Do not trust sextortion emails claiming your devices were broken into via network router
Phishing/ScamAlso Known As: I broke into your computer system using the Wireless network router sextortion email
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "I broke into your computer system using the Wireless network router" email?
After inspecting the "I broke into your computer system using the Wireless network router" email, we determined that it is spam that operates as a sextortion scam.
It must be emphasized that all the claims made by this letter (i.e., possession of an explicit recording featuring the recipient, system infection, data exfiltration, etc.) - are all false. Therefore, these emails pose no actual threat to the recipients.
"I broke into your computer system using the Wireless network router" email scam overview
The scam email states that the recipient's system was hacked "using the Wireless network router" a couple of months ago. Supposedly, the "hacker" exfiltrated data from all of the recipient's devices. Additionally, a recording was made them while they were visiting adult-oriented websites.
Unless 1400 USD in Bitcoin cryptocurrency are paid within three days, the sexually explicit video (which does not exist) will be sent to the recipient's contacts (e.g., email, social networking, messengers, etc.). Furthermore, the stolen data will be leaked online.
The sender claims to be untraceable; hence, the recipient is told not to contact law enforcement or perform other actions like changing their passwords - as that will not amount to anything.
As mentioned in the introduction, all the information provided by this email is fake. Therefore, neither were the devices infiltrated nor infected by the sender, their data was not stolen, and no compromising recordings exist. The "I broke into your computer system using the Wireless network router" email must simply be ignored, as its threats are empty.
| Name | I broke into your computer system using the Wireless network router sextortion email |
| Threat Type | Sextortion, Scam, Social Engineering, Fraud |
| Fake Claim | Recipient's devices were infected and used to record explicit videos (featuring the recipient), and sensitive data stolen. |
| Ransom Amount | 1400 USD in Bitcoin cryptocurrency |
| Cyber Criminal Cryptowallet Addresses | bc1qhnc03qcjh8u98ydkanwz3h39s9cqunje96jlw3, bc1qpv6lnzsjrkjuqhwv6wpn32kndf6pze8hznunfk, bc1ql3jcgq847g6fpjlp3klrccu7qkh99lzyz6x4q5 |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Monetary loss |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Sextortion scam email examples
We have analyzed dozens of emails akin to "I broke into your computer system using the Wireless network router"; "E-mail To You From An Account Of Yours", "Your system has been hacked with a Trojan virus", "I have been watching you" - are just a couple of examples.
Spam mail is commonly used for various scams (e.g., sextortion, phishing, etc.) and even malware proliferation. These letters can make varied claims and use the names/logos of legitimate entities - to gain and subsequently abuse users' trust.
How do spam campaigns infect computers?
Spam emails are often employed to distribute malware. They can have infectious files attached to them or contain links leading to malicious websites designed to stealthily download/install malware or trick users into doing so. Virulent files can be archives (ZIP, RAR, etc.), executables (.exe, .run, etc.), Microsoft Office and PDF documents, JavaScript, and so on.
Once such a file is opened, the infection process is triggered. It is noteworthy that some document formats may require additional user interaction to begin downloading/installing malware. For example, Microsoft Office documents cause infections by executing malicious macro commands.
How to avoid installation of malware?
We strongly advise exercising caution with incoming mail. The attachments and links present in suspicious emails and messages - must not be opened, as they can contain malware. Additionally, it is important to use Microsoft Office versions released after 2010 since they have the "Protected View" mode, which prevents automatic execution of macro commands.
However, malware is not spread just via spam mail. Therefore, we also recommend downloading only from official/verified sources and activating/updating software with tools provided by legitimate developers (illegal activation tools "cracks" and fake updates can cause system infections).
We must stress the importance of having a reputable anti-virus installed and kept updated. Security programs must be used to perform regular system scans and to remove threats and issues. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
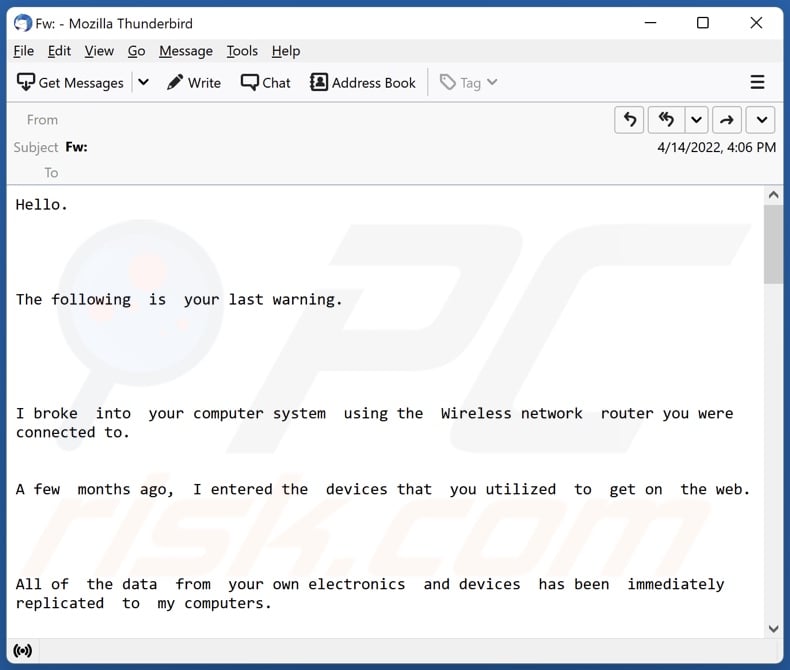
Text presented in the "I broke into your computer system using the Wireless network router" email letter:
Hello.
The following is your last warning. I broke into your computer system using the Wireless network router you were connected to.
A few months ago, I entered the devices that you utilized to get on the web.
All of the data from your own electronics and devices has been immediately replicated to my computers.
I get access to all your mobile device messengers, social networks, e-mails, chat history, and list of contacts.
My malware constantly updates its signatures (driver based), therefore it remains unnoticeable to anti-virus software. I guess right now you fully grasp, exactly why I stayed unnoticed right until todayWhilst collecting data in regards to you, I found you're a big fan of mature web pages & even more. You actually like to stop by adult sites and watch dirty videos whilst having an orgasm. I have actually made a cam capturing videos of you jerking off. The editing of the video you're seeing at the same time and your self pleasure. Your own happy face is clearly seeable. I don't think this type of information would-be really good for your reputation. I can send this footage out to everyone who know your identity.
I additionally have no trouble with making all your private info open to public through the web. I think you know exactly what I'm talking about.
It may be a huge disaster for you.
I am able to wreck your life for a long time. I suspect that you definitely don't want this to occur.
Let's fix it in such a manner: you transfer me 1400 $ (usd) using btc equivalent at the moment of financial transaction), and i'll right away remove all your data from my servers.
After that, we will ignore one another.
My btc payment address for transaction: bc1qhnc03qcjh8u98ydkanwz3h39s9cqunje96jlw3
Should you not realize how to transfer finances and exactly what Bitcoin is. Simply type in the google search engine "purchase Bitcoin". I present you with 3 days to send me the funds. The time started monitoring automatically once you opened the message. I'll see a notification once this e-mail is open. Don't try and search for aid, as the wallet address cannot be traced, email the note came from and can't be traced also & created automatically, hence there's no point in messaging me. Do not try to make contact with the law enforcement and other protection solutions, and if so, your own info will be revealed. Switching security passwords in social networks, email, and gadgets isn't going to help you, since all the information has already been saved to my servers. Good luck and try to not do something foolish. Give some thought to your forthcoming future.
Appearance of the "I broke into your computer system using the Wireless network router" email (GIF):
Examples of other emails from the same spam campaign:
Example 1:
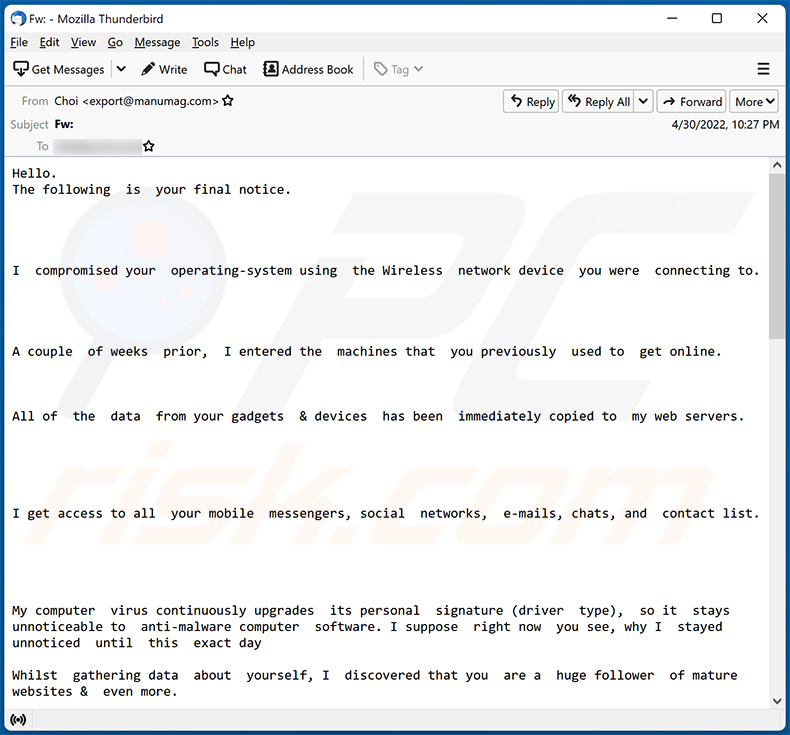
Text presented within:
Hello.
The following is your final notice.I compromised your operating-system using the Wireless network device you were connecting to.
A couple of weeks prior, I entered the machines that you previously used to get online.
All of the data from your gadgets & devices has been immediately copied to my web servers.
I get access to all your mobile messengers, social networks, e-mails, chats, and contact list.
My computer virus continuously upgrades its personal signature (driver type), so it stays unnoticeable to anti-malware computer software. I suppose right now you see, why I stayed unnoticed until this exact dayWhilst gathering data about yourself, I discovered that you are a huge follower of mature websites & even more.
You actually love to go to mature websites and view kinky vids while having an ejaculation.
I've actually made a web camera capturing videos of you jacking off. The croping and editing of the clip you're watching at that moment and your masturbation. Your own face is clearly visible. I do not think this sort of information would be really good for your personal reputation.
I can now forward this video footage to everybody who know your identity.
I additionally have no problem with making all your private data open to public on line. I do believe you realize what i am talking about.
It'll be a true problem for you personally.
I can mess up your daily life for a long time.
I think that you definitely don't want this to occur.Why don't we resolve it in this manner: you send me 1400 $ (dollars) thru Bitcoin equivalent at the time of payment), and I will right away get rid of all of your info from my servers. Following that, we will disregard each other.
My btc address for transfering: bc1q2kn4x3rurxkg6uzl9y48ky3js5c0nwptl9a6z7
If you don't know how to send finances & what exactly Bitcoin is. Then type in the Google "Buy btc".I provide you with 2 days to send me money.
The timer started monitoring automatically as soon as you opened up the message.I will see a message once this e-mail is exposed. Do not try and search help, as the wallet address cannot be monitored, address the message is originating from & can not be tracked also and created digitally, therefore there isn't any point in writing to me.
Do not make an attempt to get hold of the police & other protection solutions, & if you do, your personal info will undoubtedly be revealed. Switching passwords online in social media sites, e-mail, and gadgets will not help you, as all the information has already been saved to my web servers.
All the best and do not do anything dumb. Carefully consider your own future.
Example 2:
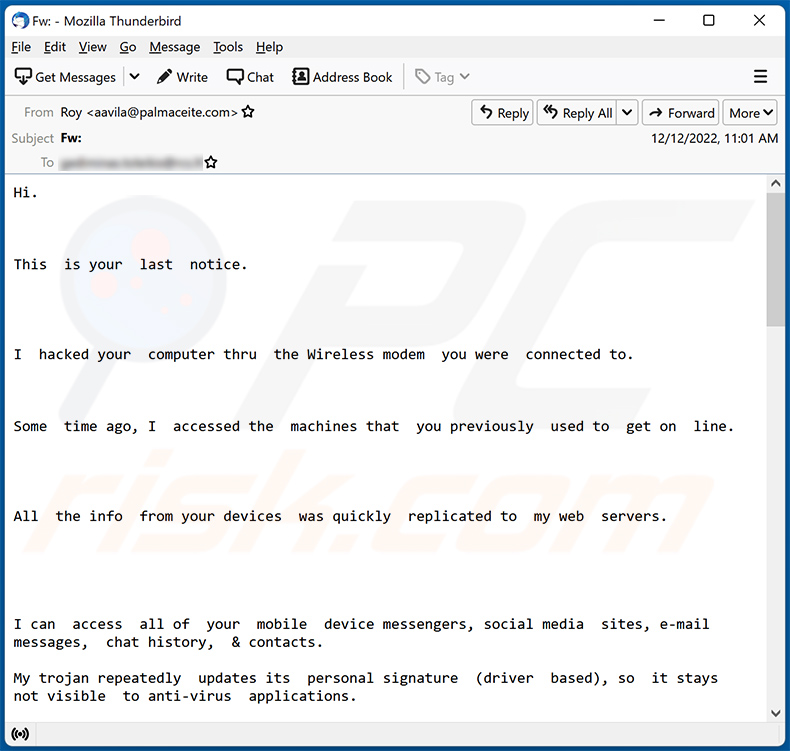
Text presented within:
Hi.
This is your last notice.I hacked your computer thru the Wireless modem you were connected to.
Some time ago, I accessed the machines that you previously used to get on line.
All the info from your devices was quickly replicated to my web servers.
I can access all of your mobile device messengers, social media sites, e-mail messages, chat history, & contacts.
My trojan repeatedly updates its personal signature (driver based), so it stays not visible to anti-virus applications.
I imagine at this point you understand, why I remained unseen until this present day
While gathering infos about yourself, I discovered that you are a big follower of porn web sites & more.
You truly prefer to stop by porn web sites and look at filthy video clips whilst having an ejaculation. I've surely created a web camera shooting videos of you jacking off.
A montage of the video you're watching at the time & your masturbation. Your own face is clearly seeable. I do not think this kind of material will be good for your profile.
I can send this video to everybody who know who you are.
I in addition have no problem with rendering all of your personal information open to public in cyberspace.
I think you know exactly what I mean.It could be an absolute disaster for you.
I am able to mess up your life forever.
I really think you really do not need this to occur.
Why don't we solve it this way: you transfer me 1300 $ (US dollars) thru btc equivalent at the moment of exchange), & i'll right away remove all of your data from my web servers.And then, we will just disregard each other.
My bitcoin address for transaction: bc1ql3jcgq847g6fpjlp3klrccu7qkh99lzyz6x4q5Should you not realize how to transfer cash and what exactly btc is. Simply type in the Google "Buy Bitcoin".
I give you two business days to send me money. The timer started counting instantly after you opened this letter.
I'll see a message when this e-mail is opened.
Don't attempt to search for aid, as the wallet address cannot be traced, address the letter is originating from & cannot be traced also and created digitally, hence there is no point in texting me. Don't make an attempt to reach out to the authorities and some other security solutions, and if you do, your personal data will be published.
Switching passwords online in social media sites, email, & devices isn't going to help you, since all the information has already been downloaded to my hosting space.
All the best & avoid doing something stupid. Think of your future.
Example 3:
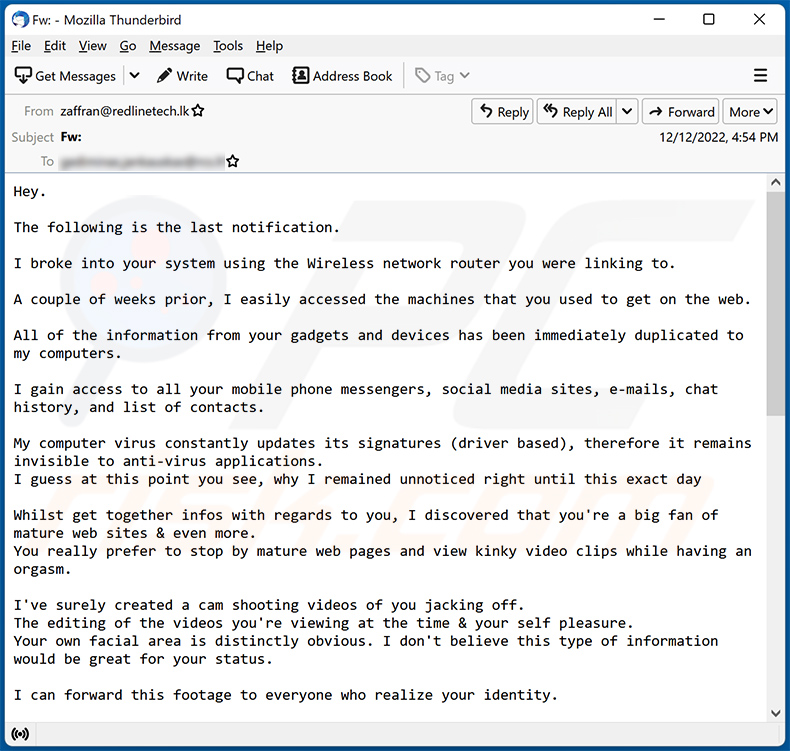
Text presented within:
Hey.
The following is the last notification.
I broke into your system using the Wireless network router you were linking to.
A couple of weeks prior, I easily accessed the machines that you used to get on the web.
All of the information from your gadgets and devices has been immediately duplicated to my computers.
I gain access to all your mobile phone messengers, social media sites, e-mails, chat history, and list of contacts.
My computer virus constantly updates its signatures (driver based), therefore it remains invisible to anti-virus applications.
I guess at this point you see, why I remained unnoticed right until this exact dayWhilst get together infos with regards to you, I discovered that you're a big fan of mature web sites & even more.
You really prefer to stop by mature web pages and view kinky video clips while having an orgasm.I've surely created a cam shooting videos of you jacking off.
The editing of the videos you're viewing at the time & your self pleasure.
Your own facial area is distinctly obvious. I don't believe this type of information would be great for your status.I can forward this footage to everyone who realize your identity.
I in addition have no trouble with making all your discreet information public via the internet.
I believe you realize what I mean.It would be a true frustration for you.
I'm able to wreck your life for a long time.
I really feel you definitely don't want this to take place.
Now let's fix it that way: you send me 1500 $ (dollars) thru btc equivalent at the time of payment), & I will immediately remove all of your information from my web servers.
Proceeding that, we will just disregard one another.My bitcoin wallet address for transaction: bc1qpv6lnzsjrkjuqhwv6wpn32kndf6pze8hznunfk
If you do not understand how to send cash and exactly what btc is. Simply key in the Search engines like google "purchase Bitcoin".
I give you 3 business days to transfer money.
The time launched monitoring instantly after you read the letter.
I will get a warning the minute this e-mail is opened.Do not attempt to seek out aid, as the wallet can not be monitored, email the letter came from & can not be followed either and created digitally, so there is no point in texting me.
Don't make an attempt to get hold of the police & other security solutions, and should you choose to do, your personal info will undoubtedly be posted.Switching online passwords in social networking sites, e mail, and devices isn't going to help you, since all the data has already been downloaded to my servers.
Good-luck and don't do anything dumb. Think of your foreseeable future.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is I broke into your computer system using the Wireless network router sextortion email?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal. Cyber criminals distribute them in mass-scale operations; hence, thousands of users receive identical letters.
Was my computer actually hacked and does the sender have any information?
No, all the claims made by the "I broke into your computer system using the Wireless network router" email - are fake. Therefore, your devices have not been infected or otherwise compromised, and no recordings of you or other personal data - exist in the scammers' possession. This email poses no threat and must simply be ignored.
How did cyber criminals get my email password?
Your email might have been compromised through a phishing scam (e.g., a fake email requesting you to re-login and address some issue, a hoax registration/submission form that had to be filled for a service or a reward, etc.). The less likely scenario is that your email was exposed due to a data breach of a service/platform that you use.
I have sent cryptocurrency to the address presented in this email, can I get my money back?
No, since cryptocurrency transactions are virtually untraceable - they are irreversible.
I have provided my personal information when tricked by a spam email, what should I do?
If you have disclosed account credentials - change the passwords of all potentially compromised accounts and inform their official support without delay. If the provided information was of a different personal nature (e.g., ID card details, credit card numbers, etc.) - immediately contact the corresponding authorities.
I have read a spam email but didn't open the attachment, is my computer infected?
No, merely opening a spam email will not trigger any system infection processes. They are jumpstarted when the attachments or links present in these emails - are opened/clicked.
I have downloaded and opened a file attached to a spam email, is my computer infected?
Whether your system was infected may depend on the file's format. If it was an executable - most likely, yes - your device was infected. However, you might have avoided initiating malware download/installation processes if it was a document (.doc, .xls, .pdf, etc.). These files may require more interaction (e.g., enabling macro commands) to begin infection processes.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner can detect and eliminate almost all known malware infections. It has to be mentioned that high-end malicious programs tend to hide deep within systems - therefore, performing a full system scan is paramount.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion