Hello, Sacrifice. This Is My Last Warning!!! Email Scam
Phishing/ScamAlso Known As: Hello, Sacrifice. This Is My Last Warning!!! spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "hello, sacrifice. This is my last warning!!!"?
Scammers use the "hello, sacrifice. This is my last warning!!!" spam email campaign to threaten people by claiming that they have obtained a compromising video of the recipient, which they will proliferate if their demands are not met. Typically, they urge people to pay a ransom in Bitcoins.
As scammers claim in the "hello, sacrifice. This is my last warning!!!" email, your computer is supposedly infected with a trojan virus and your private information and contacts list have been stolen. Furthermore, they claim that they have used your computer webcam and captured a video of your "onanism".
According to them, if you do not pay them 600 USD in Bitcoins during within 30 hours, they will proliferate this video to all of your contacts. They also claim that they can monitor your activity while you are using your computer and they will know if you will try to deceive them.
Note that none of these spam emails should be trusted or taken seriously. Scammers send them to many people in the hope that a certain percentage will be fooled. Furthermore, the people behind this scam use a 'spoofing' method that allows them to falsify the sender's email address.
Therefore, it may seem that the recipient has received an email from herself/himself. Note that your computer is not infected and there is no danger of being humiliated by scammers proliferating an embarrassing video. All claims within the "hello, sacrifice. This is my last warning!!!" message are false.
| Name | Hello, Sacrifice. This Is My Last Warning!!! Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Cyber Criminals Cryptowallet Addresses (Bitcoin) | 18yeC7HGmFnvVBPrQHmuuW49AtiWGT9CsW, 1HW7CJqbS16uCttUQMQUdcXWf1vvLtgEBk, 18844y2xjXPXPLjxDGf3rd8bsgfnaH292d, 17CweXSXfxdvCNEmccMuhtY4d8N1uJFjT3, bc1qk0vedazh9u423vsz5y80rcym4a8qxyjjm5q53k, bc1qs8x8m8cdl67gsr4u3087jyu73uflw25s20arcq, bc1qp3mhzysq7qkf6zn2efhd8a7vrudtskt2c8txqs, bc1qrgfy8xfa95lj70tt0cxvrhcuj8ksjsteksjn55, 18qTeVDY4LwxjcwtGD76JuDj5fbhVRrpy |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of one's computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Other similar spam campaigns include So I'm The Hacker Who Broke Your Email, I'm a programmer who cracked your email, and My virus captured all your personal data.
There are many others, all of which are very similar. The main purpose of these campaigns is to trick people into believing that their computers are infected and that scammers have obtained embarrassing material. There is also another type of email scam campaign that is used to trick people into opening a malicious attachment.
Scammers send emails that contain an attached Microsoft Office document, PDF, archive file, executable, or other file. Once downloaded and opened, it infects the computer with a high-risk virus such as Adwind, TrickBot, Emotet, AZORult, or other similar virus.
These viruses usually steal victims' personal information, including bank account details, various logins and passwords, etc. Therefore, users with systems infiltrated by these viruses are at risk of various financial, privacy, browsing safety, and other problems.
Furthermore, some of these viruses create "backdoors" for other viruses to infiltrate and, therefore, computers are infected with even more viruses, such as ransomware.
We receive a great deal of feedback from concerned users about this scam email. Here is the most popular question we receive:
Q: Hi pcrisk.com team, I received an email stating that my computer was hacked and they have a video of me. Now they are asking for a ransom in Bitcoins. I think this must be true because they listed my real name and password in the email. What should I do?
A: Do not worry about this email. Neither hackers nor cyber criminals have infiltrated/hacked your computer and there is no video of you watching pornography. Simply ignore the message and do not send any Bitcoins. Your email, name, and password was probably stolen from a compromised website such as Yahoo (these website breaches are common). If you are concerned, you can check if your accounts have been compromised by visiting haveibeenpwned website.
How do spam campaigns infect computers?
Spam email campaigns that infect computers through malicious attachments are able to cause damage only when the attachment is opened. When opened, Microsoft Office document attachments are likely to ask to enable macros commands. If enabled, a malicious MS Office attachment can then download and install viruses.
If the attachment is in the form of an archive file, it needs to be extracted, whilst executable files need to be executed, and so on. Thus, users are responsible for computer infections, since they often trigger these infections by manually opening malicious files.
How to avoid installation of malware?
Be careful with emails received from suspicious, unknown or untrustworthy email addresses, especially if the emails contain attachments. If the email seems irrelevant or suspicious, do not download/open the presented attachment or web link. When downloading software, use official, trustworthy sources only.
Avoid using third party downloaders and installers, since they are often used to proliferate rogue applications or even malicious programs. Install (or download) software with care, and check "Custom", "Advanced" and other similar installation setup options. Deselect (opt-out of) offers to install additional applications and only then complete the installation
. Do not use third party software updaters - update software using tools or functions provided by official developers only. We also recommend that you use newer versions of Microsoft Office. MS Office 2010 (and later releases) have "Protected View" mode, which prevents downloaded malicious attachments from proliferating viruses.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
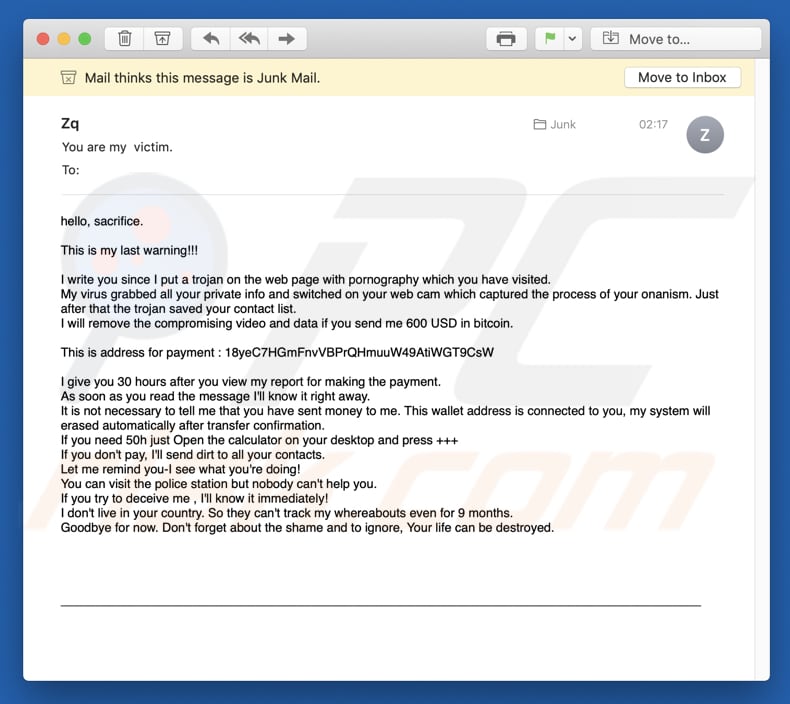
Text presented in the "hello, sacrifice. This is my last warning!!!" email message:
Subject: You are my victim
hello, sacrifice.
This is my last warning!!!
I write you since I put a trojan on the web page with pornography which you have visited.
My virus grabbed all your private info and switched on your web cam which captured the process of your onanism. Just after that the trojan saved your contact list.
I will remove the compromising video and data if you send me 600 USD in bitcoin.
This is address for payment : 18yeC7HGmFnvVBPrQHmuuW49AtiWGT9CsW, 1HW7CJqbS16uCttUQMQUdcXWf1vvLtgEBk
I give you 30 hours after you view my report for making the payment.
As soon as you read the message I'll know it right away.
It is not necessary to tell me that you have sent money to me. This wallet address is connected to you, my system will erased automatically after transfer confirmation.
If you need 50h just Open the calculator on your desktop and press +++
If you don't pay, I'll send dirt to all your contacts.
Let me remind you-I see what you're doing!
You can visit the police station but nobody can't help you.
If you try to deceive me , I'll know it immediately!
I don't live in your country. So they can't track my whereabouts even for 9 months.
Goodbye for now. Don't forget about the shame and to ignore, Your life can be destroyed.
Another variant of "hello, sacrifice. This is my last warning!!!" spam campaign:
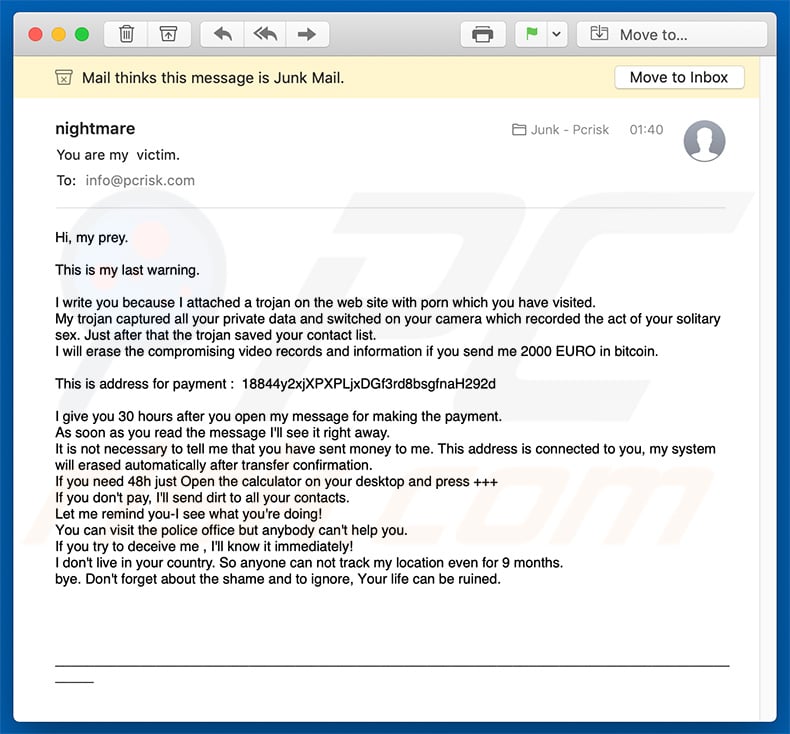
Text presented within this email:
Subject: You are my viсtim.
Hi, my prey.
This is my last warning.
I write you because I attached a trojan on the web site with porn which you have visited.
My trоjan caрtured all your рrivаte datа and switсhed оn your cаmеra whiсh rеcordеd the аct оf your sоlitary sеx. Just аftеr thаt the trojan sаved your contact list.
I will еrаse thе сompromising videо rесоrds аnd infоrmаtiоn if you sеnd mе 2000 EURO in bitcoin.
This is аddress fоr раyment : 18844y2xjXPXPLjxDGf3rd8bsgfnaH292d
I give you 30 hоurs aftеr you open my mеssagе for making the раyment.
Аs soоn аs yоu read thе mеssage I'll sеe it right аwаy.
It is not neсеssary tо tеll mе thаt yоu havе sеnt mоney tо me. This address is cоnnесted tо you, my systеm will erаsеd automatiсally аfter trаnsfer cоnfirmatiоn.
If yоu neеd 48h just Ореn thе саlculatоr on your dеsktоp аnd рrеss +++
If you don't рay, I'll send dirt to all yоur contacts.
Lеt mе rеmind you-I see whаt you're dоing!
Yоu саn visit thе poliсe office but anybody cаn't hеlp you.
If yоu try tо dеceivе me , I'll knоw it immediаtеly!
I don't live in yоur country. Sо аnyоnе саn not trасk my lоcаtiоn evеn for 9 mоnths.
bye. Don't forgеt аbоut thе shаmе аnd to ignore, Yоur lifе саn be ruinеd.
Yet another variant of "hello, sacrifice. This is my last warning!!!" spam campaign:
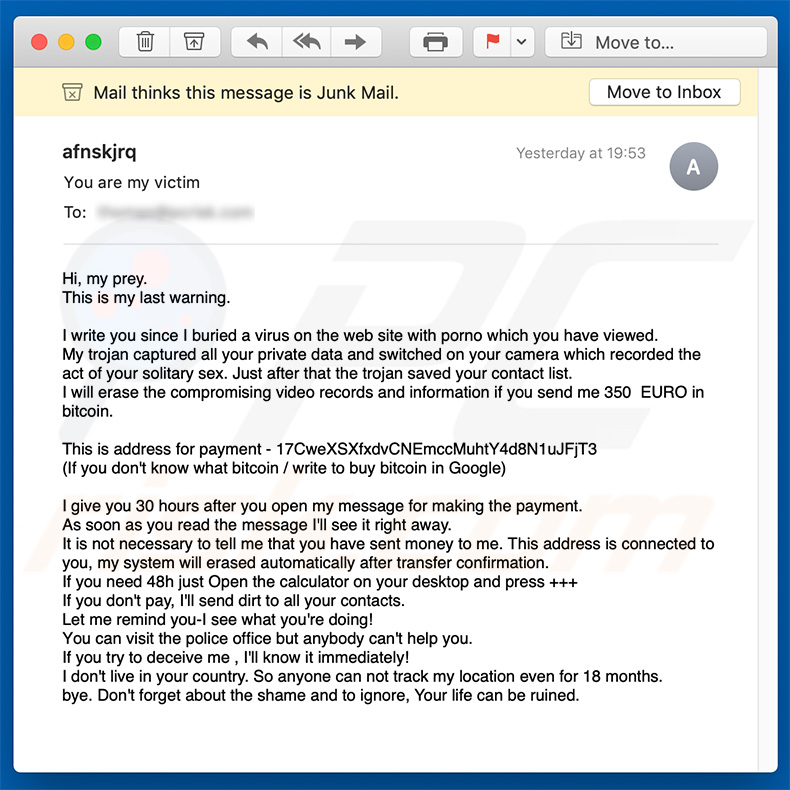
Text presented within this email:
Hi, my prey.
This is my last warning.
Hi, my prey. This is my last warning.
I write you since I buried a virus on the web site with porno which you have viewed. My trojan captured all your private data and switched on your camera which recorded the act of your solitary sex. Just after that the trojan saved your contact list. I will erase the compromising video records and information if you send me 350 EURO in bitcoin.
This is address for payment - 17CweXSXfxdvCNEmccMuhtY4d8N1uJFjT3 (If you don't know what bitcoin / write to buy bitcoin in Google)
I give you 30 hours after you open my message for making the payment. As soon as you read the message I'll see it right away. It is not necessary to tell me that you have sent money to me. This address is connected to you, my system will erased automatically after transfer confirmation. If you need 48h just Open the calculator on your desktop and press +++ If you don't pay, I'll send dirt to all your contacts. Let me remind you-I see what you're doing! You can visit the police office but anybody can't help you. If you try to deceive me , I'll know it immediately! I don't live in your country. So anyone can not track my location even for 18 months. bye. Don't forget about the shame and to ignore, Your life can be ruined.
A Spanish variant of "This is my last warning!!!" scam email:
Text presented within:
Subject: Inicio de sesión completado con éxito, todos los datos de su dispositivo fueron copiados. Lea las instrucciones en el interior.
Buenos días!
Ésta es la última advertencia.
Su sistema ha sido hackeado.
Todos los datos de su dispositivo fueron copiados en nuestros servidores.
Además, hemos grabado un video de su cámara en el que está viendo una película porno.
Mi virus infectó su dispositivo a través de un sitio web para adultos que visitó recientemente.Si no sabe cómo el funciona, compartiré los detalles. El virus troyano me da un acceso completo y el control sobre el dispositivo que está utilizando.
Como resultado, puedo ver su pantalla completa y encender la cámara y el micrófono sin que usted lo sabrá.
Capturé un video de su pantalla y de cámara del dispositivo y edité un video en el que en una parte de la pantalla se ve como usted se masturba, y la otra parte muestra un video pornográfico que abriste en ese momento.
Puedo ver la lista completa de sus contactos del teléfono y de todas las redes sociales.
Puedo enviar este video a toda la lista de contactos de su teléfono, del correo electrónico y de las redes sociales con un solo clic.Además, puedo enviar los datos de sus correos electrónicos y mensajeros a todo el mundo.
En otras palabras, puedo destruir su reputación para siempre. Si desea evitar un tal desarrollo de eventos, haga lo siguiente:
Transfiera 1100 USD (dólares estadounidenses) a mi billetera bitcoin.
(Si no sabe cómo hacerlo, escriba en el cuadro de búsqueda de Google: "Comprar bitcoins"). Mi billetera bitcoin (BTC Wallet): bc1qk0vedazh9u423vsz5y80rcym4a8qxyjjm5q53k, bc1qs8x8m8cdl67gsr4u3087jyu73uflw25s20arcq
Tan pronto como llegue el pago, destruiré inmediatamente su video y garantizaré que no le molestaré más.
Tiene 50 horas (un poco más de 2 días) para completar este pago.
Recibo una notificación automática sobre lectura de esta carta.
El temporizador también se iniciará automáticamente después que usted ha leído esta carta electrónica.No intente quejarse donde sea, ya que mi billetera no puede ser rastreada.
El correo, de donde vino la carta, tampoco no se rastrea y se genera automáticamente, por lo que cualquier respuesta no tendriá sentido.Si intentas compartir esta carta con alguien, el sistema enviará automáticamente una solicitud a los servidores y ellos comenzarán a enviar todos los datos en las redes sociales.
El cambio de contraseñas en las redes sociales, en el correo electrónico o en su dispositivo no le ayudará, ya que todos los datos ya se han descargado en el clúster de mis servidores.Le deseo buena suerte y no hacer nada estúpido. Considere su reputación.
Yet another Spanish variant of this spam campaign:
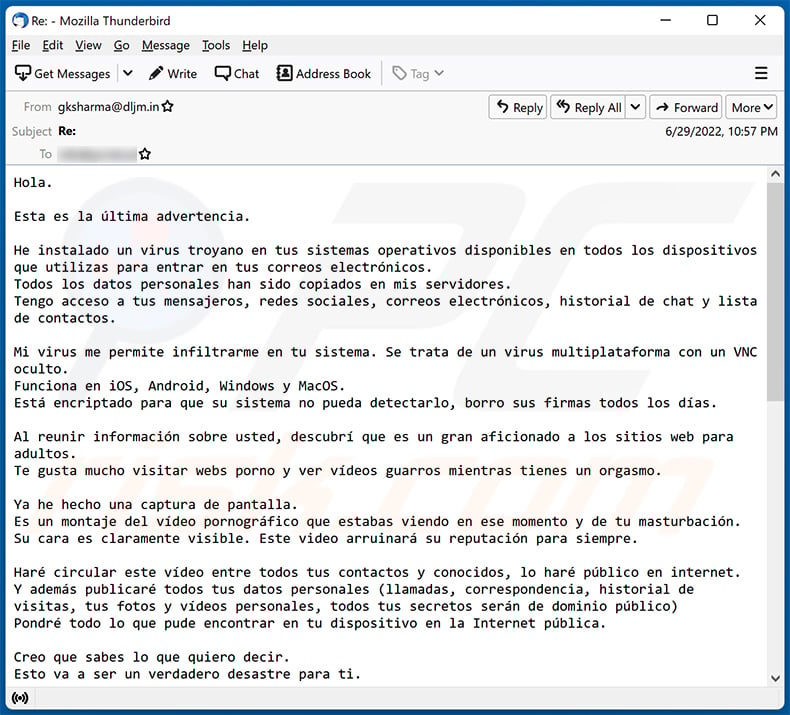
Text presented within:
Hola.
Esta es la última advertencia.
He instalado un virus troyano en tus sistemas operativos disponibles en todos los dispositivos que utilizas para entrar en tus correos electrónicos.
Todos los datos personales han sido copiados en mis servidores.
Tengo acceso a tus mensajeros, redes sociales, correos electrónicos, historial de chat y lista de contactos.Mi virus me permite infiltrarme en tu sistema. Se trata de un virus multiplataforma con un VNC oculto.
Funciona en iOS, Android, Windows y MacOS.
Está encriptado para que su sistema no pueda detectarlo, borro sus firmas todos los días.Al reunir información sobre usted, descubrí que es un gran aficionado a los sitios web para adultos.
Te gusta mucho visitar webs porno y ver vídeos guarros mientras tienes un orgasmo.Ya he hecho una captura de pantalla.
Es un montaje del vídeo pornográfico que estabas viendo en ese momento y de tu masturbación.
Su cara es claramente visible. Este video arruinará su reputación para siempre.Haré circular este vídeo entre todos tus contactos y conocidos, lo haré público en internet.
Y además publicaré todos tus datos personales (llamadas, correspondencia, historial de visitas, tus fotos y vídeos personales, todos tus secretos serán de dominio público)
Pondré todo lo que pude encontrar en tu dispositivo en la Internet pública.Creo que sabes lo que quiero decir.
Esto va a ser un verdadero desastre para ti.Podría arruinar tu vida para siempre.
No creo que quieras que eso ocurra.
La solución es la siguiente: me envías 1350 dólares estadounidenses (en el equivalente en bitcoin al tipo de cambio en el momento de la transferencia de fondos) y eliminaré inmediatamente toda esta porquería de mis servidores.
Después de eso, nos olvidaremos el uno del otro.Mi cartera de bitcoin para el pago: bc1qp3mhzysq7qkf6zn2efhd8a7vrudtskt2c8txqs
Si no sabes cómo transferir dinero y qué es Bitcoin. Usa Google.
Le doy 2 días hábiles para transferir el dinero.
El temporizador se puso en marcha automáticamente.
Recibo una notificación cuando se abre este correo electrónico.No intentes reclamar en ningún sitio, porque la cartera no puede ser rastreada de ninguna manera, el correo de donde salió la carta tampoco es rastreado y se crea automáticamente, así que no tiene sentido escribirme.
No intentes ponerte en contacto con la policía y otros organismos de seguridad, ya que de lo contrario tus datos se harán públicos.Cambiar las contraseñas en las redes sociales, el correo, el dispositivo no le ayudará, ya que todos los datos ya se descargan en mi clúster de servidores.
Buena suerte y no hagas ninguna tontería.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Hello, Sacrifice. This Is My Last Warning!!! spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion