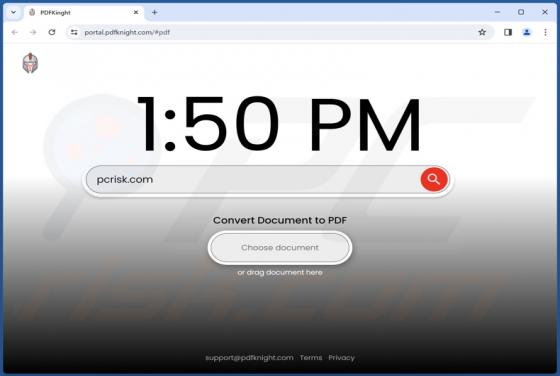
PdfKnight Unwanted Application
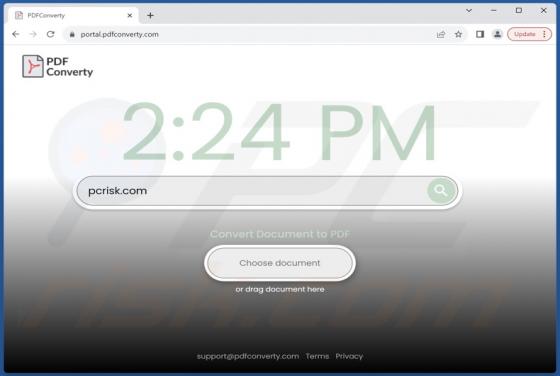
Our research team discovered the PdfKnight PUA (Potentially Unwanted Application) while inspecting suspicious websites. According to the webpage promoting this app, it supposedly operates as a file format converter that can convert PDFs to Doc format documents. Our analysis revealed that PdfKnigh