Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is MetaStealer?
MetaStealer is a type of malware designed to target Mac users. Its primary objective is to obtain sensitive information from its victims. This malicious software is built using the Go programming language. Once infiltrated, MetaStealer poses a significant threat to the privacy and security of Mac users.
MetaStealer overview
In 2023, a surge in infostealers targeting macOS users has been witnessed, with one of the prominent threats being the MetaStealer malware. This malware exhibits distinctive characteristics that set it apart from other recent infostealers. What is noteworthy is the deliberate targeting of macOS business users through social engineering tactics, where attackers pose as fake clients to lure victims into executing malicious payloads.
These lures often take the form of disk image bundles with seemingly business-related filenames, creating an unusual pattern for macOS malware. The core executable within MetaStealer bundles is an Intel x86 Mach-O containing obfuscated Go source code.
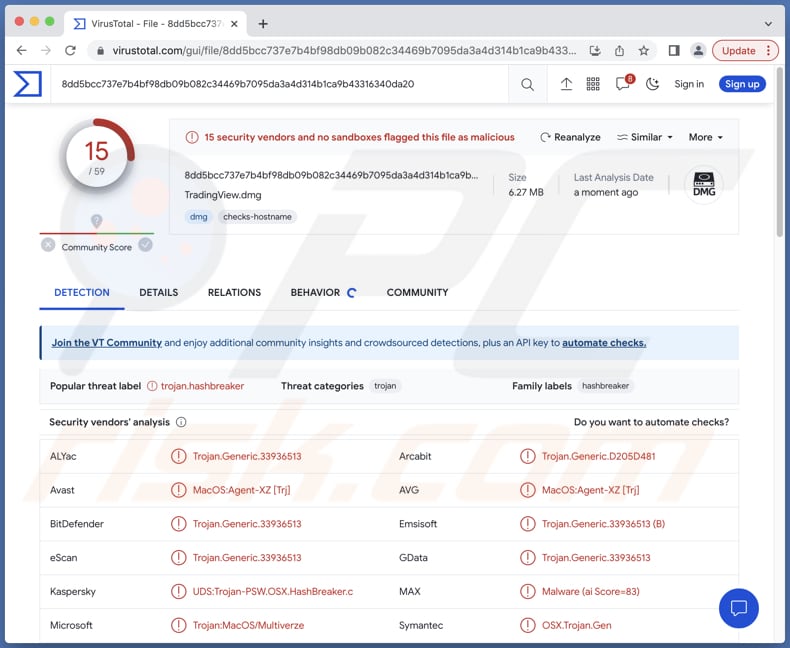
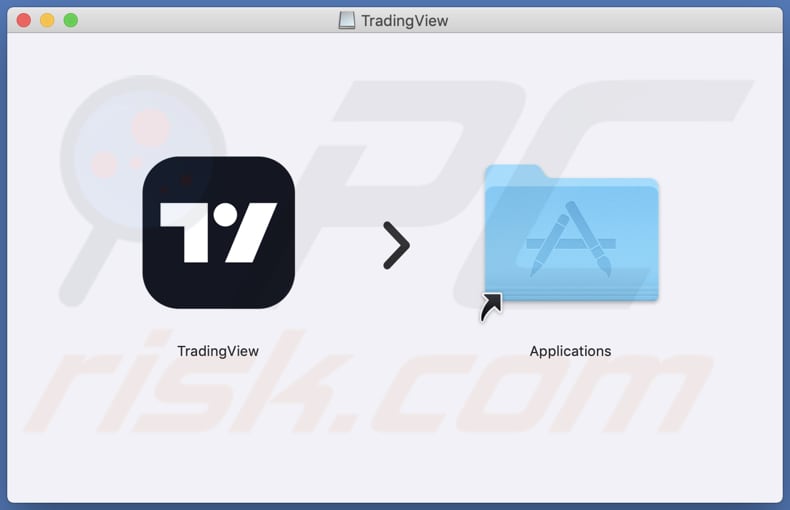
While heavily obfuscated, some functional aspects remain discernible, including functions for exfiltrating the keychain, extracting saved passwords, and retrieving files. Intriguingly, some versions of MetaStealer target Telegram and Meta services. It is also known that MetaStealer (some of its versions) masquerades as a TradingView application.
MetaStealer poses a significant threat to data security by stealing sensitive information, potentially leading to identity theft, financial losses, and privacy breaches. When targeting business users, MetaStealer can disrupt corporate operations, compromise proprietary data, and result in financial setbacks and damage to the organization's reputation.
| Name | MetaStealer information stealer |
| Threat Type | Information stealer |
| Detection Names | Avast (MacOS:Agent-XZ [Trj]), Combo Cleaner (Trojan.Generic.33936513), Emsisoft (Trojan.Generic.33936513 (B)), Kaspersky (UDS:Trojan-PSW.OSX.HashBreaker.c), Symantec (OSX.Trojan.Gen), Full List (VirusTotal) |
| Symptoms | Information stealers are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Fake applications, DMG files obtained from shady sources, infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, financial loss, and more. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
In conclusion, MetaStealer represents a concerning evolution in the landscape of macOS-focused infostealers, demonstrating the adaptability and sophistication of contemporary cyber threats. This malware's deliberate targeting of business users through social engineering tactics and the use of obfuscation techniques underscore its potential for extensive data theft and corporate espionage.
As cybercriminals continue to refine their strategies, vigilant cybersecurity practices and proactive threat detection are imperative to safeguard against the insidious impact of MetaStealer and similar malicious software on both individuals and organizations.
More examples of malware targeting Mac users are XLoader, JokerSpy, and Geacon.
How did MetaStealer install on my computer?
Cybercriminals employ cunning tactics to lure users into infecting their computers with MetaStealer. They primarily rely on social engineering techniques, such as posing as fake clients or leveraging enticing filenames, to deceive victims into launching malicious payloads. The malware is often concealed within disk image bundles, with filenames that suggest business relevance, creating a sense of legitimacy to entice business users.
These social engineering tactics play on the victim's trust, leading them to execute the disguised malware. Once executed, MetaStealer gains unauthorized access to the victim's macOS system, initiating its infostealing operations. Fake apps like TradingView are also used to deliver MetaStealer.
How to avoid installation of unwanted applications?
Adhere to official app stores and authorized websites when downloading software, steering clear of cracked or pirated versions from untrustworthy sources. Exercise caution when handling email attachments or links, particularly if the sender is unfamiliar or if the email raises suspicion. Regularly update your operating system, software, and applications.
Use reputable antivirus or anti-malware software to identify and thwart threats, and keep these security tools up-to-date to combat the latest malware strains. In some instances, victims are tricked into believing that the malicious payload is related to their ongoing negotiations with supposed clients.
If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate all threats.
MetaStealer malware masquerading as TradingView application:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
Video showing how to remove adware and browser hijackers from a Mac computer:
Unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
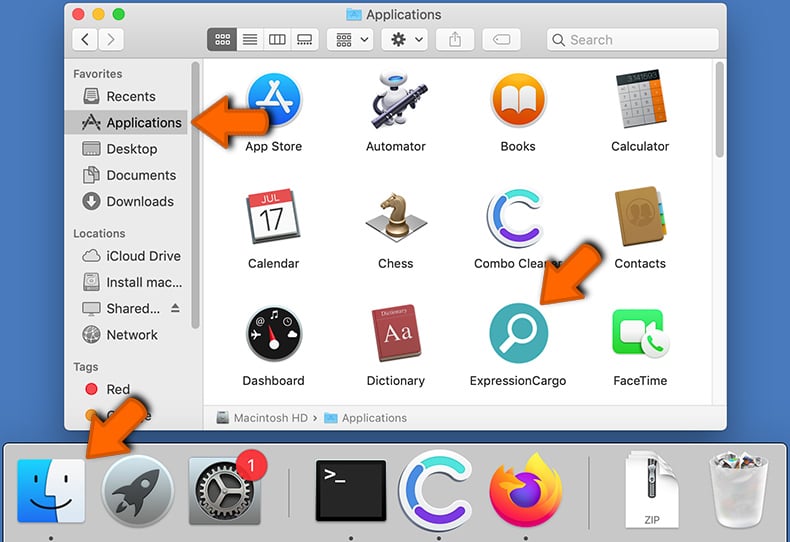
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Frequently Asked Questions (FAQ)
My computer is infected with MetaStealer malware, should I format my storage device to get rid of it?
In the event of a MetaStealer malware infection on your device, formatting your storage should be regarded as a drastic yet potent solution for its removal. However, it should be viewed as a last-resort option since formatting will result in the complete erasure of all data on the storage device. Prior to considering formatting, it is advisable to explore alternative methods, such as employing reputable security software like Combo Cleaner.
What are the biggest issues that malware can cause?
Malware poses several significant threats to individuals and organizations. These include data breaches and theft, leading to identity theft and financial losses; system and network disruptions, resulting in downtime and decreased productivity; and the potential for the spread of additional malware, creating a cascading effect of security vulnerabilities and further cyberattacks.
What is the purpose of MetaStealer malware?
The primary purpose of MetaStealer malware is to covertly steal sensitive information from macOS users. This malicious software is specifically designed to infiltrate macOS systems and harvest valuable data, including login credentials, personal information, and confidential files.
How did MetaStealer malware infiltrate my computer?
Cybercriminals utilize cunning tactics, notably relying on social engineering methods, to ensnare users into unwittingly infecting their computers with MetaStealer. Their approach involves posing as fraudulent clients or enticing victims with deceptive filenames, all within the context of seeming business relevance. Fake apps (e.g., TradingView) are also used to distribute MetaStealer.
Will Combo Cleaner protect me from malware?
Combo Cleaner possesses the capability to detect and remove nearly all known malware infections. However, it is crucial to note that advanced malware often conceals itself deep within the system's core. Therefore, conducting a comprehensive full system scan is imperative to uncover and address these hidden threats.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion