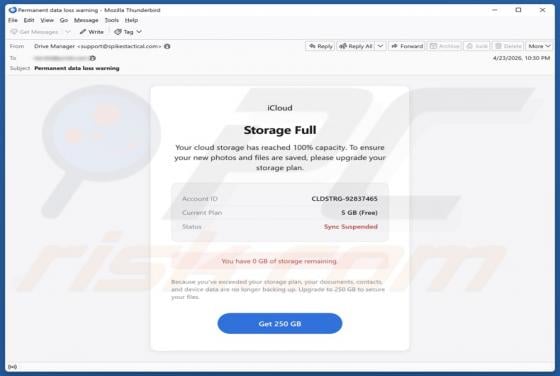
iCloud Storage Full Email Scam
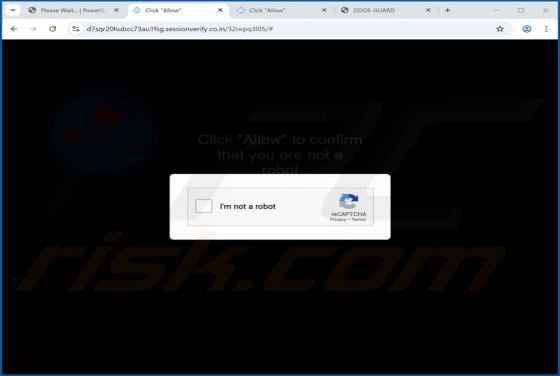
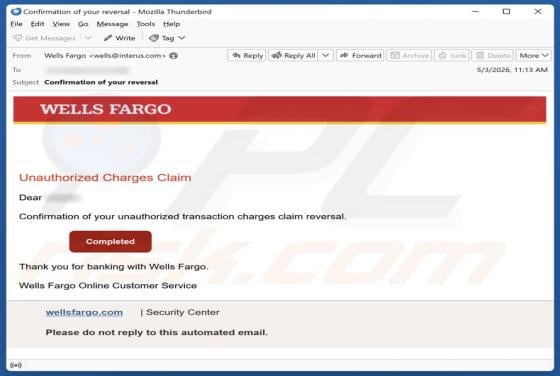
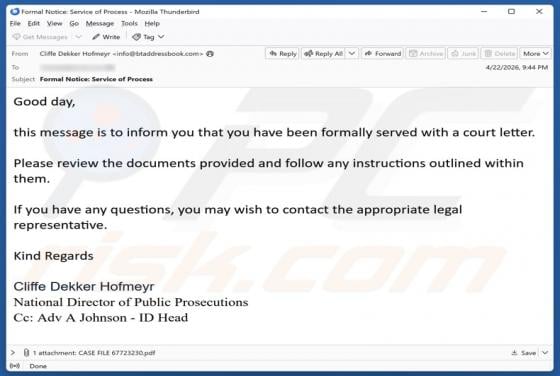
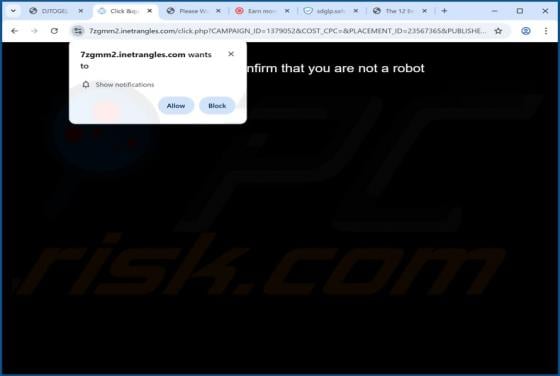
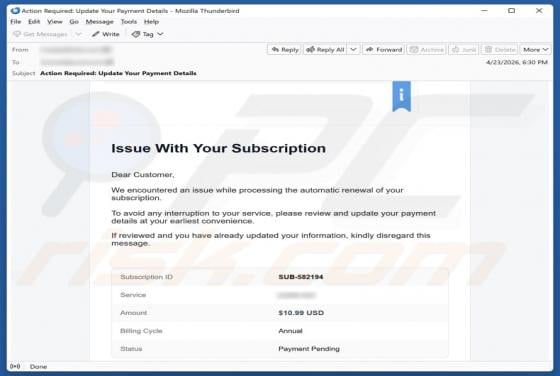
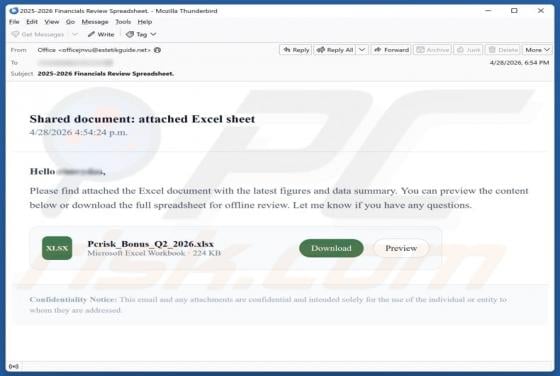
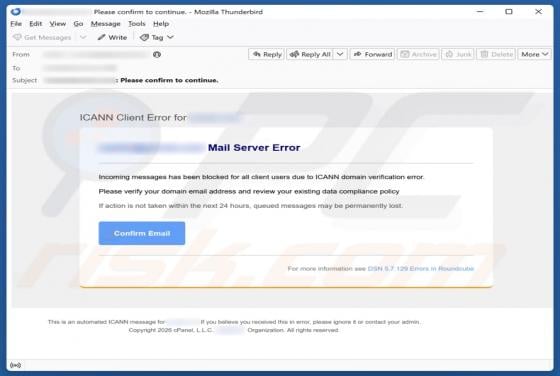
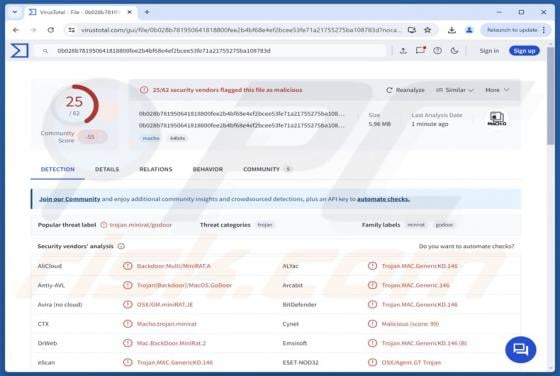
After analyzing the message, we identified it as a deceptive email impersonating a cloud service provider. Its purpose is to lure recipients to fake websites that present fabricated alerts and misleading instructions designed to manipulate users into performing specific actions. Recipients are adv