Placed A Malware On The Xxx Streaming Site Email Scam
Phishing/ScamAlso Known As: Placed A Malware On The Xxx Streaming Site spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "Placed a malware on the xxx streaming site"?
"Placed a malware on the xxx streaming site" is a typical scam which is distributed through a spam campaign (by sending bogus emails to many people). This particular campaign is categorized as a sextortion scam. Scammers who distribute it try to make recipients believe that humiliating material will be sent to other people unless they pay a specific cryptocurrency payment.
The email states that the person responsible for sending the email placed malicious software on a pornography website, which was recently visited by the recipient. This malware apparently gave access to the victim's screen and webcam, which was used to record a double-screen video of the recipient watching pornography.
It is also stated that the aforementioned malicious program allowed this cyber criminal to steal contacts from Facebook (Messenger) and email accounts. Unless the recipient transfers $966 (in Bitcoins) to a cryptocurrency wallet provided, the criminal behind this scam threatens to send the compromising video to all of the recipient's contacts.
It is also claimed that this can be proven by sending the video to six of the recipient's contacts. Scams of this type are not new and criminals have been using them for some time, however, many people are not aware and take them seriously. These emails should never be trusted and the best option is to simply ignore them.
| Name | Placed A Malware On The Xxx Streaming Site Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | These criminals falsely claim to have 'embarrassing material', which will be publicized unless the recipient pays a ransom. |
| Cyber Criminal Cryptowallet Address | 18zNp5JhvTMDx8oCN36Ghp4NuUqvU5MXmf, 1K8is5xdVxsAvhiVoocPz6y3XhE3LQJKVa, bc1q3h9lq7z4uke8q8uslx5rlr2xq0xgnu37zt8ywn, bc1qzl2qlywq8fzfm49e7mvsuz4yvpdwpzfqs5g85r, bc1qflasaggvrat2kavt5ygy043k9p5rjwr9kkql03, bc1qpq0ptyh6cwzksu0mkmg4t5xkhvp9q4vfgh4gyq, bc1qehk8rsppsqtwh7hvmmgdz4rnkydtdsx8pqdwjw (the address may vary depending on spam campaign variant). |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of computers. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
This spam campaign is similar to other scams such as "This Account Was Recently Infected", "Hey. It's me! Your Future Friend Or Enemy", "I Have A Forum In The Darkweb", and many more. Typically, scammers use them to trick people into sending cryptocurrency payments. There is also another type of spam campaign.
In many cases, cyber criminals attempt to infect computers with high-risk malicious programs such as LokiBot, Hancitor, Emotet , AZORult, and other similar malware. They send emails that contain attachments and try to trick people into opening them.
Some examples of commonly-used files to spread viruses are Microsoft Office, PDF documents, JavaScript files, archives (ZIP, RAR), executables, and so on. If opened, they trigger download and installation of various malicious programs designed to proliferate other viruses, steal personal information and browsing-related data, and so on.
If a computer is infected with a malware of this type, it could cause financial/data loss, problems with privacy and browsing safety, and other serious issues. We receive a great deal of feedback from concerned users about this scam email. Here is the most popular question we receive:
Q: Hi pcrisk.com team, I received an email stating that my computer was hacked and they have a video of me. Now they are asking for a ransom in Bitcoins. I think this must be true because they listed my real name and password in the email. What should I do?
A: Do not worry about this email. Neither hackers nor cyber criminals have infiltrated/hacked your computer and there is no video of you watching pornography. Simply ignore the message and do not send any Bitcoins. Your email, name, and password was probably stolen from a compromised website such as Yahoo (these website breaches are common). If you are concerned, you can check if your accounts have been compromised by visiting the haveibeenpwned website.
How do spam campaigns infect computers?
Spam campaigns that cause damage though attached files can do so only when those files are opened. Therefore, they cannot infect computers without the manual intervention of the email recipient. For instance, if the attachment is a Microsoft Office document, when opened, it will demand permission to enable macros commands (to disable Protected View mode).
If allowed, the document will download and install a malicious program. If the attachment is an executable file, to cause an infection it needs to be executed/opened, whilst archive files need to be extracted and their contents executed, and so on.
How to avoid installation of malware?
Irrelevant emails that are received from unknown/untrustworthy addresses and contain attachments or web links leading to them should not be trusted ( and the included files should not be opened). Software should not be downloaded from dubious, unofficial websites, using third party downloaders, Peer-to-Peer networks such as torrent clients, eMule, and so on.
The safest method to download software is using official websites and direct download links. Do not use third party, unofficial (fake) software updaters to update operating systems or installed programs. These tools might install malware rather than updates, or exploit bugs and flaws of already installed, outdated software.
Use functions or tools that are provided by official software developers only. Later versions of Microsoft Office (2000 and newer) have "Protected View" mode, which prevents malicious attachments from downloading viruses. Therefore, do not use old versions of MS Office. Do not activate installed software using 'cracking' tools that supposedly bypass paid software activation.
These tools are illegal and often cause download/installation of malware. Finally, have an anti-virus or anti-spyware suite installed and enabled at all times. If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
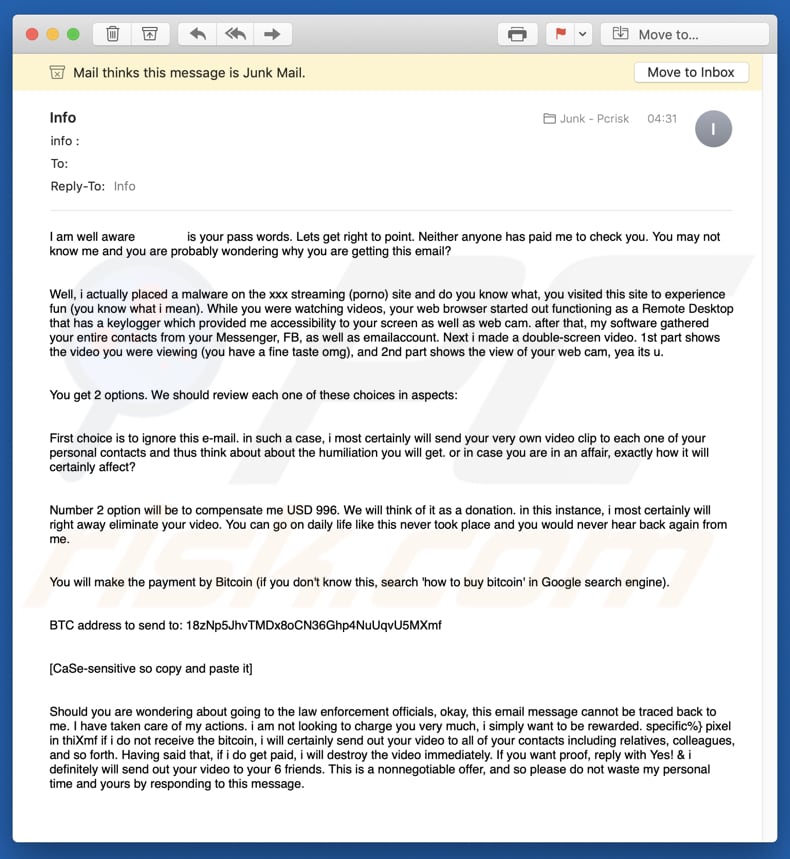
Text presented in the "Placed a malware on the xxx streaming site" email message:
I am well aware * is your pass words. Lets get right to point. Neither anyone has paid me to check you. You may not know me and you are probably wondering why you are getting this email?
Well, i actually placed a malware on the xxx streaming (porno) site and do you know what, you visited this site to experience fun (you know what i mean). While you were watching videos, your web browser started out functioning as a Remote Desktop that has a keylogger which provided me accessibility to your screen as well as web cam. after that, my software gathered your entire contacts from your Messenger, FB, as well as emailaccount. Next i made a double-screen video. 1st part shows the video you were viewing (you have a fine taste omg), and 2nd part shows the view of your web cam, yea its u.
You get 2 options. We should review each one of these choices in aspects:
First choice is to ignore this e-mail. in such a case, i most certainly will send your very own video clip to each one of your personal contacts and thus think about about the humiliation you will get. or in case you are in an affair, exactly how it will certainly affect?
Number 2 option will be to compensate me USD 996. We will think of it as a donation. in this instance, i most certainly will right away eliminate your video. You can go on daily life like this never took place and you would never hear back again from me.
You will make the payment by Bitcoin (if you don't know this, search 'how to buy bitcoin in Google search engine).
BTC address to send to: 18zNp5JhvTMDx8oCN36Ghp4NuUqvU5MXmf
[CaSe-sensitive so copy and paste it]
Should you are wondering about going to the law enforcement officials, okay, this email message cannot be traced back to me. I have taken care of my actions. i am not looking to charge you very much, i simply want to be rewarded. specific%} pixel in thiXmf if i do not receive the bitcoin, i will certainly send out your video to all of your contacts including relatives, colleagues, and so forth. Having said that, if i do get paid, i will destroy the video immediately. If you want proof, reply with Yes! & i definitely will send out your video to your 6 friends. This is a nonnegotiable offer, and so please do not waste my personal time and yours by responding to this message.
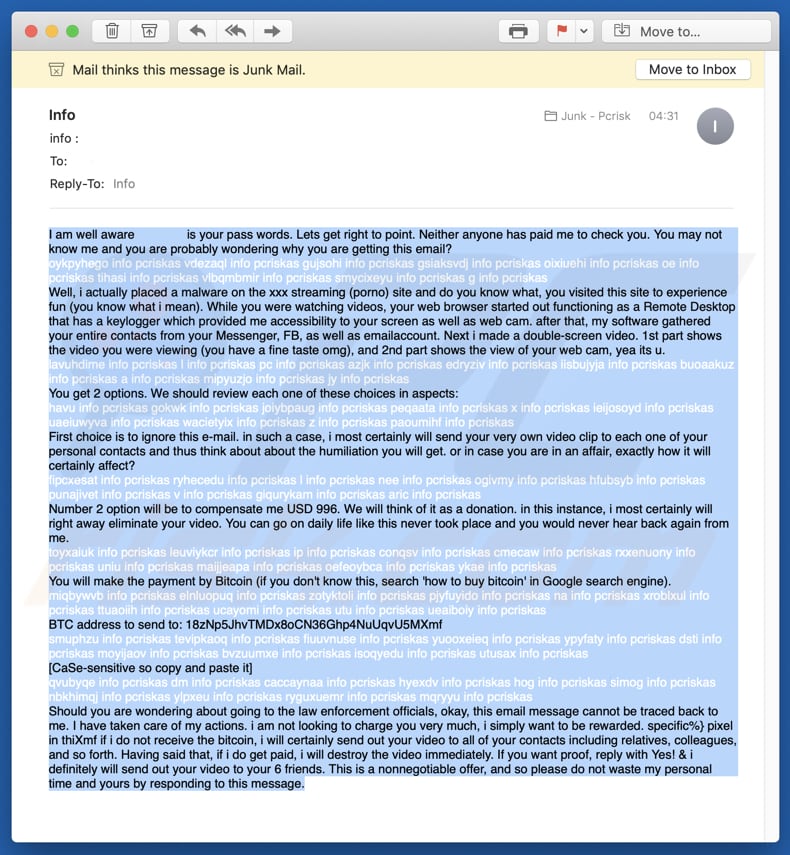
Screenshot of this scam with revealed hidden characters that help to avoid the emails being detected by spam filters:
French variant of this scam email:
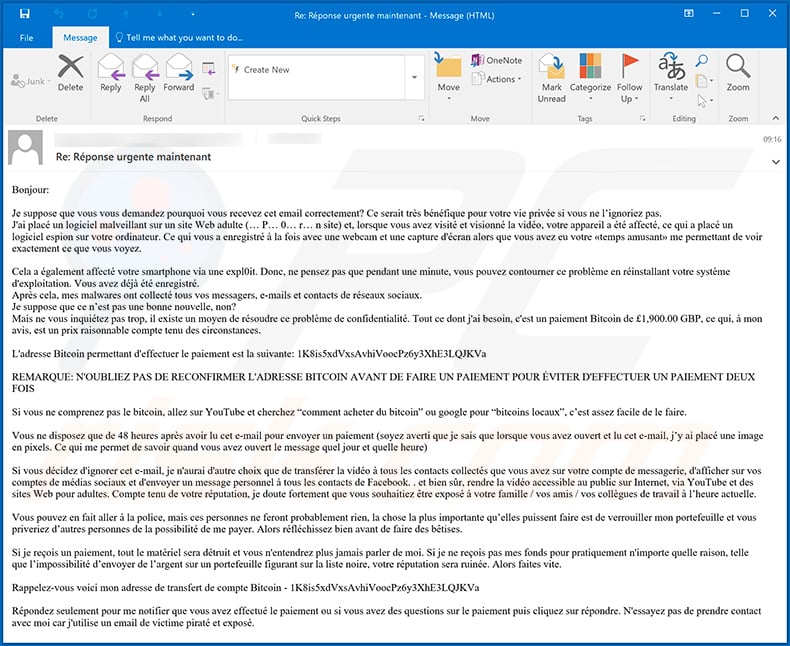
Text presented within this email:
Subject: Re: Réponse urgente maintenant
Bonjour:
Je suppose que vous vous demandez pourquoi vous recevez cet email correctement? Ce serait très bénéfique pour votre vie privée si vous ne l’ignoriez pas.
J'ai placé un logiciel malveillant sur un site Web adulte (… P… 0… r… n site) et, lorsque vous avez visité et visionné la vidéo, votre appareil a été affecté, ce qui a placé un logiciel espion sur votre ordinateur. Ce qui vous a enregistré à la fois avec une webcam et une capture d'écran alors que vous avez eu votre «temps amusant» me permettant de voir exactement ce que vous voyez.Cela a également affecté votre smartphone via une expl0it. Donc, ne pensez pas que pendant une minute, vous pouvez contourner ce problème en réinstallant votre système d'exploitation. Vous avez déjà été enregistré.
Après cela, mes malwares ont collecté tous vos messagers, e-mails et contacts de réseaux sociaux.
Je suppose que ce n’est pas une bonne nouvelle, non?
Mais ne vous inquiétez pas trop, il existe un moyen de résoudre ce problème de confidentialité. Tout ce dont j'ai besoin, c'est un paiement Bitcoin de £1,900.00 GBP, ce qui, à mon avis, est un prix raisonnable compte tenu des circonstances.L'adresse Bitcoin permettant d'effectuer le paiement est la suivante: 1K8is5xdVxsAvhiVoocPz6y3XhE3LQJKVa
REMARQUE: N'OUBLIEZ PAS DE RECONFIRMER L'ADRESSE BITCOIN AVANT DE FAIRE UN PAIEMENT POUR ÉVITER D'EFFECTUER UN PAIEMENT DEUX FOIS
Si vous ne comprenez pas le bitcoin, allez sur YouTube et cherchez “comment acheter du bitcoin” ou google pour “bitcoins locaux”, c’est assez facile de le faire.
Vous ne disposez que de 48 heures après avoir lu cet e-mail pour envoyer un paiement (soyez averti que je sais que lorsque vous avez ouvert et lu cet e-mail, j’y ai placé une image en pixels. Ce qui me permet de savoir quand vous avez ouvert le message quel jour et quelle heure)
Si vous décidez d'ignorer cet e-mail, je n'aurai d'autre choix que de transférer la vidéo à tous les contacts collectés que vous avez sur votre compte de messagerie, d'afficher sur vos comptes de médias sociaux et d'envoyer un message personnel à tous les contacts de Facebook. . et bien sûr, rendre la vidéo accessible au public sur Internet, via YouTube et des sites Web pour adultes. Compte tenu de votre réputation, je doute fortement que vous souhaitiez être exposé à votre famille / vos amis / vos collègues de travail à l’heure actuelle.
Vous pouvez en fait aller à la police, mais ces personnes ne feront probablement rien, la chose la plus importante qu’elles puissent faire est de verrouiller mon portefeuille et vous priveriez d’autres personnes de la possibilité de me payer. Alors réfléchissez bien avant de faire des bêtises.
Si je reçois un paiement, tout le matériel sera détruit et vous n'entendrez plus jamais parler de moi. Si je ne reçois pas mes fonds pour pratiquement n'importe quelle raison, telle que l’impossibilité d’envoyer de l’argent sur un portefeuille figurant sur la liste noire, votre réputation sera ruinée. Alors faites vite.
Rappelez-vous voici mon adresse de transfert de compte Bitcoin - 1K8is5xdVxsAvhiVoocPz6y3XhE3LQJKVa
Répondez seulement pour me notifier que vous avez effectué le paiement ou si vous avez des questions sur le paiement puis cliquez sur répondre. N'essayez pas de prendre contact avec moi car j'utilise un email de victime piraté et exposé.
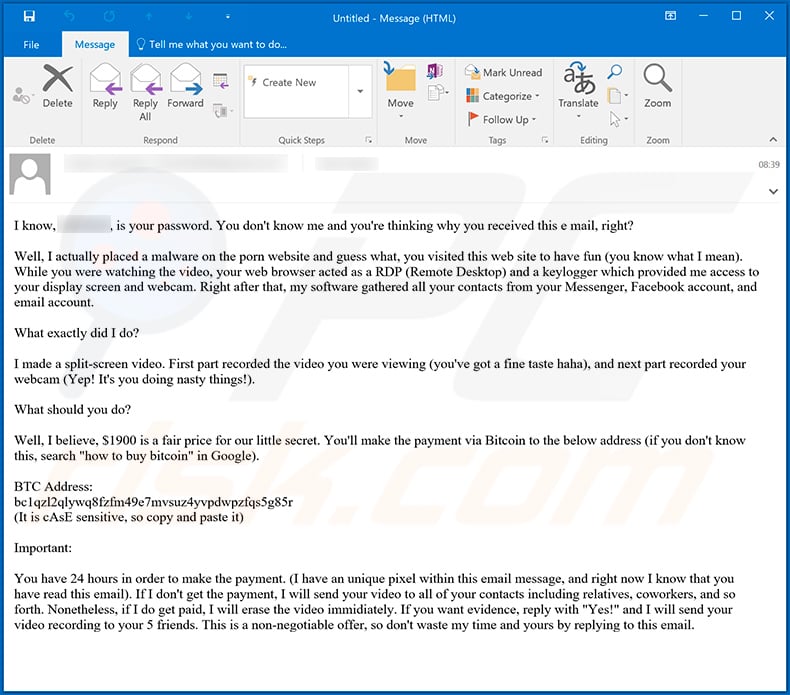
Text presented within this email:
I know, *****, is your password. You don't know me and you're thinking why you received this e mail, right?
Well, I actually placed a malware on the porn website and guess what, you visited this web site to have fun (you know what I mean). While you were watching the video, your web browser acted as a RDP (Remote Desktop) and a keylogger which provided me access to your display screen and webcam. Right after that, my software gathered all your contacts from your Messenger, Facebook account, and email account.
What exactly did I do?
I made a split-screen video. First part recorded the video you were viewing (you've got a fine taste haha), and next part recorded your webcam (Yep! It's you doing nasty things!).
What should you do?
Well, I believe, $1900 is a fair price for our little secret. You'll make the payment via Bitcoin to the below address (if you don't know this, search "how to buy bitcoin" in Google).
BTC Address:
bc1qzl2qlywq8fzfm49e7mvsuz4yvpdwpzfqs5g85r
(It is cAsE sensitive, so copy and paste it)Important:
You have 24 hours in order to make the payment. (I have an unique pixel within this email message, and right now I know that you have read this email). If I don't get the payment, I will send your video to all of your contacts including relatives, coworkers, and so forth. Nonetheless, if I do get paid, I will erase the video immidiately. If you want evidence, reply with "Yes!" and I will send your video recording to your 5 friends. This is a non-negotiable offer, so don't waste my time and yours by replying to this email.
Another French variant of "Placed A Malware On The Xxx Streaming Site" scam email:
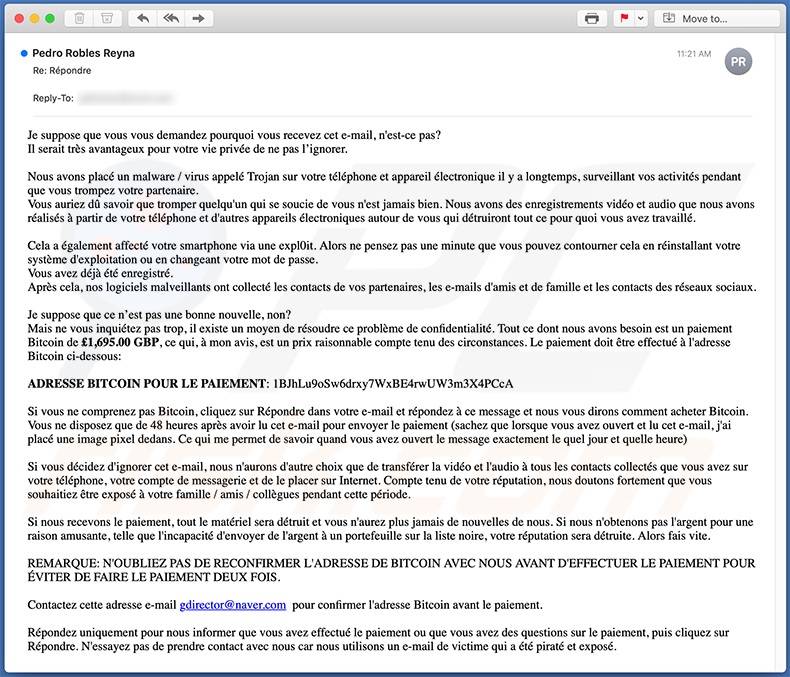
Text presented within:
Subject: Re: Répondre
Je suppose que vous vous demandez pourquoi vous recevez cet e-mail, n'est-ce pas?
Il serait très avantageux pour votre vie privée de ne pas l’ignorer.
Nous avons placé un malware / virus appelé Trojan sur votre téléphone et appareil électronique il y a longtemps, surveillant vos activités pendant que vous trompez votre partenaire.
Vous auriez dû savoir que tromper quelqu'un qui se soucie de vous n'est jamais bien. Nous avons des enregistrements vidéo et audio que nous avons réalisés à partir de votre téléphone et d'autres appareils électroniques autour de vous qui détruiront tout ce pour quoi vous avez travaillé.
Cela a également affecté votre smartphone via une expl0it. Alors ne pensez pas une minute que vous pouvez contourner cela en réinstallant votre système d'exploitation ou en changeant votre mot de passe.
Vous avez déjà été enregistré.
Après cela, nos logiciels malveillants ont collecté les contacts de vos partenaires, les e-mails d'amis et de famille et les contacts des réseaux sociaux.
Je suppose que ce n’est pas une bonne nouvelle, non?
Mais ne vous inquiétez pas trop, il existe un moyen de résoudre ce problème de confidentialité. Tout ce dont nous avons besoin est un paiement Bitcoin de £1,695.00 GBP, ce qui, à mon avis, est un prix raisonnable compte tenu des circonstances. Le paiement doit être effectué à l'adresse Bitcoin ci-dessous:
ADRESSE BITCOIN POUR LE PAIEMENT: 1BJhLu9oSw6drxy7WxBE4rwUW3m3X4PCcA
Si vous ne comprenez pas Bitcoin, cliquez sur Répondre dans votre e-mail et répondez à ce message et nous vous dirons comment acheter Bitcoin.
Vous ne disposez que de 48 heures après avoir lu cet e-mail pour envoyer le paiement (sachez que lorsque vous avez ouvert et lu cet e-mail, j'ai placé une image pixel dedans. Ce qui me permet de savoir quand vous avez ouvert le message exactement le quel jour et quelle heure)
Si vous décidez d'ignorer cet e-mail, nous n'aurons d'autre choix que de transférer la vidéo et l'audio à tous les contacts collectés que vous avez sur votre téléphone, votre compte de messagerie et de le placer sur Internet. Compte tenu de votre réputation, nous doutons fortement que vous souhaitiez être exposé à votre famille / amis / collègues pendant cette période.
Si nous recevons le paiement, tout le matériel sera détruit et vous n'aurez plus jamais de nouvelles de nous. Si nous n'obtenons pas l'argent pour une raison amusante, telle que l'incapacité d'envoyer de l'argent à un portefeuille sur la liste noire, votre réputation sera détruite. Alors fais vite.
REMARQUE: N'OUBLIEZ PAS DE RECONFIRMER L'ADRESSE DE BITCOIN AVEC NOUS AVANT D'EFFECTUER LE PAIEMENT POUR ÉVITER DE FAIRE LE PAIEMENT DEUX FOIS.
Contactez cette adresse e-mail gdirector@naver.com pour confirmer l'adresse Bitcoin avant le paiement.
Répondez uniquement pour nous informer que vous avez effectué le paiement ou que vous avez des questions sur le paiement, puis cliquez sur Répondre. N'essayez pas de prendre contact avec nous car nous utilisons un e-mail de victime qui a été piraté et exposé.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Placed A Malware On The Xxx Streaming Site spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion