Researchers Discover a Ransomware Mystery
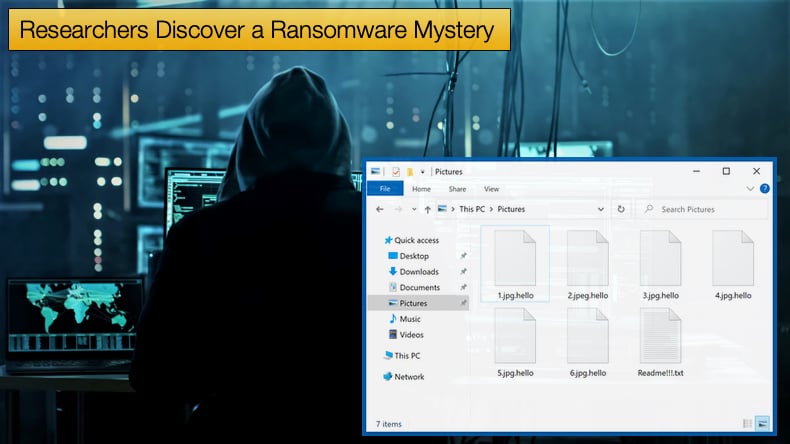
Security firm eSentire published an article detailing an odd ransomware incident. In summary, the incident is odd as it used advanced techniques to gain initial access and compromise the target’s network. However, the ransomware dropped, Hello, is regarded as fairly unsophisticated. This provided researchers with a few head-scratching moments.
The victim in the instance observed was a testing company that evaluates hundreds of products from around the globe. This implies that during testing the company has access to a ton of intellectual property, making the company a high-profile target for attackers. The attack was also determined by researchers to be a hands-on-keyboard attack.
This is a relatively new term and is used to describe threat actors who actively explore the target network rather than rely on automated scripts to do the work for them. In many ways, it is similar to the now commonly used term human-operated, used to describe many modern ransomware operations. Some might argue it is exactly the same.
The term hands-on-keyboard is gaining traction in the InfoSec community following a two (one; two) part analysis of the LemonDuck crypto miner that has evolved to make use of the technique published by Microsoft.
The attack also made use of known tactics and malware tools used by Chinese threat actor APT27, also known as Bronze Union, Emissary Panda, Iron Tiger, Lucky Mouse, or TG-3390 depending on which law enforcement agency or security firm is writing about the group.
One such tactic is the use of a SharePoint exploit along with the China Chopper malware. There are several other similarities between the threat group and the threat actor in this incident, possibly linking APT27 directly, however, the researchers were quick to point out that the use of similar tactics and techniques may be part of a false flag operation. Researchers noted,
“Of course, the attack could be part of a false flag campaign. The attack chain borrows from publicly disclosed Chinese, nation-state tools and procedures, including a SharePoint exploit and the use of a popular tool called China Chopper. Additionally, the Hello Ransomware, which the threat group is known to deploy into the victims’ environment, does not appear to have a leak site or blog and the ransomware is not delivered under a typical Ransomware-as-a-Service model.”
Looking at the incident in more detail, the attack was detected when the threat actor deployed, like so many other attacks today, a Cobalt Strike Beacon. To try and keep the beacon's deployment undetected the threat actors masqueraded it as a Kaspersky service. It was further noted by researchers that,
“Further investigation revealed that the target’s compromised server was hosting an out-of-date version of the Windows operating system and a vulnerable SharePoint instance. Both initial access and post-compromise behavior of this attack have previously been observed in recent Hello Ransomware incidents and resemble attack chains previously attributed to Chinese nation-state actors such as Emissary Panda and/or UNC215.”
Answering a definite yes or no with regards to APT27, like always, is difficult. Chinese APT groups have been seen to deploy ransomware recently, so if proved that APT27 is behind the attack it is not without precedent. APT27 is believed to be behind several attacks abusing Windows BitLocker to encrypt drives.
That being said FireEye recently published a report stating that it had not seen APT27 related activity since 2015, actively challenging the idea that APT27 is behind the above-mentioned incident or the several others investigated by other security firms.
The Curious Case of Hello
The use of the Hello ransomware is puzzling for a variety of reasons. Unlike many of the world's top ransomware threats, Hello is not offered as a ransomware as a service (RaaS). It makes no use of affiliates to handle compromising networks and encrypting data.
Unlike many other ransomware gangs, it does not appear that those deploying the ransomware either steal data or make use of a dedicated leak site so common in double extortion ransomware campaigns today. The history of Hello dates back to after the WannaCry incident, and typically seen as derivative of WannaCry, complete with the same flaws that its progenitor had.
At the time when WannaCry brought the world's attention to ransomware analysis of the ransom note led some to believe it was of Chinese origin.
However, WannaCry has been attributed to, through a US Indictment to the Reconnaissance General Bureau (RGB), a military intelligence agency of the Democratic People’s Republic of Korea (DPRK). The three men indicted were shown to have spent time in China and Russia. Researchers noted,
“Interestingly, the encryption software used to create Hello Ransomware was only available in two languages in 2017: English and Russian. It is not clear whether the 2017 variant of Hello Ransomware and the current variant are part of the same operation. In 2017, Hello Ransomware charged a flat rate of .05 Bitcoin (~$200 USD at the time) but an associated wallet (17pXroP4MruitJzpTa88FAPAGD5q5QAPzb) has no transaction history. The Hello Ransomware operators have since updated their ransom letter template and no longer have a fixed fee. In place of using a wallet address, in 2021, the operators began using anonymous email services ProtonMail and Tutenota, as well as the messaging app, WickrMe, to communicate with its victims.”
While it might be still too early to tell if APT27 was responsible the incident investigated by eSentire researchers did not that there appears to be evidence of increased use of ransomware by Chinese APT groups. This is in contrast to the previously held belief that nation-state activities differed from financially motivated cybercrime groups.
However, since the VHD ransomware was linked to North Korean threat group Lazarus the lines have blurred considerably. Some researchers believe that this shift in tactics, which is slowly been seen in China as well, is done in attempts to cover larger espionage operations by directing the attention of defenders away from a mission's objectives, effectively mudding the water. Researchers noted,
“At least two countries and one security company loyal to Russian national interests have accused China of participating in the booming ransomware market. Most recently (July 2021), the Biden administration claimed that China participated in ransomware extortion campaigns against U.S. companies. Before that (May 2021), Taiwan accused China’s Winnti threat group of participating in a ransomware attack on Taiwanese oil infrastructure. At the end of 2020, Positive Technologies (a Russian IT company) attributed an attack to Emissary Panda that used a unique ransomware strain, which Positive Technologies dubbed Polar Ransomware. This was detailed by Security Joes in a report highlighting China’s interest in ransomware (Figure 2). Positive Technologies has since been accused by the U.S. of supporting national interests alongside sanctions against Russia.”
Again, eSentire researchers did not that the use of APT27 tactics and techniques may just be part of an elaborate ruse to make attribution that much more difficult.
The incident observed poses a unique mystery to researchers who while having provided evidence are still left wondering what the motives or purposes behind the attack might be. Answering if the attack is financially motivated or part of a wider espionage campaign might prove to be all but impossible in the near term.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion