Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware KandyKorn?
A recently discovered macOS malware called KandyKorn has been found in an attack linked to the North Korean Lazarus hacking group. Their targets are blockchain engineers who work with cryptocurrency exchange platforms. The attackers pretend to be part of the cryptocurrency community on Discord to share Python modules, which then kickstart a complicated infection process involving KandyKorn.
KandyKorn malware overview
KandyKorn is a highly sophisticated final-stage payload utilized as a tool that enables threat actors to infiltrate and extract data from the compromised computer. Operating covertly in the background as a daemon, KandyKorn patiently awaits commands from the Command and Control (C2) server.
This versatile malware supports various commands, each tailored for multiple purposes. These commands empower the attackers to perform actions ranging from gathering system information and listing directory contents to uploading and exfiltrating files, securely deleting files, managing running processes, executing system commands, and even initiating an interactive shell session for more hands-on control.
The consequences that victims may face as a result of this versatile malware, capable of executing a wide array of commands, are multifaceted and can be highly detrimental.
The KandyKorn's ability to gather system information and list directory contents enables attackers to gain deep insights into the victim's system, potentially leading to the theft of sensitive data, such as login credentials, financial information, or proprietary files.
By uploading and exfiltrating files, the attackers can engage in data theft, which could result in compromised intellectual property, financial loss, or data breaches. The malware's capacity for securely deleting files raises concerns for victims, as it may be employed to cover their tracks by erasing evidence of their activities, making it challenging for cybersecurity professionals to investigate or recover lost data.
Managing running processes can disrupt the victim's system operations and potentially lead to system instability or crashes. Furthermore, executing system commands and initiating an interactive shell session give the attackers significant control over the victim's computer, allowing them to carry out various malicious activities, such as installing additional malware, altering system settings, or launching cyberattacks.
Overall, KandyKorn's extensive capabilities create a broad spectrum of potential consequences for victims, including data breaches, financial losses, system disruptions, and a significant invasion of privacy.
| Name | KandyKorn macOS malware |
| Threat Type | Mac malware, Mac virus |
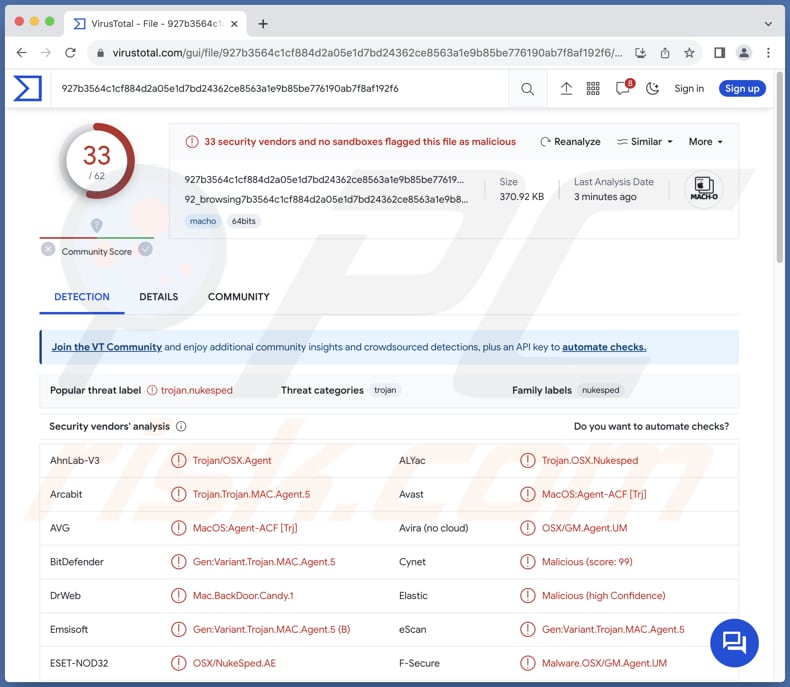
| Detection Names | Avast (MacOS:Agent-ACF [Trj]), Combo Cleaner (Gen:Variant.Trojan.MAC.Agent.5), ESET-NOD32 (OSX/NukeSped.AE), Kaspersky (HEUR:Backdoor.OSX.Agent.ao), Full List Of Detections (VirusTotal) |
| Symptoms | Malicious apps like KandyKorn are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution Methods | Discord, Social engineering, Deceptive ZIP files. |
| Damage | Monetary loss, identity theft, additional infections, data loss, system disruptions, privacy invasion, and more. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
In conclusion, KandyKorn is a highly sophisticated macOS malware associated with the Lazarus hacking group, designed for targeted attacks on blockchain engineers and cryptocurrency exchange platforms. Its multi-stage infection chain, initiated through Discord impersonation, grants attackers a wide range of capabilities, from data theft and file manipulation to system disruption and command execution.
More examples of malware targeting macOS users are MetaStealer, XLoader, and JokerSpy.
How did KandyKorn install on my computer?
The infection process initiates on Discord with a social engineering approach designed to trick targets into downloading a deceptive ZIP archive named "Cross-platform Bridges.zip". This archive masquerades as a legitimate arbitrage bot for cryptocurrency trading.
After extracting the ZIP archive's contents, a Python script called "Main.py" launches, importing 13 modules, including "Watcher.py", a downloader. Watcher.py proceeds to unpack and run "testSpeed.py" while obtaining "FinderTools" from a Google Drive URL.
FinderTools serves as a dropper, fetching and executing an obfuscated binary named "SugarLoader". SugarLoader establishes a connection with a command and control (C2) server and loads the final payload, KandyKorn.
How to avoid installation of malicious applications?
Only obtain software and files from reputable sources (official pages and application stores), and be wary of email attachments and links in suspicious emails from unknown sources. Avoid clicking on pop-up ads or visiting potentially harmful websites. Keep your operating system, software, and antivirus programs up to date.
Use reliable antivirus software and never download pirated software or tools designed to bypass software activation. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate all threats.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
Video showing how to remove adware and browser hijackers from a Mac computer:
Unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
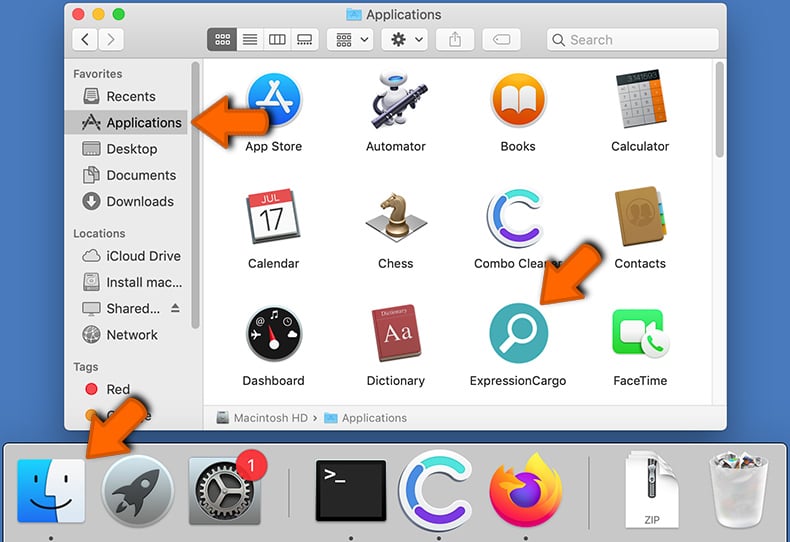
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Frequently Asked Questions (FAQ)
My computer is infected with KandyKorn malware, should I format my storage device to get rid of it?
Formatting your storage device is a drastic solution and should be considered a last resort. Before doing that, try running reputable security software like Combo Cleaner to scan and remove the KandyKorn malware.
What are the biggest issues that malware can cause?
Malware can cause significant issues, including data loss, identity theft, financial fraud, and system instability. It can lead to the theft of sensitive personal and financial information, as well as the loss of critical data. Malware can also damage or disrupt computer systems, slowing down performance and potentially rendering them inoperable. Furthermore, it can be used as a tool for cyberattacks, such as Distributed Denial of Service (DDoS) attacks.
What is the purpose of KandyKorn malware?
KandyKorn allows threat actors to gather sensitive system information, list directory contents, upload and exfiltrate files, securely delete files, manage running processes, execute system commands, and initiate interactive shell sessions, providing extensive control over the victim's computer.
How did KandyKorn malware infiltrate my computer?
KandyKorn malware is delivered through a Discord social engineering attack. Victims are being deceived into downloading a deceptive ZIP archive posing as a cryptocurrency arbitrage bot. This archive contains a Python script, "Main.py", which triggers a chain of processes, including the execution of "SugarLoader", ultimately establishing a connection to a command and control (C2) server and loading KandyKorn as the final payload.
Will Combo Cleaner protect me from malware?
Combo Cleaner has the capability to detect and remove nearly all well-known malware infections. Sophisticated malware often conceals itself deeply within the system. Therefore, running a comprehensive system scan is essential.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion