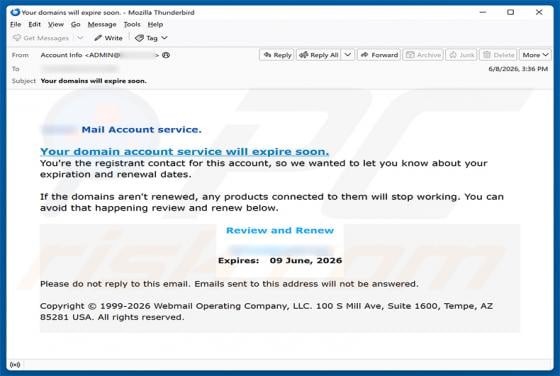
Your Domain Account Service Will Expire Soon Email Scam
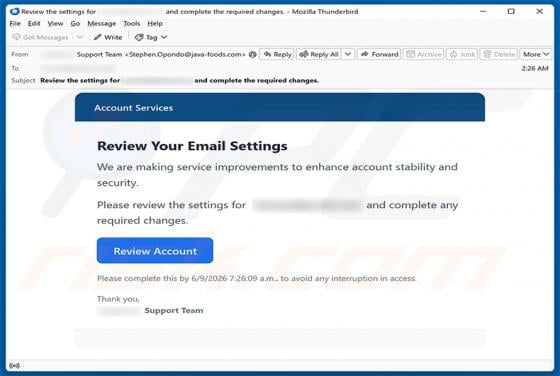
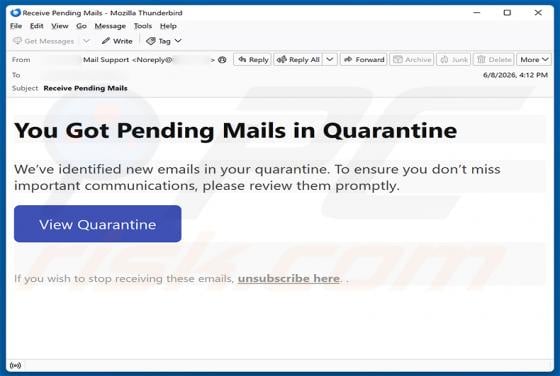
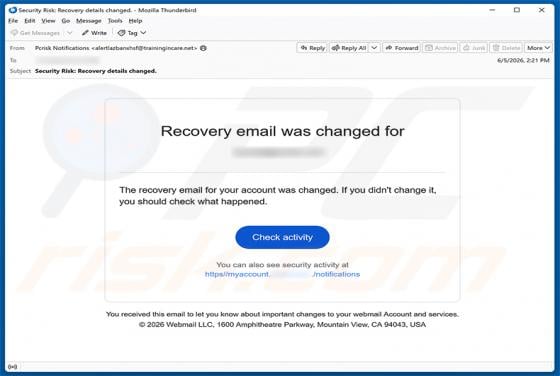
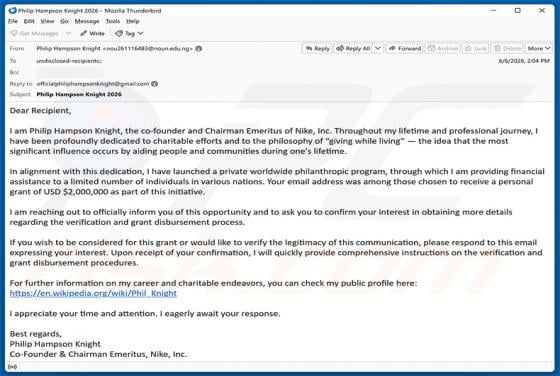
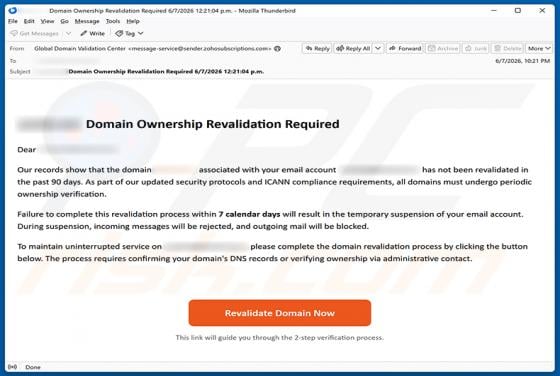
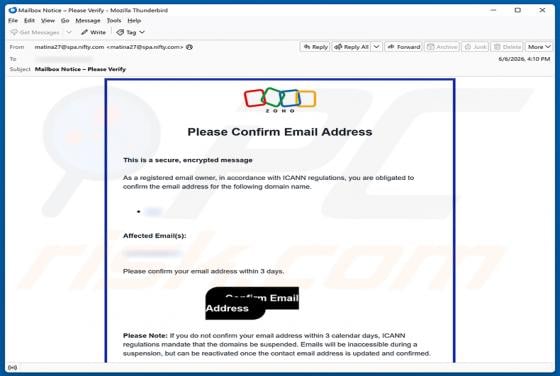
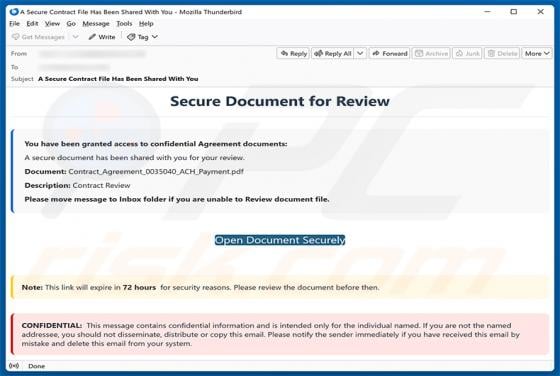
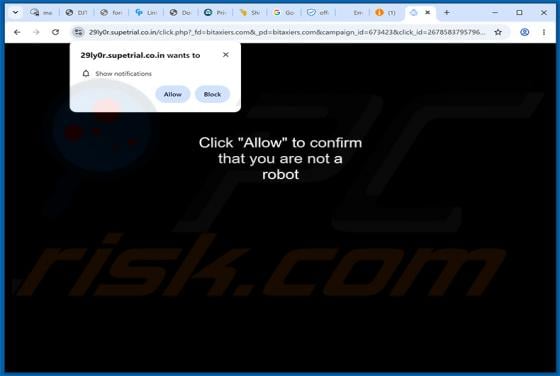
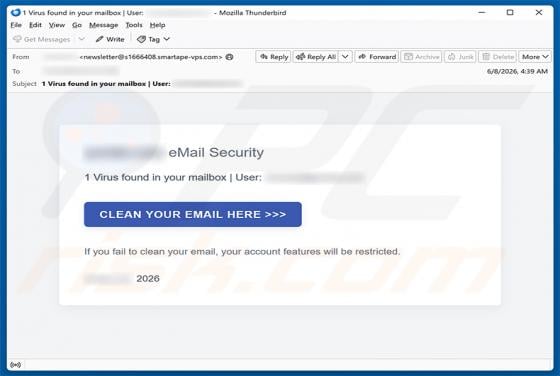
We have examined this email and determined that it is a phishing scam. It is disguised as an urgent notice from a webmail service provider, falsely warning that the recipient's domain account is about to expire. The goal is to trick users into visiting a fraudulent website where their login creden