Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Shamos?
Shamos is a variant of the AMOS (Atomic) stealer. This malicious program targets macOS devices and seeks to steal sensitive data. Shamos has been around since at least the summer of 2025. It was developed and is offered as MaaS (Malware-as-a-Service) by a threat actor group dubbed "COOKIE SPIDER". Shamos stealer has been actively spread via ClickFix scams.
Shamos malware overview
At the time of research, Shamos infiltrated systems through ClickFix scams. Victims are deceived into copying/pasting and executing a malicious command in Terminal, thus triggering the download of a Bash script file. This technique enables bypassing Gatekeeper security checks. After obtaining the user account log-in credentials, the file downloads and executes a Mach-O file containing Shamos.
The stealer uses anti-analysis mechanisms, such as detecting when it is launched on a VM (Virtual Machine) or in a sandbox environment. It then starts collecting relevant device data. Shamos searches the system for files of interest, e.g., ones relating to passwords and cryptocurrency wallets.
This program can also extract information from Keychain (Mac's native password storage app), the Notes application, and browsers. Typically, data-stealing software aims to extract the following information from browsers: browsing and search engine histories, Internet cookies, auto-fills (e.g., personally identifiable details, usernames, etc.), passwords, credit/debit card numbers, and so on.
Furthermore, Shamos can download/install additional malicious programs or components. The stealer has been observed introducing a botnet module and a fake Ledger Live wallet app into systems. However, it could be used to infiltrate other content.
Theoretically, programs capable of causing chain infections can introduce just about any type of malware into devices (e.g., trojans, ransomware, cryptocurrency miners, etc.). Although practically, these programs tend to operate within certain specifications or limitations.
To summarize, the presence of software like Shamos on devices can lead to multiple system infections, severe privacy issues, financial losses, and identity theft.
| Name | Shamos malware |
| Threat Type | Mac malware, Mac virus, stealer, password-stealing virus. |
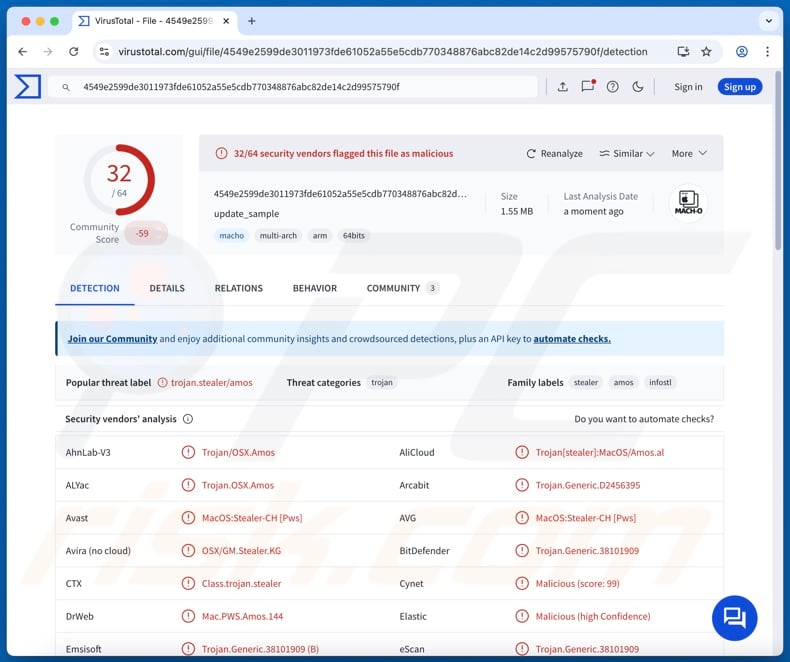
| Detection Names | Avast (MacOS:Stealer-CH [Pws]), Combo Cleaner (Trojan.Generic.38101909), ESET-NOD32 (A Variant Of OSX/PSW.Agent.EA), Kaspersky (HEUR:Trojan-PSW.OSX.Amos.an), Full List Of Detections (VirusTotal) |
| Symptoms | Malware is designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution Methods | Online scams, deceptive pop-up ads, free software installers (bundling), malspam. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Stealer-type malware infections
We have written thousands of articles on malware; mac.c stealer, Odyssey, Cthulhu, Banshee, and ROD are just some of ours on stealers. Targeted information can be incredibly broad or narrow. What is more, stealers are often used in combination with other malware, and data-exfiltrating functionalities are prevalent in general.
However, regardless of how malicious software works – its presence on a system endangers device integrity and user safety. Therefore, all threats must be eliminated immediately upon detection.
How did Shamos infiltrate my computer?
As previously mentioned, Shamos has been proliferated via ClickFix scams. The core element of these scams is to lure users into copying/pasting and executing a command in Terminal. Multiple ClickFix campaigns wearing different disguises have been noted.
Malvertising (malicious advertising) and SEO poisoning techniques were used to promote fake Mac help websites. These pages may utilize the names and branding of genuine companies, thereby creating an impression of legitimacy.
Targeted users were located in the United States, the United Kingdom, Canada, China, Colombia, Italy, Japan, and Mexico. One notable exclusion – Russia – was observed; however, this is not surprising, as many MaaS (Malware-as-a-Service) online marketplaces are based in Russia.
Shamos-spreading ClickFix scams were also endorsed via deceptive GitHub repositories. The lures were promises of free downloads for various Mac-specific tools, such as iTerm2, optimization software, video editors, audio programs, CAD (Computer-Aided Design) software, AI (Artificial Intelligence) tools, etc.
However, Shamos stealer could be distributed using other techniques. Phishing and social engineering tactics are standard in malware proliferation.
Aside from scams, malware is widely spread via drive-by (stealthy/deceptive) downloads, malvertising, malicious attachments/links in spam mail (e.g., emails, PMs/DMs, etc.), suspicious download channels (e.g., freeware and third-party websites, Peer-to-Peer sharing networks, etc.), pirated programs/media, illegal software activation tools ("cracks"), and fake updates.
Furthermore, some malicious programs can self-proliferate through local networks and removable storage devices (e.g., external hard drives, USB flash drives, etc.).
How to avoid installation of malware?
We highly recommend vigilance when browsing since the Internet is full of deceptive and dangerous content. Incoming emails and other messages must be approached with caution. Attachments or links present in dubious/irrelevant mail must not be opened, as they can be virulent.
Another recommendation is to download only from official and verified sources. Additionally, all programs must be activated and updated using legitimate functions/tools, as those obtained from third-parties can contain malware.
We must emphasize the importance of having a reputable antivirus installed and kept up-to-date. Security software must be used to perform regular system scans and to remove detected threats and issues. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Fake pages used in ClickFix scams spreading Shamos malware (image source – CrowdStrike Cybersecurity Blog):
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "Shamos"?
- Remove PUA related files and folders from OSX.
- Remove rogue extensions from Safari.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
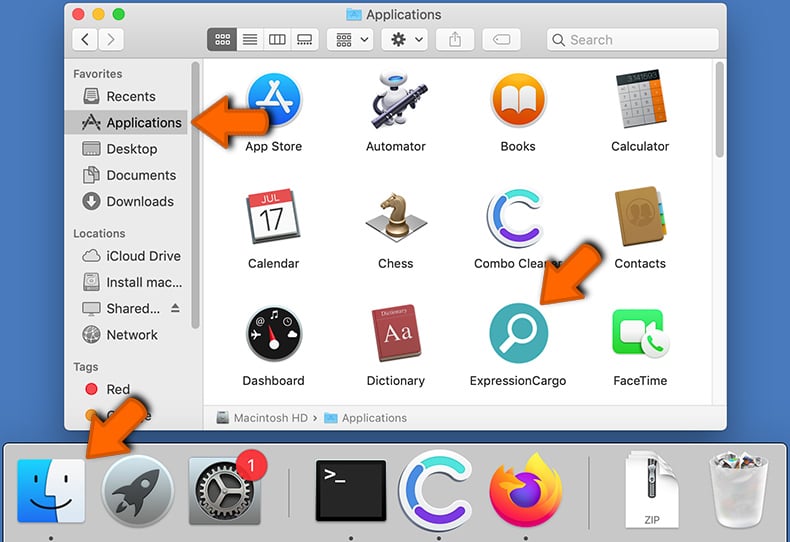
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Frequently Asked Questions (FAQ)
My computer is infected with Shamos malware, should I format my storage device to get rid of it?
No, Shamos stealer's removal does not require formatting.
What are the biggest issues that Shamos malware can cause?
The dangers associated with an infection depend on the malware's abilities and the attackers' modus operandi. Shamos is a stealer that targets vulnerable data and can cause chain infections. Hence, the presence of this software can lead to system infections, severe privacy issues, financial losses, and identity theft.
What is the purpose of Shamos malware?
The most prevalent motivation behind malware attacks is financial gain. Other possible reasons include: attackers seeking amusement or realization of personal grudges, process disruption (e.g., websites, services, companies, organizations, etc.), hacktivism, and political/geopolitical motivations.
How did Shamos malware infiltrate my computer?
Shamos has been distributed through multiple ClickFix scam campaigns. Other distribution techniques are not unlikely. Generally, malware is proliferated via drive-by downloads, spam emails/messages, malvertising, dubious download channels (e.g., freeware and free file-hosting websites, P2P sharing networks, etc.), illegal software activation tools ("cracks"), pirated content, and fake updates. Some malicious programs can self-spread through local networks and removable storage devices.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is capable of detecting and removing practically all known malware infections. Remember that performing a complete system scan is essential since sophisticated malicious programs tend to hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate


▼ Show Discussion