Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Vidar?
Vidar (also known as Vidar Stealer) is a trojan (a malicious program) commonly used by cyber criminals. The program steals various personal information from users who have computers infected with the virus.
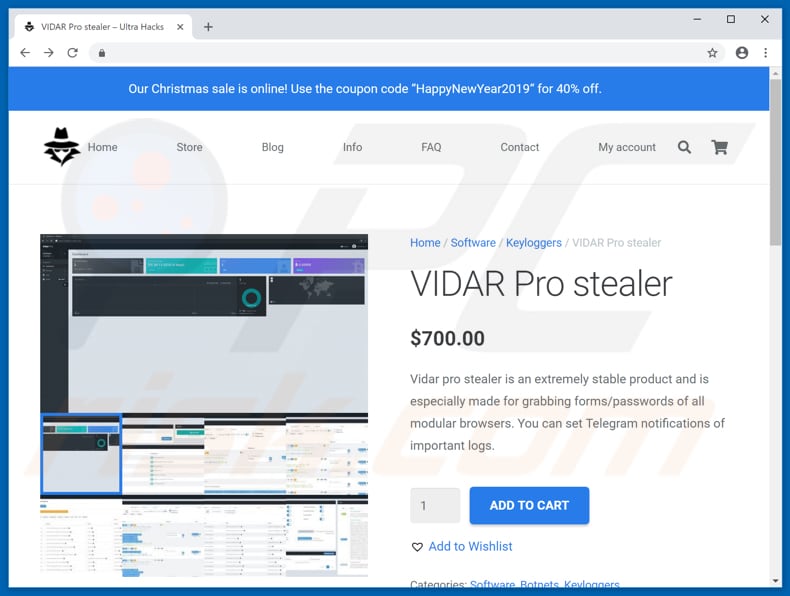
Vidar is distributed mainly through Fallout exploit kit, however, there might also be other ways. The program can be purchased by anyone at a cost of $700 (at time of research).
Vidar malware overview
Cyber criminals employ this tool to steal IP addresses, browsing history (including from Tor browsers), cryptocurrency wallets, saved passwords, messages from messenger software, and so on. It can also take screenshots. Furthermore, criminals can choose the type of information they wish to steal using Vidar's internal options.
One option allows Vidar to infect computers with the GandCrab 5.0.4 ransomware-type infection. This, however, depends on the malware distributor used. You can read more about this ransomware distribution in this article. Vidar records all stolen data within a text file, compresses it to an archive file (ZIP), and then sends it to a Command and Control (C2C) server.
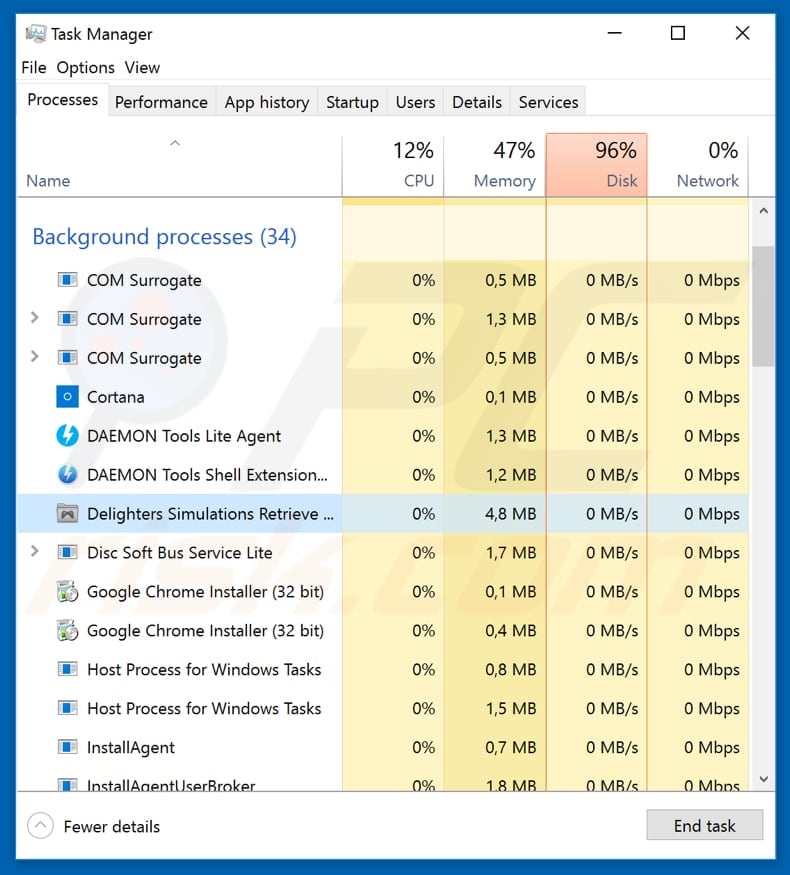
Generally, trojans such as Vidar go unnoticed - they run stealthily without victims being aware of their presence. In this case, it can be identified as running in Task Manager as the "Deligthers Simulations Retriever..." process.
See the screenshot above. Having a computer infected with malicious programs of this type might cause serious problems relating to finances, data loss, privacy issues, and so on. If you suspect that your computer (operating system) is infected with Vidar, we recommend that you remove it immediately.
| Name | Vidar Stealer |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Malicious Filename | verinstere.xls |
| Websites Spreading Vidar By Disguising It As Legitimate Software | dumepad[.]com, hurimis[.]com, kisomer[.]com, metersik[.]com, nuktose[.]com, nviktus[.]com, opriky[.]com, vikolin[.]com, viulinik[.]com, kulinkos[.]com, crypto-widget[.]live, download-best[.]com, github[.]llc, intuitquickbooks[.]space |
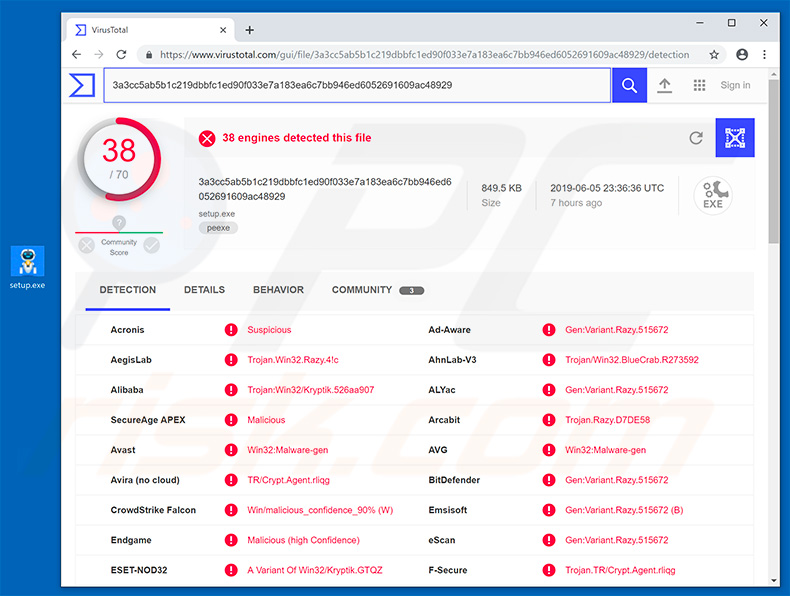
| Detection Names | Avast (Win32:Malware-gen), BitDefender (Trojan.GenericKD.32180278), ESET-NOD32 (A Variant Of Win32/Kryptik.GUVT), Kaspersky (Trojan.Win32.Chapak.dwtd), Full List (VirusTotal) |
| Malicious Process Name(s) | Deligthers Simulations Retriever... (the process name may vary). |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Data-stealing malware examples
Other trojan-type programs are capable of stealing a range of data. Some examples are AZORult, Hancitor, LokiBot, and FormBook. These infections are usually distributed through spam email campaigns (malicious attachments within emails). They steal personal, private information, and other data.
Some trojans (including Vidar) are capable of proliferating other infections such as ransomware-type viruses. For these reasons, you should eliminate this malware immediately.
How did Vidar infiltrate my computer?
This trojan is usually distributed by 'malvertising' campaigns, whereby cyber criminals trick victims into clicking links or ads that redirect to malicious websites.
The Fallout exploit kit is also used to proliferate Vidar. To infect computers, this kit uses various exploits that target Flash Player and the Internet Explorer browser. More information about the Fallout exploit kit is available at the link provided in the introduction above.
How to avoid installation of malware?
To keep computers safe from infection by the Vidar trojan, keep operating systems and installed software updated at all times. This will prevent download processes using known exploits and inflicting damage. Have a web protection tool and ad blocker software installed: these can help to avoid being redirected to malicious websites by 'malvertising' campaigns.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Hacker website promoting Vidar trojan:
Update June 7th, 2019 - Cyber criminals have recently developed a fake Cryptohopper (cryptocurrency trading platform) website and use it to distribute various infections, including Vidar.
Screenshot of fake Cryptohopper website (crypto-widget[.]live)
![Fake Cryptohopper website - crypto-widget[.]live](/images/stories/screenshots201904/vidartrojanupdate-2019jun6website3.jpg)
List of malicious installer's (promoted via fake Cryptohopper website) detection names in various malware databases:
Update May 6, 2020 - Cyber criminals have recently started a new spam campaign to distribute Vidar trojan, alongside with Nemty Special Edition ransomware. The spam campaign targets South Korean users:
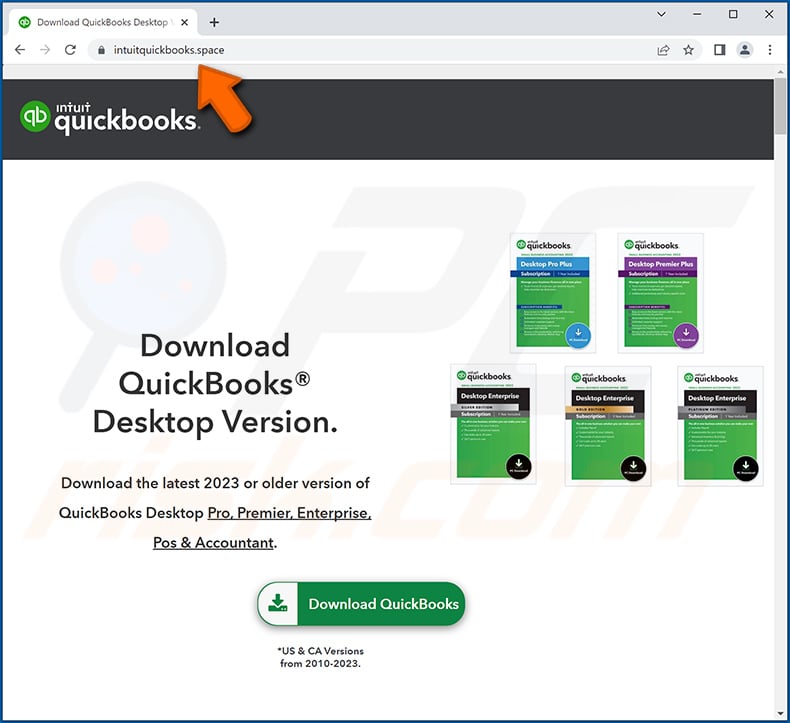
Update October 25, 2022 - new distribution methods for Vidar have been observed. Fake websites that imitate legitimate ones have been noted spreading the Vidar stealer.
These pages can be practically identical visually to those they mimic, and their URLs can have but a letter's difference from the genuine site's. Common themes for malicious websites include - social media and social networking, software and mobile app, cryptocurrency, and many others.
To elaborate, Vidar has been distributed through fake sites of the following: Brave browser (bogus URL - braves-browsers[.]org), Microsoft's Visual Studio Code (codevisualstudio[.]org), Notepad++ text editor (notepads-plus-plus[.]org), Thunderbird email (thundersbird[.]org), etc.
This technique relies on user negligence when entering URLs and disregard when accessing a site. However, websites of this kind are not accessed exclusively through mistyped URLs. Visitors can also enter them via redirects caused by malicious ads, spam mail (emails, PMs/DMs, SMSes, etc.), sites using rogue advertising networks, browser notification spam, or installed adware.
Screenshot of another deceptive website (download-best[.]com) used to spread Vidar malware:
![Vidar stealer-spreading website (download-best[.]com)](/images/stories/screenshots202211/vidar-stealer-update-2022-11-07-promoter.jpg)
Screenshot of a fake GitHub website (github[.]llc) used to spread Vidar trojan:
![Vidar Trojan-spreading fake GitHub website (github[.]llc)](/images/stories/screenshots202211/vidar-update-2022-11-24-fake-github-website.jpg)
Screenshot of a fake QuickBooks download website (intuitquickbooks[.]space) used to spread Vidar trojan:
Update January 11, 2023 – distribution techniques described in the previous update are still in active use for Vidar's proliferation. In the newest campaigns, the malicious sites mimic AnyDesk remote access software's official website. However, there is significant variation in the URLs – of which there are at least 1300.
In addition to resembling AnyDesk's domain, these pages also use ones similar to those of 7-ZIP, Blender, Dashlane, MSI Afterburner, OBS, Slack, VLC, cryptocurrency-related applications, and others. Despite the differences in URLs – they all impersonate AnyDesk's website.
The malignant webpages redirect to a Dropbox folder containing a file named "AnyDeskDownload.zip" (may vary) that triggers Vidar's infection chain once opened. At the time of research, the malicious file had been taken down by Dropbox, although the fake AnyDesk sites were still up.
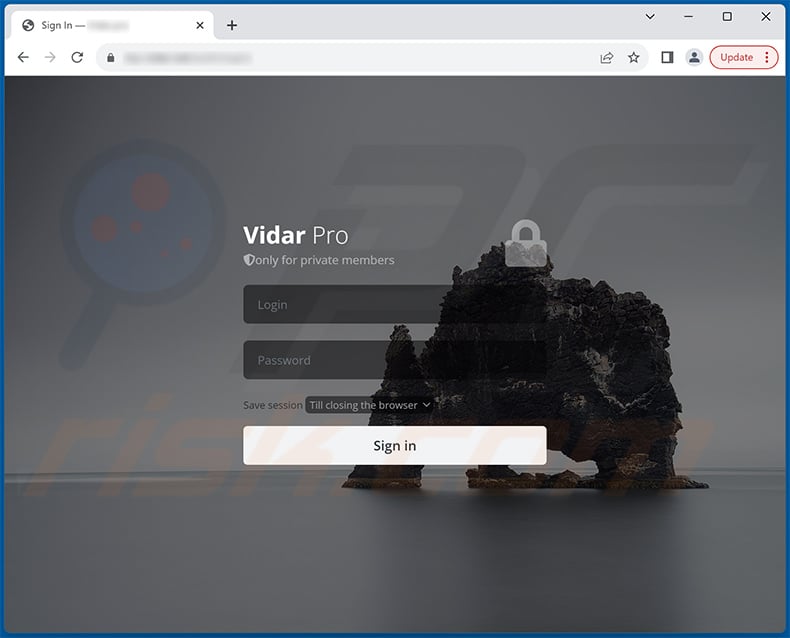
Screenshot of Vidar's web admin panel's login page:
Screenshot of the homepage of the site hosting Vidar's web admin panel:
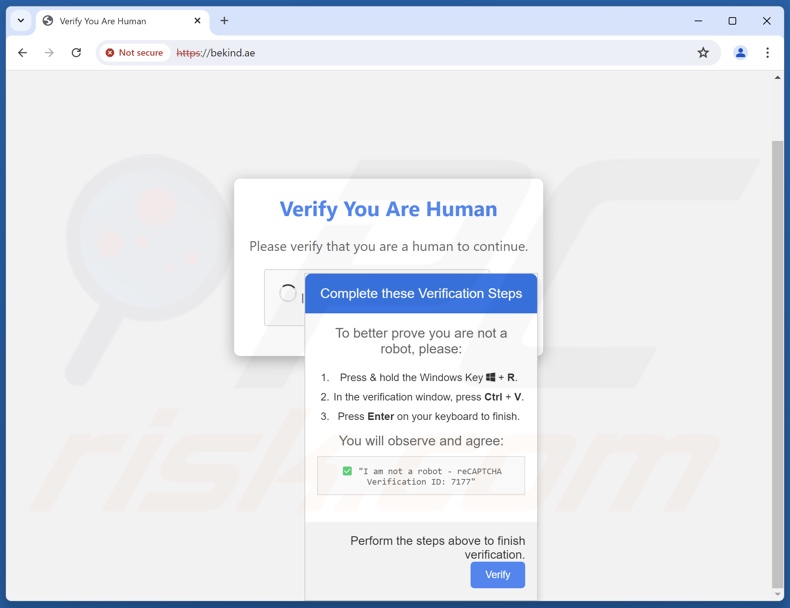
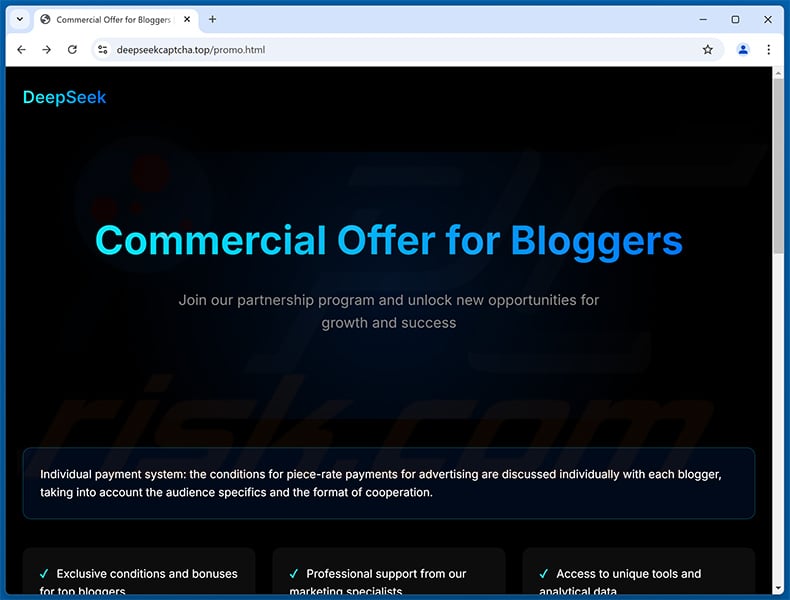
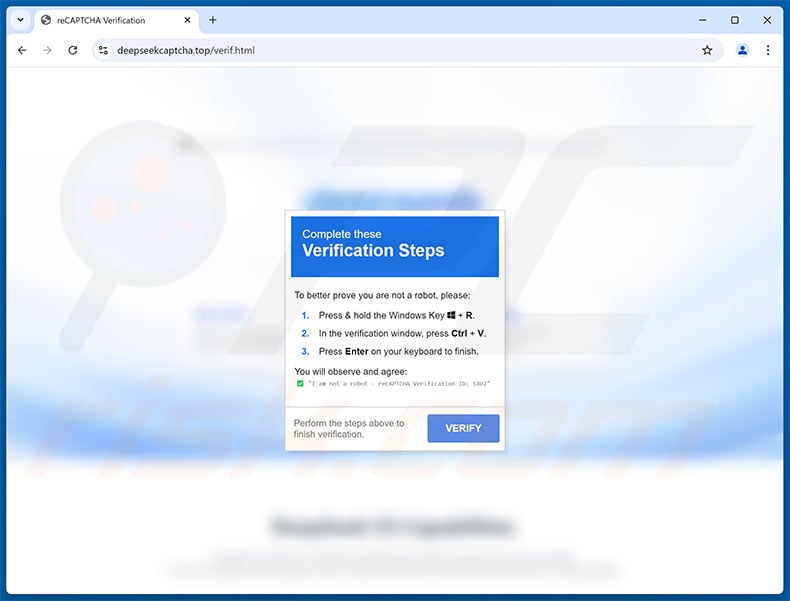
Update January 28, 2025 – Vidar stealer has been spread using a new technique. It is called "ClickFix", and it basically deceives victims into executing malicious commands on their systems by presenting it as a solution to a specific issue. Vidar was proliferated via such a scam that claimed it was CAPTCHA verification. More on ClickFix can be read in our dedicated article.
Screenshot of a ClickFix scam promoting the Vidar stealer:
Screenshot of a DeepSeek-themed ClickFix website (deepseekcaptcha[.]top) spreading Vidar trojan:
Page 1:
Page 2:
Update 23 May, 2025 – Recently, a new malware campaign exploiting TikTok was observed being used to deploy Vidar through deceptive short videos. These clips, likely made using AI, verbally and visually guide viewers to manually enter PowerShell commands, supposedly to activate software like Spotify or Microsoft Office.
This method is particularly dangerous because the commands are not shown as text or clickable links—instead, users are tricked into typing them out. Once executed, the commands download a script from a remote server, injecting the Vidar malware (or Stealc).
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Vidar malware, should I format my storage device to get rid of it?
No, most malware infections can be removed without resorting to formatting.
What are the biggest issues that Vidar malware can cause?
The threats posed by a malicious program depend on its abilities and the cyber criminals' modus operandi. Vidar is a stealer-type trojan that can exfiltrate a wide variety of data. It can also infect devices with other malware, e.g., trojans, ransomware, etc. This stealer has been observed being used to infiltrate the GANDCRAB 5.0.4 ransomware into systems.
In summary, the presence of malware like Vidar on devices can lead to multiple system infections, severe privacy issues, permanent data loss, financial losses, and identity theft.
What is the purpose of Vidar malware?
Malware is typically used for profit. However, cyber criminals can also employ this software to disrupt processes such as those of websites, services, companies, organizations, etc. These attacks can be motivated by personal grudges and political/geopolitical reasons as well.
How did Vidar malware infiltrate my computer?
Malware is primarily proliferated through drive-by downloads, malvertising, online scams, spam mail (e.g., emails, PMs/DMs, SMS, etc.), untrustworthy download sources (e.g., unofficial and freeware websites, P2P sharing networks, etc.), illegal software activation tools ("cracks"), and fake updates.
Furthermore, some malicious programs can self-spread via local networks and removable storage devices (e.g., external hard drives, USB flash drives, etc.).
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is designed to detect and remove threats. It can eliminate nearly all known malware infections. Note that running a complete system scan is paramount - as high-end malicious programs usually hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion