Operation Lotus Blossom, a New Advanced Persistent Threat, Discovered in the Wild
There have been an increasing number of advanced persistent threats (APTs) discovered in recent months. These attacks threaten PC security on a global scale and the people behind these attacks are no slouches either. To create an effective APT campaign, many resources are required that go well beyond the scope of the everyday cybercriminal out looking to make a few fraudulent dollars at the expense of others. In general, a large amount of time, money, and knowledge is required to create the custom malicious programs that are at the heart of any APT campaign. These campaigns are specifically created to carry out specific, targeted attacks against powerful targets – usually government and state-sponsored entities. Recently, a new APT campaign was discovered by security researchers from AlienVault Labs that has been dubbed Operation Lotus Blossom.
This advanced malware campaign seems to specifically target government-related entities in Hong Kong, Vietnam, Indonesia, and the Philippines. While security researchers believe that this attack is being used to gain a geopolitical advantage by the hackers behind the campaign, the possibility hasn’t yet been ruled out that this attack could extend into the private sector in the near future – just as Stuxnet and Duqu have in the past. Operation Lotus Blossom works because of a custom malware toolkit that the creators of the campaign have named Elise.
Some of the features inherent to this malware toolkit include the ability to evade sandbox detection, the ability to connect to (and control) servers on infected networks, the ability to exfiltrate sensitive data, and finally, the ability to deliver a secondary malware payload if deemed necessary.
The level of organization behind this campaign indicates that it is most likely a state-sponsored malware attack; although at the time of this writing, the nation behind the attack is still unknown. Based on the targeted countries, however, it is clear that whoever is behind Operation Lotus Blossom has a significant interest in Southeast Asia and hopes to benefit from the information obtained from government entities within the countries mentioned above. According the researchers from AlienVault Labs, over 50 confirmed attacks have already taken place using this custom malware toolkit.
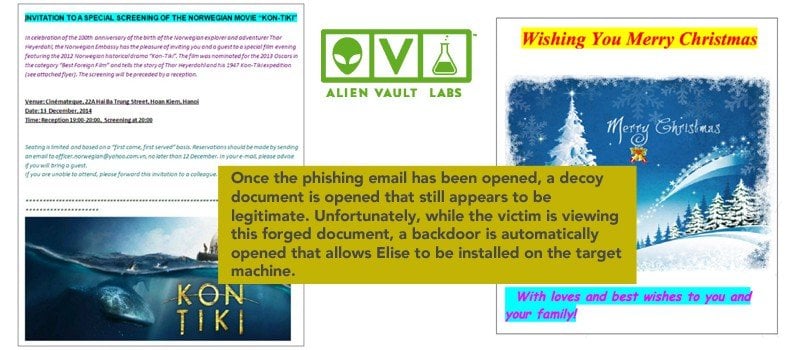
Like so many other instances of cyber espionage before it, Elise is spread via a spear phishing email campaign. In this case, the email campaign is specifically designed to look like authentic information that government and military targets would expect to see. For example, the email might contain an attachment that includes a military roster or an invoice from another government agency. These attachments look legitimate enough that most victims open the email. Once the phishing email has been opened, a decoy document is opened that still appears to be legitimate. Unfortunately, while the victim is viewing this forged document, a backdoor is automatically opened that allows Elise to be installed on the target machine. After Elise has been successfully installed, the malware immediately contacts a command and control server in search of further instructions from the hackers behind this nation state-driven malware campaign. Once a single government or military-related network has been compromised, the attackers behind this attack are able to conduct network reconnaissance (remember that Elise is capable of controlling network servers once installed).
The attackers are also able to use the newly infected network as a base of operations for compromising new systems and can even deliver additional malware payloads via the compromised network.
While once again reiterating that Elise has not yet been observed targeting civilian PCs, hackers can quickly adapt this malware campaign to specifically target individuals. Since the basic premise of this campaign is the theft of data while avoiding detection, it isn’t a stretch at all to assume that a modified version of Elise could be released at any time with the sole purpose of infecting PCs to steal data. This data could range from sensitive personal information that could be used in identity theft crimes to financial data used to steal money from banks via anonymous wire transfers to banks outside the jurisdiction of local law enforcement entities. As of this writing, the researchers at AlienVault Labs responsible for identifying this malware strain have already released an IDS signature for Elise to help detect malicious activity as a result of an Elise infection.
That said, other security suite manufacturers haven’t yet identified the Elise signature meaning that machines not protected by AlienVault Labs Unified Security Management (USM) Platform will not be able to detect Elise until more information about this threat becomes available. Until that time comes, the best way to protect your PC from Elise is to ensure that all applications are updated – both the Windows OS and any third-party applications. Also, ensure that all Web browser plugins are updated or better yet, uninstalled if they are not needed for daily PC tasks.
Examples of browser plugins that are susceptible to exploitation by Elise and other popular malware variants include Adobe Flash Player, Java, and Microsoft Silverlight.
In addition, check to make sure macros are disabled in Microsoft Office as this is another common method of infection when dealing with any spear phishing email campaign. Many of the fake email attachments associated with Elise and Operation Lotus Blossom leverage a backdoor made possible by the use of macros so making sure that this feature is disabled unless absolutely necessary is a good way to prevent infection. Finally, keep antivirus signatures regularly updated as security software manufacturers continue to identify this threat and update their proprietary virus signature files to detect the activities that are associated with a covert Elise infection. As APT campaigns become increasingly popular among hackers funded by unknown countries, the effects of these attacks will become more prevalent and could threaten your PC in the very near future.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion