Removal instructions for software preventing you from using Google.com
Browser HijackerAlso Known As: Google.com browser hijacker
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the google.com redirect?
Google.com, developed by the Google LLC multinational technology company, is the most popular search engine in the world. "Google redirect" can refer to two types of undesirable phenomena.
First, when Google had been the default search engine but no longer is, and users experience a redirect to a different site when they try to use it.
The second is an unwanted redirect to Google when the default search engine was not it. Additionally, users can experience so-called "drive-by/chain" redirects when a browser hijacker redirects to a suspicious site which, in turn, redirects users to Google as a disguise.
Such redirects to various search engines are caused by software classified as browser hijackers. They modify browser settings to promote (mostly fake) Web searching tools. Furthermore, browser-hijacking software spies on users' browsing activity.
Browser-hijacking software overview
If you open your browser's homepage, new tab/window, or type a search query into the URL bar - and instead of accessing your default search engine (e.g., google.com), get redirected elsewhere - this can be caused by a browser hijacker.
Browser-hijacking software is designed to promote certain search engines by assigning them as browsers' default, as well as their homepage and new tab/window URLs. Hence, when users open the previously mentioned windows or attempt to search the Web via the URL bar - they experience an unexpected redirect.
This software typically promotes fake search engines, and since they are rarely capable of providing search results - they redirect to legitimate ones (e.g., Google, Yahoo, Bing, etc.).
Therefore, if the promoted illegitimate search engine redirects to google.com (and it is the user's preferred search engine) - it may be difficult to notice and appear innocuous. However, fake search engines tend to collect (and sell) information about their visitors.
It must be emphasized that the legitimate search engines that browser hijackers redirect to (e.g., Google) are not associated with this untrustworthy software.
Changing the settings modified by browser hijackers can be complicated, as this software often uses persistence-ensuring techniques (e.g., "Managed by your organization" Google Chrome feature, etc.) to prevent users from recovering their browsers.
Examples of such browser hijackers include ISEEK, SURFSEE, SEEKSE, JDISearch, KSEARCHY, Kinsearch, UKASEE, Kaseek, Searchisty, SEARCHBOX, and ONFIND. In this case, malicious extensions cause the aforementioned chain redirect. Firstly, user is redirected to findflarex.com, which in turn redirects to boyu.com.tr. Causing chain redirects is a common tactic to generate traffic for multiple websites at once.
Furthermore, browser-hijacking software usually has data tracking abilities. Targeted information can include: URLs visited, webpages viewed, search queries typed, personally identifiable details, usernames/passwords, financial/banking data, and so on. The collected information can be monetized by being shared with or sold to third-parties (potentially, cyber criminals).
In summary, the presence of browser hijackers on browsers/systems can lead to severe privacy issues, financial losses, and even identity theft.
| Name | Google.com browser hijacker |
| Threat Type | Browser Hijacker, Redirect, Search Hijacker, Toolbar, Unwanted New Tab |
| Supposed Functionality | Browser hijackers promise enhanced search results, faster searches, improved web browsing experience, etc. |
| Affected Browser Settings | Homepage, new tab URL, default search engine |
| Symptoms | Manipulated Internet browser settings (homepage, default Internet search engine, new tab settings). Users are forced to visit the hijacker's website and search the Internet using their search engines. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), fake Flash Player installers. |
| Damage | Internet browser tracking (potential privacy issues), display of unwanted ads, redirects to dubious websites. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Browser hijacker examples
We have analyzed thousands of browser hijackers; SwiftSearch, To Go Web, Keep Secure Search, Cool Search, and Tap togo are merely some examples. This software appears legitimate and offers "handy" features, which are rarely operational.
Browser hijackers alter browser settings to promote fake search engines, which typically redirect to genuine ones. Fraudulent search engines also tend to appear ordinary and harmless; nearbyme[.]io, star-search[.]xyz, websearches[.]club, searchtoolshub[.]com - are just a couple examples of such websites.
How did a browser hijacker install on my computer?
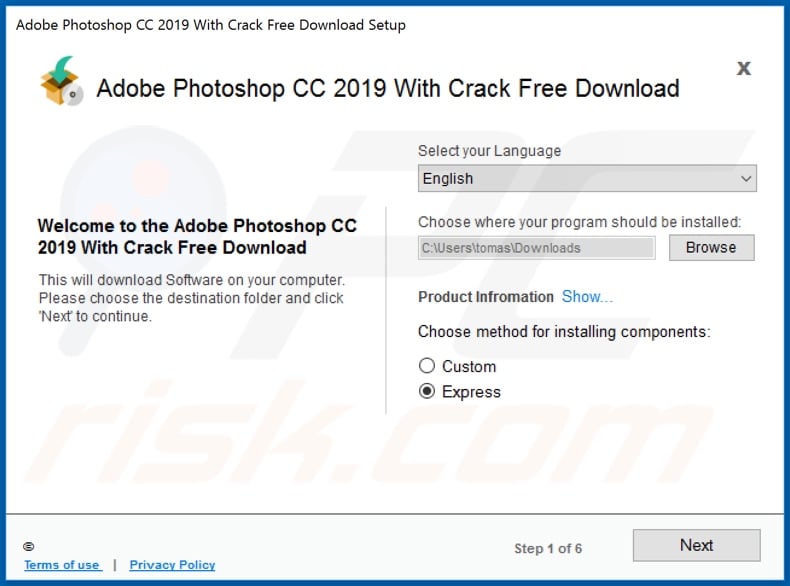
Browser hijackers are distributed using the "bundling" marketing method - packing regular program installation setups with unwanted/malicious additions. Download from untrustworthy sources (e.g., freeware and third-party sites, P2P sharing networks, etc.) and rushed installations (e.g., skipped steps, used "Easy/Express" settings, etc.) increase the risk of allowing bundled content into the system.
Intrusive advertisements are also used to proliferate browser-hijacking software. When clicked on, some of these ads can execute scripts to make downloads/installations without user consent.
Additionally, browser hijackers are pushed through "official" promotional webpages and scam sites. Most users enter these websites via redirects caused by mistyped URLs, pages using rogue advertising networks, spam browser notifications, intrusive ads, or installed adware.
How to avoid installation of browser hijackers?
We strongly advise researching software and only downloading from official/verified channels. Additionally, installation processes must be approached with caution, e.g., by reading terms, inspecting possible options, using the "Custom/Advanced" settings, and opting-out of all supplements.
We also recommend being vigilant when browsing since fraudulent and malicious content typically looks innocuous. For example, intrusive adverts appear legitimate/harmless yet redirect to questionable websites (e.g., gambling, adult-dating, pornography, etc.).
In case of encounters with such advertisements and/or redirects, check the system and immediately remove all dubious applications and browser extensions/plug-ins. If your computer is already infected with browser hijackers, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
Example of a rogue installer used to distribute browser hijackers:
Appearance of a browser hijacker redirecting to a fake search engine (GIF):
Update January 18, 2023 - At this current moment usage of malicious Google Chrome extensions is the most popular method to cause unwanted redirects. Cyber criminals employ deceptive social engineering techniques in order to trick users into installation. By presenting them as browser updates or various useful tools crooks create the impression of legitimacy and thus gullible users often end up unwillingly installing malicious extensions by themselves. Here are the screenshots of the latest and most popular Chrome extensions (fake Chrome extension, fake Google Docs extension, fake Google Translate extension, Clean Notifications and Landscape Scroller) that cause unwanted redirects to google.com:
Examples of fake/deceptive pop-up messages promoting such malicious browser extension:
Update June 17, 2025 – Malicious Chrome/Edge extensions remain the primary cause of Google redirect hijacks in 2025, but cybercriminals have adopted more insidious techniques. Recent reports describe malware campaigns bundling fake software installers that force-install hidden browser extensions and even modify browser files to hijack searches.
These threats redirect user queries through attacker-controlled servers (enabling browsing data theft) and often chain multiple redirects via new fake search domains (e.g. a query going from mobilisearch.com to mobility-search.com before ending at Yahoo or Bing). Several new browser hijacker variants (such as MicroSearch, Your Search Bar, Mobilisearch, etc.) have appeared, some with thousands of victims.
In some cases, even legitimate extensions have been hijacked via compromised updates – users on tech forums traced unexpected Google redirects to seemingly benign add-ons (for example, a popular "Web Paint" page editor extension was identified as the culprit on some systems). These modern hijackers also employ aggressive persistence: malicious extensions may be installed as "enterprise" policies and thus won't appear in the normal extensions list, making removal tricky.
Removal advice is to scan your device with reputable anti-malware (for example Combo Cleaner) and checking for any unauthorized browser policies or unknown add-ons. If the redirect persists, users should disable all extensions and re-enable them one-by-one to pinpoint the malicious plugin – then uninstall it. In highly persistent cases (where browser settings or even DLL files were altered to enforce redirects), a full browser reset or reinstall is often necessary to completely eliminate the hijacker.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is a google.com redirect?
- STEP 1. Uninstall unwanted applications using Control Panel.
- STEP 2. Remove browser hijackers from Google Chrome.
- STEP 3. Remove browser hijacker homepage and default search engine from Mozilla Firefox.
- STEP 4. Remove browser hijacker redirects from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
Browser hijacker redirect removal:
Windows 11 users:
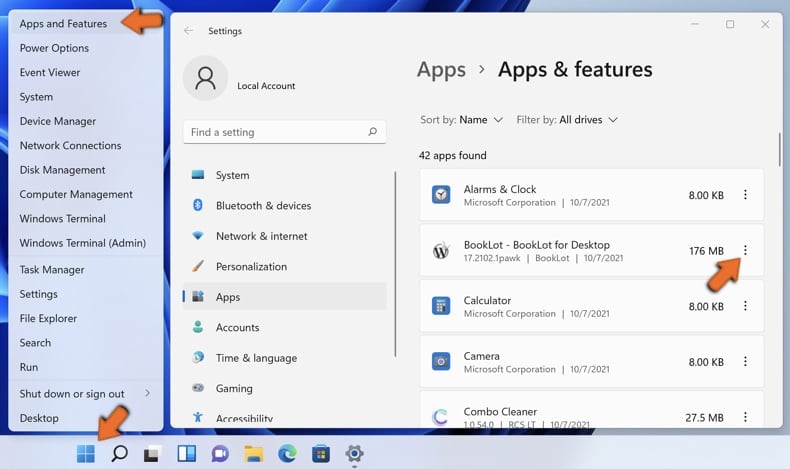
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
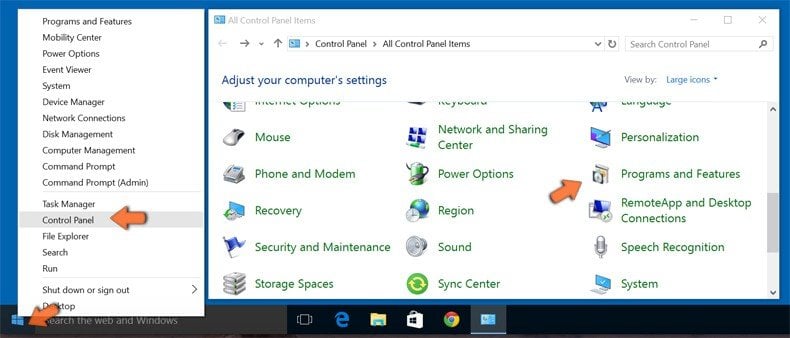
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.
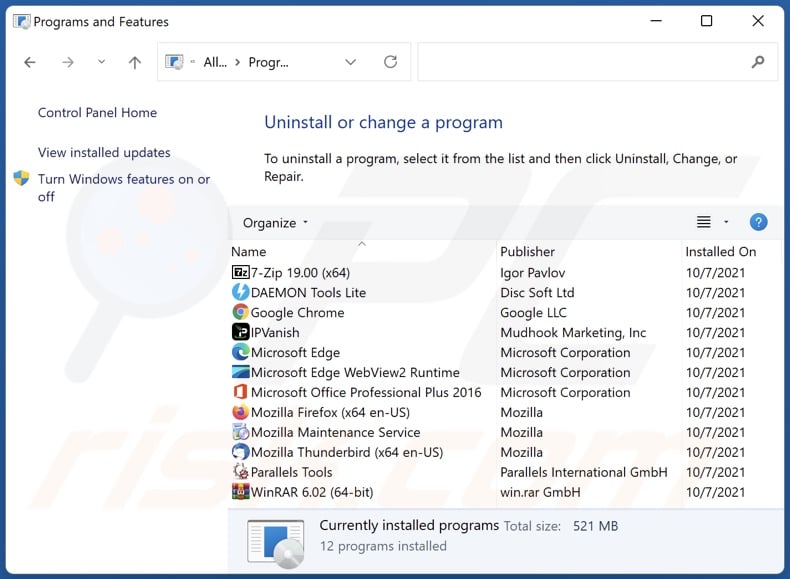
In the uninstall programs window: look for any recently installed suspicious applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the potentially unwanted applications, scan your computer for any remaining unwanted components. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Browser hijacker redirect removal from Internet browsers:
Video showing how to remove browser redirects:
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
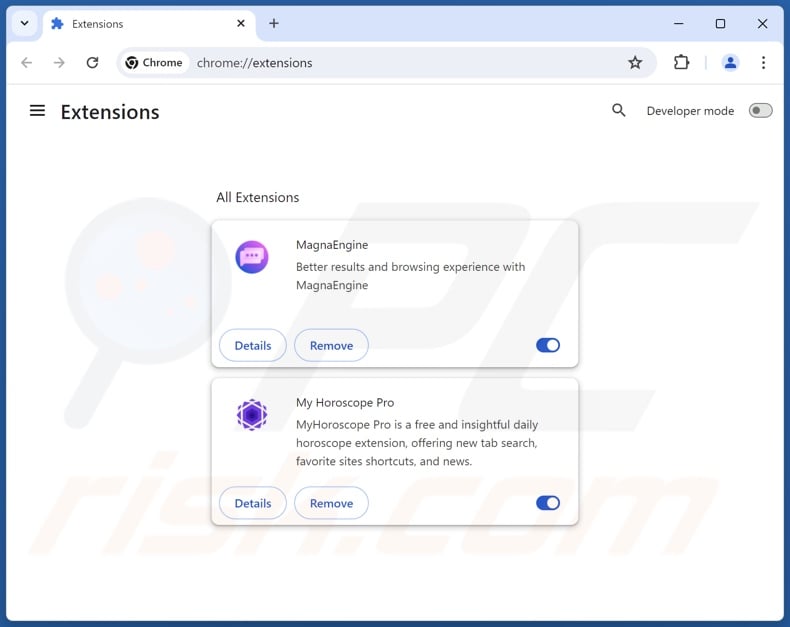
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
Change your homepage:
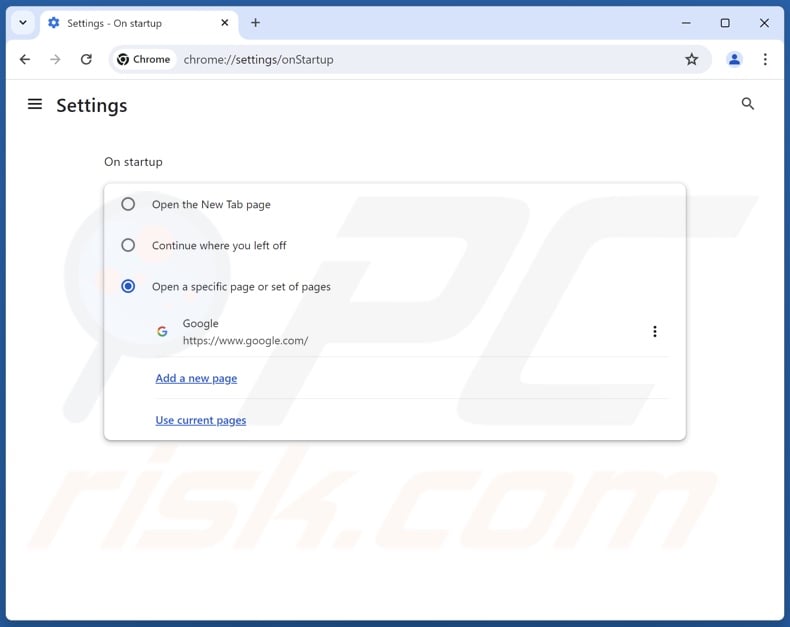
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Settings". In the "On startup" section, disable suspicious extensions, look for a browser hijacker URL below the "Open a specific or set of pages" option. If present click on the three vertical dots icon and select "Remove".
(at the top right corner of Google Chrome), select "Settings". In the "On startup" section, disable suspicious extensions, look for a browser hijacker URL below the "Open a specific or set of pages" option. If present click on the three vertical dots icon and select "Remove".
Change your default search engine:
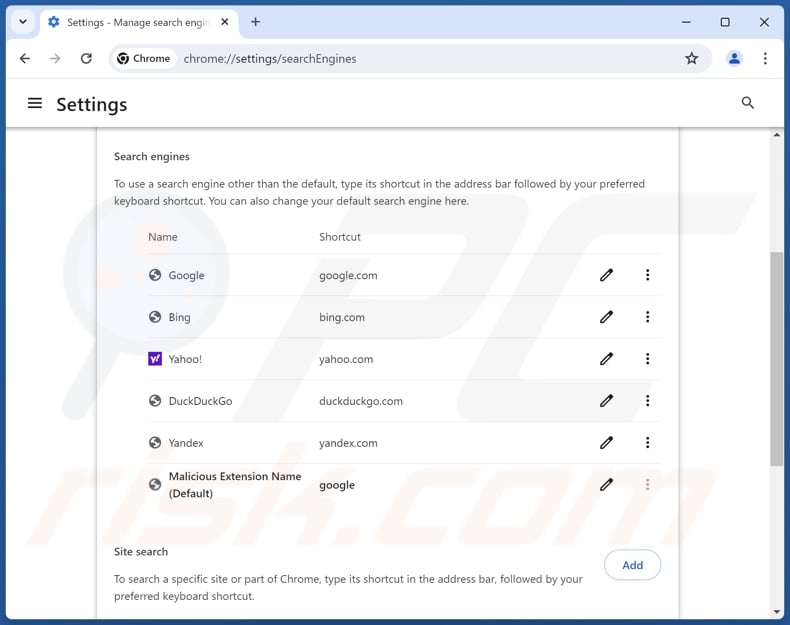
To change your default search engine in Google Chrome: Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Settings", in the "Search engine" section, click "Manage search engines...", in the opened list look for the browser hijacker promoted URL, when located click the three vertical dots near this URL and select "Delete".
(at the top right corner of Google Chrome), select "Settings", in the "Search engine" section, click "Manage search engines...", in the opened list look for the browser hijacker promoted URL, when located click the three vertical dots near this URL and select "Delete".
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
Optional method:
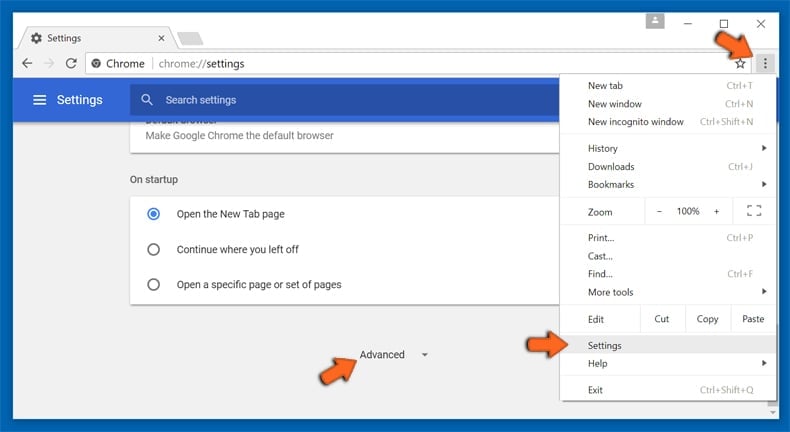
If you continue to have problems with removal of the google.com browser hijacker, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
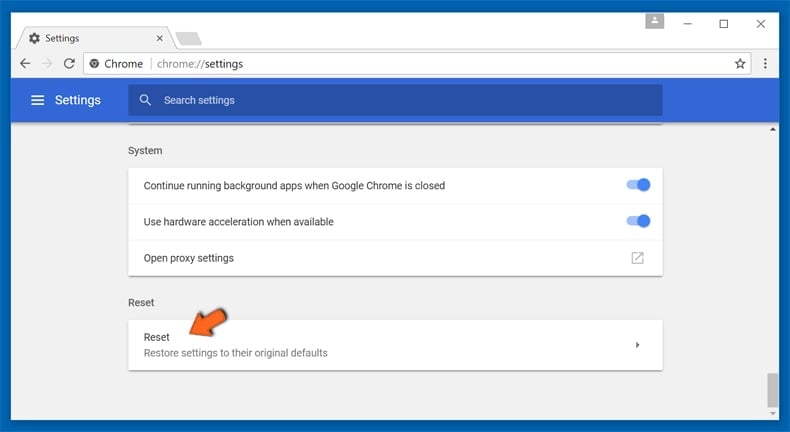
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
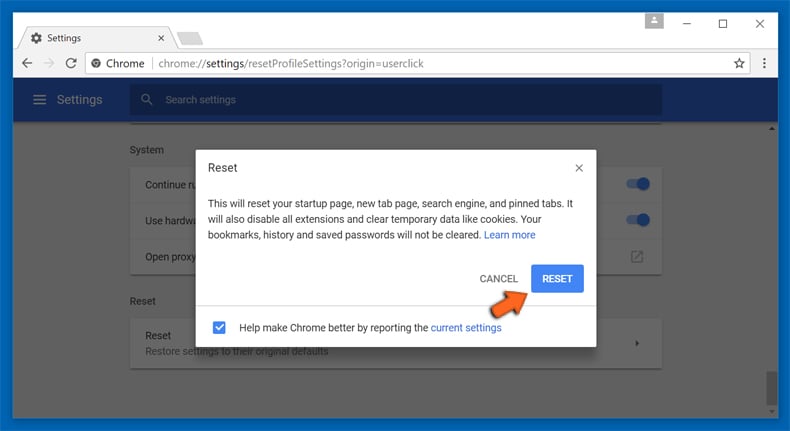
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
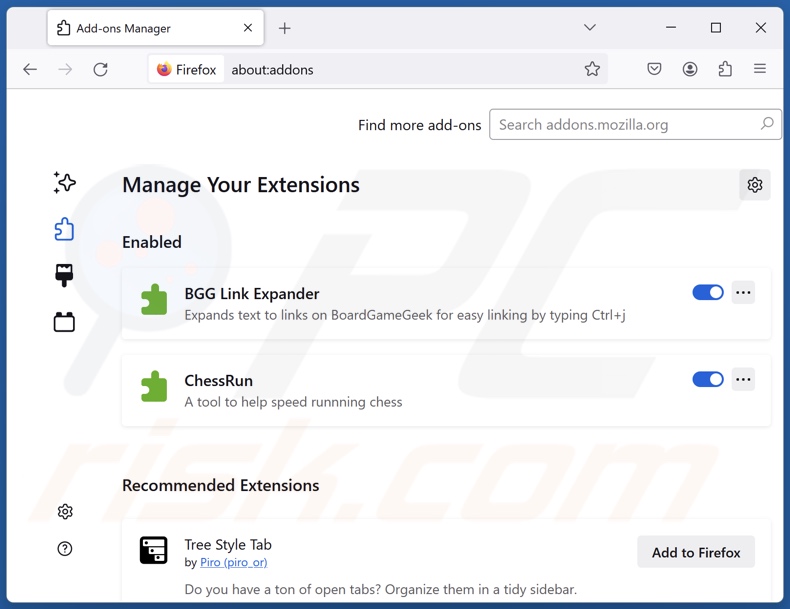
Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
Change your homepage:
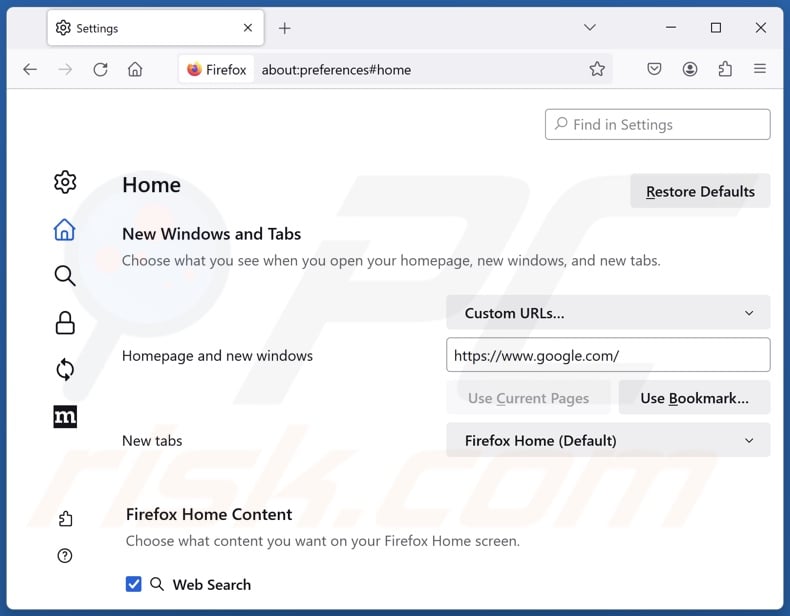
To reset your homepage, click the Firefox menu ![]() (at the top right corner of the main window), then select "Settings", in the opened window disable suspicious extensions, remove the browser hijacker promoted URL and enter your preferred domain, which will open each time you start Mozilla Firefox.
(at the top right corner of the main window), then select "Settings", in the opened window disable suspicious extensions, remove the browser hijacker promoted URL and enter your preferred domain, which will open each time you start Mozilla Firefox.
Change your default search engine:
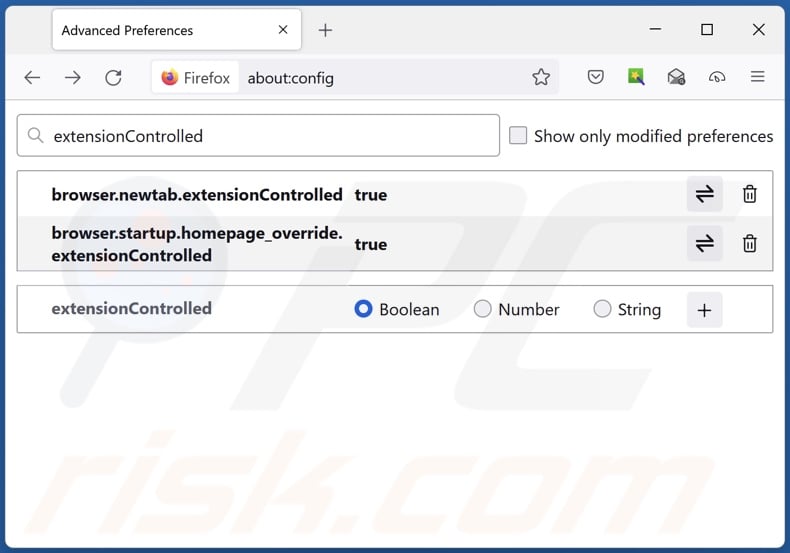
In the URL address bar, type "about:config" and press Enter. Click "Accept the Risk and Continue".
In the search filter at the top, type: "extensionControlled". Set both results to "false" by either double-clicking each entry or clicking the ![]() button.
button.
Optional method:
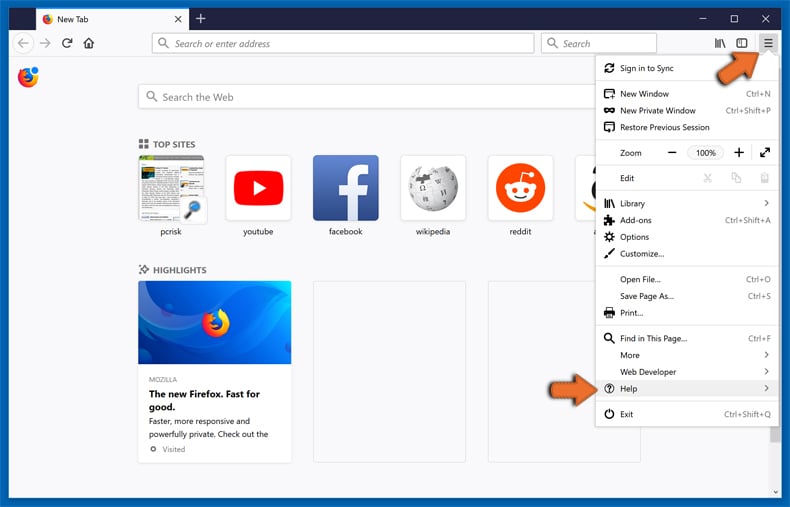
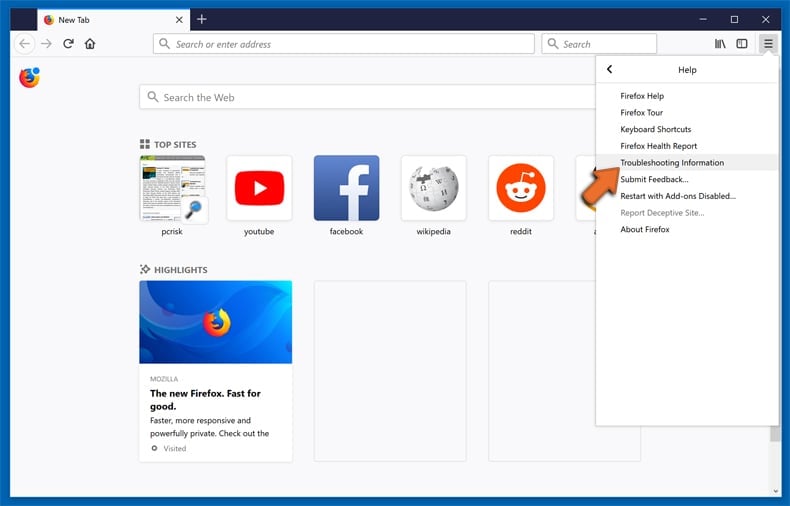
Computer users who have problems with google.com browser hijacker removal can reset their Mozilla Firefox settings.
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
Select Troubleshooting Information.
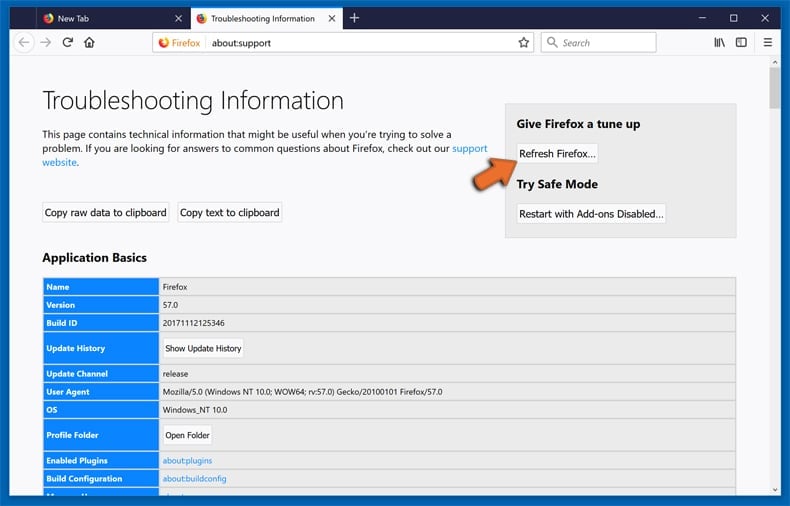
In the opened window, click the Refresh Firefox button.
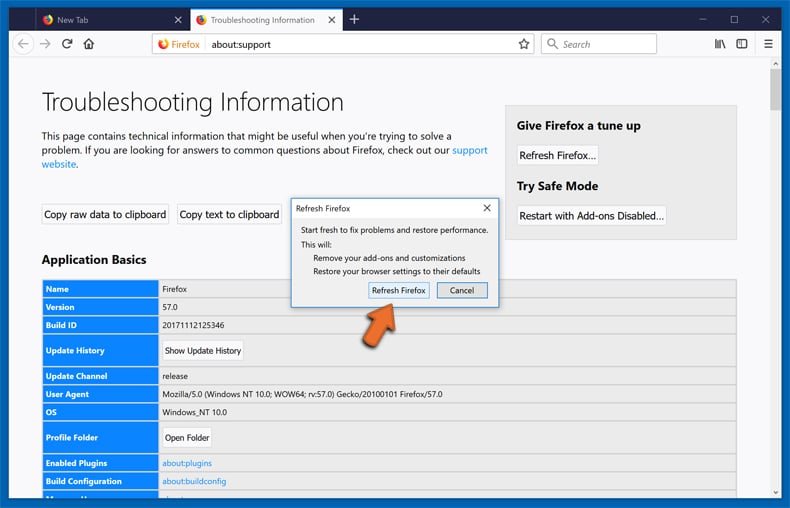
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
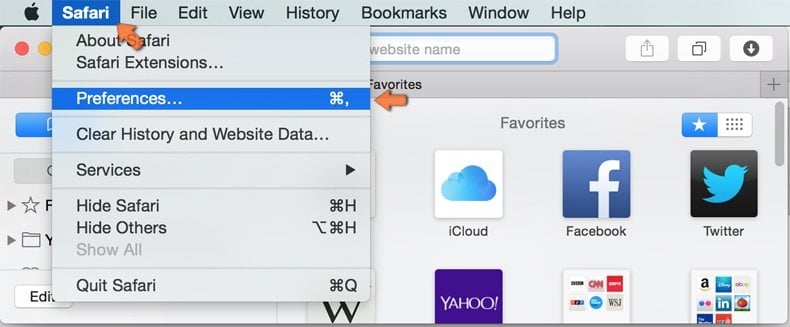
Make sure your Safari browser is active and click Safari menu, then select Preferences...
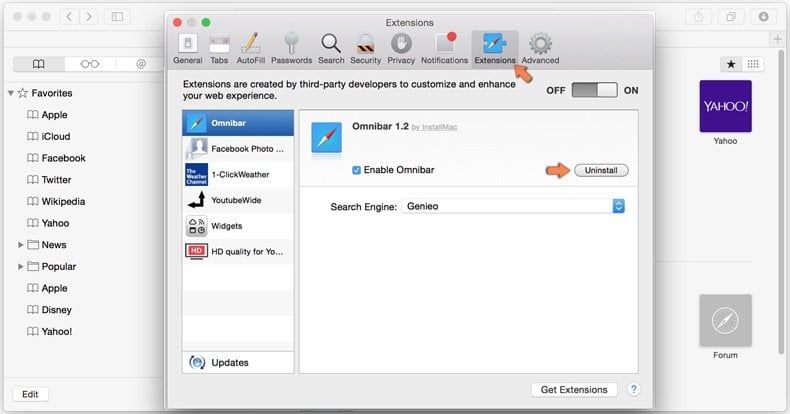
In the preferences window select the Extensions tab. Look for any recently installed suspicious extensions and uninstall them.
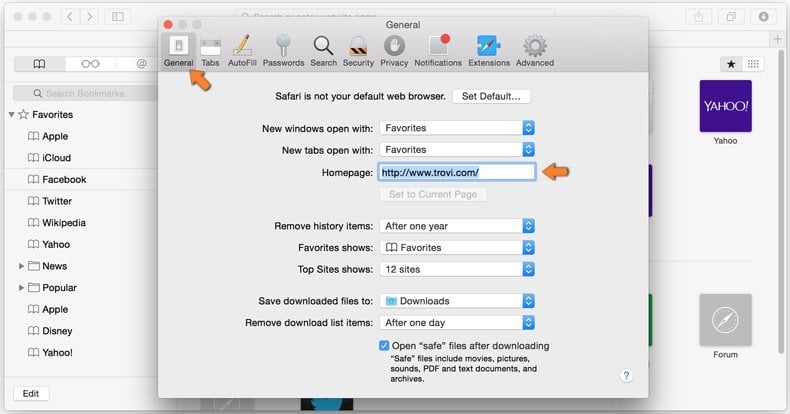
In the preferences window select General tab and make sure that your homepage is set to a preferred URL, if its altered by a browser hijacker - change it.
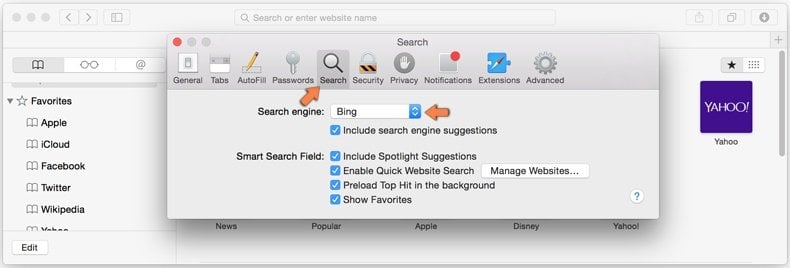
In the preferences window select Search tab and make sure that your preferred Internet search engine is selected.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
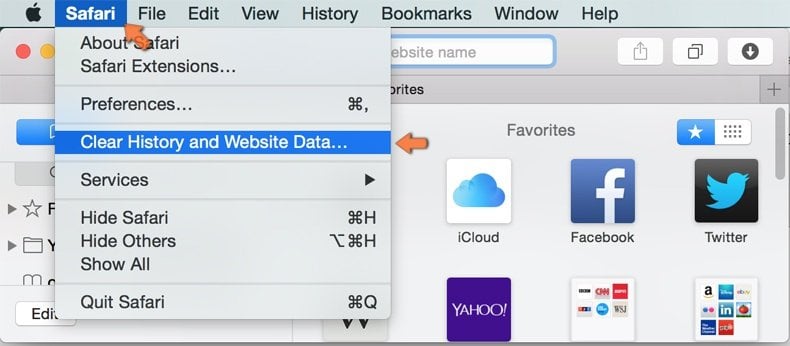
In the opened window select all history and click the Clear History button.

If you continue having problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
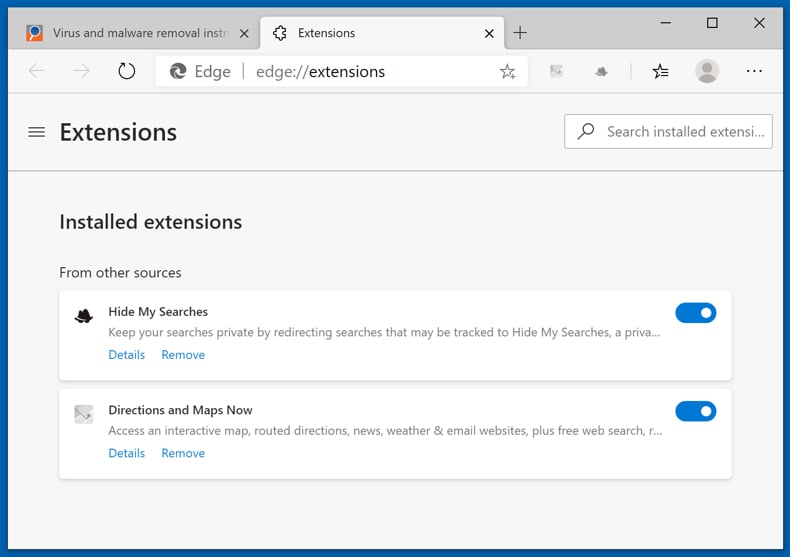
Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge), select "Extensions". Locate any recently-installed suspicious browser add-ons, and remove them.
(at the top right corner of Microsoft Edge), select "Extensions". Locate any recently-installed suspicious browser add-ons, and remove them.
Change your homepage and new tab settings:
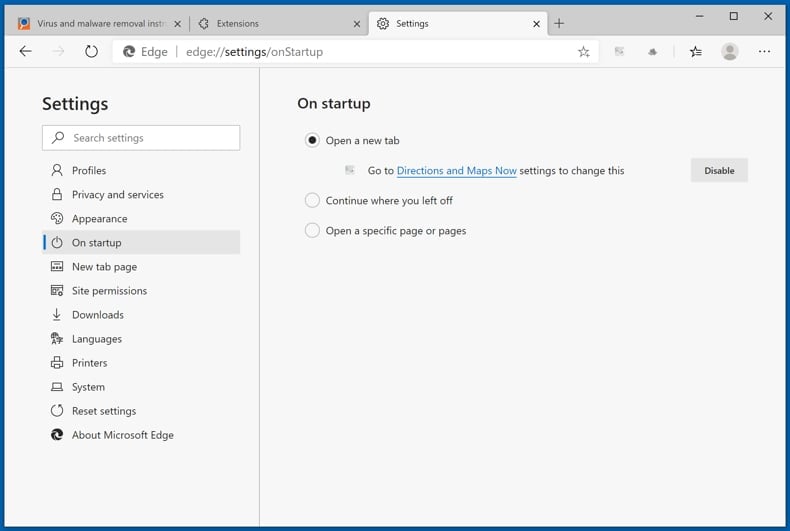
Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge), select "Settings". In the "On startup" section look for the name of the browser hijacker and click "Disable".
(at the top right corner of Microsoft Edge), select "Settings". In the "On startup" section look for the name of the browser hijacker and click "Disable".
Change your default Internet search engine:
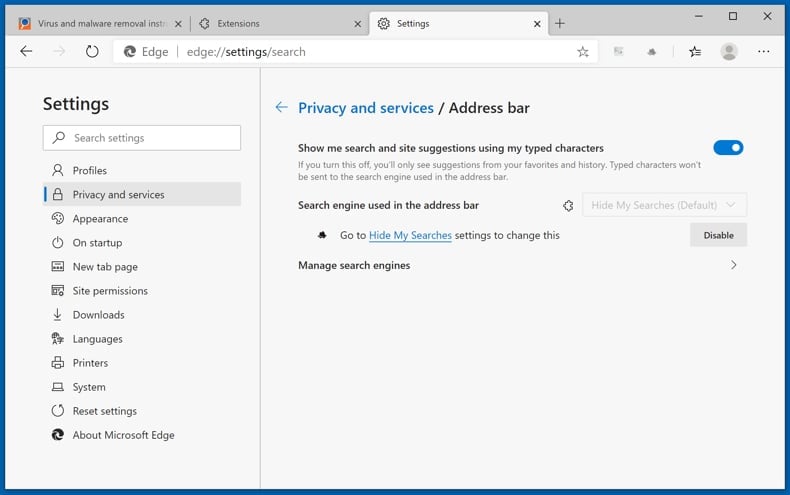
To change your default search engine in Microsoft Edge: Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge), select "Privacy and services", scroll to bottom of the page and select "Address bar". In the "Search engines used in address bar" section look for the name of the unwanted Internet search engine, when located click the "Disable" button near it. Alternatively you can click on "Manage search engines", in the opened menu look for unwanted Internet search engine. Click on the puzzle icon
(at the top right corner of Microsoft Edge), select "Privacy and services", scroll to bottom of the page and select "Address bar". In the "Search engines used in address bar" section look for the name of the unwanted Internet search engine, when located click the "Disable" button near it. Alternatively you can click on "Manage search engines", in the opened menu look for unwanted Internet search engine. Click on the puzzle icon ![]() near it and select "Disable".
near it and select "Disable".
Optional method:
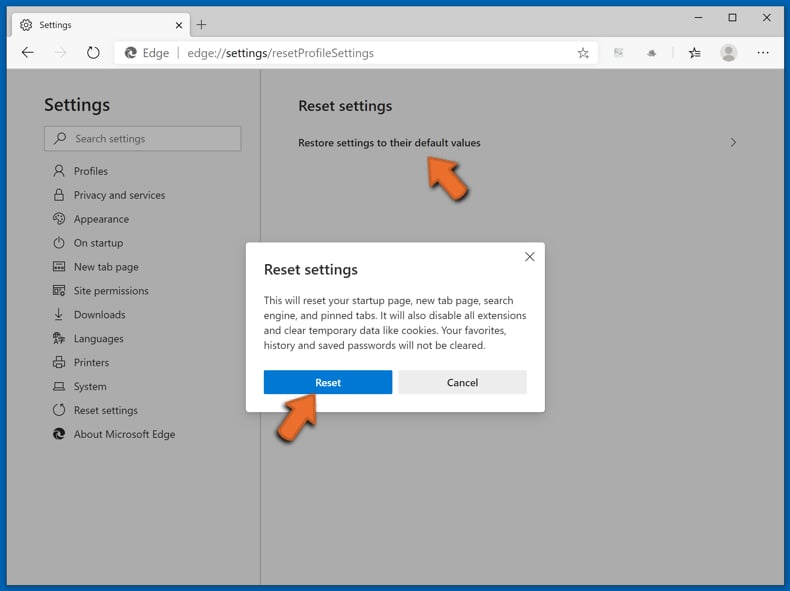
If you continue to have problems with removal of the google.com browser hijacker, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
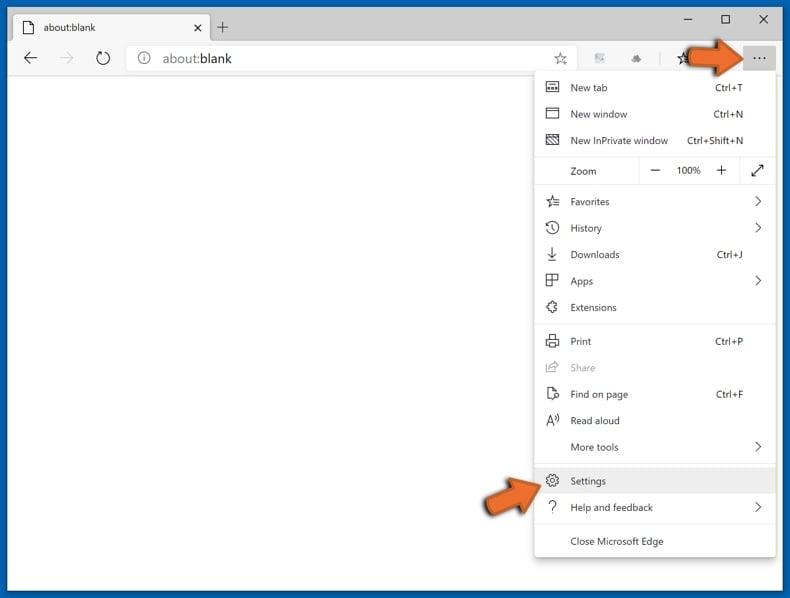
In the opened settings menu select Reset settings.
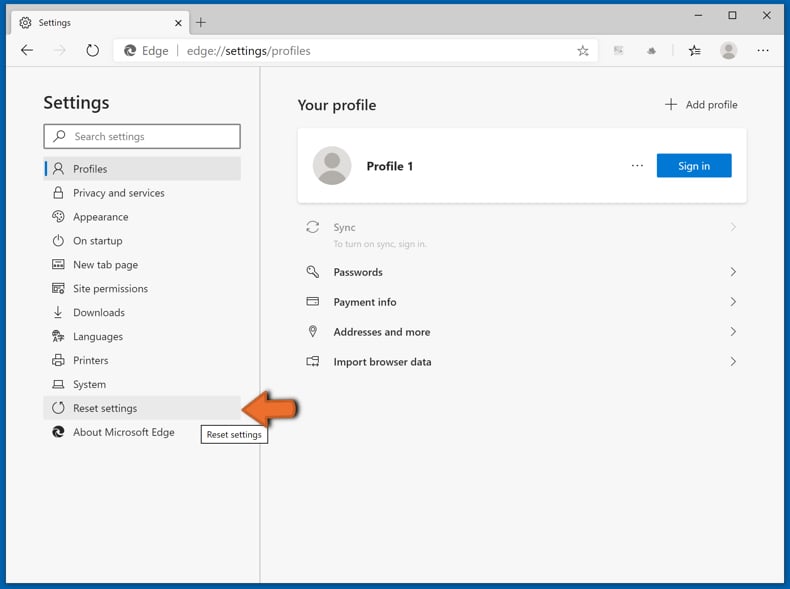
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Summary:
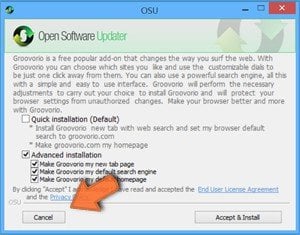 A browser hijacker is a type of adware infection that modifies Internet browser settings by assigning the homepage and default Internet search engine settings to some other (unwanted) website URL. Commonly, this type of adware infiltrates operating systems through free software downloads. If your download is managed by a download client, ensure that you decline offers to install advertised toolbars or applications that seek to change your homepage and default Internet search engine settings.
A browser hijacker is a type of adware infection that modifies Internet browser settings by assigning the homepage and default Internet search engine settings to some other (unwanted) website URL. Commonly, this type of adware infiltrates operating systems through free software downloads. If your download is managed by a download client, ensure that you decline offers to install advertised toolbars or applications that seek to change your homepage and default Internet search engine settings.
Post a comment:
If you have additional information on google.com browser hijacker or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
Why am I unable to use google.com?
If Google was your default search engine, but you experience redirects to a different website whenever you enter a search query into the URL bar, open a new tab/window or the homepage on your browser - that is most likely caused by a browser hijacker. Software within this classification modifies browsers to promote (mainly fake) search engines and generate revenue by collecting private data.
Why am I seeing a different URL when trying to use google.com?
This is likely a "drive-by" redirect caused by a browser hijacker that first redirects to a suspicious site, which then redirects to Google. Browser-hijacking software primarily promotes fake search engines that lead to genuine ones (e.g., google.com) due to their inability to generate search results.
Why am I forced to use google.com?
As mentioned in the previous answer, browser-hijacking software promotes fake search engines that tend to redirect to legitimate ones (e.g., google.com). Fraudulent search engines typically collect (and sell) information about their visitors, but since they are unable to provide search results - they redirect to genuine ones as a disguise.
Is being forced to visit google.com or a different website a threat to my privacy?
Privacy issues when visiting google.com are not a primary concern. Browser hijackers that cause redirects to various search engines are known to collect users' data. Data-tracking behavior is also typical of fake search engines that are often part of the redirection chains caused by hijacker software. Furthermore, the gathered information can be particularly sensitive. Therefore, the threat does not originate from visiting google.com but rather from the software forcing users to do so.
How did a browser hijacker infiltrate my computer?
Browser hijackers are distributed via software bundling, misleading promotional webpages, unofficial and freeware download sites, deceptive browser notifications/ intrusive advertisements, online scams, fake updaters/installers, and so on.
Will Combo Cleaner help me remove browser hijackers?
Yes, Combo Cleaner will scan your device and eliminate installed browser-hijacking applications. However, it must be noted that manual removal might not be a perfect solution when multiple browser hijackers are present. In such cases, it is possible for browser hijackers to re-install one another if they are not all eliminated at the same time. Furthermore, removal-related settings might be inaccessible while this software is on the system. Therefore, it is crucial to remove browser hijackers thoroughly and all at once.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate










▼ Show Discussion