You have been blocked from our website! Virus
Phishing/ScamAlso Known As: You have been blocked from our website! Hosts File Hijacker
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is You have been blocked from our website?
This message states that the Internet user was blocked from accessing popular websites (such as Google.com, Facebook.com, eBay.com, etc.) and demands completion of online surveys in order to restore access. This is a scam, a rogue website to which users are redirected when their computers are infected with Hosts file-modifying malware.
The operating system Hosts file is used to resolve canonical names of websites to IP addresses, and when this file is changed, users may be redirected to malicious websites whilst observing legitimate URLs in the browser address bar.
The deceptive message (used to trick unsuspecting PC users into completing online surveys), states that the website block was imposed for security reasons and forces users into downloading "TRUSTe Website Unlocker", which supposedly removes the malware purported to affect Internet browsing.
In fact, this message is a scam and the name of TRUSTe is exploited by cyber criminals who are responsible for creating this Hosts file hijacker, which redirects Internet users to this website.
If you cannot access Google.com or other popular websites and you see the message, "You have been blocked from our website!", your operating system Hosts file was modified by malware. Ignore this message and do not complete any online surveys.
The "You have been blocked from our website!" virus is distributed using fake downloads. For example, Internet users can be tricked into downloading this virus by malicious websites, which supposedly promote Facebook password-hacking tools, WiFi password-hacking tools, etc.
Other popular sources of this Hosts file hijacker are P2P networks and drive-by download infections. Note that completing online surveys when requested by this deceptive message can result in signing up for some costly mobile services. Avoid such online survey scams.
To protect your PC from Hosts file-modifying malware such as this, use legitimate antivirus and anti-spyware software. If your computer is already infected, use the removal guide provided to eliminate this virus from your PC.
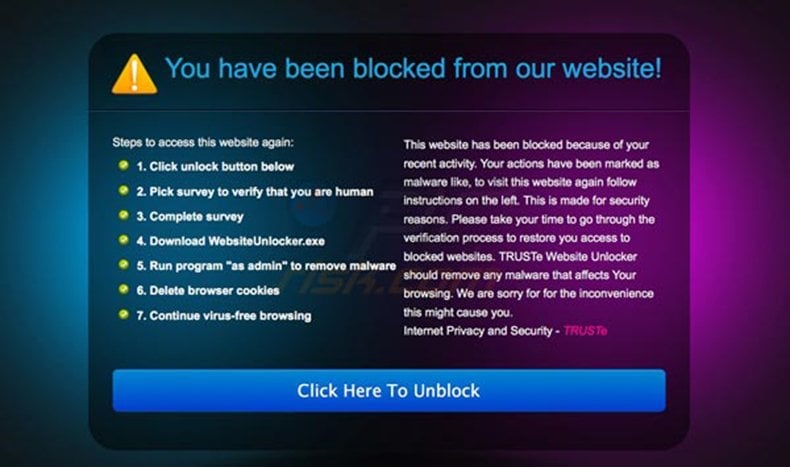
A deceptive message used to trick Internet users into completing online surveys:
You have been blocked from our website!
This website has been blocked because of your recent activity. Your actions have been marked as malware like, to visit this website again follow instructions on the left. This is made for security reasons. Please take your time to go through the verification process to restore you access to blocked websites. TRUSTe Website Unlocker should remove any malware that affects Your browsing. We are sorry for for the inconvenience this might cause you.
Internet Privacy and Security - TRUSTe
Steps to access this website again:
1. Click unlock button below
2. Pick survey to verify that you are human
3. Complete survey
4. Download WebsiteUnlocker.exe
5. Run program "as admin" to remove malware
6. Delete browser cookies
7. Continue virus-free browsing
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is You have been blocked from our website!?
- STEP 1. "You have been blocked from our website!" virus removal using software.
- STEP 2. Uninstall adware applications using Control Panel.
- STEP 3. Remove adware from Internet Explorer.
- STEP 4. Remove rogue plug-ins from Google Chrome.
- STEP 5. Remove adware-type extensions from Mozilla Firefox.
- STEP 6. Remove malicious extensions from Safari.
- STEP 7. Remove rogue plug-ins from Microsoft Edge.
"You have been blocked from our website! " virus removal:
Internet browser redirects to the "You have been blocked from our website! " website are caused by a Trojan, which modifies the operating system Hosts file. To remove this Trojan, download recommended malware removal software and run a full system scan.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
After eliminating this Trojan, check your operating system Hosts file. Information stored in this file is responsible for resolving canonical names of websites - if the information within this file is changed by a malicious program, you could encounter redirect problems whilst surfing the Internet.
The Hosts file is used to resolve canonical names of websites to IP addresses. When it is changed, the user may be redirected to malicious sites, despite seeing legitimate URLs in address bar. It is difficult to determine sites are genuine when the Hosts file is modified.
To fix this, please download the Microsoft Fix It tool, that restores your Hosts file to the Windows default. Run this tool when downloaded and follow the on-screen instructions. Download link below:
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion