game. If we see professional negotiator from Recovery Company™ - we will just destroy the data. Recovery Company™ as we mentioned above will get paid either way. The strategy of Recovery Company™ is not to pay requested amount or to solve the case but to stall. So we have nothing to loose in this case. Just the time economy for all parties involved. What will this Recovery Companies™ earn when no ransom amount is set and data simply destroyed with zero chance of recovery? We think - millions of dollars. Clients will bring money for nothing. As usual." - Grief ransomware gang.”
This change in tactics is believed to be a move to operate outside US sanctions. To help in this endeavor, the gang has also moved away from receiving Bitcoin as the ransom currency, now favoring Monero.
There are possibly two reasons for this, Monero has tighter privacy and anonymity controls, which is appealing to cybercriminals for several obvious reasons. Secondly, law enforcement agencies have proven capable of seizing Bitcoin in wallets controlled by suspected cybercriminals.
The tactic preventing the hiring of negotiators is seen by security professionals as an evolution on the now popular double extortion tactic, which has evolved even further to include the hiring of call center agents to phone victims and demand payment.
Another tactic was designed to place the victim under increased pressure to pay the ransom. With the attack on the NRA, the days of Grief laying low may be behind us. With the retirement of Sodinokibi, there will be a scramble to control the now-defunct ransomware’s large market share.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion