Needle Stealer
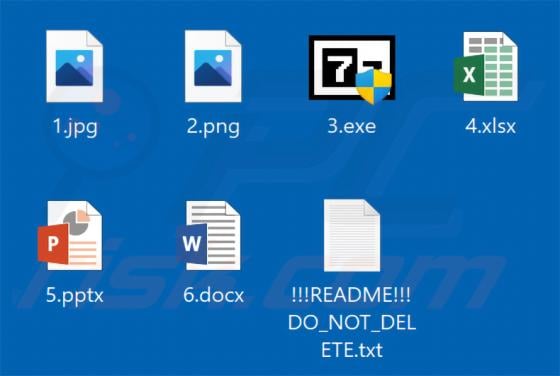
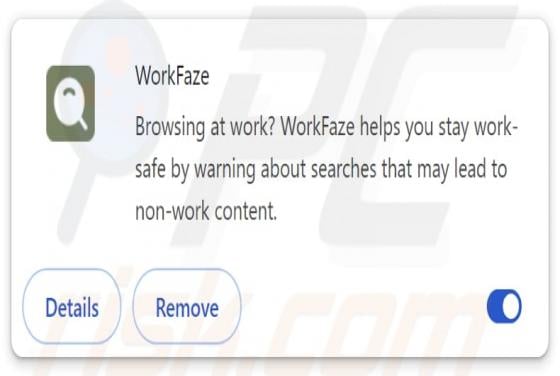
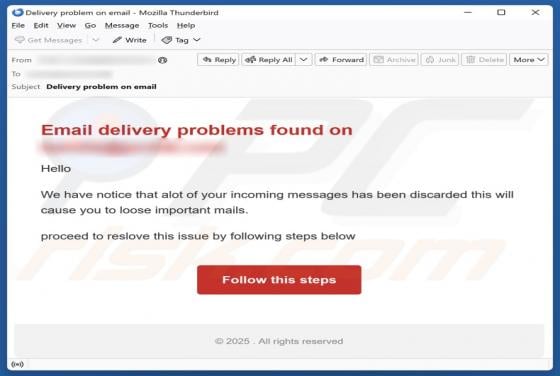
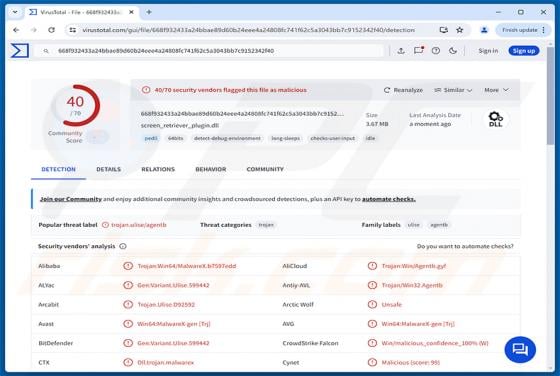
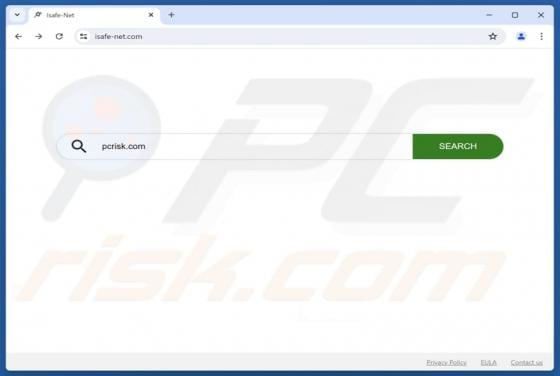
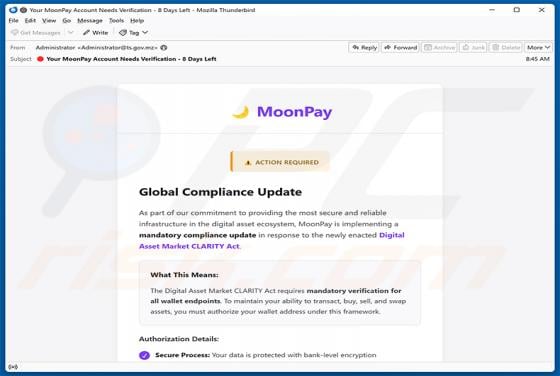
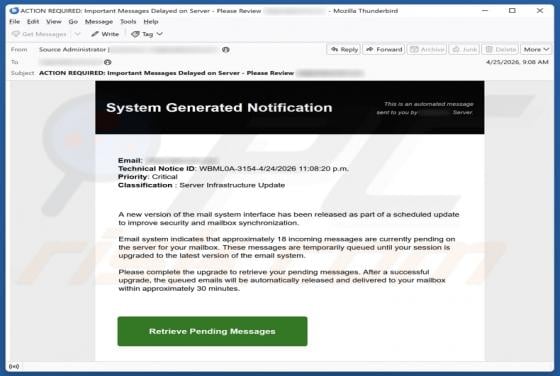
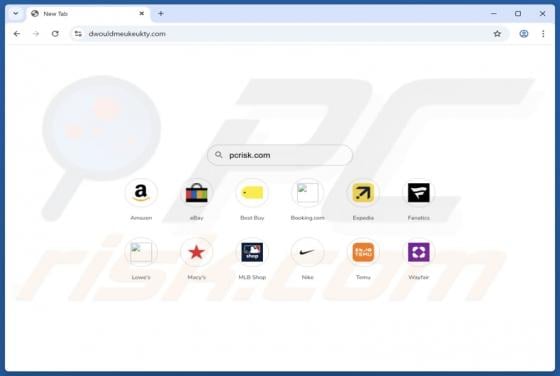
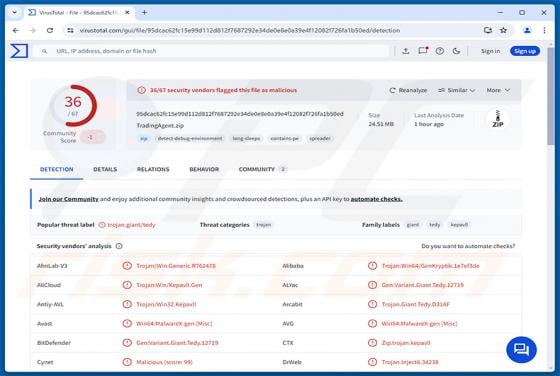
Needle Stealer is a modular information stealer written in Golang that harvests saved browser credentials, cryptocurrency wallet files, messaging app data, and other sensitive files from infected computers. It also installs a companion malicious browser extension that gives attackers real-time con