New Malware Destroys Hard Drive to Avoid Detection
Security researchers recently discovered a new strain of malware that uses unique – and somewhat extraordinary – measures to avoid detection and analysis. Known as Rombertik, this malware strain is unique even among other forms of self-destructing malware due to its unusual evasion techniques. Once Rombertik detects any analysis tool on the infected machine, it immediately attempts to delete the PCs Master Boot Record (MBR) and all home directories. This puts the machine in a constant reboot loop – essentially making the computer unusable. This complex piece of malware collects data about everything a user does online in an attempt to obtain login credentials and other sensitive information.
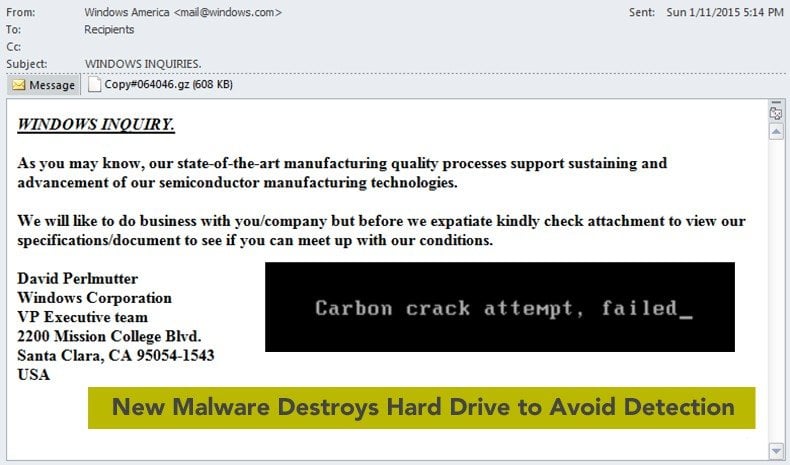
According to security researchers from Cisco, Rombertik is installed on vulnerable machines via a phishing campaign that combines a ‘standard’ phishing email with a malicious attachment. Once loaded in the PC, the malware runs a series of tests to determine if it is running in a sandbox environment. If no sandbox is detected, Rombertik decrypts and installs itself on the infected PC. Then Rombertik launches a second copy of itself which is subsequently overwritten by the malware’s core functionality. To further avoid detection, the malware then runs another series of checks to ensure it isn’t being analyzed in system memory.
If any indication that the malware is being analyzed is detected, Rombertik immediately attempts to destroy the machine’s MBR before restarting the PC.
Without a MBR, the PC enters an endless restart loop that is difficult, if not impossible, to fix without completely reformatting the hard drive. Rombertik also protects itself from analysis in a sandbox environment by writing random data to memory over 960 million times. This action overwhelms most analysis tools that detect malware by logging system activity. To put that into perspective, any analysis tool attempting to record all 960 million write instructions would create a log file over 100 gigabytes in size – a lot of data to analyze and an effective way to cover its tracks when a sandbox is detected.
What security researchers have been able to determine so far is that Rombertik contains lots of “garbage code” that has been added simply to complicate analysis. Over 75 images and 8,000 functions have been found in the packed version of the malware that serve absolutely no function to the malware and are included only to make the job of security researchers more difficult. Self-destructive malware is nothing new. Just a few months ago, a strain of self-destructive malware was used in the notorious Sony Pictures Entertainment breach and in 2013, Wiper malware was used in a campaign against South Korean banks and media outlets.
Rombertik is more advanced than either of these malware strains and could pose a significant threat to PC users around the world for the next several months.
The best way to protect yourself from Rombertik and other self-destructive malware strains is to ensure your PC is updated regularly. Never download or open an attachments from unsolicited emails and do not follow any links from email addresses you are not already familiar with. Notice that there are different opinions about this malware - some security researches claim that Rombertik is not that dangerous at all - for example Blue Coat.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion