Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Torrent Movies Virus?
Torrent Movies Virus is the generic name of malware that disguises itself as a video format file. In fact, it is a Windows shortcut. Cyber criminals proliferate the virus via The Pirate Bay torrent tracker, which is notorious for distribution of malware and potentially unwanted applications (PUAs).
Torrent Movies Virus is a high-risk virus that poses a significant threat to your privacy, finances, and computer safety.
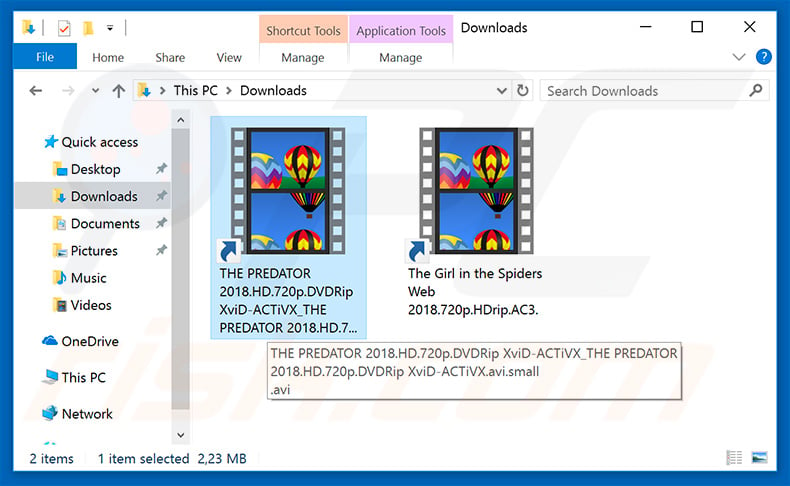
As mentioned above, the Torrent Movies Virus is distributed using a Windows shortcut (.LNK file), which appears to be a video file.
Cyber criminals disguise the malicious shortcut by adding a legitimate file name (for example, at time of research, two names used were "The Girl in the Spiders Web 2018.720p.HDrip.AC3.lnk" and "THE PREDATOR 2018.HD.720p.DVDRip XviD-ACTiVX_THE PREDATOR 2018.HD.720p.DVDRip XviD-ACTiVX.avi.small.lnk).
Many users do not notice that the downloaded 'movie' extension is .LNK, rather than an .avi, .mp4, or other video format. Once opened, the shortcut executes a number of PowerShell commands that infect the system. The downloaded malware performs malicious actions. Firstly, it injects web browsers and visited websites with JavaScript scripts that modify displayed content.
The Google and Yandex web search engines are just a few examples of these modified sites. The injected script displays intrusive advertisements and changes the displayed search results by delivering those determined by cyber criminals. Therefore, users are fed with false search results.
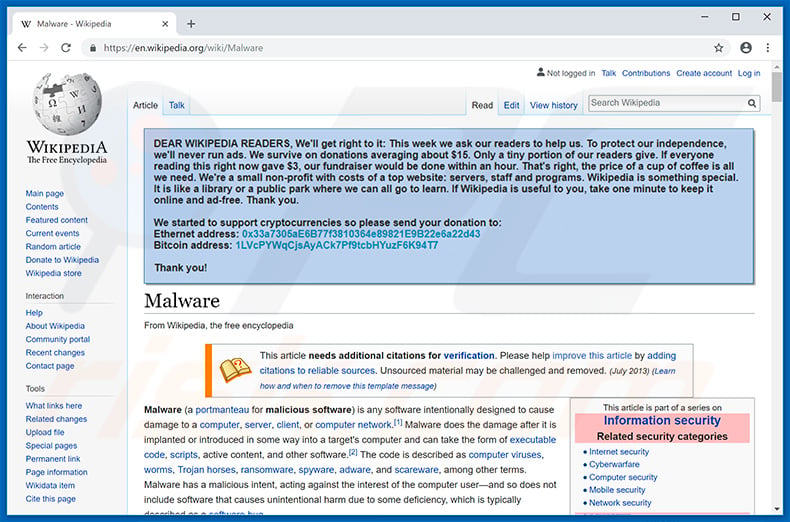
This is typically done to make users visit malicious websites (which will lead to even more computer infections) and to promote various websites and generate revenue via affiliate programs and/or advertising. In addition, Torrent Movies Virus modifies the content of the Wikipedia website. This malware inserts a message onto the site asking for a donation.
The message essentially states that Wikipedia is a non-profit organization, and thus never feeds users with advertisements. The website supposedly "survives" on donations only and receives very low income. Therefore, users are asked to donate to help developers take care of the site. The donation must be transferred to a Bitcoin or Ethereum cryptocurrency wallet.
Again, this is a scam - criminals attempt to trick users by appealing to their credulity and generosity. Torrent Movies Virus also contains another high-risk feature: it detects when the user is visiting cryptowallet websites used to transfer cryptocurrency. It steals cryptocurrency by changing the recipient wallet's address to one belonging to cyber criminals.
Cryptocurrency wallet addresses are long strings of random characters and digits, and thus users are unlikely to notice any changes (all this is performed immediately the user attempts to paste a copied cryptowallet address). In summary, users end up transferring cryptocurrency to cyber criminals, rather than their intended recipient.
Ultimately, the presence of this malware can lead to various issues: users' computers might be infected with even more viruses, the browsing experience is diminished (they encounter intrusive advertisements, false search results, pop-ups, etc.), and their money (cryptocurrency) might be stolen. Therefore, eliminating Torrent Movies Virus is paramount.
If you have recently downloaded movies using The Pirate Bay or another torrent tracker, we strongly advise you to scan the system with a reputable anti-virus/anti-spyware suite and eliminate all detected threats. Be aware that these download sources are often used to proliferate viruses.
Furthermore, this type of piracy is considered to be a cyber crime - it violates copyright law. Therefore, never download any illegal copies of media (music, movies, eBooks, etc.) or cracked software/games using torrents and other unofficial software download sources. In doing so, you simply steal from the copyright owner and put your system at risk.
| Name | Torrent Movies malware |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
There are dozens of viruses that steal information, deliver advertisements, cause unwanted redirects, inject additional malware, and perform other malicious actions. The list of examples includes (but is not limited to) Vidar, Hancitor, TrickBot, FormBook, Adwind, and AZORult.
These viruses are developed by different cyber criminals and their behavior may also differ slightly. Nevertheless, they all pose a significant threat to your privacy and browsing safety. For this reason, eliminate them immediately.
How did Torrent Movies Virus infiltrate my computer?
As mentioned above, Torrent Movies Virus is mainly distributed using The Pirate Bay torrent tracker, however, using peer-to-peer (P2P) networks to proliferate these viruses is one of many popular methods used by cyber criminals. The malware is also proliferated using spam email campaigns, trojans, fake software update tools, and various unofficial download sources.
Spam emails deliver malicious attachments (executables, archives, MS Office documents, PDFs, and so on) that, once opened, download and install malware. Trojans cause so-called "chain infections". They essentially infiltrate the system and continue to inject other malware.
Fake updaters infect computers by exploiting old software bugs/flaws or simply downloading and installing malware rather than updates.
Unofficial download sources (free file hosting websites, freeware download websites, and so on) present malicious executables as legitimate, thereby tricking users into downloading and installing malware. In summary, the main reasons for computer infections are poor knowledge of these threats and careless behavior.
How to avoid installation of malware?
The key to computer safety is caution. Therefore, pay attention when browsing the internet and downloading, installing, and updating software. Think twice before opening email attachments. If the file seems irrelevant or the sender's email address is suspicious/unrecognizable, do not open any file.
Furthermore, download your programs from official sources only, using direct download links. Third party downloaders/installers often include rogue apps, and thus these tools should never be used. The same applies to software updates.
It is important to keep installed applications updated, however, this should be achieved using implemented functions or tools provided by the official developer.
Having a reputable anti-virus/anti-spyware suite installed and running is also essential, since these tools can detect and eliminate malware before it does any harm. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
A quote of scam message asking for a donation in Wikipedia website:
DEAR WIKIPEDIA READERS, We'll get right to it: This week we ask our readers to help us. To protect our independence, we'll never run ads. We survive on donations averaging about $15. Only a tiny portion of our readers give. If everyone reading this right now gave $3, our fundraiser would be done within an hour. That's right, the price of a cup of coffe is all we need. We're a small non-profit with costs of a top website: servers, staff and programs. Wikipedia is something special. It is like a library or a public park where we can all go to learn. If Wikipedia is useful to you, take one minute to keep it online and ad-free. Thank you.
We started to support cryptocurrencies so please send your donation to:
Ethernet: 0x33a7305aE6B77f3810364e89821E9B22e6a22d43
Bitcoin: 1LVcPYWqCjsAyACk7Pf9tcbHYuzF6K94T7Thank you!
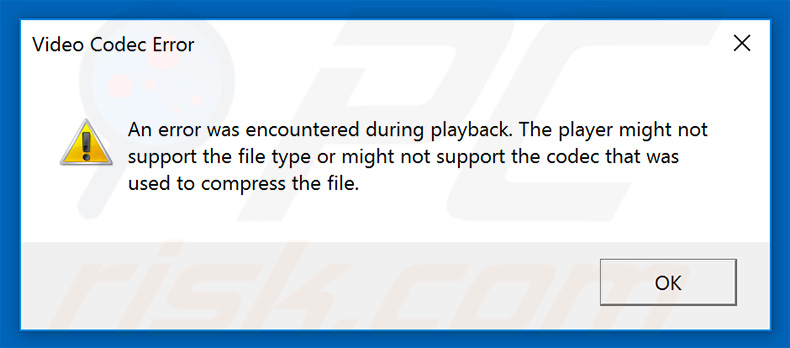
Once opened, the malicious .LNK file displays a fake error message stating that the "video file" cannot be opened because it is not supported:
Examples of malicious .LNK files used to spread Torrent Movies Virus:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Torrent Movies Virus?
- STEP 1. Manual removal of Torrent Movies malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion