Brilliant Check Browser Hijacker (Mac)
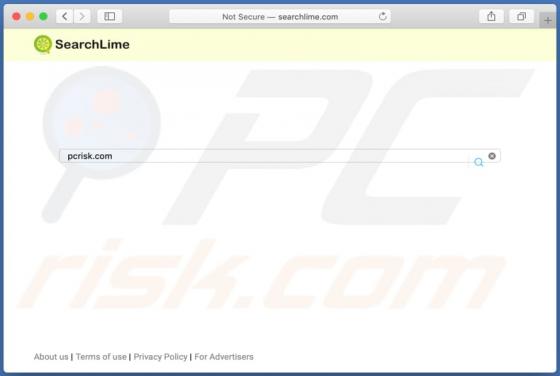
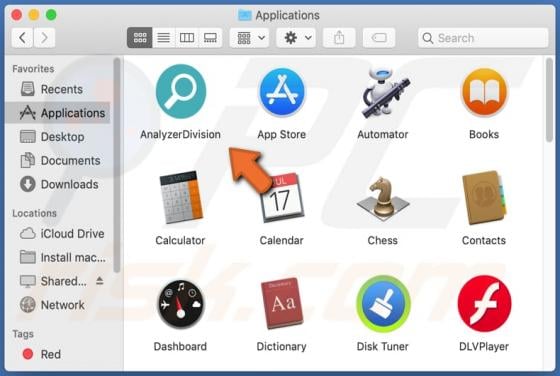
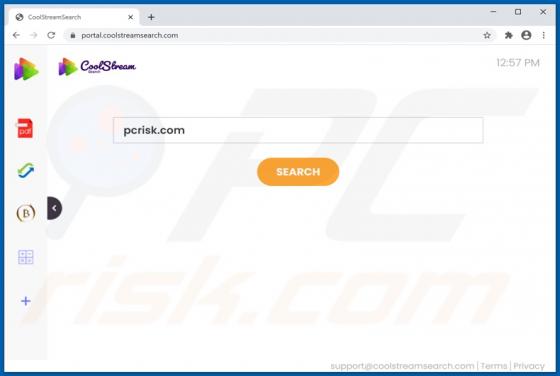
Identical to Searchlee, and similar to countless others, Brilliant Check is a browser hijacker. Following successful infiltration, it changes browser settings in order to promote brilliantcheck.com, a fake search engine. In addition, Brilliant Check operates as adware - it injects various advert