Avoid getting scammed by emails claiming you have a McAfee subscription
Phishing/ScamAlso Known As: Payment For McAfee Subscription spam email
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of email is "Payment For McAfee Subscription"?
"Payment For McAfee Subscription" is the name of an email spam campaign. The letters can be plain or quite elaborate, but they all refer to purchases or renewals of the McAfee anti-virus.
It must be emphasized that these emails are fake, and they are not associated with the actual McAfee Corp. This spam mail aims to trick recipients into phoning the provided telephone numbers - thus pulling them into a callback scam.
"Payment For McAfee Subscription" email scam overview
We have analyzed five emails that are part of the "Payment For McAfee Subscription" campaign, but way more variants are likely. These letters vary in design; some are in plain text - while others are formatted and contain McAfee's logo or other associated graphics.
The message within the emails differs, but the common through-line is that the recipient is being billed for a product/service from McAfee, and if they wish to cancel or have any questions - they are to call the provided number. As mentioned in the introduction, these letters are fake and not associated with actual McAfee company.
Spam mail of this kind operates as a callback scam. Like all scams, this type is designed to generate revenue for the scammers. However, how they achieve this goal can differ drastically. These criminals either do so by obtaining sensitive information, having the victim make bogus monetary transactions, or by infecting their devices with malware. When on call, the scammers pretend to be support or technicians, but they can follow different scenarios.
When targeting data, cyber criminals can request the victims to disclose or enter it into a phishing website/file, or extract it with malware. Information of interest can include: personally identifiable details (e.g., names, ages, addresses, occupations, etc.), log-in credentials (e.g., online banking, e-commerce, email, social networking, and various other accounts), and finance-related details (e.g., bank account numbers, credit card details, etc.).
These schemes often incorporate requests for the user to allow the "support"/"technician" to remotely access their device (with the use of AnyDesk, TeamViewer, UltraViewer, etc.). This is an element of refund and tech support scams.
In the former, the victim is asked to sign into their online bank account, and the screen is then darkened on the user's end while they are supposed to enter the refund sum. The scammers claim that an error occurred during the transaction, and a significantly larger amount was transferred.
The deceit is carried out by either moving the victim's funds between accounts (e.g., from savings to checking) or by editing the website's HTML. Whatever the method, it creates the appearance of a considerably larger sum having been transferred. Note that neither of the techniques actually affects the funds within the account. The criminal then begs for the excess to be returned.
In technical support scams, the scammers pretend to run diagnostics, find viruses or "connected hackers", perform bogus malware removal processes, etc. The fees for these fake services tend to be exorbitant.
Furthermore, while connected to the victim's computer, the criminals can remove genuine security tools, install fake anti-viruses, steal data, or infect the system with malware (e.g., trojans, ransomware, etc.).
Computers can also be infected without using remote access, e.g., by criminals tricking users into visiting malware-proliferating websites that can either stealthily infiltrate software or lure visitors into downloading/installing it themselves.
Scammers typically ask for money to be transferred using difficult/impossible to trace methods, such as cryptocurrencies, gift cards, pre-paid vouchers, cash hidden in packages and shipped, etc.
Regardless of how a callback scam operates, victims of them can experience multiple system infections, data loss, severe privacy issues, significant financial losses, and identity theft.
If you have allowed cyber criminals to remotely access your device, you must first disconnect it from the Internet. Afterward, uninstall the remote access software the criminals used (as they may not need your consent to reconnect). And lastly, run a full system scan with a reputable anti-virus and remove all detected threats.
If you believe that your log-in credentials have been exposed, we advise you to change the passwords of all potentially affected accounts and contact their official support. And if you suspect that other vulnerable data has been compromised (e.g., ID card details, credit card numbers, etc.) - immediately contact the appropriate authorities.
| Name | Payment For McAfee Subscription spam email |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Recipient is being billed for a McAfee product/subscription |
| Disguise | McAfee |
| Scammer Phone Number(s) | +1 (805) 827-0666, +1 (828) 782-7324, +1(888) 390-5761, +1 877 371 2385, +1 818 293 8028, +1 (877) 260-7792, +1 (847) 794-8021, +1 (833) 882-4208, +1(888)-405-4401, (888) 246-2390, +1 (888) 306-1173, +1 (805)-354-1797, (888) 404-4624, (888) 986-9208, 320-566-9101, +1(830-267-4097), 877-374-2075, 808-468-8860, 855-522-4401, 833-469-4751, +1-740-247-0459, 888-278-1649, +1 (805)-(960)-(5349), 843-888-7720, (888) 988-6921, 808-320-6786, 855-708-1312, 844-407-4215, +1 (808) 229-4068, +1 866 201 9479, +1 (843) 291-5838 |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Spam campaigns in general
We have inspected thousands of spam emails; "Mail Server Update Scam", "Annual Email Version Upgrade", "BRITISH CAMELOT ONLINE LOTTERY", "YоuTubе Suppоrt Shared An Item", "Concept Design Drawings" - are just some of our latest finds.
In addition to phishing and various scams, these letters are used to distribute malware. Spam letters are usually disguised as "important", "urgent", "priority", etc.; they can even be presented as messages from legitimate companies, service providers, organizations, institutions, and other entities.
Due to how widespread this deceptive and dangerous mail is, we highly recommend exercising caution with incoming emails, PMs/DMs, SMSes, and other messages.
How do spam campaigns infect computers?
Spam emails can have infectious files attached to or linked inside them. These files can be Microsoft Office and PDF documents, archives (RAR, ZIP, etc.), executables (.exe, .run, etc.), JavaScript, and so on.
When a virulent file is executed, run, or otherwise opened - the infection chain (i.e., malware download/installation) is triggered. For example, Microsoft Office documents infect systems by executing malicious macro commands.
How to avoid installation of malware?
We strongly advise against opening the attachments or links present in suspicious emails and messages, as they can be malicious and cause infections.
However, malware is not proliferated exclusively via spam mail. Therefore, we also recommend being cautious while browsing since fraudulent and hazardous content usually appears legitimate and harmless. Another recommendation is to download from official/verified channels and activate/update programs using legitimate functions or tools.
We must stress the importance of having a dependable anti-virus installed and kept up-to-date. Security software must be used to run regular system scans and to remove detected threats/issues. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
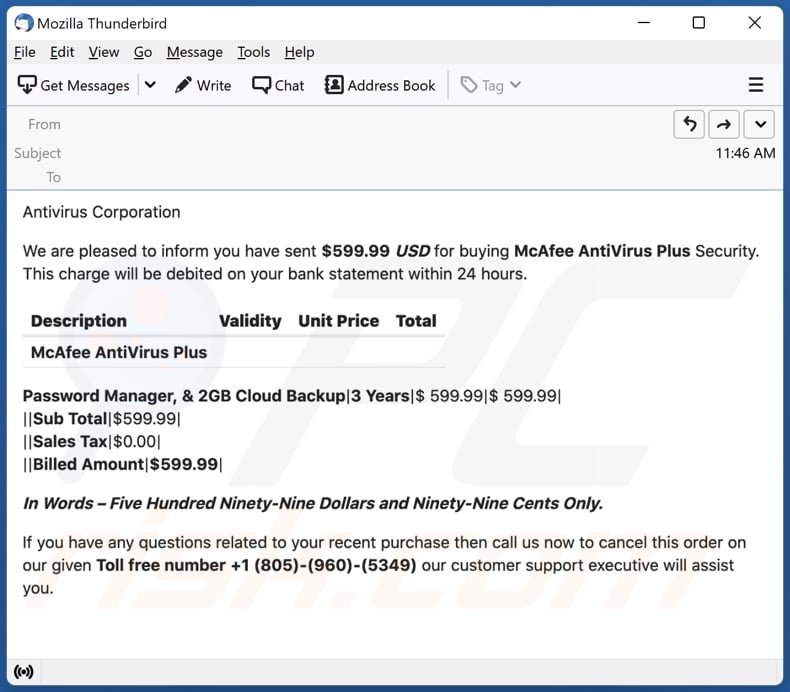
Text presented in a variant of the "Payment For McAfee Subscription" email letter:
Antivirus Corporation
We are pleased to inform you have sent $599.99 USD for buying McAfee AntiVirus Plus Security. This charge will be debited on your bank statement within 24 hours.
Description Validity Unit Price Total
McAfee AntiVirus Plus
Password Manager, & 2GB Cloud Backup|3 Years|$ 599.99|$ 599.99|
||Sub Total|$599.99|
||Sales Tax|$0.00|
||Billed Amount|$599.99|
In Words – Five Hundred Ninety-Nine Dollars and Ninety-Nine Cents Only.
If you have any questions related to your recent purchase then call us now to cancel this order on our given Toll free number +1 (805)-(960)-(5349) our customer support executive will assist you.
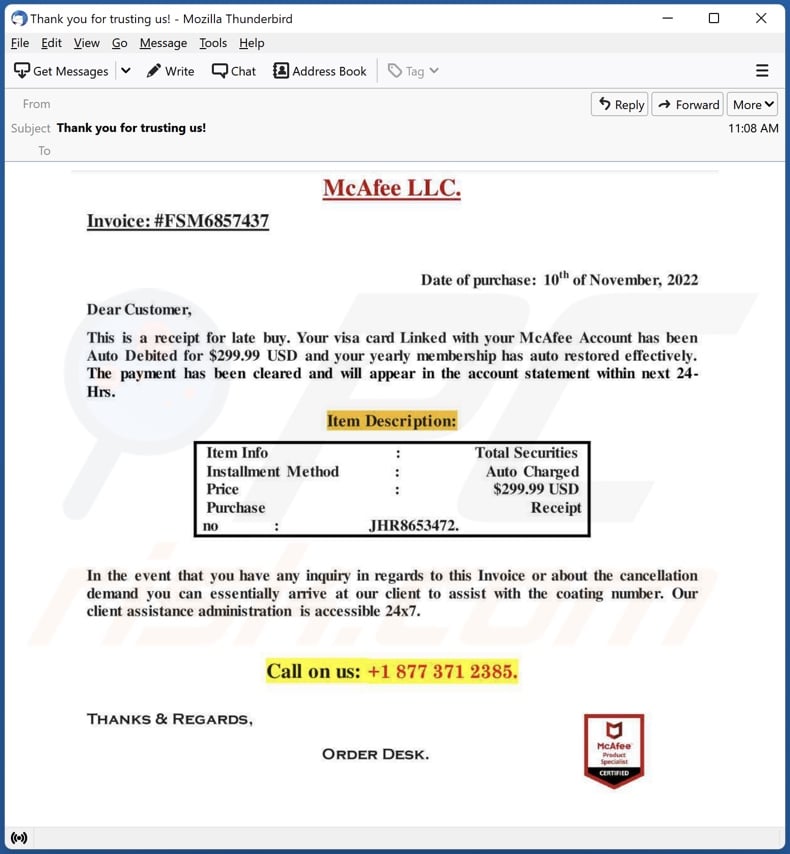
Screenshot of another "Payment For McAfee Subscription" spam email variant:
Text presented in this variant:
Subject: Thank you for trusting us!
McAfee LLC.
Invoice: #FSM6857437
Date of purchase: 10th of November, 2022
Dear Customer,
This is a receipt for late buy. Your visa card Linked with your McAfee Account has been Auto Debited for $299.99 USD and your yearly membership has auto restored effectively. The payment has been cleared and will appear in the account statement within next 24-Hrs.
Item Description:
Item Info: Total Securities
Installment Method : Auto Charged
Price : $299.99 USD
Purchase Receipt
no : JHR8653472
In the event that you have any inquiry in regards to this Invoice or about the cancellation demand you can essentially arrive at our client to assist with the coating number. Our client assistance administration is accessible 24x7.
Call on us: +1 877 371 2385
Thanks & Regards,
Order Desk.
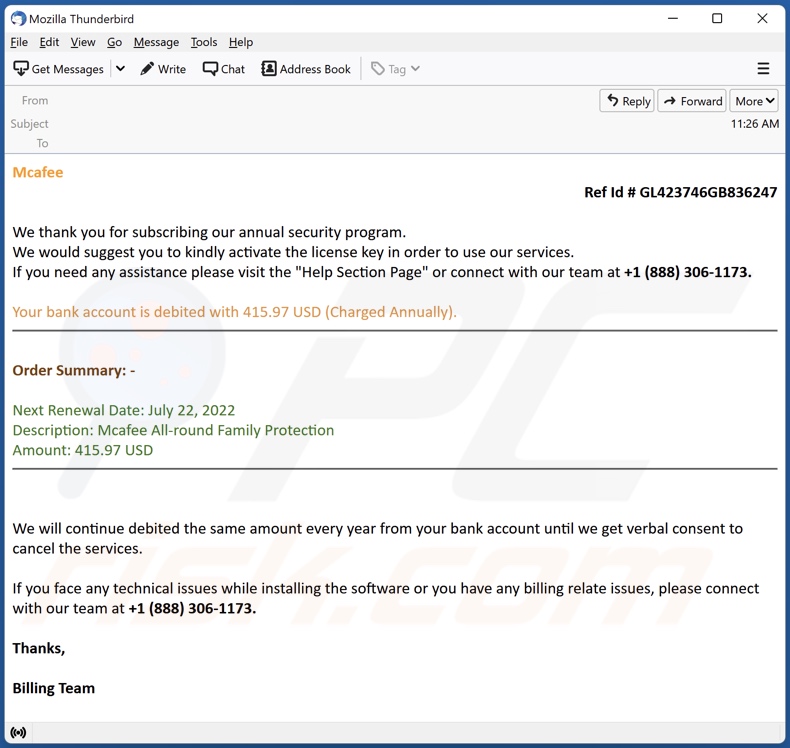
Screenshot of another "Payment For McAfee Subscription" spam email variant:
Text presented in this variant:
Mcafee
Ref Id # GL423746GB836247
We thank you for subscribing our annual security program.
We would suggest you to kindly activate the license key in order to use our services.
If you need any assistance please visit the "Help Section Page" or connect with our team at +1 (888) 306-1173.
Your bank account is debited with 415.97 USD (Charged Annually).
Order Summary: -
Next Renewal Date: July 22, 2022
Description: Mcafee All-round Family Protection
Amount: 415.97 USD
We will continue debited the same amount every year from your bank account until we get verbal consent to cancel the services.
If you face any technical issues while installing the software or you have any billing relate issues, please connect with our team at +1 (888) 306-1173.
Thanks,
Billing Team
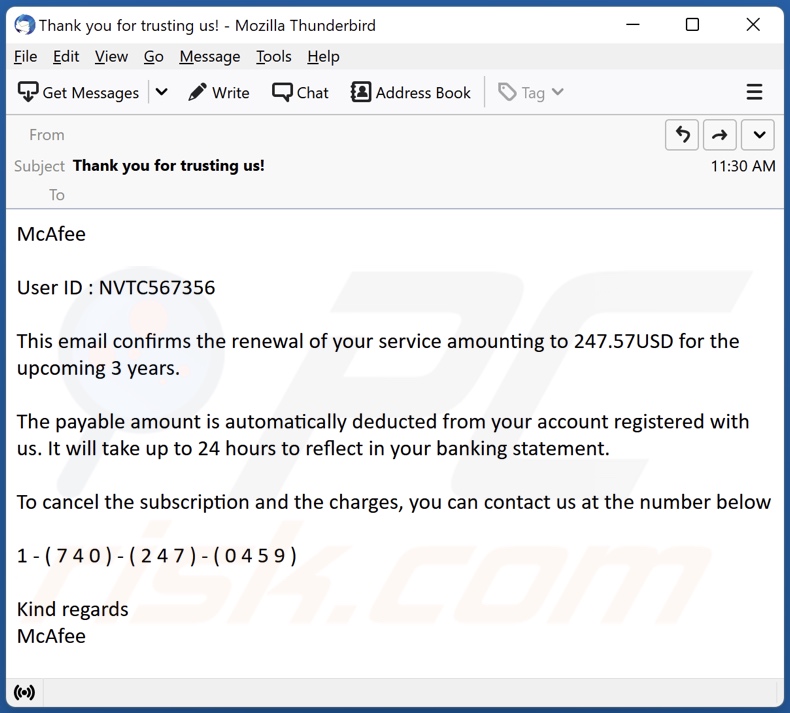
Screenshot of another "Payment For McAfee Subscription" spam email variant:
Text presented in this variant:
Subject: Thank you for trusting us!
McAfee
User ID : NVTC567356
This email confirms the renewal of your service amounting to 247.57USD for the upcoming 3 years.
The payable amount is automatically deducted from your account registered with us. It will take up to 24 hours to reflect in your banking statement.
To cancel the subscription and the charges, you can contact us at the number below
1 - ( 7 4 0 ) - ( 2 4 7 ) - ( 0 4 5 9 )
Kind regards
McAfee
Screenshot of another "Payment For McAfee Subscription" spam email variant:
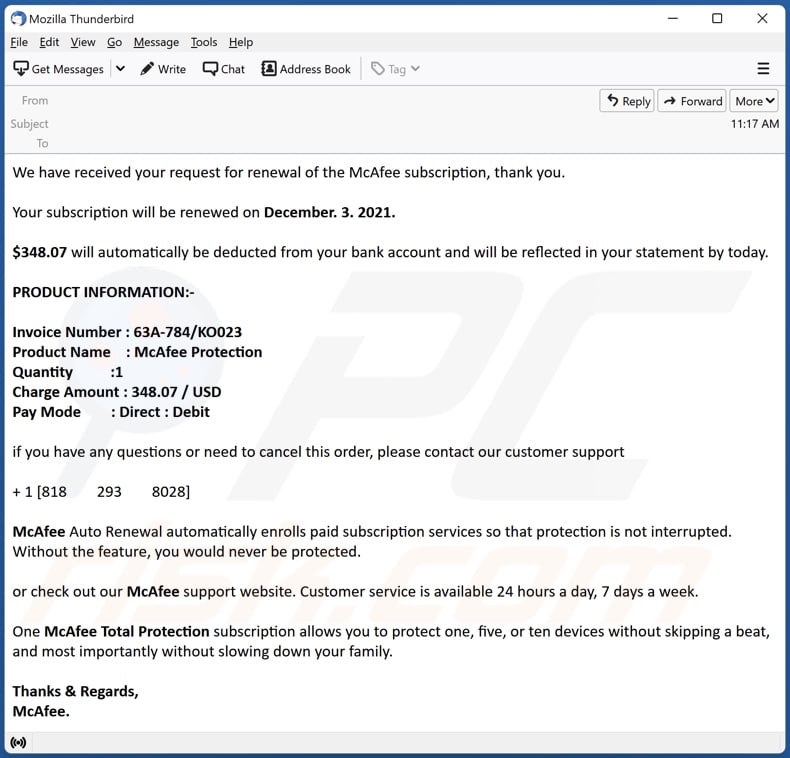
Text presented in this variant:
We have received your request for renewal of the McAfee subscription, thank you.
Your subscription will be renewed on December. 3. 2021.
$348.07 will automatically be deducted from your bank account and will be reflected in your statement by today.
PRODUCT INFORMATION:-
Invoice Number : 63A-784/KO023
Product Name : McAfee Protection
Quantity :1
Charge Amount : 348.07 / USD
Pay Mode : Direct : Debit
if you have any questions or need to cancel this order, please contact our customer support
+ 1 [818 293 8028]
McAfee Auto Renewal automatically enrolls paid subscription services so that protection is not interrupted. Without the feature, you would never be protected.
or check out our McAfee support website. Customer service is available 24 hours a day, 7 days a week.
One McAfee Total Protection subscription allows you to protect one, five, or ten devices without skipping a beat, and most importantly without slowing down your family.
Thanks & Regards,
McAfee.
Yet another example of an email from the "Payment For McAfee Subscription" spam campaign:
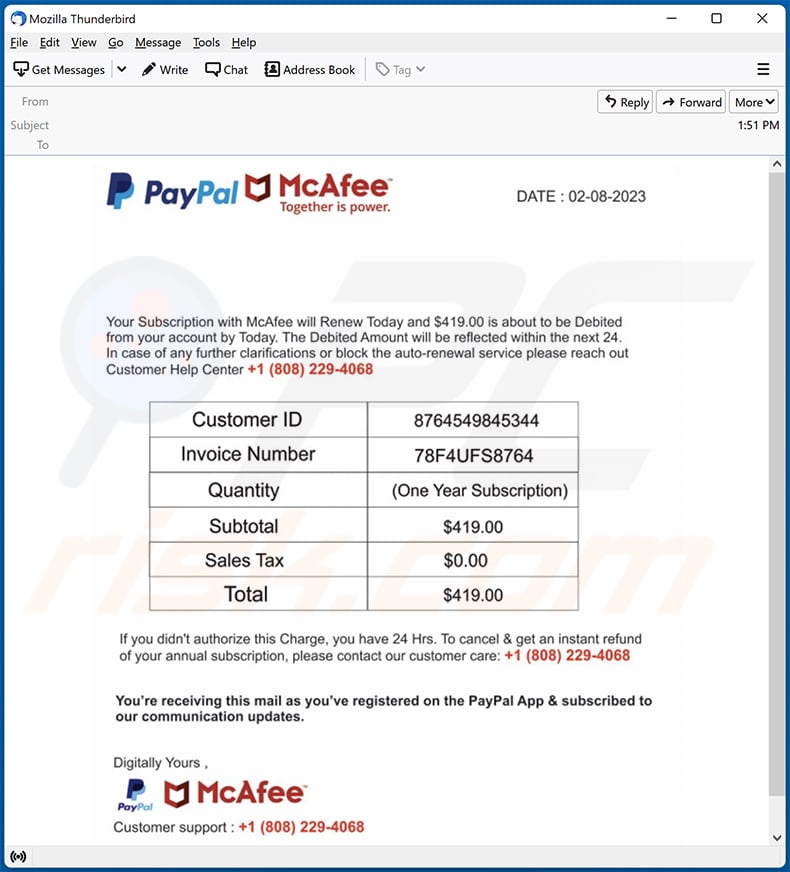
Text presented within:
PayPal McAfee Together is power
DATE : 02-08-2023Your Subscription With McAfee will Renew Today and $419.00 is about to be Debited from your account by Today. The Debited Amount will be reflected within the next 24. In case of any further clarifications or block the auto-renewal service please reach out Customer Help Center +1 (808) 229-4068
Customer ID 8764549845344
Invoice Number 78F4UFS8764
Quantity (One Year Subscription)
Subtotal $419.00
Sales Tax $0.00
Total $419.00If you didn't authorize this Charge, you have 24 Hrs. To cancel & get an instant refund of your annual subscription, please contact our customer care: +1 (808) 229-4068
You're receiving this mail as you've registered on the PayPal App & subscribed to our communication updates.
Digitally Yours ,
PayPal McAfee
Customer support : +1 (808) 229-4068
Another example of a McAfee subscription renewal-themed spam email:
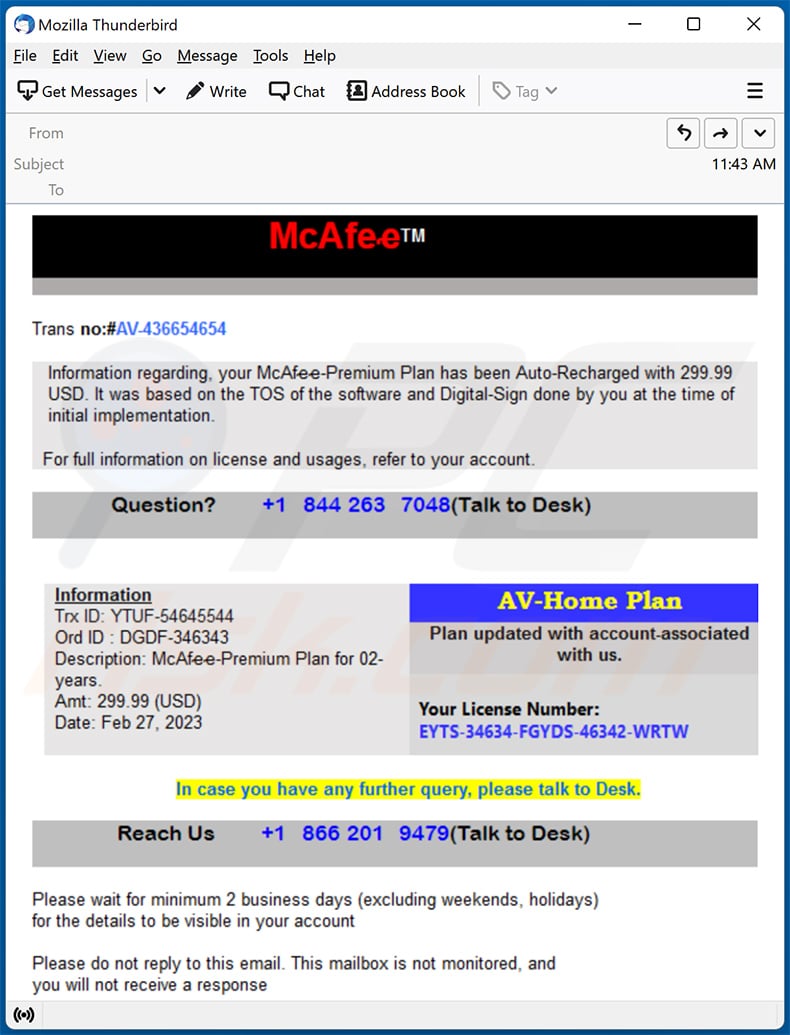
Text presented within:
McAfee
Trans no:#AV-436654654
Information regarding, your McAf-e-e-Premium Plan Has been Auto-Recharged with 299.99 USD. It was based on the TOS of the software and DIgital-Sign done by you at the time of initial implementation.
For full information on license and usages, refer to your account.
Question? +1 844 263 7048(Talk to Desk)
Information
Trx ID: YTUF-54645544
Ord ID : DGDF-346343
Description: McAf-e-e-Premium Plan for 02-years.
Amt: 299.99 (USD)
Date: Feb 27, 2023
AV-Home Plan
Plan updated with account-associated with us.
Your License Number:
EYTS-34634-FGYDS-46342-WRTWIn case you have any further query, please talk to Desk.
Reach Us +1 866 201 9479(Talk to Desk)
Please wait for minimum 2 business days (excluding weekends, holidays) for the details to be visible in your account.
Please do not reply to this email. This mailbox is not monitored, and you will not receive a response
Yet another example of a McAfee subscription renewal-themed spam email:
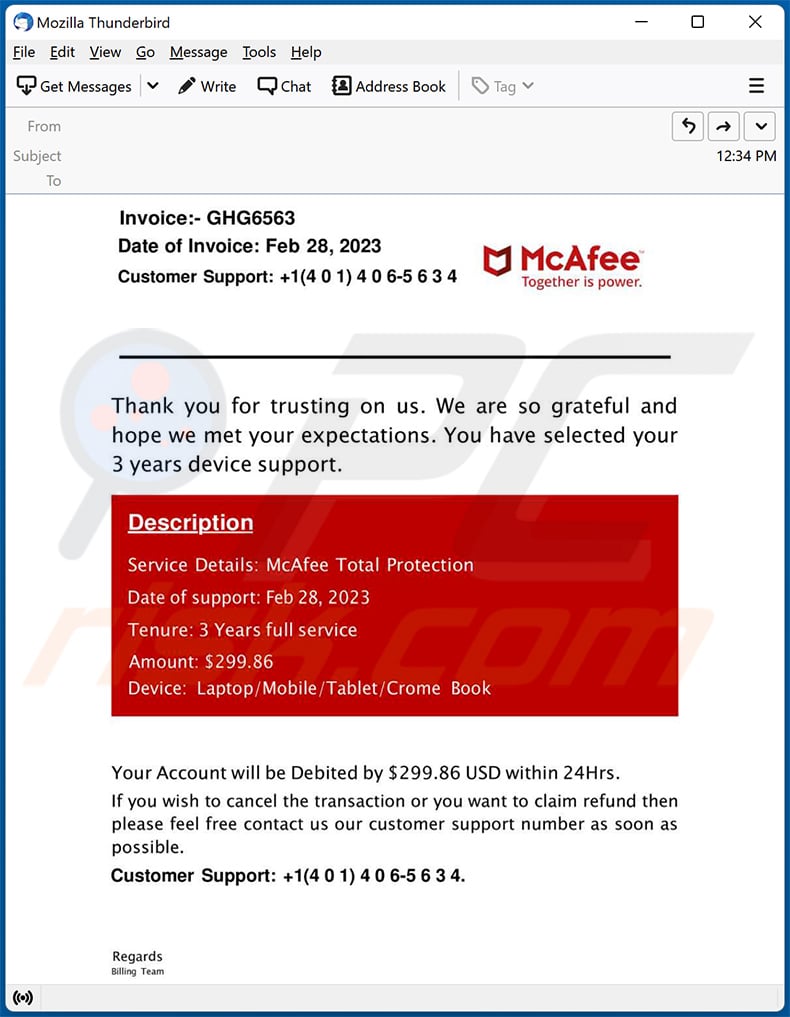
Text presented within:
Invoice:- GHG6563
Date of Invoice: Feb 28, 2023
Customer Support: +1(4 0 1) 4 0 6-5 6 3 4
McAfee
Together is power.Thank you for trusting on us. We are so grateful and hope we met your expectations. You have selected your 3 years device support.
Description
Service Details: McAfee Total Protection
Date of support: Feb 28, 2023
Tenure: 3 Years full service
Amount: $299.86
Device: Laptop/Mobile/Tablet/Crome BookYour Account will be Debited by $299.86 USD within 24Hrs.
If you wish to cancel the transaction or you want to claim refund then please feel free to contact us our customer support number as soon as possible.
Customer Support: +1(4 0 1) 4 0 6-5 6 3 4Regards
Billing Team
Yet another example of an email from "Payment For McAfee Subscription" spam campaign:
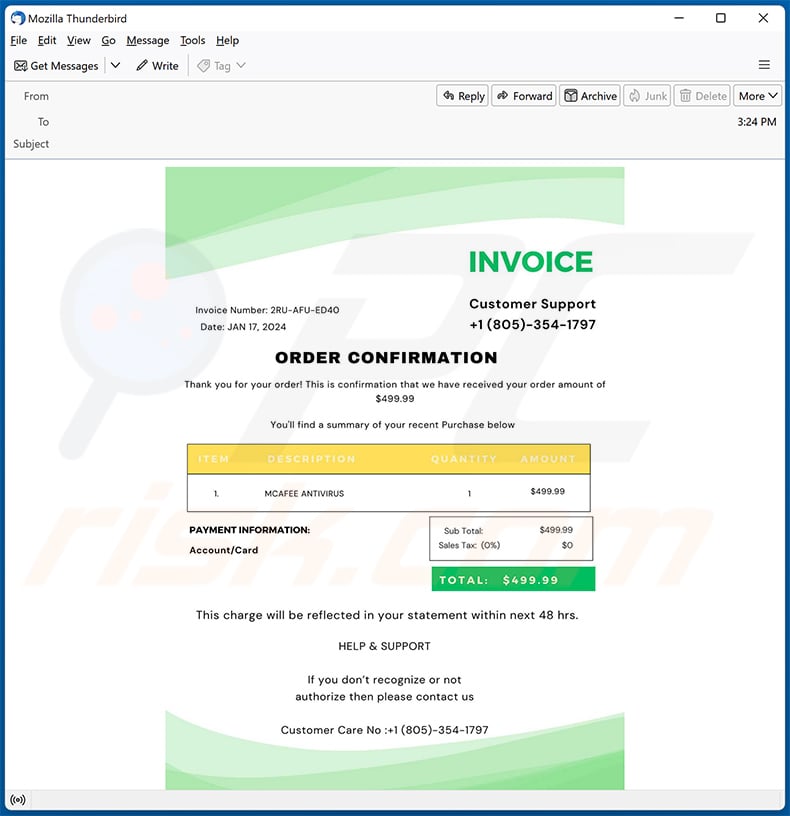
Text presented within:
INVOICE
Invoice Number: 2RU-AFU-ED40
Date: JAN 17, 2024Customer Support
+1 (805)-354-1797ORDER CONFIRMATION
Thank you for your order! This is confirmation that we have received your order amount of $499.99You'll find a summary of your recent Purchase blow
Item Description Quantity Amount
1 MCAFEE ANTIVIRUS 1 $499.99
Sub Total: $499.99
Sales Tax: (0%) $0
TOTAL: $499.99
PAYMENT INFORMATION:
Account/Card
This charge will be reflected in your statement within next 48 hrs.HELP & SUPPORT
If you don't recognize or not authorize then please contact us
Customer Care No :+1 (805)-354-1797
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Payment For McAfee Subscription spam email?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal. This mail is distributed in massive operations - therefore, thousands of users receive identical letters.
I have provided my personal information when tricked by a spam email, what should I do?
If you've disclosed account credentials - change the passwords of all possibly compromised accounts and inform their official support. And if you have revealed other private information (e.g., ID card details, passport scans, credit card details, etc.) - immediately contact the corresponding authorities.
I have allowed cyber criminals to remotely access my computer, what should I do?
If you have permitted cyber criminals to access your device remotely, you must disconnect it from the Internet. Afterwards, remove the remote access program (e.g., AnyDesk, UltraViewer, TeamViewer, etc.) that the criminals used. The last step is to run a full system scan with an anti-virus and use it to remove all threats.
I have read a spam email but didn't open the attachment, is my computer infected?
No, merely reading an email will not trigger any system infection processes. Devices are compromised when the attachments/links found in spam mail are opened/clicked.
I have downloaded and opened a file attached to a spam email, is my computer infected?
Whether your device was infected might depend on the opened file's format. If it was an executable (.exe, .run, etc.) - most likely, yes - the system was infected. However, you might have avoided it if the file was a document (.doc, .xls, .pdf, etc.). These formats may require additional actions (e.g., enabling macro commands) to start downloading/installing malware.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner is designed to detect and eliminate threats. It is capable of removing most of the known malware infections. However, it must be stressed that performing a full system scan is crucial since high-end malicious programs usually hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion