Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Mispadu?
Mispadu (also known as URSA) is the name of a banking Trojan. Cyber criminals behind this software target people living in Brazil, Spain and Mexico.
They seek to steal credentials, credit card and banking data. Research shows that this malware is distributed through spam campaigns and malicious advertisements. People with computers infected with Mispadu are likely to experience monetary loss and online privacy issues. This banking Trojan should be removed from the system immediately.
More about Mispadu
The malware can be used to simulate keyboard, mouse actions, take screenshots, record keystrokes, and collect information such as operating system versions, computer names, list of installed computer security programs and banking apps that are commonly used in Latin America.
Furthermore, Mispadu can update itself through a file that it downloads and executes via Visual Basic Script (VBS). A keystroke logging feature allows it to record keys pressed on the keyboard. Therefore, it can be used to record login usernames, passwords, and other sensitive information.
The screenshots might also contain personal details. Mispadu is installed with browser apps that it uses to steal credentials saved on browsers such as Google Chrome, Mozilla Firefox, Internet Explorer, and email clients such as Mozilla Thunderbird, Microsoft Outlook, Windows Live Mail, and others.
One of the apps (a malicious Google Chrome extension) is capable of stealing credit card data by recording the contents of various input fields completed by victims on various websites, mainly those relating to online banking.
This app targets the Boleto payment system and is capable of replacing ID numbers with one associated with a bank account used to receive funds for an attacker. Therefore, a legitimate web page can be misused to generate a payment barcode using the attacker’s account number rather than a legitimate one.
Furthermore, the Mispadu banking Trojan can be used to replace data saved on the clipboard with attacker's data. In this way, cyber criminals can replace a saved cryptocurrency wallet address with their own, and thus victims might inadvertently make payments to the wallet address of an attacker.
| Name | Mispadu banking malware |
| Threat Type | Trojan, password-stealing virus, banking malware, spyware. |
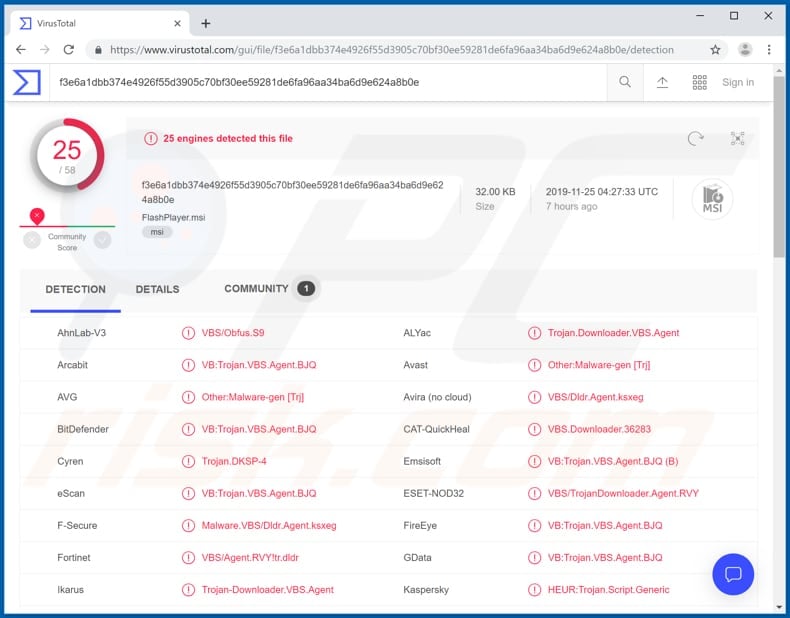
| Detection Names | Avast (Other:Malware-gen [Trj]), BitDefender (VB:Trojan.VBS.Agent.BJQ), ESET-NOD32 (VBS/TrojanDownloader.Agent.RVY), Kaspersky (HEUR:Trojan.Script.Generic), Full List (VirusTotal) |
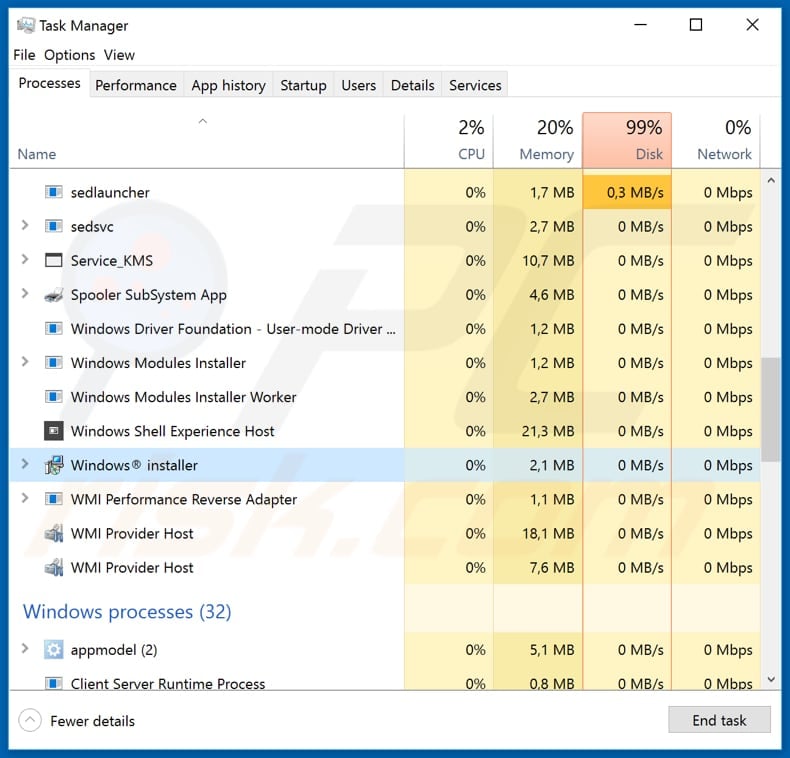
| Malicious Process Name(s) | Windows installer |
| Payload | This Trojan installs malicious Google Chrome extension and other browser apps. |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similar malware
Mispadu is similar to another banking Trojan called Casbaneiro. More examples of these Trojans include Bolik and Tinynuke.
Despite their differences, most of these malicious programs are used to steal credit card data and other sensitive details relating to online banking. Cyber criminals use banking malware to steal funds from victims by misusing stolen details, making fraudulent transactions, and so on. If your computer is infected with Mispadu or other malicious software, remove it immediately.
How did Mispadu infiltrate my computer?
Cyber criminals proliferate Mispadu through spam campaigns and malicious online advertisements. They send emails containing website links. They present these emails as legitimate, official, and attempt to trick recipients into opening the link, which then downloads a malicious file.
If opened/executed, the file installs Mispadu. Cyber criminals also distribute malware through malicious attachments. Rather than including a link, they attach a file which, if opened, leads to installation of malware. Additionally, research shows that Mispadu is distributed through malicious ads, fake coupons, and discounts for McDonald's on Facebook.
If clicked, these ads lead to dubious websites that contain download buttons, which download a malicious archive file (ZIP) containing an MSI installer. If executed, the installer begins the installation process of the Mispadu banking Trojan.
How to avoid installation of malware
Do not trust intrusive ads, especially if they are displayed on dubious web pages (or lead to web pages of this kind). They often trick people into download/installation of malware. Website links and attachments that are included in irrelevant emails should not be opened, especially if the messages are received from unknown, suspicious addresses.
Software should not be downloaded through third party downloaders, unofficial websites, Peer-to-Peer networks such as torrent clients, eMule, or other such tools/sources. Download only from official web pages and via direct links. Update installed software using implemented functions or tools provided by official software developers, and not third party, fake updaters.
The same applies to activation of paid software. Software 'cracking' tools are illegal and often cause computer infections.
Protect systems from malware attacks by regularly scanning them with a reputable anti-spyware or antivirus suite, and ensure that it is up-to-date. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Mispadu trojan hiding under the name of "Windows installer" in Windows Task Manager:
Screenshots of spam emails used to spread Mispadu trojan:
Example 1:
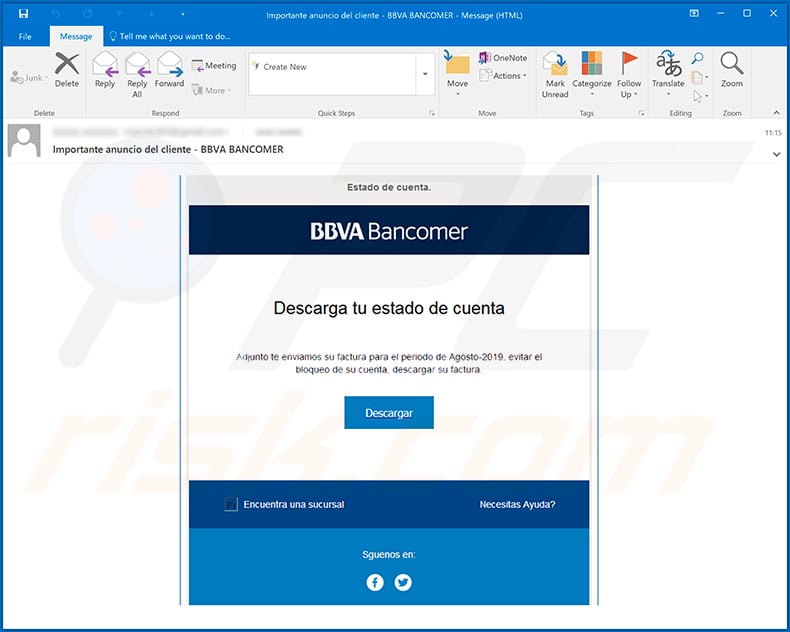
Text presented within:
Subject: Importante anuncio del cliente - BBVA BANCOMER
Estado de cuenta.
BBVA Bancomer
Desgarda tu estado de cuenta
Adjunto te enviamos su factura para el periodo de Agosto-2019, evitar el bloqueo de cuenta, descargar su factura.Descargar
Encuenta una sucursal
Necesitas Ayuda?
Sguenos en:
Example 2:
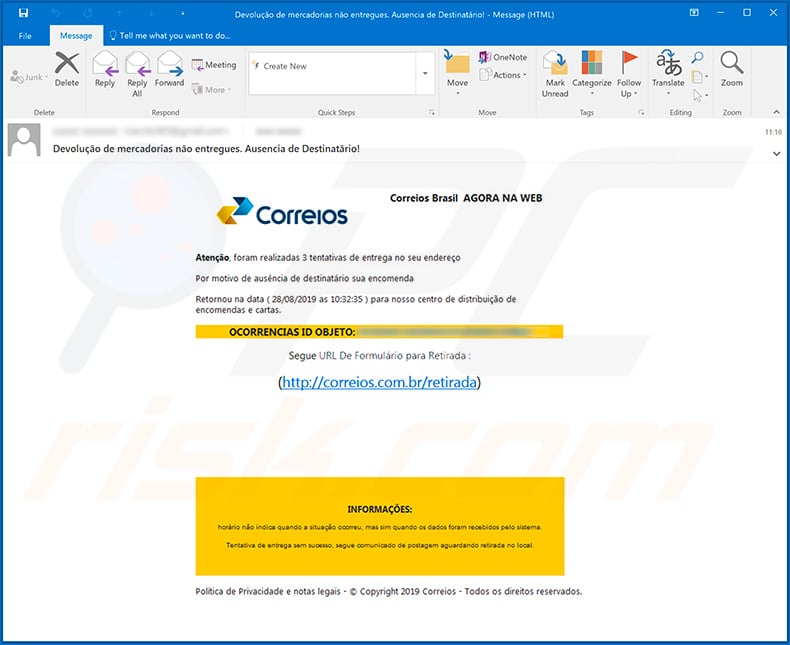
Text presented within:
Subject: Devolução de mercadorias não entregues. Ausencia de Destinatário!
Correios Brasil AGORA NA WEB
Correios
Atenção, foram realizadas 3 tentativas de entrega no seu endereço
Por motivo de ausência de destinatário sua encomenda
Retornou na data ( 28/08/2019 as 10:32:35 ) para nosso centro de distribuição de encomendas e cartas.
OCORRENCIAS ID OBJETO: -
Segue URL de Formulário para Retirada :
hxxp://correios.com.br/retiradaINFORMAÇÕES
horário não indica quando a situação ocorreu, mas sim quando os dados foram recebidos pelo sistema.
Tentativa de entrega sem sucesso, segue comunicado de postagem aguardando retirada no local.Política de Privacidade e notas legais - © Copyright 2019 Correios - Todos os direitos reservados.
Update September 16, 2020 - Mispadu trojan's area of interest has expanded to include Argentina, Bolivia, Chile, Colombia, Costa Rica, Ecuador, Italy, Paraguay, Peru and Portugal.
It is noteworthy that in Portugal this malware has been proliferated under the guise of content related to four legitimate organizations: Vodafone and MEO (Serviços de Comunicações e Multimédia) - telecommunication service providers, Polícia Judicíaria - one of Portugal's key criminal investigation police agencies, and EDP (Energias de Portugal) - electric utilities company.
Update February 2, 2024 - The perpetrators behind the Mispadu banking malware have seized the opportunity to exploit an already patched Windows SmartScreen security bypass flaw to compromise users. In the latest infection chain, they utilized deceitful internet shortcut files concealed within fake ZIP archive files, leveraging CVE-2023-36025, a high-severity bypass flaw addressed by Microsoft in November 2023.
At the core of this exploit is the crafting of an internet shortcut file (.URL) or a hyperlink that directs to malicious files, effectively circumventing SmartScreen's warnings.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Mispadu?
- STEP 1. Manual removal of Mispadu malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Mispadu malware, should I format my storage device to get rid of it?
Users should first try using reputable antivirus software to remove the Mispadu malware before resorting to formatting. Formatting will erase all data on the storage device.
What are the biggest issues that malware can cause?
Malware can cause data loss, financial damage, identity theft, system instability, and unauthorized access to sensitive information.
What is the purpose of Mispadu malware?
The purpose of the Mispadu malware includes simulating keyboard and mouse actions, capturing screenshots, recording keystrokes, collecting system information, updating itself, stealing credentials from browsers and email clients, specifically targeting online banking systems (such as Boleto), and manipulating clipboard data to replace cryptocurrency wallet addresses for fraudulent transactions.
How did Mispadu infiltrate my computer?
Users can infect computers by falling victim to Mispadu through spam emails containing deceptive website links or malicious attachments. Cybercriminals also use malicious online ads, fake coupons, and Facebook discounts for McDonald's to lure users into clicking on dubious websites with download buttons. These sites prompt the download of a malicious archive file (ZIP) containing an MSI installer. If users execute the installer, it initiates the installation process of the Mispadu banking Trojan.
Will Combo Cleaner protect me from malware?
Combo Cleaner is equipped to detect and eliminate almost all well-known malware infections. It is crucial to be aware that advanced malware tends to hide extensively within the system. Hence, performing a thorough system scan is imperative.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion