Egregor’s Rampage Continues
Since Egregor’s discovery in late September early October of 2020, the ransomware has wrecked a bloody toll in the short time it has been actively claiming victims. The first few of which included Barnes and Noble, Crytek, and Ubisoft. Since the apparent retirement of the Maze ransomware gang, Egregor has been quick to capitalize on the gap left in the market by Maze’s departure.
Not only has the group behind Egregor been quick to fill the gap left by the Maze gang, but they have also been quick to adopt the tactics that made Maze so successful. Namely the human-operated tactics involving targeting large organizations with complex networks increases the likelihood of demanding a bigger ransom once critical network assets are encrypted resulting in increased downtime.
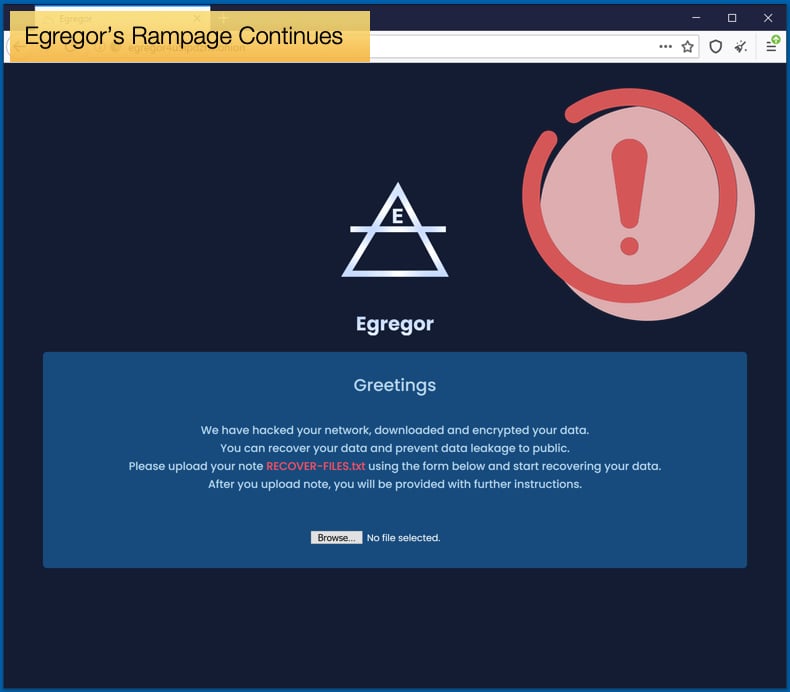
Secondly, Egregor was quick to adopt the double-extortion tactic which involves the stealing and subsequent releasing of sensitive data from victims. The data is released if the victim fails to pay the ransom on time. To facilitate the leaking of sensitive data Egregor has set up a Dark Web site that announces victims and when data will be released. Often to prove that they’ll make good on their threats the gang releases a small portion of data that identifies the victim.
Since making headlines with the first three major victims mentioned above, the gang has only picked up the pace. Security researchers at Digital Shadows have been tracking Egregor’s activity and found that in the last quarter of 2020 the gang has seemingly found a higher gear. In a report published by the firm by the middle of November, the gang has already claimed 71 victims across 19 economic sectors. Most victims being based in the US, roughly 83% of the total number of victims to date.
Given the quick rise in victim numbers as well as the spread across several economic sectors, researchers believe that the ransomware may have been in development for some time before being released into the wild. This view is further supported by the rate of adaptation to varying targets the group has achieved. Speaking to ZDNet, Lauren Palace, an analyst at Digital Shadows, noted,
“The level of sophistication of their attacks, adaptability to infect such a broad range of victims, and significant increase in their activity suggests that Egregor ransomware operators have been developing their malware for some time and are just now putting it to (malicious) use…Given their sophisticated technical capabilities to hinder analysis of malware and target a large variety of organizations across the ransomware landscape, we can only conclude that the Egregor ransomware group will likely continue in the future, posing more and more of a risk to your organization,”
Egregor Partners with QBot
As if to highlight what researchers have noted, Egregor recently partnered with the banking trojan QakBot, also sometimes referred to as QBot or QuakBot. Previously, another prominent ransomware strain has been seen partnering with other malware operations for better distribution capabilities, that being Ryuk and TrickBot. Previously, QakBot had partnered with ProLocker but seems to have ditched them for Egregor’s rising star. Like with partnerships researchers have seen in the past involving ransomware strains and banking trojans, it is believed that QakBot will initially infect a machine and once the trojan is done access to the machine is handed over to the ransomware gangs to then encrypt data and demand a ransom.
QakBot is a Windows malware specifically designed to steal banking credentials and other banking related information. Further, QakBot will also steal Windows Domain credentials which in turn can then be used by ransomware operators to gain access to the compromised network. QakBot’s main method of distribution is via spam phishing emails containing malicious Excel documents. Once the ransomware operators take up the task, they will often use CobaltStrike, a penetration testing tool, to spread laterally across the network. Only once access is gained to the domain admin account is the ransomware deployed. This is an effective tactic for causing the most amount of damage in relatively short time periods, sometimes entire networks can be rendered useless in an hour or two.
Detailing this partnership between QakBot and Egregor, security firm Group-IB noted seeing Egregor being assisted in October by QakBot, rather than the expected ProLocker. From a business perspective, this does make sense seeing how rapidly the ransomware has stepped up operations. Even the tactics used by ProLocker and Egregor were incredibly similar once access to the compromised machine was granted by QakBot. Researchers stated,
“Also we've seen the same script to enable comfortable lateral movement - "rdp.bat". It was used by the threat actors to modify registry and firewall rules to enable connections via Remote Desktop Protocol…To compromise the whole network infrastructure, the threat actor used Cobalt Strike – an extremely popular post-exploitation tool we've seen in almost 70% of incidents involving Big Game Hunting operations this year…In some cases, the threat actors also distributed Qakbot through the network via PsExec, just like in cases with Prolock we observed in the past, they use a file named "md.exe" – that is the Qakbot binary.”
Despite the similarities in tactics they are proving to be incredibly effective. This effectiveness has allowed Egregor significant room to maneuver as well as charging incredibly high ransoms. Researchers have seen ransoms of up to 4 million USD in Bitcoin demanded by the ransomware gang. In defending against Egregor, those tasked with doing this should note that many of Maze’s affiliates are believed to be working with Egregor now, so the same tactics employed to defend against Maze should likewise also be adopted by those defending against Egregor. While Egregor has proven its ability to attack across economic sectors based on analysis the gang seems to favor targeting organizations that fall in the manufacturing and retail sectors.
Retail Giant Hit by Egregor
To prove the point that retail is a favored target for Egregor if the attack on Barnes and Noble wasn’t enough, the gang successfully attacked retail giant Cencosud. The Chilean-based multinational is one of the largest retail companies in Latin America, with over 140,000 employees and 15 billion USD in revenue for 2019. Cencosud manages a wide variety of stores in Argentina, Brazil, Chile, Colombia, and Peru. Their portfolio includes Easy home goods, Jumbo supermarkets, and the Paris department stores.
According to reports, the retail giant was hit on November 14, 2020, and resulted in the encryption of devices across several outlets and impacted the company’s operations. Retail stores were still open but they were warning customers that they could not accept “Cencosud Card” credit cards, accepting returns, or allowing the pickup of web purchases because of the attack. After news of the attack broke, Bleeping Computer managed to get a copy of the ransom note, which is the same note seen in other Egregor attacks. Further, printers and other devices began printing out the ransom note once data encryption had taken place. This is a known quirk of Egregor in that the ransomware that once the ransom note is dropped instructions are sent to printers on the network to print the ransom note.
As to how exactly Egregor is capable of compromising networks without the assistance of QakBot, only theories exist now due to the ransomware still being new to the scene despite the impact it has made. Many of the tactics used to defend against other human-operated ransomware will go a long way to shore up an organization’s defenses. Organizations should employ multi-factor authentication wherever possible. If password and username combinations are compromised via phishing attempts or brute-force attacks at least there is an added layer of security preventing further compromise.
Like with all ransomware strains, having a robust backup policy with several fallbacks can prevent victims from feeling the true might of a well-executed ransomware attack and can recover faster resulting in less downtime and cheaper recovery costs. Further, having good backups will help prevent the need to pay the ransom, which is never advised to do for several reasons including funding criminal activity. Lastly, please make sure updates are downloaded and installed upon release.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion