Avoid getting scammed by the "I have been watching you" sextortion email
Phishing/ScamAlso Known As: I have been watching you sextortion email
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the "I have been watching you" email?
"I have been watching you" is a spam email our researchers have classified as a sextortion scam. This letter falsely claims that there is proof of the recipient's infidelity and threatens to leak it - unless a payment is made. It must be emphasized that this mail is merely a scam, and none of its claims are true.
"I have been watching you" email scam overview
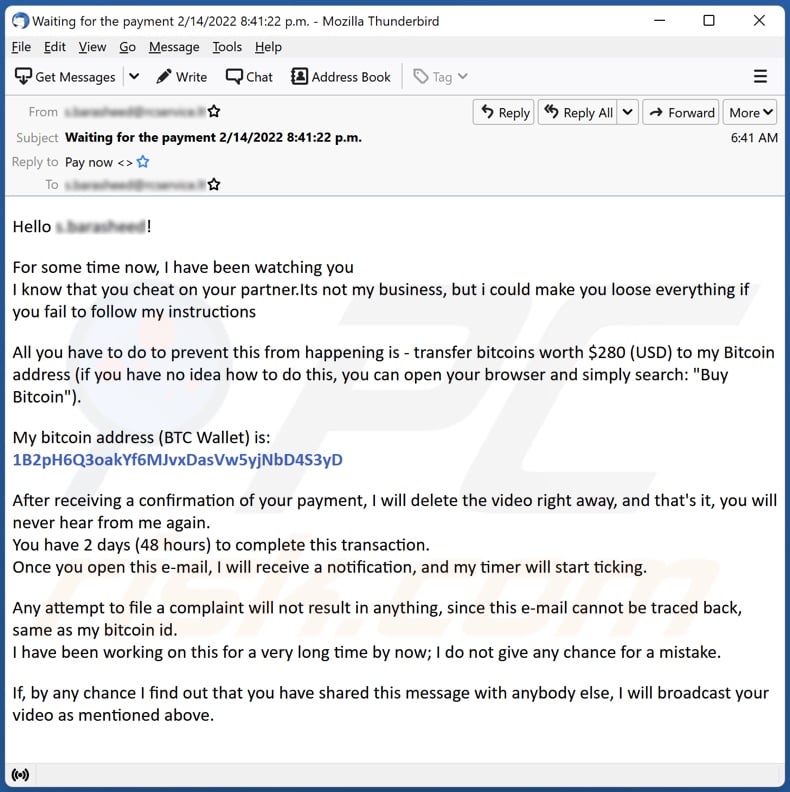
The scam email with the subject "Waiting for the payment ([date] D/MM/YYYY [time] HH/MM/SS)" claims that the recipient has been under surveillance for quite some time. This has allegedly allowed the sender to obtain a video of the recipient cheating on their partner.
The letter demands 280 USD in Bitcoin cryptocurrency for the deletion of the nonexistent recording. The ransom must be paid within two days. Once the transfer is verified, the video will be erased. The email also warns against filling complaints or disclosing the contents of the letter - since the sender is untraceable, and acting against these warnings will result in the recording's publication.
As mentioned in the introduction, the "I have been watching you" email is a scam - meaning that there are no videos featuring the recipient, and all of the threats made by it are empty. We strongly advise recipients of this email to simply ignore it, as it poses no threat whatsoever.
| Name | I have been watching you sextortion email |
| Threat Type | Scam, Social Engineering, Fraud |
| Fake Claim | Video containing proof the recipient's infidelity is in the sender's possession. |
| Ransom Amount | 280 USD in Bitcoin cryptocurrency |
| Cyber Criminal Cryptowallet Addresses | 3DpnEuqUnMv6img2nLZW8nhUQnqLNczBW6, 15Yc5fp7h98SeQ8cKsqjEhnkq1U4oQMsAt, 3HVYoeDCwLgiyWWuBSeoZfYpt4kTCjM9uX, B3QvgttQQsbgboah6NmBKW7NY6y1XCX6jRi, 38oZGzFRT3pBjg8BYzwabU38t87SDJ6hEM, 1BCbQEJN1bHXAsLak9MEZeCvyZGC4N3F3T, bc1qwur3cu4jqgul9xwxc6qrs8yls3rk3y6uyv0gay, bc1qq2zd2mtfeaj7ygmpxvm80cd2krma8kw727kyll, 3PosdxC7wnXfi2GvVDYAGSKSF3XUVoi3tM, 3EQoeB9w9U9QiczVQkYEATqizxysZqHoji, 1LjwoPTNDBYLBWjJdFnvUMezEMHEWJsVrc, bc1qfez4vzwhlmpuf9geqkc2cz7d92l3alanzg75ak, 1D9NgNsdmYXMYbw2z4oxEJvTwx1ut3F7o3, 0x19d7216905992b71661ee43d034b32d3a214a53f, LSsNNMc2SQm9gXrruCnBLuv9XvR2tRwWkc, TGtCAJprpGbJYBEH9nCYLQ9LDmgNoSjqU5, addr1v8q0zs6ecar9crccr6sslmyj5rl29s90ttv3y2r6sw4cgqq23d5ep, 1B2pH6Q3oakYf6MJvxDasVw5yjNbD4S3yD, bc1qpufdmxs884art3jzgeyuh2hlz7a3gknkn3hq93, bc1qwe3agnheqqmf8yjucuunhvmgany5vv2ageg7ux, bc1q97q6laq85g07gu3p5gpxqqaxrv59y7amsnd0u7, 36bk8h1aVnPP6TCdLKkTEQAQEUBeuqHg7f, 3B7jzuZ8EbE6xJ2BtLAZsJvjNZEJpqbmpk, bc1q49g4lpmpm2tdkzd22nyuvhmk45fuy7pcql524h, 0x3f16ced93b23a136cdd4a4f330e75b84e0f512e9, 3QSNQztBoLiQiVuzccBC5Sx3sA1KYDzvk8, 3KBUXeFq7G1LYeFp54CRS5yMHExLgzx3ug, 32bK8ew53L5JDQm4uXv1trnEhKgU7K2ELL, 3HzaCwcSSyWYMQ9CvxAWeJSzAYmY5tGEPF, 36i4csGjfN2PatMze834FM6khurZ5X1udW, bc1qrfg9fav0q0umk666jvu897ceqnx4uhzx99ydz7, bc1qc7uadefgy5qm9pzfxng2cuy4pdgc76qu0v5q5j, bc1qztat090zf2r6ylx9lkm2ht9ndwx7lc02tflmcq, bc1qkvd6d6gytuepd39zuzu5nh2a98ck4u32qs3mnu, bc1q3rjn8jj8x723svxfyyz7k9nkpekh6uml8wd3t3 |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Spam campaigns in general
We have analyzed thousands of spam emails. This mail is commonly used for phishing and various other scams, as well as malware proliferation (e.g., trojans, ransomware, etc.). The scam models can differ drastically, ranging from empty threats to ordinary-looking notifications from genuine entities - however, the end-goal of practically all spam campaigns is to generate revenue for the cyber criminals behind them.
"Start The Conversation With Bad News", "I would like to avoid any accusations against you", and "I am sorry to inform you but your device was hacked" are just a few examples of the sextortion emails that we have researched.
How do spam campaigns infect computers?
Spam emails can have infectious files as attachments. Alternatively, these letters can contain links leading to websites capable of stealthily downloading/installing such files or ones designed to trick users into doing so themselves.
Malicious files can be archives, executables, Microsoft Office and PDF documents, JavaScript, etc. When the files are opened - malware download/installation is triggered.
For example, MS documents opened in pre-2010 Microsoft Office versions immediately initiate infection processes by executing malicious macro commands. Later versions have the "Protected View" mode, and users can manually enable macros (i.e., editing/content). It is noteworthy that virulent documents often contain deceptive messages to trick users into enabling macro commands.
How to avoid installation of malware?
We strongly advise against opening/clicking the attachments and links found in suspicious and irrelevant emails, as that can lead to a system infection. It is also recommended to use Microsoft Office versions released after 2010.
However, malware is not proliferated exclusively through spam mail. Therefore, we also recommend downloading only from official/verified sources and activating/updating software with tools provided by legitimate developers.
It is paramount to have a dependable anti-virus installed and kept updated. Security programs must be used to run regular system scans and to remove detected threats. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "I have been watching you" email letter:
Subject: Waiting for the payment 2/14/2022 8:41:22 p.m.
Hello -!
For some time now, I have been watching you
I know that you cheat on your partner.Its not my business, but i could make you loose everything if you fail to follow my instructions
All you have to do to prevent this from happening is - transfer bitcoins worth $280 (USD) to my Bitcoin address (if you have no idea how to do this, you can open your browser and simply search: "Buy Bitcoin").
My bitcoin address (BTC Wallet) is:
1B2pH6Q3oakYf6MJvxDasVw5yjNbD4S3yD
After receiving a confirmation of your payment, I will delete the video right away, and that's it, you will never hear from me again.
You have 2 days (48 hours) to complete this transaction.
Once you open this e-mail, I will receive a notification, and my timer will start ticking.
Any attempt to file a complaint will not result in anything, since this e-mail cannot be traced back, same as my bitcoin id.
I have been working on this for a very long time by now; I do not give any chance for a mistake.
If, by any chance I find out that you have shared this message with anybody else, I will broadcast your video as mentioned above.
Example of a Spanish variant of "I Have Been Watching You" scam email:
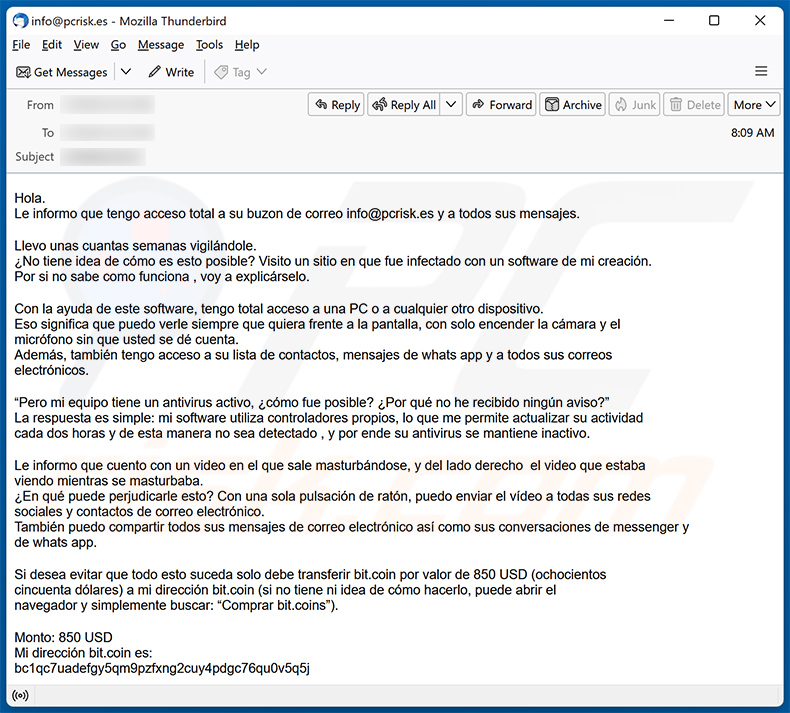
Text presented within:
Hola.
Le informo que tengo acceso total a su buzon de correo - y a todos sus mensajes.Llevo unas cuantas semanas vigilándole.
¿No tiene idea de cómo es esto posible? Visito un sitio en que fue infectado con un software de mi creación.
Por si no sabe como funciona , voy a explicárselo.Con la ayuda de este software, tengo total acceso a una PC o a cualquier otro dispositivo.
Eso significa que puedo verle siempre que quiera frente a la pantalla, con solo encender la cámara y el
micrófono sin que usted se dé cuenta.
Además, también tengo acceso a su lista de contactos, mensajes de whats app y a todos sus correos
electrónicos.“Pero mi equipo tiene un antivirus activo, ¿cómo fue posible? ¿Por qué no he recibido ningún aviso?”
La respuesta es simple: mi software utiliza controladores propios, lo que me permite actualizar su actividad
cada dos horas y de esta manera no sea detectado , y por ende su antivirus se mantiene inactivo.Le informo que cuento con un video en el que sale masturbándose, y del lado derecho el video que estaba
viendo mientras se masturbaba.
¿En qué puede perjudicarle esto? Con una sola pulsación de ratón, puedo enviar el vídeo a todas sus redes
sociales y contactos de correo electrónico.
También puedo compartir todos sus mensajes de correo electrónico así como sus conversaciones de messenger y
de whats app.Si desea evitar que todo esto suceda solo debe transferir bit.coin por valor de 850 USD (ochocientos
cincuenta dólares) a mi dirección bit.coin (si no tiene ni idea de cómo hacerlo, puede abrir el
navegador y simplemente buscar: “Comprar bit.coins”).Monto: 850 USD
Mi dirección bit.coin es:
bc1qc7uadefgy5qm9pzfxng2cuy4pdgc76qu0v5q5jUna vez que yo reciba el aviso de que usted efectuó el pago, borraré el vídeo de inmediato, y se acabó, no
volverá nunca a saber de mí.
Tiene solo dos días (48 horas) para completar esta transacción.
Cuando Usted abra este mensaje de correo, recibiré una notificación y mi temporizador se pondrá en marcha.Presentar una queja o denuncia no le va a servir de nada, ya que este mensaje no puede ser rastreado, al igual
que mi identificador de pagos.
Llevo años dedicándome a esto y creáme.. Nunca cometo errores.Si advierto que ha mostrado este mensaje a cualquier otra persona, distribuiré inmediatamente su vídeo, tal
como se lo he indicado. El tiempo comienza a correr en este momento.
Yet another example of an email from "I Have Been Watching You" spam campaign:
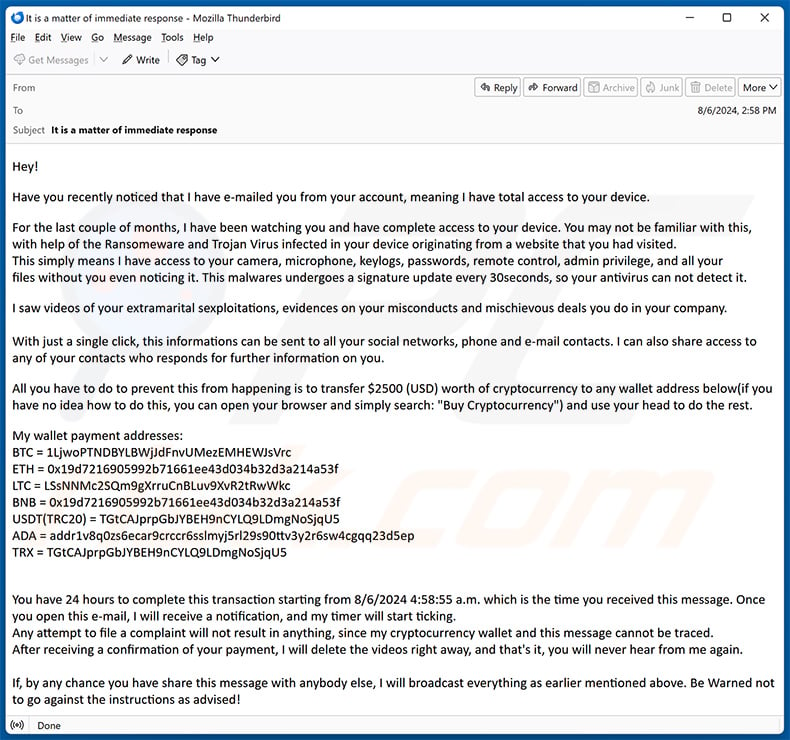
Text presented within:
Subject: It is a matter of immediate response
Hey!
Have you recently noticed that I have e-mailed you from your account, meaning I have total access to your device.
For the last couple of months, I have been watching you and have complete access to your device. You may not be familiar with this, with help of the Ransomeware and Trojan Virus infected in your device originating from a website that you had visited.
This simply means I have access to your camera, microphone, keylogs, passwords, remote control, admin privilege, and all your files without you even noticing it. This malwares undergoes a signature update every 30seconds, so your antivirus can not detect it.I saw videos of your extramarital sexploitations, evidences on your misconducts and mischievous deals you do in your company.
With just a single click, this informations can be sent to all your social networks, phone and e-mail contacts. I can also share access to any of your contacts who responds for further information on you.
All you have to do to prevent this from happening is to transfer $2500 (USD) worth of cryptocurrency to any wallet address below(if you have no idea how to do this, you can open your browser and simply search: "Buy Cryptocurrency") and use your head to do the rest.
My wallet payment addresses:
BTC = 1LjwoPTNDBYLBWjJdFnvUMezEMHEWJsVrc
ETH = 0x19d7216905992b71661ee43d034b32d3a214a53f
LTC = LSsNNMc2SQm9gXrruCnBLuv9XvR2tRwWkc
BNB = 0x19d7216905992b71661ee43d034b32d3a214a53f
USDT(TRC20) = TGtCAJprpGbJYBEH9nCYLQ9LDmgNoSjqU5
ADA = addr1v8q0zs6ecar9crccr6sslmyj5rl29s90ttv3y2r6sw4cgqq23d5ep
TRX = TGtCAJprpGbJYBEH9nCYLQ9LDmgNoSjqU5You have 24 hours to complete this transaction starting from 8/6/2024 4:58:55 a.m. which is the time you received this message. Once you open this e-mail, I will receive a notification, and my timer will start ticking.
Any attempt to file a complaint will not result in anything, since my cryptocurrency wallet and this message cannot be traced.
After receiving a confirmation of your payment, I will delete the videos right away, and that's it, you will never hear from me again.If, by any chance you have share this message with anybody else, I will broadcast everything as earlier mentioned above. Be Warned not to go against the instructions as advised!
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is I have been watching you sextortion email?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal, and thousands of users receive them.
Was my computer actually hacked and does the sender have any information?
No, the claims made by the "I have been watching you" email are fake. Therefore, neither have the scammers infiltrated your devices, nor do they have any compromising videos of you.
How did cyber criminals get my email password?
Your email might have been exposed after a data breach, or you could have fallen victim to a phishing scam (e.g., provided your email password to a phishing website disguised as a sign-in page or similar).
I have sent cryptocurrency to the address presented in this email, can I get my money back?
Cryptocurrency transactions are virtually untraceable, which makes them irreversible. Hence, you will not be able to return the lost funds.
I have provided my personal information when tricked by a spam email, what should I do?
If you have disclosed account credentials - change the passwords of all potentially compromised accounts and inform their official support without delay. And if the provided information was of a different personal nature (e.g., ID card details, credit card numbers, etc.) - immediately contact the relevant authorities.
I have read a spam email but didn't open the attachment, is my computer infected?
No, merely reading a spam email will not trigger any infection processes. Malware download/installation begins when the email attachments or links presented in spam letters - are opened/clicked.
I have downloaded and opened a file attached to a spam email, is my computer infected?
If the opened file was an executable (.exe, .run, etc.) - most likely, yes - your system was infected. However, if it was a document (.doc, .xls, .pdf, etc.) - you might have avoided triggering an infection chain, since these formats can require additional interaction (e.g., enabling macro commands, etc.) to begin downloading/installing malicious software.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner can detect and eliminate most of the known malware infections. It must be stressed that running a complete system scan is vital - as high-end malicious programs typically hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion