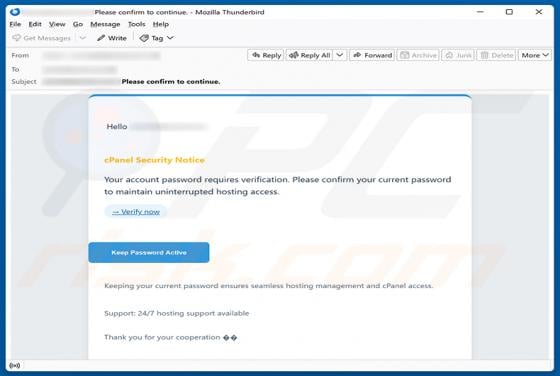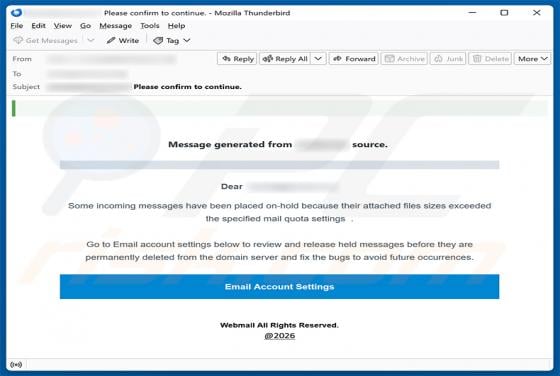
Attached Files Sizes Exceeded Mail Quota Settings Email Scam
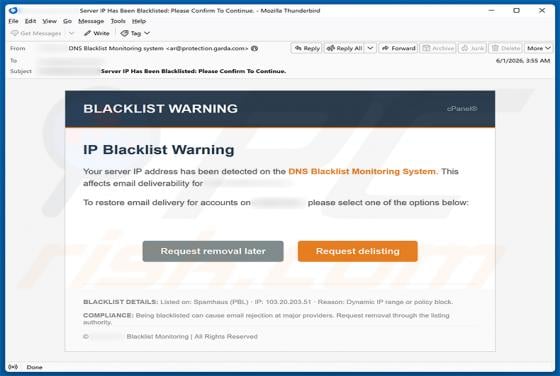
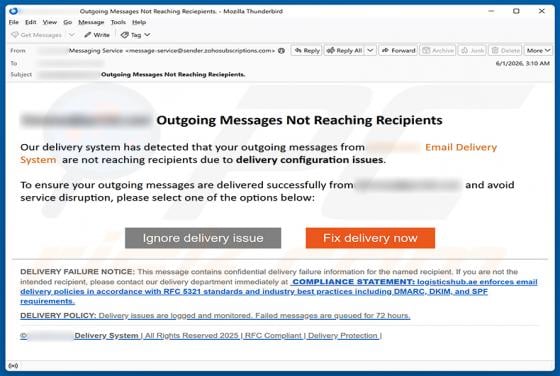
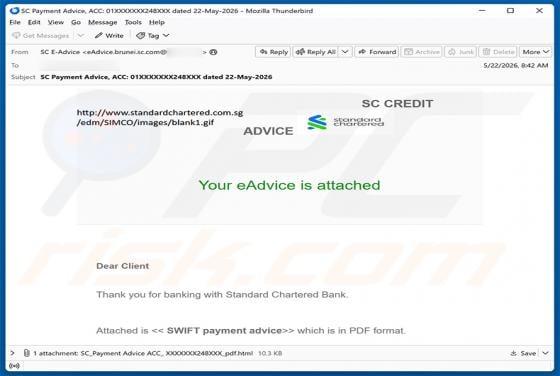
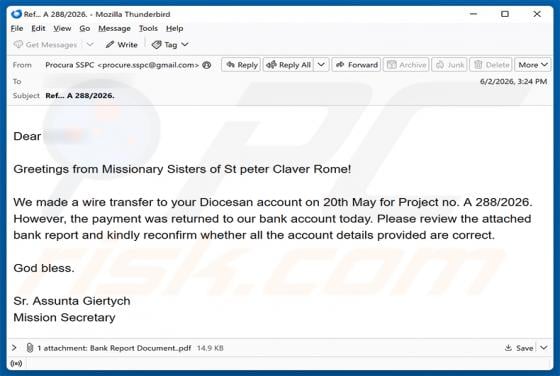
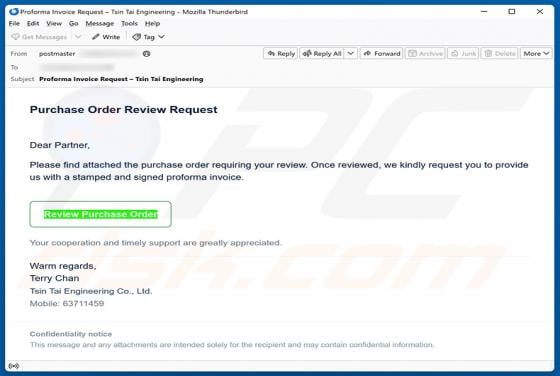
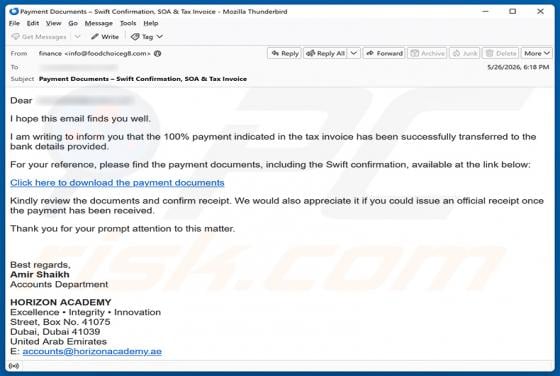
After inspecting this email, we determined that it is a scam. The message is designed to appear as an automated alert from a webmail service, claiming that some incoming messages have been placed on hold. It is a phishing email intended to trick recipients into entering their email account credent