Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Win32/Bluteal.B!rfn?
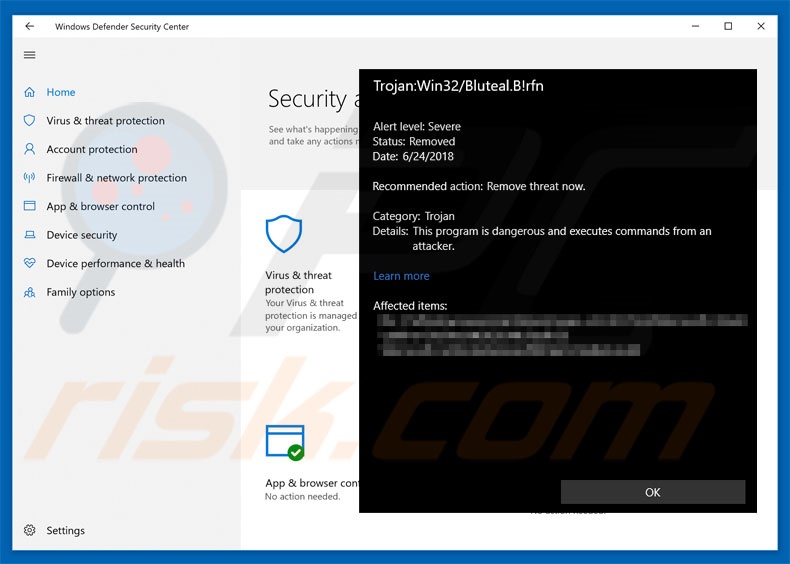
Recently, thousands of users have encountered a pop-up stating that the system is infected with the Win32/Bluteal.B!rfn trojan. The pop-up is displayed by Microsoft Windows Defender, however, this anti-malware tool detects completely legitimate files and identifies them as Win32/Bluteal.B!rfn trojans. This is frustrating and dangerous, since false-positive detections can lead to permanent data loss.
Win32/Bluteal.B!rfn overview
False-positive detections typically occur due to anti-malware suite database flaws - the database contains false information and, therefore, the anti-virus tool detects irrelevant files. Initially, these "flaws" may seem insignificant, however, the tools can permanently delete false-positives.
Furthermore, this behavior might be concerning, since users continually encounter interrupting pop-ups. Resolving this issue is simple - developers must simply update the database and redefine the Win32/Bluteal.B!rfn entry. Remember that Win32/Bluteal.B!rfn malware exists. Currently there are many users of Windows Defender with outdated databases.
Therefore, they will encounter these false-positives. If Windows Defender has detected the Win32/Bluteal.B!rfn trojan on your system, we strongly advise you to firstly update the tool (especially if you are certain that the detected file is legitimate) before taking any further action. To update Windows Defender, follow these steps below.
| Name | Win32/Bluteal.B!rfn virus |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Trojan examples
The Internet is full of trojans, most of which are extremely dangerous. The list of examples includes (but it is not limited to) TrickBot, Emotet, FormBook, and Adwind.
Most of these viruses are developed to gather sensitive information (which is later misused to generate revenue [via online money transfers, identity theft, and so on]) and promote other viruses (typically ransomware). These viruses present a strong case to actively protect your privacy and computer safety.
Trojans are commonly proliferated using various spam campaigns, such as Monthly Invoice, You Have A Santander Secure Email, and others.
How did Win32/Bluteal.B!rfn install on my computer?
As mentioned above, trojans are typically distributed using spam emails campaigns. Developers send thousands of emails with malicious attachments (typically, MS Office documents). Once opened, these files execute scripts that stealthily download and install malware.
Note that malicious MS Office attachments are only capable of downloading malware when opened using the Office program. If documents are opened with other apps (capable of reading that format), the malware will not be downloaded. Trojans might also be distributed using fake update tools and a deceptive marketing method called "bundling".
Fake updaters infect the system by exploiting outdated software bugs/flaws or simply downloading and installing malware rather than updates. "Bundling" is stealth installation of rogue software together with regular software.
Developers hide "bundled" apps within "Custom/Advanced" settings (or other sections) of the download/installation processes. By rushing these procedures and skipping steps, users often expose their systems to risk of various infections.
How to avoid installation of malware?
The main reasons for computer infections are poor knowledge and careless behavior. Therefore, pay close attention when browsing the Internet and downloading/installing software. You are advised to think twice before opening email attachments. Files that seem irrelevant or been received from suspicious email addresses should not be opened.
Note that newer versions (2010 and above) of MS Office open newly-downloaded documents in "Protected View" mode. This prevents malware installation. Older versions do not have this feature and using them is risky. We also strongly recommend that you keep installed applications up-to-date.
To achieve this use only implemented functions or tools provided by the official developer. Furthermore, carefully analyze each download/installation step and opt-out additionally-included programs. Software should be downloaded from official sources only (using direct download links), rather than using third party downloaders/installers.
These tools are monetized using the "bundling" method and should not be used. Have a reputable anti-virus/anti-spyware suite installed and running. The key to computer safety is caution. If you have been presented with a Win32/Bluteal.B!rfn detection, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
To update Windows Defender, follow these steps:
- Settings -> Update & Security -> Windows Update -> Check For Updates.
- This should prevent further false-positive detections.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Win32/Bluteal.B!rfn?
- STEP 1. Manual removal of Win32/Bluteal.B!rfn malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Win32/Bluteal.B!rfn malware, should I format my storage device to get rid of it?
No, Win32/Bluteal.B!rfn can be removed without formatting.
What are the biggest issues that Win32/Bluteal.B!rfn malware can cause?
That depends on whether it is the phenomenon of legitimate files being detected and identified as Win32/Bluteal.B!rfn, or whether it is the actual Win32/Bluteal.B!rfn trojan. The former could lead to permanent data loss, nonoperational software, and similar. It is possible to save a quarantined file before its deletion, but if it is not - that would lead to the previously described outcomes. If Windows Defender has detected the Win32/Bluteal.B!rfn trojan on your system, you should first update the security tool (update steps). If it is confirmed as the latter (genuine trojan infection), generally - malware infections can cause decreased system performance, severe privacy issues, financial losses, and identity theft.
How did Win32/Bluteal.B!rfn malware infiltrate my computer?
Malware is primarily distributed using phishing and social engineering techniques. For example, malicious programs are spread through drive-by downloads, online scams, freeware and third-party download websites, Peer-to-Peer sharing networks, spam mail, illegal software activation ("cracking") tools, fake updates, and so on.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is capable of detecting and eliminating most of the known malware infections. However, it must be stressed that sophisticated malicious software tends to hide deep within a system - hence, performing a complete system scan is a must.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion