Do not trust "Professional Hacker Managed To Hack Your Operating System" email
Phishing/ScamAlso Known As: "Professional Hacker Managed To Hack Your Operating System" sextortion email
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of email is "Professional Hacker Managed To Hack Your Operating System"?
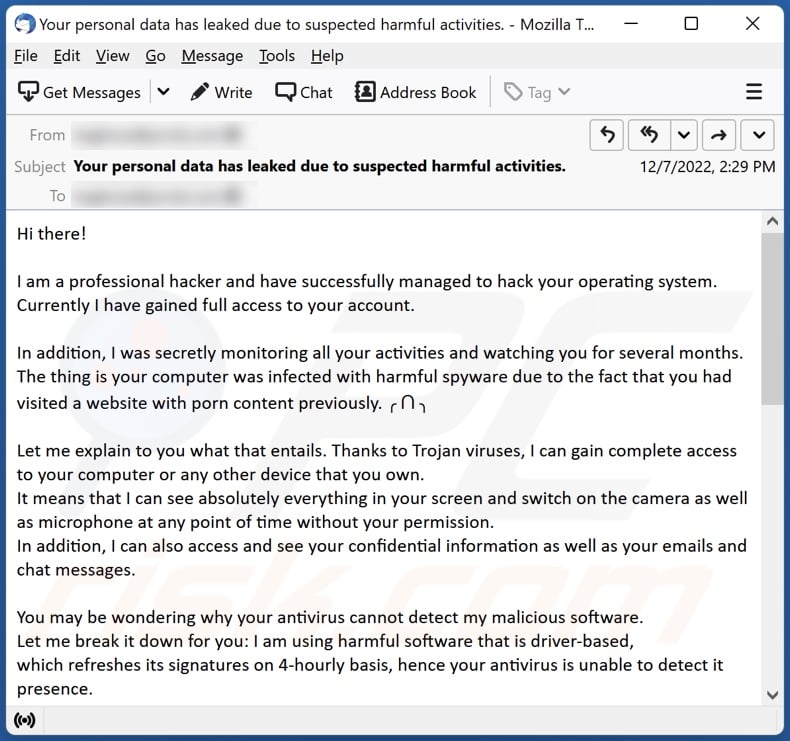
After inspecting the "Professional Hacker Managed To Hack Your Operating System" email and its German language equivalent - we determined that this mail is spam.
These letters operate as sextortion scams. They make false claims about the recipients' devices being infected with malware and subsequently used to obtain compromising recordings and other private content. The fake emails demand payment under threat of the explicit content being leaked.
It must be emphasized that all the claims made by this mail are false and pose no danger to the recipients.
"Professional Hacker Managed To Hack Your Operating System" email scam overview
The emails with the subjects "Your personal data has leaked due to suspected harmful activities." and "Ihre persönlichen Daten sind wegen des Verdachts auf schädliche Aktivitäten nach außen gelangt." (subjects may vary) inform recipients that all their devices have been infected with malware by a professional hacker.
Supposedly, the cyber criminal used the compromised machines to monitor the user for several months. Furthermore, the non-existent malicious software was used to record explicit videos while the recipient was visiting websites hosting adult-oriented content. The spam letters also claim that the fake malware was used to extract email and messenger contacts and histories.
The recipient is given 50 hours to transfer 850 USD or 1750 EUR in Bitcoin cryptocurrency to the scammer - else the explicit recordings will be sent to their contacts. Additionally, the allegedly exfiltrated emails and chat histories will be publicized. The recipient is warned that if they disclose the contents of the spam email – the outcome will be the same as if they'd refused to pay.
As mentioned in the introduction, all the claims made by the "Professional Hacker Managed To Hack Your Operating System" emails are false. Therefore, recipients' devices were not infected, their data was not stolen, nor was any compromising recording ever made by the sender.
If you have already paid the scammers, you will not be able to return your funds. Cryptocurrency transactions are virtually untraceable – hence, they are practically irreversible.
| Name | "Professional Hacker Managed To Hack Your Operating System" sextortion email |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Hacker has infected the recipient's devices and then used them make explicit recordings, which will be leaked unless a ransom is paid. |
| Ransom Amount | 850 USD or 1750 EUR in Bitcoin cryptocurrency |
| Cyber Criminal Cryptowallet Addresses | 1QBybsYTttsWrY5B2HnGGURHufeHYEKKf9, 1BXNuQZQFDNoPjvncpkUBVxPZmwbQtK8g7, 14fok5BvdSjZRY5qn11Twt9r6NXVtGCYV8, bc1qzxzazuz7twfx4e0mzfg97606d5dytksue9j3ag, 1N6TYc2FFJmjMDPnAKQgjRh65ou58EfQNM, bc1qz3hct7u9x6tfh4guk3e7wyjaxa2gnalzfgr3kh, bc1qmmupyfp50cfas5j4ptw846m7h80a6v3n0ta6cz, bc1qsqz048pdk3y408j39vepwujvkjpyvl03kjuf0q, 12nEVuGNtRFMVjeVmLtD4nt2sHX68S47yH, bc1q2vw5zwhkc8nyfp8t0je8smyxwlakf8ug59pra7, 1Er1bTsfVpy2uZ88hBDJf1i66SuYxQCRKb, 1FVL5uejtneDHSm9Md7xtUuXxvBJhz3hHs, 15ypvac98Ta8UD7kZHF5MGSwdfeZ5NHEqu, 1LqSNBE9rcvypxXF8fiBE88YenJsRfvsEZ, 1HBiRxpSxekVND1Rqwqh1gbUKeZiYBsDkt, bc1qqsc5afd0ayrk64uwrhrzx56rngxng5mzrsucge, 19AEV6b6SMVTByErnpaQUDCUWK5cN8gYqh , 1Jv4gYRkCiDQqBQvdmDW9c2Dqwg1pYfn6y, 1LZQP5zXfx1VSPFiLvtc5p5yhjsLg9m6xR, 1AsRkzQSorZAc66fdXof9NHTNJdU4T8nC8, 16rGyggURQvJw6RMwigDVzEGjjoCC5fZFP, 1CRJGomhCirQGNUVwjCC8uNRwA5AWDZafd, 1GyYujUxs2eJpECpYu3Ns6F4RvZqsp8NT6, 1GdVKgGS8iXeSSrynTfHyDugrpchwVDmdZ, 1NEV8SZ5PocCEBs5Q3oXx8mF7KHfYi2BtD, 1ChY91KYRAabrs9635MPYR3ArByVJTSTdo, 18JafCUSR3JWJuxbSH9Wp4AUizzTwkZz9D, 1CBf6dHegKyWSUeXS4e7cRTxEcuBKsyxCm, 1MSafx9aRzRybiqgGJnH1Ah4EJz5usuSxy, 16cX1KRRPc56LuZrWFJPXLLvrr8m4DVPrS, 1BtfPsKpk13fReZsTkVotBffkS63eN6L8p, 19eXNvqfdK7w8NVX1Db5o6GBYR1tcpWTKv, 15NCWERN56DQNf4WiPLR2txgiEF2np5Q2g, bc1qt5nafws3r2frra4z3jxcqnpumth0gxdrcl7pkn, 175REuUqdgsPFEkWjQ8RfzXi24j1BetV9H, 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg, 1KZnEyumPFBVNK7jdedYL5XwaCLNW3G5Ty, 18Qrf4hEeUL6zNHwuBiWVQYb1GefwnVAfZ, 1BYiyvoNDA7RDmKew7Fo4CNcXQkoUATEqZ |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Sextortion spam campaigns examples
We have inspected thousands of spam emails; "Porn Websites I Attacked With My Virus Xploit", "I Know That You Cheat On Your Partner", "Some Bad News That You Are About To Hear" - are merely a few examples of ones used for sextortion.
Deceptive letters are employed to facilitate a variety of scams including phishing, and they are used to distribute trojans, ransomware, and other malware. These emails can make various claims, and they can even be disguised as messages from legitimate service providers, companies, corporations, organizations, institutions, authorities, and other entities.
How do spam campaigns infect computers?
Spam emails can contain virulent files in the form of attachments or download links. These files can be in various formats, e.g., executables, archives, PDF and Microsoft Office documents, JavaScript, etc.
When an infectious file is executed, run, or otherwise opened – the malware download/installation chain is triggered. For example, Microsoft Office documents infect devices by executing malicious macro commands.
How to avoid installation of malware?
We strongly recommend exercising caution with incoming emails, PMs/DMs, SMSes, and other messages. The attachments and links found in suspicious/irrelevant mail must not be opened - since that can lead to a system infection. Another recommendation is to use Microsoft Office versions released after 2010, as they have the "Protected View" mode that prevents automatic macro execution.
However, malware is not spread exclusively via spam mail. Hence, we advise downloading only from official and trustworthy channels. Additionally, all programs must be activated and updated using functions/tools provided by genuine developers, as illegal activation "cracking" tools and third-party updaters can contain malware.
It is essential to be careful while browsing since fraudulent and malicious online content typically appears legitimate and harmless.
We must stress the importance of having a reputable anti-virus installed and kept up-to-date. Security software must be used to perform regular system scans and to remove threats/issues. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "Professional Hacker Managed To Hack Your Operating System" spam email's English variant:
Subject: Your personal data has leaked due to suspected harmful activities.
Hi there!
I am a professional hacker and have successfully managed to hack your operating system.
Currently I have gained full access to your account.
In addition, I was secretly monitoring all your activities and watching you for several months.
The thing is your computer was infected with harmful spyware due to the fact that you had visited a website with porn content previously. ╭ ᑎ ╮
Let me explain to you what that entails. Thanks to Trojan viruses, I can gain complete access to your computer or any other device that you own.
It means that I can see absolutely everything in your screen and switch on the camera as well as microphone at any point of time without your permission.
In addition, I can also access and see your confidential information as well as your emails and chat messages.
You may be wondering why your antivirus cannot detect my malicious software.
Let me break it down for you: I am using harmful software that is driver-based,
which refreshes its signatures on 4-hourly basis, hence your antivirus is unable to detect it presence.
I have made a video compilation, which shows on the left side the scenes of you happily masturbating,
while on the right side it demonstrates the video you were watching at that moment..ᵔ.ᵔ
All I need is just to share this video to all email addresses and messenger contacts of people you are in communication with on your device or PC.
Furthermore, I can also make public all your emails and chat history.
I believe you would definitely want to avoid this from happening.
Here is what you need to do - transfer the Bitcoin equivalent of 850 USD to my Bitcoin account
(that is rather a simple process, which you can check out online in case if you don't know how to do that).
Below is my bitcoin account information (Bitcoin wallet): 12nEVuGNtRFMVjeVmLtD4nt2sHX68S47yH
Once the required amount is transferred to my account, I will proceed with deleting all those videos and disappear from your life once and for all.
Kindly ensure you complete the abovementioned transfer within 50 hours (2 days +).
I will receive a notification right after you open this email, hence the countdown will start.
Trust me, I am very careful, calculative and never make mistakes.
If I discover that you shared this message with others, I will straight away proceed with making your private videos public.
Good luck!
Screenshot of the "Professional Hacker Managed To Hack Your Operating System" email's German variant:
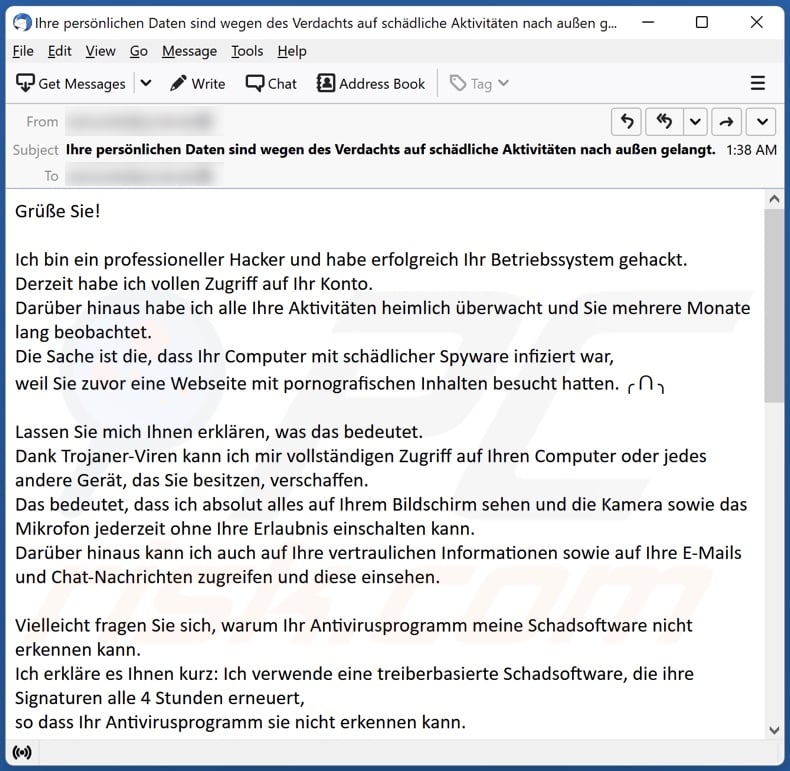
Text presented in this variant:
Subject: Ihre persönlichen Daten sind wegen des Verdachts auf schädliche Aktivitäten nach außen gelangt.
Grüße Sie!
Ich bin ein professioneller Hacker und habe erfolgreich Ihr Betriebssystem gehackt.
Derzeit habe ich vollen Zugriff auf Ihr Konto.
Darüber hinaus habe ich alle Ihre Aktivitäten heimlich überwacht und Sie mehrere Monate lang beobachtet.
Die Sache ist die, dass Ihr Computer mit schädlicher Spyware infiziert war,
weil Sie zuvor eine Webseite mit pornografischen Inhalten besucht hatten. ╭ ᑎ ╮
Lassen Sie mich Ihnen erklären, was das bedeutet.
Dank Trojaner-Viren kann ich mir vollständigen Zugriff auf Ihren Computer oder jedes andere Gerät, das Sie besitzen, verschaffen.
Das bedeutet, dass ich absolut alles auf Ihrem Bildschirm sehen und die Kamera sowie das Mikrofon jederzeit ohne Ihre Erlaubnis einschalten kann.
Darüber hinaus kann ich auch auf Ihre vertraulichen Informationen sowie auf Ihre E-Mails und Chat-Nachrichten zugreifen und diese einsehen.
Vielleicht fragen Sie sich, warum Ihr Antivirusprogramm meine Schadsoftware nicht erkennen kann.
Ich erkläre es Ihnen kurz: Ich verwende eine treiberbasierte Schadsoftware, die ihre Signaturen alle 4 Stunden erneuert,
so dass Ihr Antivirusprogramm sie nicht erkennen kann.
Ich habe eine Videozusammenstellung erstellt, die auf der linken Seite die Szenen zeigt,
in denen Sie fröhlich masturbieren, während auf der rechten Seite das Video gezeigt wird, das Sie sich in diesem Moment angesehen haben...ᵔ.ᵔ
Alles, was ich tun muss, ist, dieses Video an alle E-Mail-Adressen und Messenger-Kontakte von Personen weiterzugeben,
mit denen Sie auf Ihrem Gerät oder PC in Kontakt stehen. Darüber hinaus kann ich auch alle Ihre E-Mails und Chatverläufe veröffentlichen.
Ich denke, dass Sie dies auf jeden Fall vermeiden möchten.
Sie müssen daher Folgendes tun: Überweisen Sie Bitcoin im Gegenwert von 1750€ auf mein Bitcoin-Konto
(das ist ein ziemlich einfacher Vorgang, den Sie online nachlesen können, falls Sie nicht wissen, wie das geht).
Im Folgenden finden Sie die Informationen zu meinem Bitcoin-Konto (Bitcoin-Wallet): 1Er1bTsfVpy2uZ88hBDJf1i66SuYxQCRKb
Sobald der erforderliche Betrag auf meinem Konto eingegangen ist,
werde ich all diese Videos löschen und ein für alle Mal aus Ihrem Leben verschwinden.
Bitte stellen Sie sicher, dass Sie die oben genannte Überweisung innerhalb von 50 Stunden (2 Tage +) durchführen.
Ich werde eine Benachrichtigung erhalten, sobald Sie diese E-Mail öffnen, und der Countdown beginnt.
Glauben Sie mir, ich bin sehr vorsichtig, berechnend und mache nie Fehler.
Sollte ich feststellen, dass Sie diese Nachricht an andere weitergegeben haben, werde ich sofort damit beginnen, Ihre privaten Videos öffentlich zu machen.
Viel Glück! ⍣
Yet another German variant of an email from "Professional Hacker Managed To Hack Your Operating System" spam campaign:
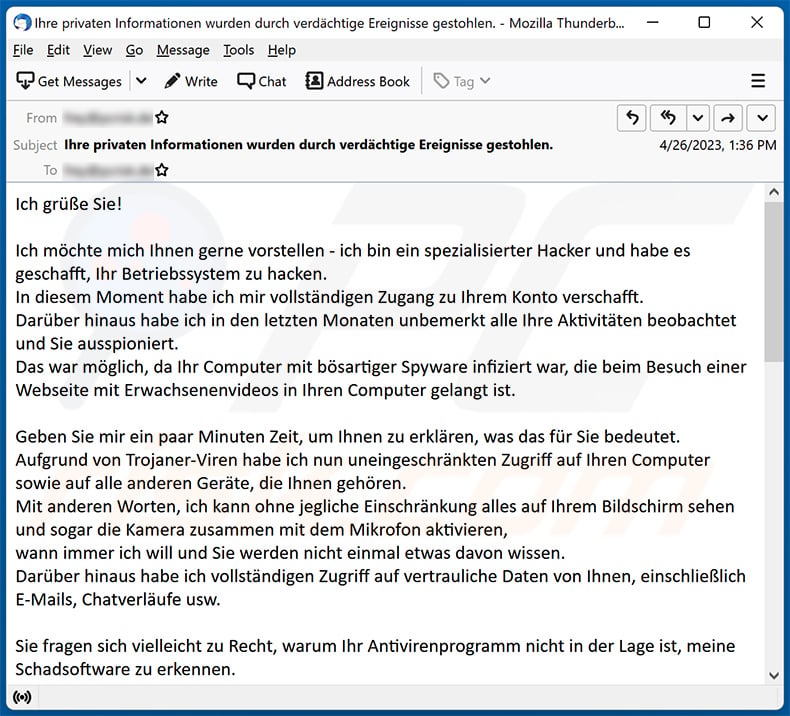
Text presented within:
Subject: Ihre privaten Informationen wurden durch verdächtige Ereignisse gestohlen.
Ich grüße Sie!
Ich möchte mich Ihnen gerne vorstellen - ich bin ein spezialisierter Hacker und habe es geschafft, Ihr Betriebssystem zu hacken.
In diesem Moment habe ich mir vollständigen Zugang zu Ihrem Konto verschafft.
Darüber hinaus habe ich in den letzten Monaten unbemerkt alle Ihre Aktivitäten beobachtet und Sie ausspioniert.
Das war möglich, da Ihr Computer mit bösartiger Spyware infiziert war, die beim Besuch einer Webseite mit Erwachsenenvideos in Ihren Computer gelangt ist.Geben Sie mir ein paar Minuten Zeit, um Ihnen zu erklären, was das für Sie bedeutet.
Aufgrund von Trojaner-Viren habe ich nun uneingeschränkten Zugriff auf Ihren Computer sowie auf alle anderen Geräte, die Ihnen gehören.
Mit anderen Worten, ich kann ohne jegliche Einschränkung alles auf Ihrem Bildschirm sehen und sogar die Kamera zusammen mit dem Mikrofon aktivieren,
wann immer ich will und Sie werden nicht einmal etwas davon wissen.
Darüber hinaus habe ich vollständigen Zugriff auf vertrauliche Daten von Ihnen, einschließlich E-Mails, Chatverläufe usw.Sie fragen sich vielleicht zu Recht, warum Ihr Antivirenprogramm nicht in der Lage ist, meine Schadsoftware zu erkennen.
Das kann ich Ihnen gerne erklären: Meine Schadsoftware ist treiberbasiert und aktualisiert daher alle 4 Stunden ihre Signaturen,
was es Ihrem Antivirusprogramm unmöglich macht, sie zu erkennen.Ich habe mir ein Video ausgedacht, das auf der linken Seite die Szenen Ihrer leidenschaftlichen Masturbationssitzungen zeigt,
während auf der rechten Seite die schmutzigen Videos zu sehen sind, die Sie sich in dieser Zeit angesehen haben.ᵔ.ᵔGlauben Sie mir, es sind nur ein paar Mausklicks nötig,
um dieses Video an Ihre gesamte E-Mail-Adressenliste sowie an Ihre Messenger-Kontakte auf Ihrem PC oder anderen Geräten weiterzuleiten.
Darüber hinaus kann ich alle Ihre E-Mails und Chatverläufe auch für die Öffentlichkeit freigeben.Ich denke, dass Sie das sicher nicht zulassen möchten.
In diesem Fall gibt es eine Lösung für Sie - überweisen Sie 1650 EUR in Bitcoin auf mein Bitcoin-Konto (das ist wirklich nicht schwer,
und Sie können im Internet eine Schritt-für-Schritt-Anleitung finden, falls Sie keine Ahnung davon haben).Die Details meines Bitcoin-Kontos finden Sie weiter unten (Bitcoin-Wallet): 1ChY91KYRAabrs9635MPYR3ArByVJTSTdo
Sobald der oben genannte Betrag auf meinem Konto eingegangen ist,
werde ich sofort alle perversen Videos löschen und vollständig aus Ihrem Leben verschwinden.
Bitte begleichen Sie diese Zahlung innerhalb von 50 Stunden (2 Tagen).
Sobald diese E-Mail geöffnet wird, erhalte ich eine Benachrichtigung, mit der der Countdown gestartet wird.Glauben Sie mir, ich bin sehr vorsichtig, professionell und mache keine Fehler.
Wenn ich erfahre, dass Sie diese Nachricht an jemand anderen weitergeben, werde ich Ihre privaten Videos sofort öffentlich machen.Ich wünsche Ihnen viel Glück!
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "Professional Hacker Managed To Hack Your Operating System" sextortion email?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal. These letters are distributed in massive operations – therefore, thousands of users receive identical ones.
Was my computer actually hacked and does the sender have any information?
No, the email in question is fake. Hence, your devices were not infected, your information was not compromised, nor did the sender make any explicit footage featuring you.
How did cyber criminals get my email password?
Your email could have been obtained through a phishing scam. They are commonly (but not exclusively) promoted via spam mail; these schemes can involve either data-recording websites or files disguised as email account sign-in webpages, registration/subscription forms, and so forth. It is quite unlikely but possible that the email was acquired through a data breach.
I have sent cryptocurrency to the address presented in this email, can I get my money back?
No, cryptocurrency transactions are practically untraceable - thus irreversible.
I have provided my personal information when tricked by a spam email, what should I do?
If you have provided your account credentials (or suspect that they have been compromised) – immediately change the passwords of all potentially exposed accounts and inform their official support. And if you've disclosed other private data (e.g., ID card details, credit card numbers, etc.) - contact the corresponding authorities without delay.
I have read a spam email but didn't open the attachment, is my computer infected?
No, opening/reading an email is harmless. Systems are infected when malicious attachments or links present in spam mail are opened/clicked.
I have downloaded and opened a file attached to a spam email, is my computer infected?
Whether an infection is jumpstarted might depend on the opened file's format. To elaborate, executables (.exe, .run, etc.) infect devices almost without fail when they are opened. While document formats (.doc, .xls, .pdf, etc.) might require additional user interaction (e.g., enabling macro commands) to start downloading/installing malware.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner is designed to detect and remove threats. It can eliminate nearly all known malware infections. However, it must be mentioned that running a complete system scan is crucial - since high-end malicious software typically hides deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion