Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Kematian?
Kematian is a stealer-type malware. It is a PowerShell-based malicious program. Kematian is designed to steal vulnerable information, including extensive system data, various log-in credentials (usernames/passwords), cryptocurrency wallets, and so on. The stealer's developers are promoting it online; hence, how Kematian is proliferated may vary between attacks.
Kematian malware overview
As mentioned in the introduction, Kematian is a piece of malicious software created to extract and exfiltrate data from compromised systems. The following is an overview of the stealer's capabilities, as gleaned from its promotional material.
Kematian has anti-analysis abilities, i.e., it can detect when launched on VMS (Virtual Machines) or in sandboxes. It also possesses anti-debugging and anti-detection features (i.e., anti-virus disablement, bypassing, and addition to exclusion lists). Kematian ensures persistence by restarting automatically following each system reboot.
The malware collects a broad range of information for infected machines, e.g., device manufacturer and model, hardware details (CPU, GPU, RAM, MAC address, etc.), device name, operating system version and architecture, drive details (drive number, used/free disk space, etc.), system language, account username, and so on.
Kematian seeks detailed geolocation data as well, e.g., IP address, country, region, city, coordinates (latitude/longitude), and ZIP code. Network information gathered by this malware includes ISP (Internet Service Provider) and Wi-Fi networks and passwords.
Additionally, the stealer obtains a list of installed applications. From apps of interest, Kematian can extract a variety of sensitive data, such as session files, log-in credentials, and 2FA (Two-Factor Authentication) codes. The malicious program targets: Chromium and Gecko based browsers, email clients, messengers, VPN (Virtual Private Network) clients, password managers, desktop and browser extension cryptocurrency wallets, FTP (File Transfer Protocol) clients, and gaming-related software (extensive list below).
Kematian can acquire the following data from browsers – browsing histories, Internet cookies, saved log-in credentials (usernames/passwords), and so forth. From messaging software, this stealer seeks sessions, and tokens from Discord specifically.
Other information-stealing capabilities include taking screenshots and snapshots via cameras, as well as exfiltrating content copied into the clipboard (copy-paste buffer). Furthermore, when attempts to terminate the stealer's process are made, it can display the Blue Screen Error, thus crashing the system.
It must be mentioned that malware developers commonly improve upon their creations. Therefore, potential future versions of Kematian can have a broader target list or additional/different capabilities.
To summarize, the presence of software like the Kematian stealer on devices may result in serious privacy issues, significant financial losses, and even identity theft.
| Name | Kematian malware |
| Threat Type | Trojan, stealer, password-stealing virus, spyware. |
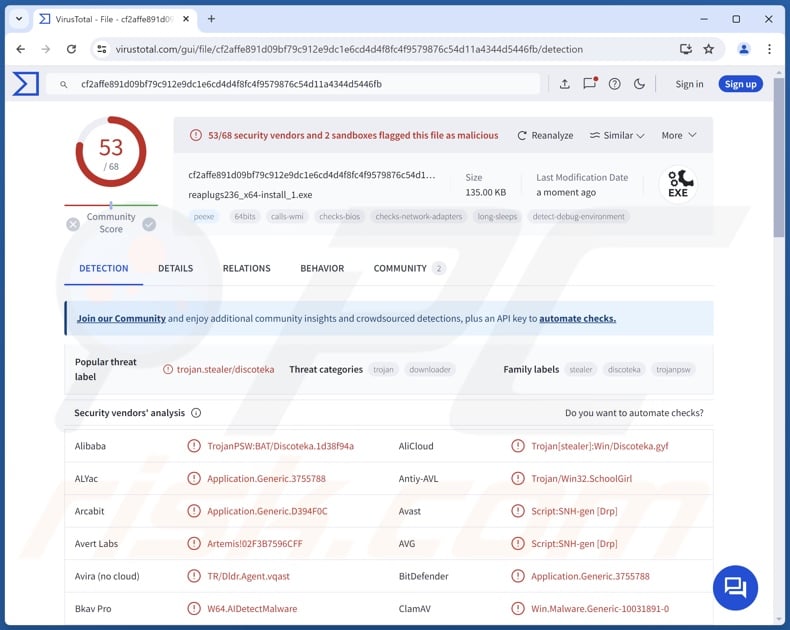
| Detection Names | Avast (Script:SNH-gen [Drp]), Combo Cleaner (Application.Generic.3755788), ESET-NOD32 (BAT/TrojanDownloader.Agent.OZP), Kaspersky (UDS:Trojan-Spy.Win32.Stealer), Malwarebytes (Generic.Malware.AI.DDS), Full List Of Detections (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Stealer-type malware examples
We have investigated thousands of malware samples; KoiStealer, Waltuhium, Vert, Stink, and Braodo are just some of our newest articles on stealers.
These programs can be incredibly versatile or extremely narrowly tailored. Furthermore, data-stealing functionalities are not limited to malware within the "stealer" classification. Even if a malicious program seeks seemingly useless or innocuous information, it can still be used for a variety of nefarious purposes.
In fact, the presence of any malware on devices threatens system integrity and user safety. Therefore, all threats must be eliminated immediately upon detection.
How did Kematian infiltrate my computer?
At the time of writing, Kematian is promoted by its developers on GitHub. Therefore, how it is spread can depend on the cyber criminals' using it.
Generally, malware is proliferated using phishing and social engineering tactics. Malicious programs are typically presented as or bundled with regular software/media. Virulent files can be executables (.exe, .run, etc.), archives (RAR, ZIP, etc.), documents (Microsoft Office, Microsoft OneNote, PDF, etc.), JavaScript, and so forth.
Malware is predominantly distributed via drive-by (stealthy/deceptive) downloads, online scams, malicious attachments or links in spam emails/messages, untrustworthy download sources (e.g., freeware and third-party websites, P2P sharing networks, etc.), pirated content, illegal software activation ("cracking") tools, fake updaters, and malvertising.
Some malicious programs can even self-proliferate through local networks and removable storage devices (e.g., external hard drives, USB flash drives, etc.).
How to avoid installation of malware?
It is essential to be vigilant while browsing since fake and dangerous online content typically appears legitimate and harmless. We recommend approaching incoming emails, DMs/PMs, SMSes, and other messages with caution. Attachments or links in dubious/irrelevant mail must not be opened, as they can be malicious.
Another recommendation is to download only from official and verified channels. We advise activating and updating software by using genuine functions/tools, as those obtained from third-parties can contain malware.
It is paramount for device integrity and user safety to have a reputable anti-virus installed and kept updated. This software must be used to perform regular system scans and to remove detected threats. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Partial list of applications targeted by Kematian malware;
Messaging software:
- Element
- ICQ
- Pidgin
- Signal
- Skype
- Telegram
- Tox
- Viber
Email clients:
- Thunderbird
FTP clients:
- FileZilla
- WinSCP
VPN clients:
- OpenVPN
- Proton
- Surfshark
Gaming-related software:
- Battle.net
- Electronic Arts
- Epic Games
- Growtopia
- Minecraft (14 launchers)
- Steam
- Ubisoft
Kematian stealer promoted on GitHub:
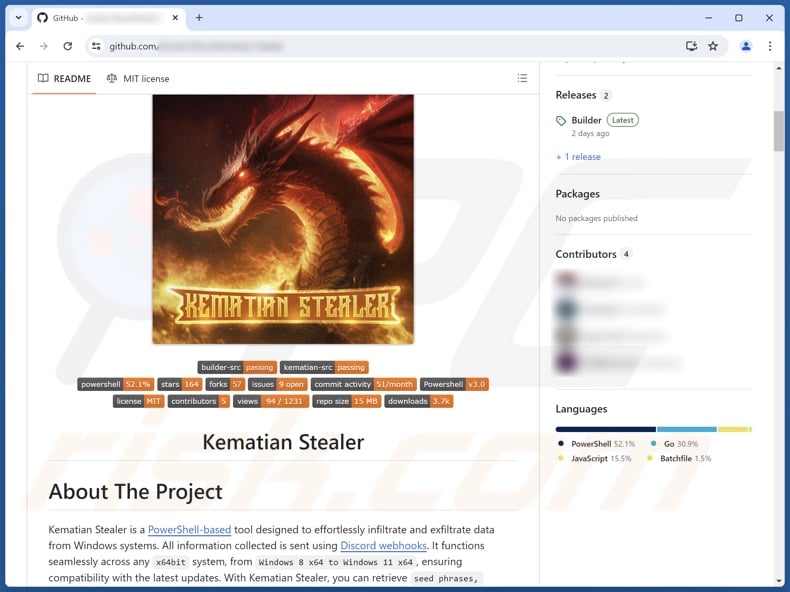
Update July 4, 2024: It is known that Kematian spreads through a Google Chrome extension called TRANSLATEXT, which bypasses security measures for email services like Gmail, Kakao, and Naver to steal sensitive information. This extension is used to gather email addresses, usernames, passwords, cookies, and take screenshots of the browser.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Kematian?
- STEP 1. Manual removal of Kematian malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Kematian malware, should I format my storage device to get rid of it?
Malware removal rarely requires formatting.
What are the biggest issues that Kematian malware can cause?
The dangers posed by an infection depend on the malicious program's functionalities and the cyber criminals' modus operandi. Kematian is an information-stealing malware; infections of this kind are associated with severe privacy issues, significant financial losses, and identity theft.
What is the purpose of Kematian malware?
The motivation behind most malware infections is profit. However, cyber criminals also use malicious programs to amuse themselves, carry out personal vendettas, disrupt processes (e.g., websites, services, companies, organizations, etc.), engage in hacktivism, and launch politically/geopolitically motivated attacks.
How did Kematian malware infiltrate my computer?
Malware is primarily distributed via drive-by downloads, dubious download channels (e.g., freeware and third-party sites, Peer-to-Peer sharing networks, etc.), spam mail, online scams, malvertising, pirated content, illegal software activation tools ("cracks"), and fake updates. Furthermore, some malicious programs can self-spread through local networks and removable storage devices.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and remove practically all known malware infections. Note that since sophisticated malicious programs usually hide deep within systems – performing a complete system scan is crucial.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion