Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is GrandSteal?
GrandSteal is malicious software, which primarily operates by exfiltrating (i.e., stealing) information stored on infected devices. It has been observed proliferating through spam campaigns, targeting German and Austrian organizations, and spreading via infectious file attachments disguised as curriculum vitaes (CVs). This malware is high risk and can lead lead to serious issues.
GrandSteal has various malicious capabilities. As a stealer, it targets browsers, cryptowallets, communication/messaging and file transfer/storage software. This malicious program can exfiltrate different data from Chromium browsers, specifically information from the browser's SQlite database.
The data can include browser cookies, autofills (automatically-completed fields in websites such as names, surnames, addresses, email addresses, etc.) and credit card details.
GrandSteal can also steal information from the Gecko browser engine, which was developed by Mozilla and is used in Firefox browsers, the Thunderbird email client and countless other products/projects. As with Chromium, it can locate and steal browser cookies, account credentials (log-ins and passwords) and other important information.
The cryptocurrency wallets that can be stolen are Bitcoin, Bytecoin, Dash, Electrum, Ethereum, Exodus, Litecoin and Monero. From the Discord application and Telegram messenger, GrandSteal attempts to recover previous communication sessions and extort information.
The targeted file transfer/storage software is FileZilla. Additionally, this malware can steal files from users' Personal Directories including the Desktop, Favorites and Personal folders. GrandSteal also targets Remote Desktop Protocol (RDP) credentials, which can potentially be used to gain further access and control over the infected system.
The stolen data can be misused in various ways. To summarize, the threats posed by GrandSteal include (but are not limited to) serious privacy and financial issues, and identity theft. To ensure device/data integrity and user safety, remove this malware immediately.
| Name | GrandSteal malware |
| Threat Type | Trojan, password-stealing virus, banking malware, spyware. |
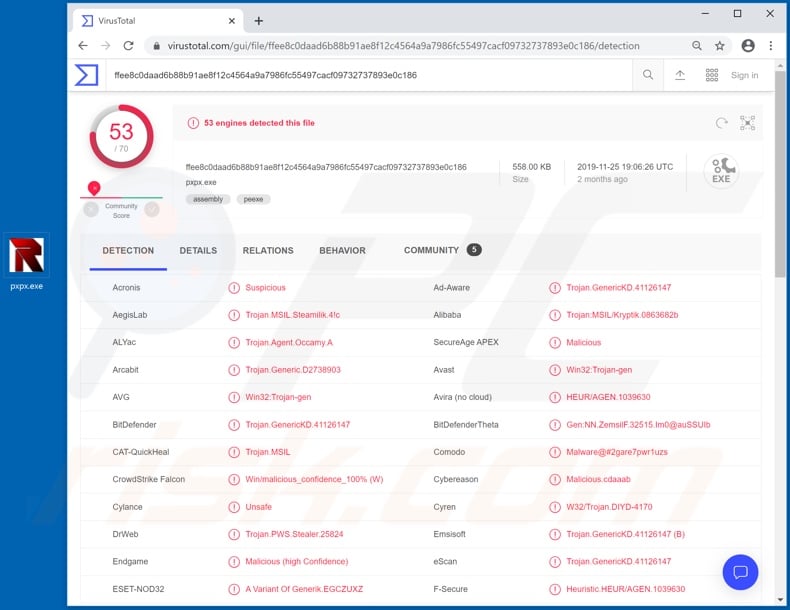
| Detection Names (GrandSteal - pxpx.exe) |
Avast (Win32:Trojan-gen), BitDefender (Trojan.GenericKD.41126147), ESET-NOD32 (A Variant Of Generik.EGCZUXZ), Kaspersky (HEUR:Trojan.MSIL.Steamilik.gen), Full List (VirusTotal) |
| Detection Names (infectious attachments) |
Avast (Other:Malware-gen [Trj]), BitDefender (VB:Trojan.VBA.Downloader.UY), ESET-NOD32 (VBA/TrojanDownloader.Agent.RPE), Kaspersky (HEUR:Trojan-Downloader.Script.Generic), Full List (VirusTotal - 190720_Bewerbung_Kaufm_Angestellte_.doc and VirusTotal - 180718_arbeitszeugnisse_aktuell.doc) |
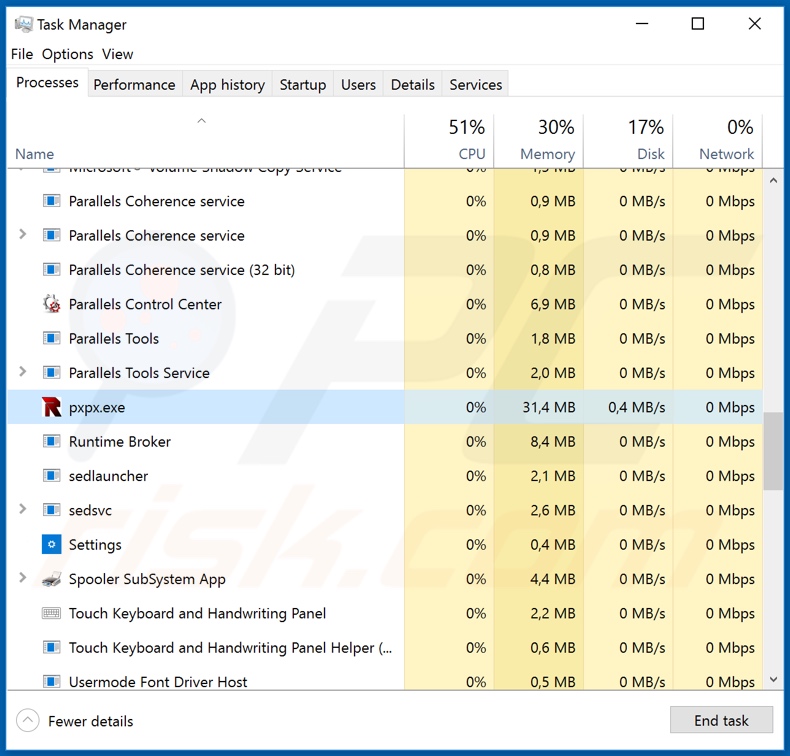
| Malicious Process Name(s) | pxpx.exe (the process name can vary depending on the malicious executable). |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Baldr, Bebloh, Megumin are some other examples of information-stealing malware. Malicious software has various dangerous capabilities. For example, data exfiltration, download/installation of additional malware, remote access, cryptocurrency mining, data encryption and countless others.
Despite these diverse capabilities, all malicious programs have just one purpose: to generate revenue for the developers. Therefore, regardless of how they operate, you should eliminate all malicious content immediately upon detection.
How did GrandSteal infiltrate my computer?
GrandSteal has proliferate via spam email campaigns. The emails used to proliferate this malicious program have been presented as job applications, including the CVs as attachments. Spam campaigns are commonly used to spread malware. Infections are caused through the dangerous files attached (or links, which lead to them).
These files come in variety of formats such as Microsoft Office and PDF documents, archive and executable files, JavaScript, etc. When they are executed, run or otherwise opened, the infection process starts. For example, once opened, MS Office documents urge users to enable macro commands (i.e., enable editing).
After they are enabled, malicious macros begin downloading/installing malware. Note that the infection process begins automatically when the document is opened in Microsoft Office programs released before 2010. Other popular sources of infection are trojans, illegal activation ("cracking") tools, fake updaters and untrusted download channels.
Trojans are malicious programs cable of causing chain infections. Rather than activating licensed products, illegal activation tools ("cracks") can download/install malware. Rogue updaters infect systems by exploiting weaknesses of outdated software or simply installing malicious programs rather than the updates.
Free file-hosting and unofficial sites, Peer-to-Peer sharing networks and other third party downloaders are untrusted and can offer malicious content for downloading.
How to avoid installation of malware
Do not open suspicious or irrelevant emails, especially those received from unknown senders. Never open attachments or links present in these messages - doing so can result in an infection. Use only official and verified download sources. Activate and update programs using functions/tools provided by legitimate developers.
To ensure device/user safety, have reputable anti-virus/anti-spyware installed and kept up to date. This software should be used to run regular system scans and for the removal of detected/potential threats. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Screenshot of deceptive email used to spread GrandSteal malware:
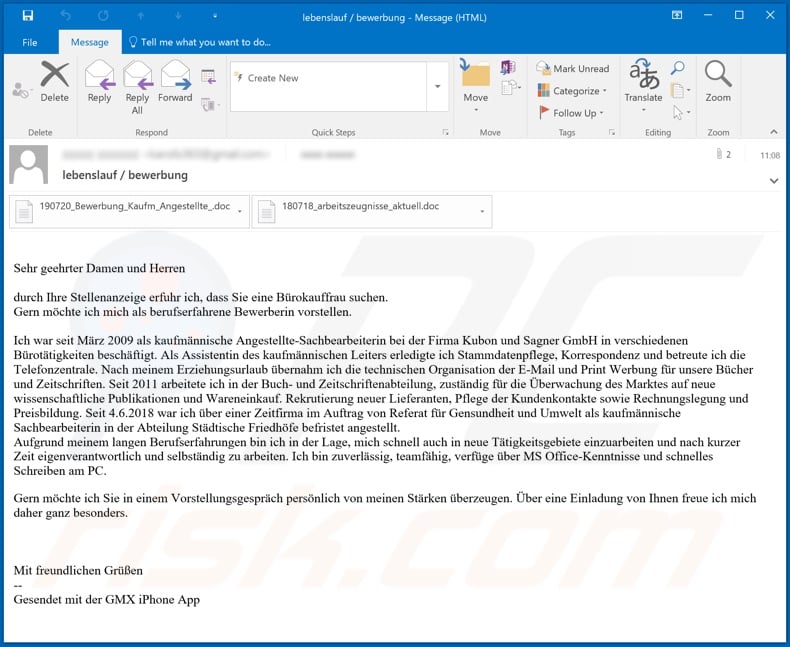
Text presented in this email:
Sehr geehrter Damen und Herren
durch Ihre Stellenanzeige erfuhr ich, dass Sie eine Bürokauffrau suchen.
Gern möchte ich mich als berufserfahrene Bewerberin vorstellen.Ich war seit März 2009 als kaufmännische Angestellte-Sachbearbeiterin bei der Firma Kubon und Sagner GmbH in verschiedenen Bürotätigkeiten beschäftigt. Als Assistentin des kaufmännischen Leiters erledigte ich Stammdatenpflege, Korrespondenz und betreute ich die Telefonzentrale. Nach meinem Erziehungsurlaub übernahm ich die technischen Organisation der E-Mail und Print Werbung für unsere Bücher und Zeitschriften. Seit 2011 arbeitete ich in der Buch- und Zeitschriftenabteilung, zuständig für die Überwachung des Marktes auf neue wissenschaftliche Publikationen und Wareneinkauf. Rekrutierung neuer Lieferanten, Pflege der Kundenkontakte sowie Rechnungslegung und Preisbildung. Seit 4.6.2018 war ich über einer Zeitfirma im Auftrag von Referat für Gensundheit und Umwelt als kaufmännische Sachbearbeiterin in der Abteilung Städtische Friedhöfe befristet angestellt.
Aufgrund meinem langen Berufserfahrungen bin ich in der Lage, mich schnell auch in neue Tätigkeitsgebiete einzuarbeiten und nach kurzer Zeit eigenverantwortlich und selbständig zu arbeiten. Ich bin zuverlässig, teamfähig, verfüge über MS Office-Kenntnisse und schnelles Schreiben am PC.
Gern möchte ich Sie in einem Vorstellungsgespräch persönlich von meinen Stärken überzeugen. Über eine Einladung von Ihnen freue ich mich daher ganz besonders.Mit freundlichen Grüßen
--
Gesendet mit der GMX iPhone App
Appearance of the infectious attachment - "190720_Bewerbung_Kaufm_Angestellte_.doc" (GIF):
Text presented in this document:
SYSTEM ERROR: 0xc004f069 (syntax error: 0xc004f069-90-IsaDLL#211%)
The program can’t start because api-ms-win-crt-stdio-l1-1-0.dll is missing from your computer.
For reinstalling the program file to fix the problem, please restart command:For more information, please visit :
hxxp://support.microsoft.com/kb/899921
hxxp://support.microsoft.com/kb/902312Microsoft © 2020
LebenslaufANGABEN ZUR PERSON
St.Augustinus Straße 20, 81825 München
+49 176 23893559
ANGESTREBTE AUSBILDUNGKauffrau für E-CommerceSCHUL- UND BER UNG
01.10.2017–HeuteBachelorstudium Publizistik&Kommunikationswissenschaften
Hauptuni Wien, Wien (Österreich)
2014–2016 Allgemeine Hochschulreife
Städtisches Lion-Feuchtwanger- Gymnasium, München (Deutschland)
2013–2014 Mittlere Hochschulreife
Adalbert-Stifter-Realschule, München (Deutschland)
BERUFSERFAHRUNG
PERSÖNLICHE FÄHIGKEITENPraktikum im Bereich Marketing
Avanade Österreich GmbH, Wien (Österreich)
Praktikum im
Brainloop AG, München (Deutschland)
Muttersprache(n)Deutsch
Fremdsprache(n)
VERSTEHENSPRECHENSCHREIBENHörenLesenAn GesprächenZusammenhängend
teilnehmenes SprechenEnglisch C1 C1 C1 C1 B2
Französisch A2 A2 A1 A1 A1
Niveaus: A1 und A2:- C1 und C2: Kompetent Gemeinsamer Europäischer Referenzrahmen für SprachenSeite 1 / 2
Kommunikative Fähigkeiten-Gute kommunikative Fähigkeiten, die -Kraft in der Gastronomie erworben habe-Stärke bei schriftlichen und mündlichen Auseinandersetzungen, die ich durch meine
Erfahrungen bei innerschulischen vertieft habe
Digitale FähigkeitenSELBSTBEURTEILUNG
Daten-Kommunikation Erstellung von Sicherheit Problemlösung
Verarbeitung Inhalten
Selbstständige Elementare Elementare Selbstständige Elementare
Verwendung Verwendung Verwendung Verwendung Verwendung
Digitale Fähigkeiten - Raster zur SelbstbewertungSeite 2 / 2
Appearance of the infectious attachment - "180718_arbeitszeugnisse_aktuell.doc" (GIF):
Text presented in this document:
SYSTEM ERROR: 0xc004f069 (syntax error: 0xc004f069-90-IsaDLL#211%)
The program can’t start because api-ms-win-crt-stdio-l1-1-0.dll is missing from your computer.
For reinstalling the program file to fix the problem, please restart command:
For more information, please visit :
hxxp://support.microsoft.com/kb/899921
hxxp://support.microsoft.com/kb/902312Microsoft © 2020
München, den 07.02.2020
Bewerbung als Kaufmännische Mitarbeiterin
Sehr geehrter Dame and Herren,
Sie suchen eine entscheidungsfreudige kaufmännische Mitarbeiterin, ...
Ob telefonisch oder persönlich, im Kontakt mit Kunden sorge ich aufgrund meines sympathischen Auftretens für eine angenehme Gesprächsatmosphäre, gebe angemessen ...Ascher-Noerpel im Kundenservice hervorheben.
Dort lag mein Schwerpunkt in der:
• Bearbeitung von Kundenanfragen z.B. Reklamation
• ...Kontrolle und Abrechnung doppelter Anfahrten
• Überarbeitung + Kontrolle von ...und stelle den Kunden stets in den Mittelpunkt. Mein Umfeld schätzt meine Zuverlässigkeit und mein Verantwortungsbewusstsein, ich gelte als ehrlich, ausdauernd und zielstrebig.
Ich bin vielseitig interessiert, sehe neue Aufgaben als Herausforderung und zeige viel Engagement und Eigeninitiative.Die Betreuung meiner Kinder ist durch die Schule gesichert.
Sollten Ihnen meine ...zur Verfügung
- 05/2016 - 06/2019 Umschulung zur Kauffrau für Büromanagement (IHK) Drexler Seminare GmbH, München Wahlqualifikation: • Kaufmännische Steuerung und Kontrolle • Kaufmännische Abläufe in kleinen und mittleren 05/2017 – 07/2018 Pflichtpraktikum im Rahmen der Umschulung zur Kauffrau für Büromanagement, grapho metronic Mess- und Regeltechnik GmbH • Beschaffung und Vertrieb von Waren und Dienstleistungen • Fakturieren von Rechnungen • Stammdatenpflege im ERP-System beitung • Korrespondenz und , Weimar 08/1999 – 08/2001 Kontrolleurin und Energieabrechnung, Energozentr AG, Pawlodar 09/1994 – 04/1999 Sekretärin, Techwest GmbH, Pawlodar Berufsausbildung Studium 09/1987 – 06/1994 Studium der Fachrichtung Elektrotechnik, Staatliche technische Universität Pawlodar, Kasachstan Abschluss: Diplom-Ingenieur (FH) Natalya Eckardt Freienfelsstraße 13, 81249 München 089 21594576, 0152 04396030 natalya.eckardt@freenet.de Schulische Ausbildung 09/1977 – 06/1987 Realschule Pawlodar, Abschluss: Mittlere Reife Sonstige Kenntnisse Sprachen Russisch Englisch Grundkenntnisse IT MS Office Persönliche Daten Name, Vorname Eckardt, Natalya Geburtsdatum und Ort 08.09.1970 in Pawlodar, deutsch Familienstand verheiratet, 2 Kinder (*1988, *2007)
Mit freundlichen Grüßen
Screenshot of GrandSteal malware's process in Windows Task Manager ("pxpx.exe"):
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is GrandSteal?
- STEP 1. Manual removal of GrandSteal malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion