How to remove BlackRock malware from Android smartphones
TrojanAlso Known As: BlackRock banking malware
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is BlackRock?
BlackRock is malicious software (banking malware) that specifically targets the Android operating systems on smartphones. BlackRock was first spotted in the second quarter of 2020.
This mobile malware is created using the source code of other malicious software called Xerxes (a strain of another banking Trojan called LokiBot). Note that BlackRock targets non-financial applications (e.g., dating, social media, communication) apps as well. I.e., cyber criminals behind BlackRock also target users who do not use mobile banking apps.

BlackRock in detail
When an unsuspecting user launches BlackRock mobile malware, this app hides its icon from the app drawer (a screen in an Android device that shows icons of installed applications).
It then asks for Accessibility Service privileges, often by displaying fake notifications offering to use Google updates.
After gaining Accessibility Service privileges, BlackRock grants itself additional permissions that allow it to function without needing any further involvement of its victims.
Research shows that BlackRock can be used to perform overlay attacks, send SMS messages to specified numbers or the numbers on the contact list of the infected devices, run applications, gather text displayed on the screen and received notifications, prevent the screen from locking, unlock the Home screen.
BlackRock can also be used to send requests for admin privileges and collect information about the infected device.
Note that BlackRock prevents victims from removing it from the infected devices by redirecting them to the Home screen when victims open certain antivirus applications or cleaners.
BlackRock can detect when victims open apps such as AVG, Avast, BitDefender, ESET, Kaspersky, McAfee, SD Maid, Symantec, Superb Cleaner, TotalCommander, or TrendMicro.
As mentioned, BlackRock can be used to perform overlay attacks. This mobile malware can display different login screens asking users to enter credentials (username, email address, password) or card grabber overlays asking them to enter credit card details.
This Trojan differs from other banking Trojans in that it targets users of social, shopping, communication, lifestyle, dating, entertainment, music, news and other applications. There are more than three hundred applications targeted by BlackRock malware.
Some examples of applications that BlackRock targets to steal login credentials are eBay, Amazon, Barclays, Gmail, Neflix, PayPal Mobile Cash, and Uber.
Examples of applications that this mobile malware targets to steal credit card details are Facebook, Instagram, Skype, Snapchat, Telegram, TikTok, Tinder, Twitter, WhatsApp, and YouTube.
| Name | BlackRock banking malware |
| Threat Type | Android malware, malicious application, unwanted application. |
| Detection Names | Avast (Android:BlackRock-B [Bank]), BitDefenderFalx (Android.Trojan.FakeApp.FY), ESET-NOD32 (A Variant Of Android/TrojanDropper.Agent.HCQ), Kaspersky (HEUR:Trojan-Dropper.AndroidOS.Hqwar.ek), Full List (VirusTotal) |
| Symptoms | The device is running slow, system settings are modified without user's permission, dubious applications appear, data and battery usage is increased significantly, browsers redirect to bogus websites, intrusive advertisements are delivered. |
| Distribution methods | Deceptive websites (download pages for fake applications), Infected email attachments, malicious online advertisements, social engineering, deceptive applications, scam websites. |
| Damage | Stolen personal information (private messages, logins/passwords, etc.), decreased device performance, battery is drained quickly, decreased Internet speed, large data losses, monetary losses, stolen identity (malicious apps might abuse communication apps). |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
BlackRock in general
In conclusion, BlackRock malware is used to extract login credentials to steal personal accounts, and credit card details. Stolen data could be used make fraudulent purchases and transactions, steal identities, send spam and malspam (deliver malware), and for other purposes. Stolen data could be sold to third parties (other cyber criminals).
BlackRock can receive commands from a C2 server, including commands to send SMS messages. In this way, the attackers use BlackRock to send spam, trick recipients into installing this app onto their devices, etc.
If there is any reason to suspect that BlackRock is installed on a device, removed it as soon as possible. More examples of Android malware are FluBot, Oscorp, and ThiefBot.
How did BlackRock infiltrate my device?
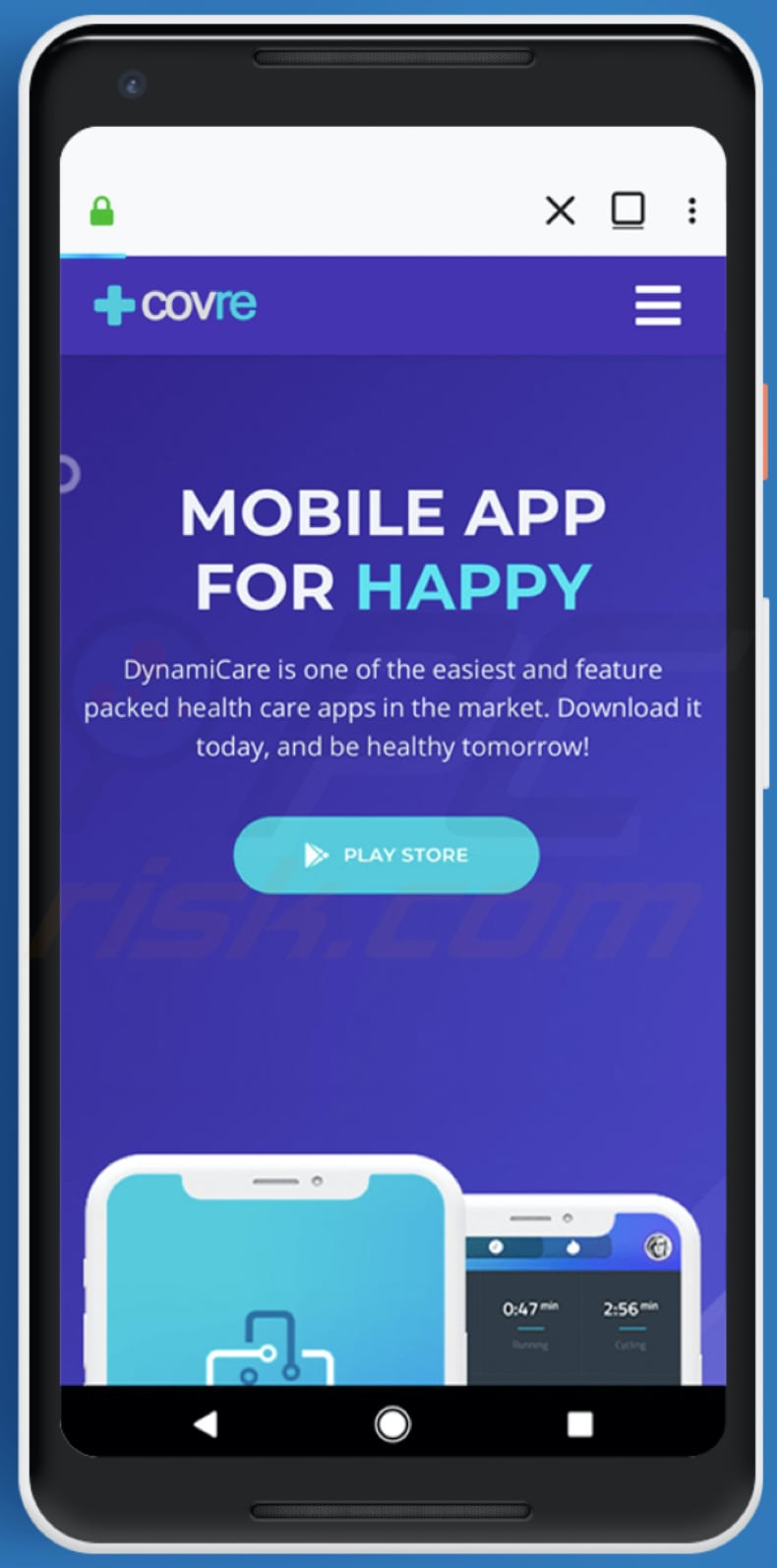
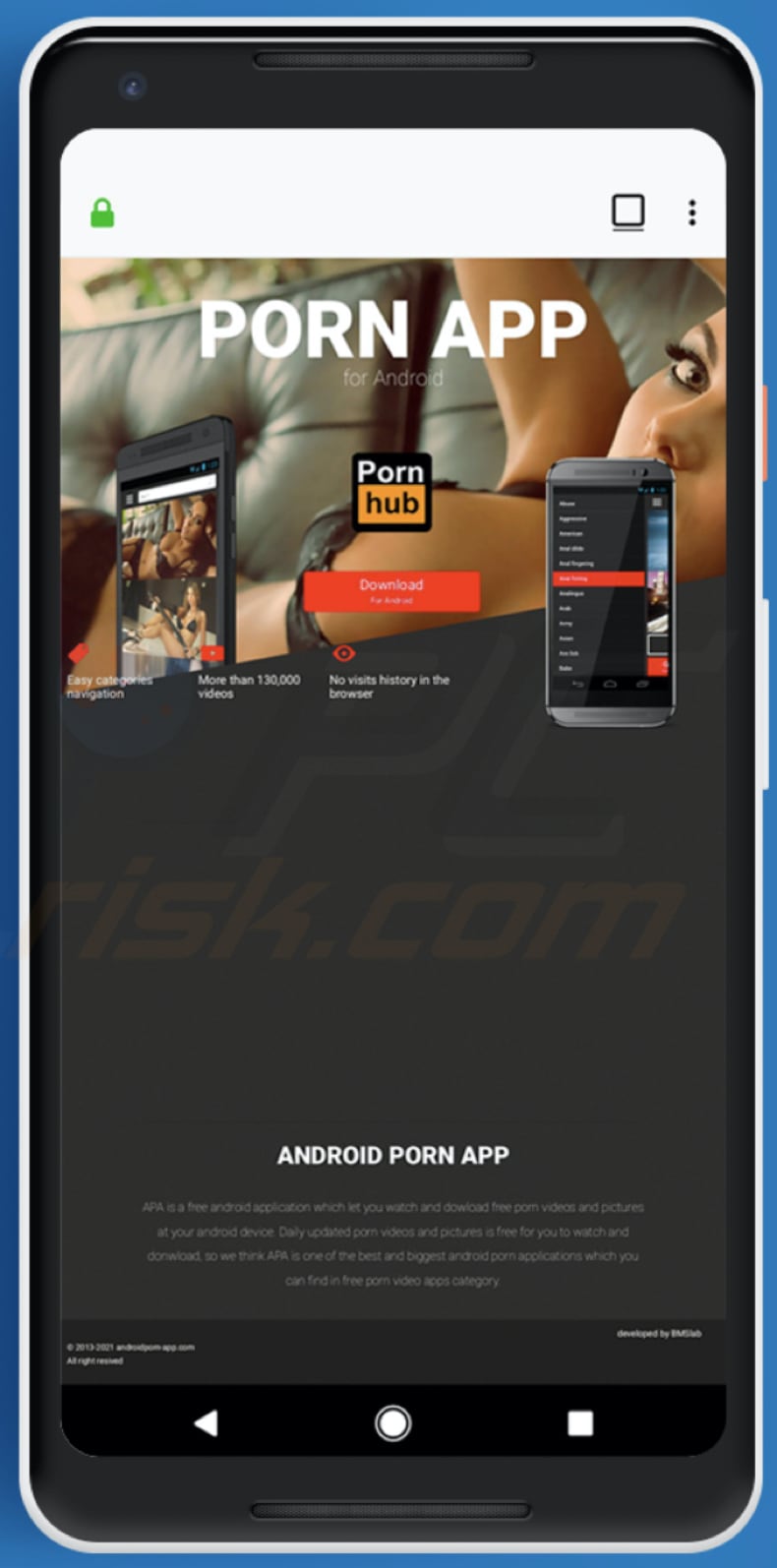
Research shows that BlackRock is distributed using deceptive websites designed to trick visitors into downloading and installing fake DynamiCare, Clubhouse applications, and some pornography applications.
It is very likely that cyber criminals also use names of other well-known apps to disguise BlackRock malware.
Cyber criminals can distribute mobile malware using SMS messages (e.g., fake notifications about packages received from legitimate couriers), phishing emails, and other channels. In some cases, they use Google Play to distribute their malicious software.
How to avoid installation of malware
To avoid infecting the system with malware spread through spam mail, you are strongly advised not to open suspicious or irrelevant emails, especially those with any attachments or links present in them. Use official and verified download channels.
Additionally, all programs must be activated and updated with tools/functions provided by legitimate developers, since illegal activation tools ("cracks") and third party updaters commonly proliferate malicious software.
To ensure device integrity and user safety, it is paramount to have reputable anti-virus/anti-spyware software installed and kept updated. Furthermore, use these programs to run regular system scans and to remove detected/potential threats.
Do not trust irrelevant emails that contain attachments or website links, especially if received from unknown, suspicious addresses.
Fake update tools infect systems by installing malicious programs rather than updates/fixes for installed software, or by exploiting bugs/flaws of outdated software that is installed on the computer.
Further encryption of any unaffected files can be prevented by uninstalling the ransomware, however, already compromised files remain encrypted even after removal of the rogue software and can only be recovered from a backup.
Screenshot of the download page for a fake DynamiCare app used to distribute BlackRock:
Screenshot of the download page for a fake Clubhouse app used to distribute BlackRock:

Screenshot of the download page for a pornography app used to distribute BlackRock:
Quick menu:
- Introduction
- How to delete browsing history from the Chrome web browser?
- How to disable browser notifications in the Chrome web browser?
- How to reset the Chrome web browser?
- How to delete browsing history from the Firefox web browser?
- How to disable browser notifications in the Firefox web browser?
- How to reset the Firefox web browser?
- How to uninstall potentially unwanted and/or malicious applications?
- How to boot the Android device in "Safe Mode"?
- How to check the battery usage of various applications?
- How to check the data usage of various applications?
- How to install the latest software updates?
- How to reset the system to its default state?
- How to disable applications that have administrator privileges?
Delete browsing history from the Chrome web browser:
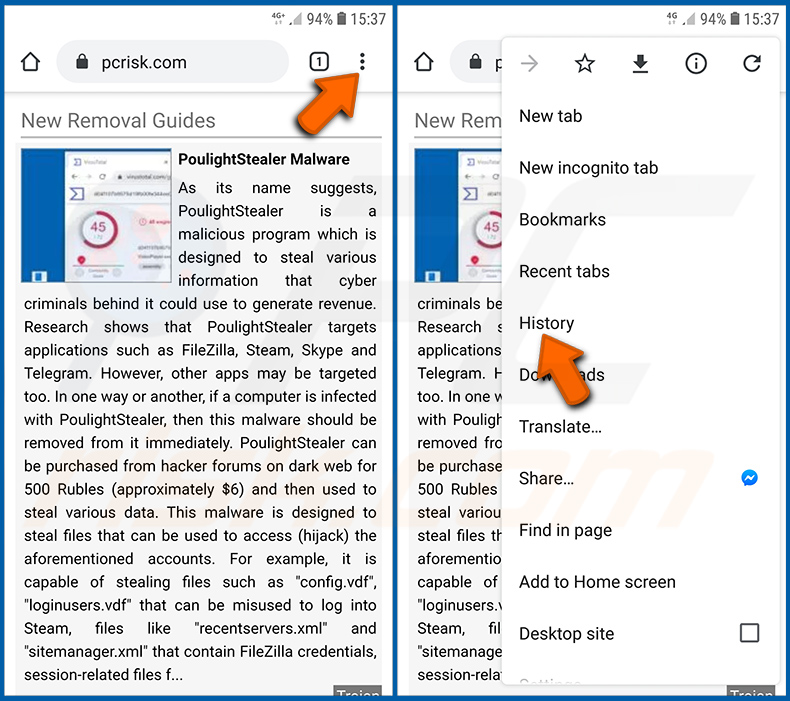
Tap the "Menu" button (three dots on the right-upper corner of the screen) and select "History" in the opened drop-down menu.
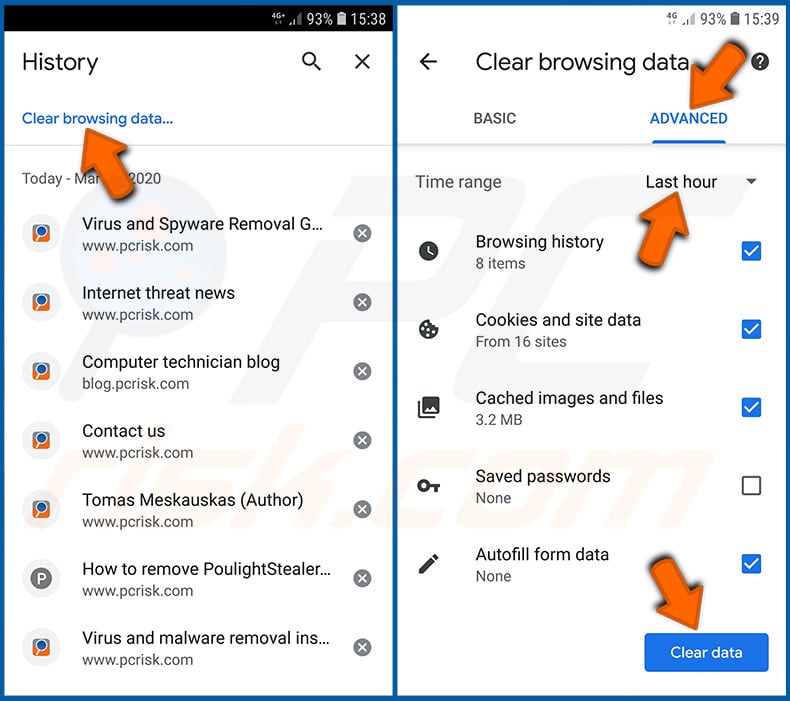
Tap "Clear browsing data", select "ADVANCED" tab, choose the time range and data types you want to delete and tap "Clear data".
Disable browser notifications in the Chrome web browser:
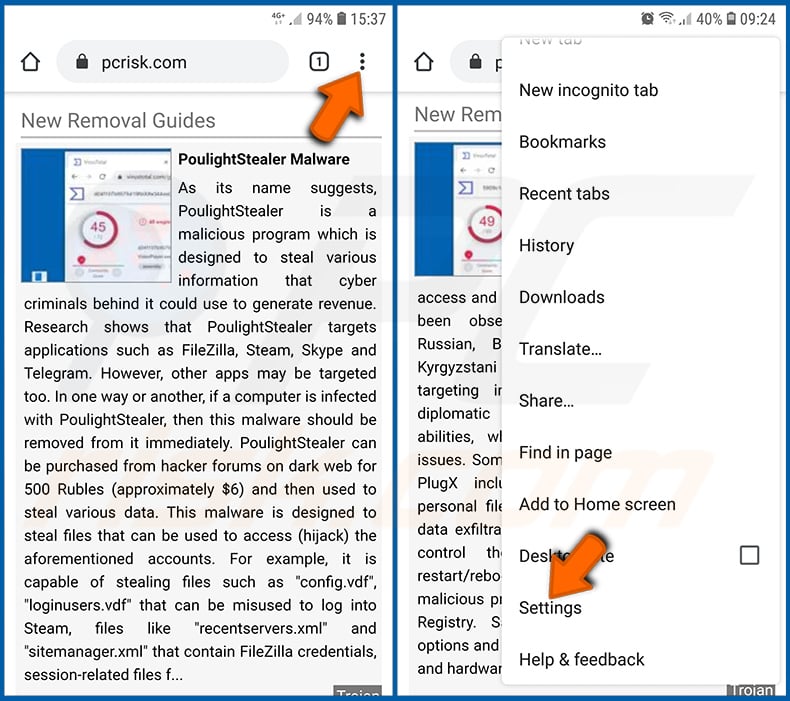
Tap the "Menu" button (three dots on the right-upper corner of the screen) and select "Settings" in the opened drop-down menu.
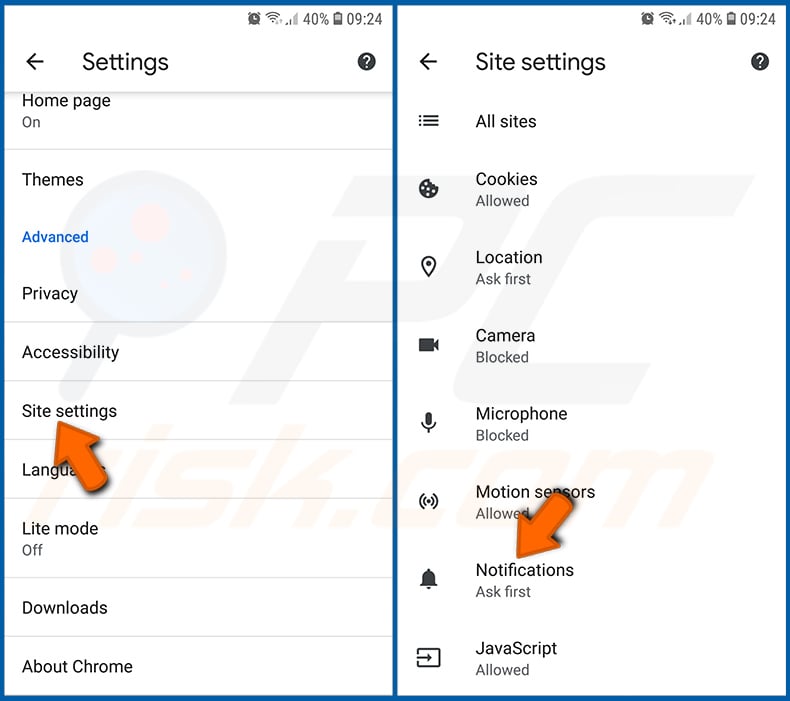
Scroll down until you see "Site settings" option and tap it. Scroll down until you see "Notifications" option and tap it.
Find the websites that deliver browser notifications, tap on them and click "Clear & reset". This will remove permissions granted for these websites to deliver notifications, however, once you visit the same site again, it may ask for a permission again.
You can choose whether to give these permissions or not (if you choose to decline the website will go to "Blocked" section and will no longer ask you for the permission).
Reset the Chrome web browser:
Go to "Settings", scroll down until you see "Apps" and tap it.
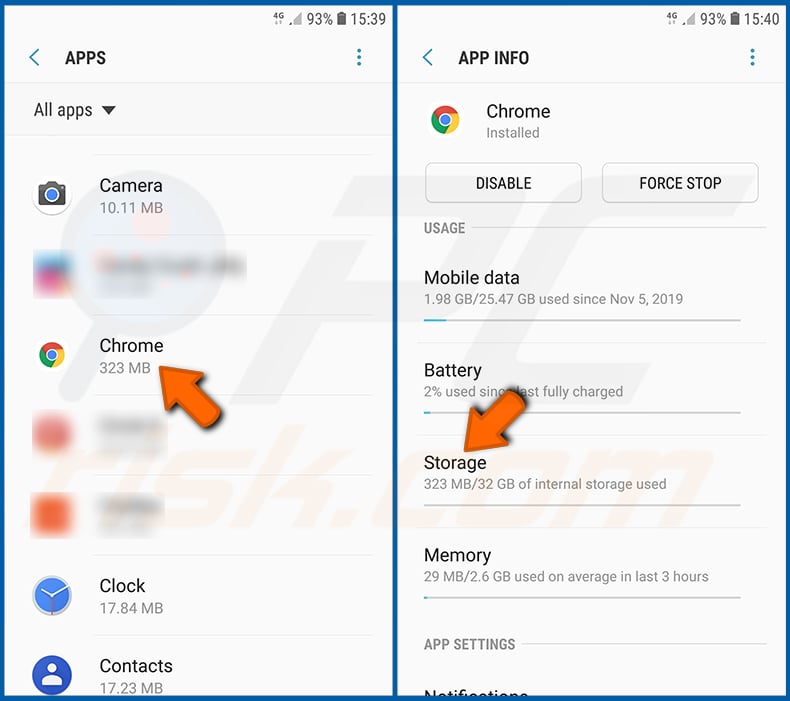
Scroll down until you find "Chrome" application, select it and tap "Storage" option.
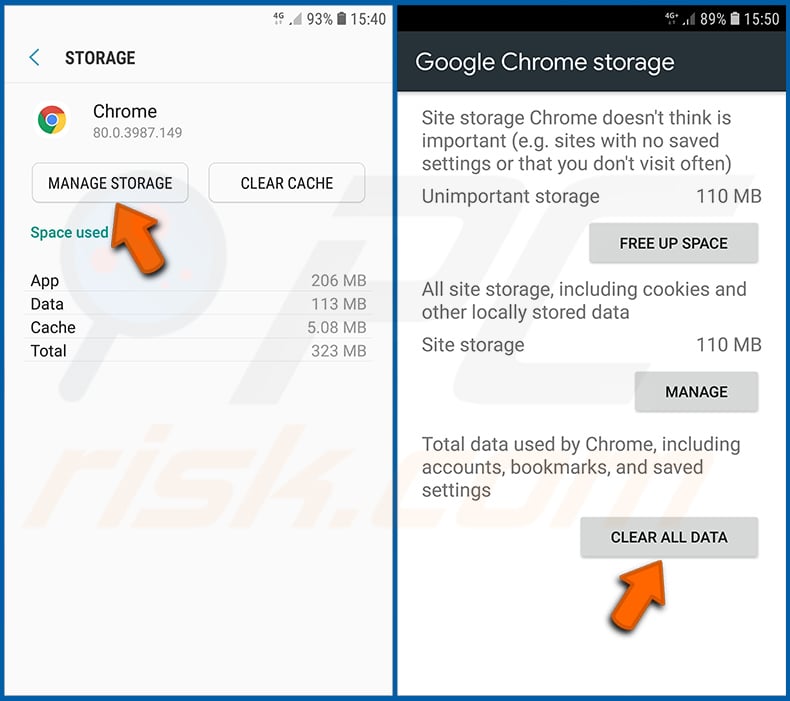
Tap "MANAGE STORAGE", then "CLEAR ALL DATA" and confirm the action by taping "OK". Note that resetting the browser will eliminate all data stored within. This means that all saved logins/passwords, browsing history, non-default settings and other data will be deleted.
You will also have to re-login into all websites.
Delete browsing history from the Firefox web browser:
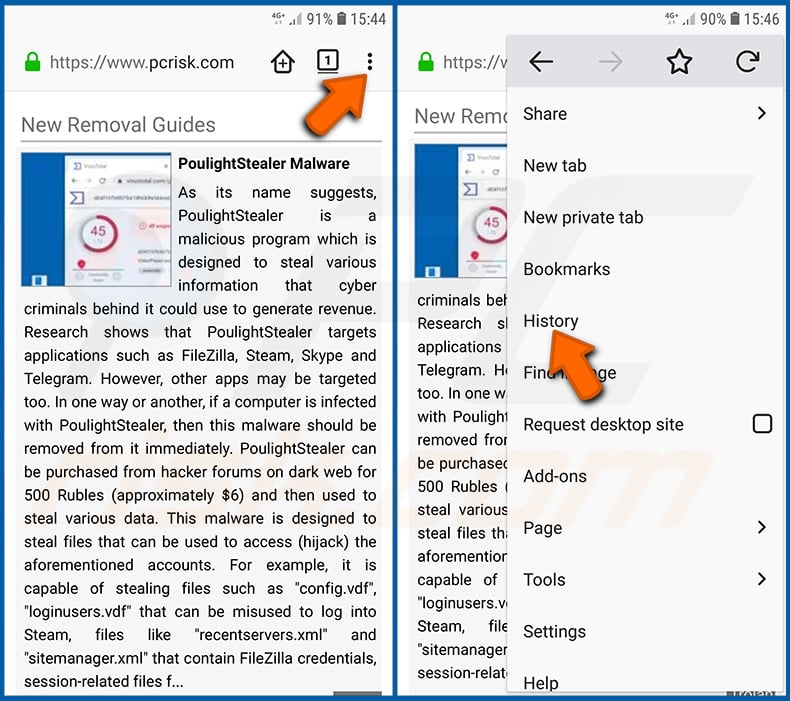
Tap the "Menu" button (three dots on the right-upper corner of the screen) and select "History" in the opened drop-down menu.
Scroll down until you see "Clear private data" and tap it. Select data types you want to remove and tap "CLEAR DATA".
Disable browser notifications in the Firefox web browser:
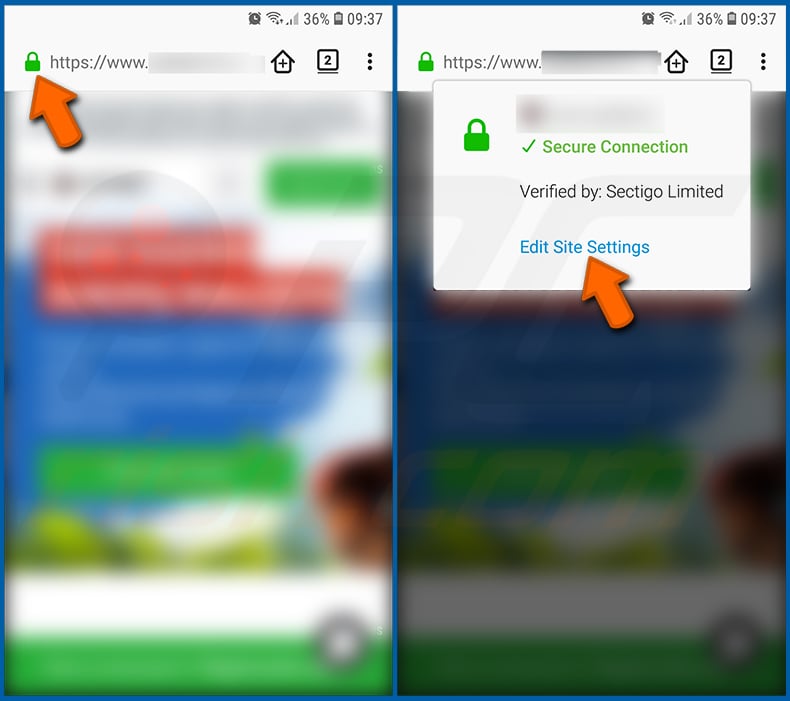
Visit the website that is delivering browser notifications, tap the icon displayed on the left of URL bar (the icon will not necessarily be a "Lock") and select "Edit Site Settings".
In the opened pop-up opt-in the "Notifications" option and tap "CLEAR".
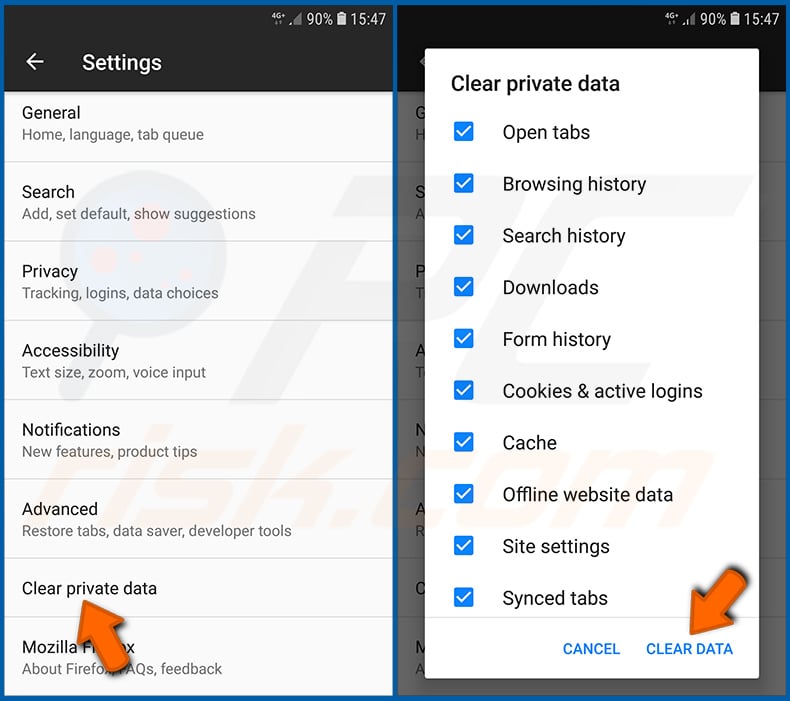
Reset the Firefox web browser:
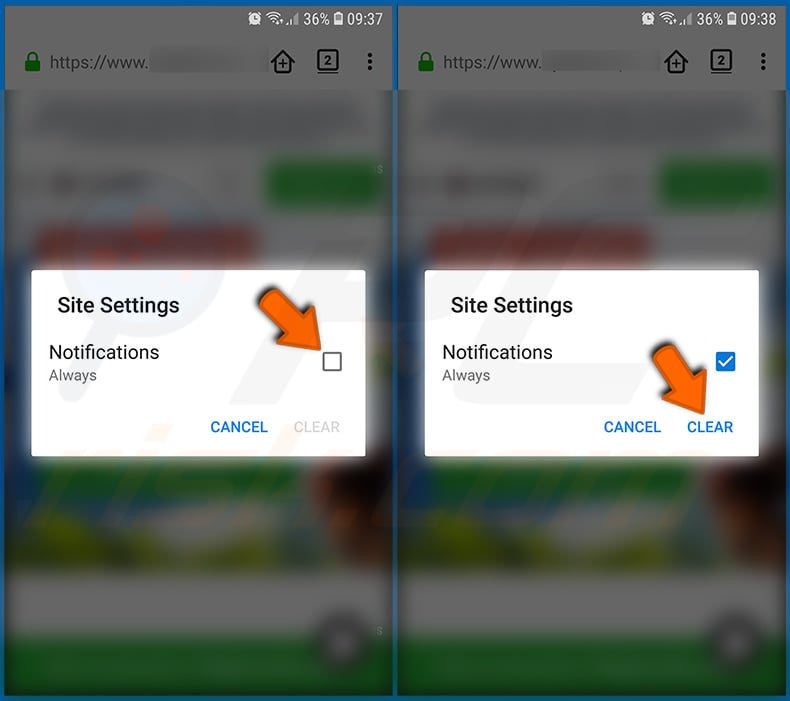
Go to "Settings", scroll down until you see "Apps" and tap it.
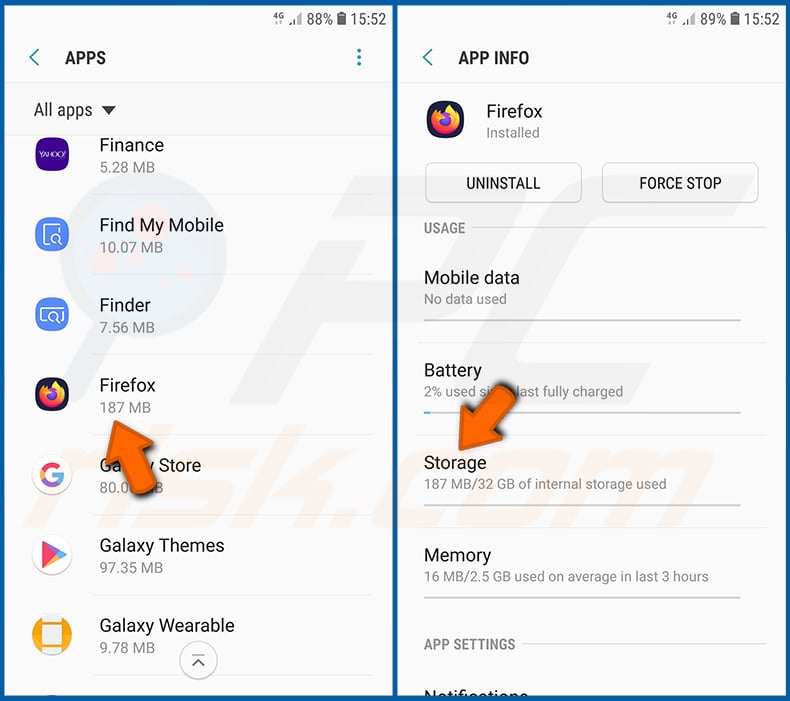
Scroll down until you find "Firefox" application, select it and tap "Storage" option.
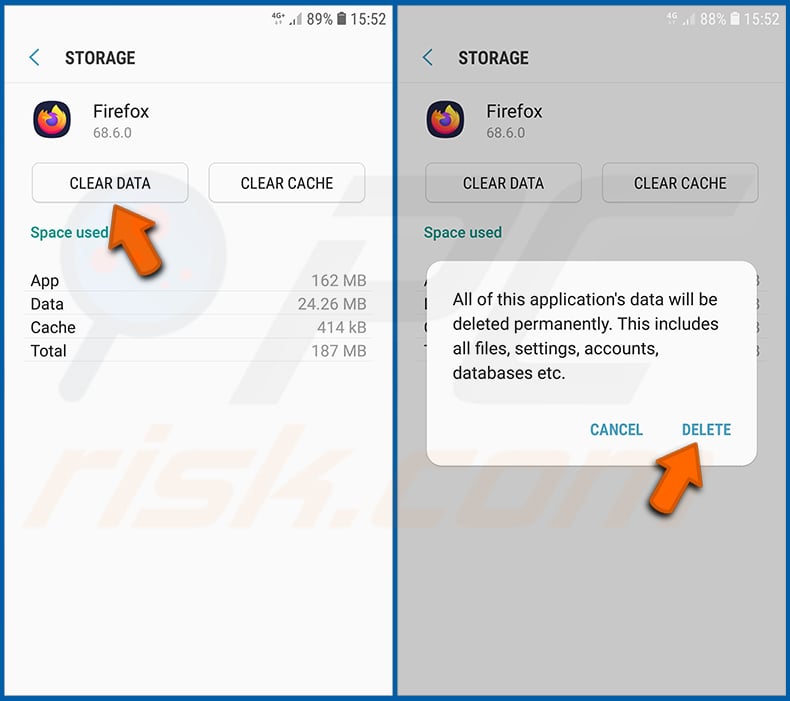
Tap "CLEAR DATA" and confirm the action by taping "DELETE". Note that resetting the browser will eliminate all data stored within. This means that all saved logins/passwords, browsing history, non-default settings and other data will be deleted. You will also have to re-login into all websites.
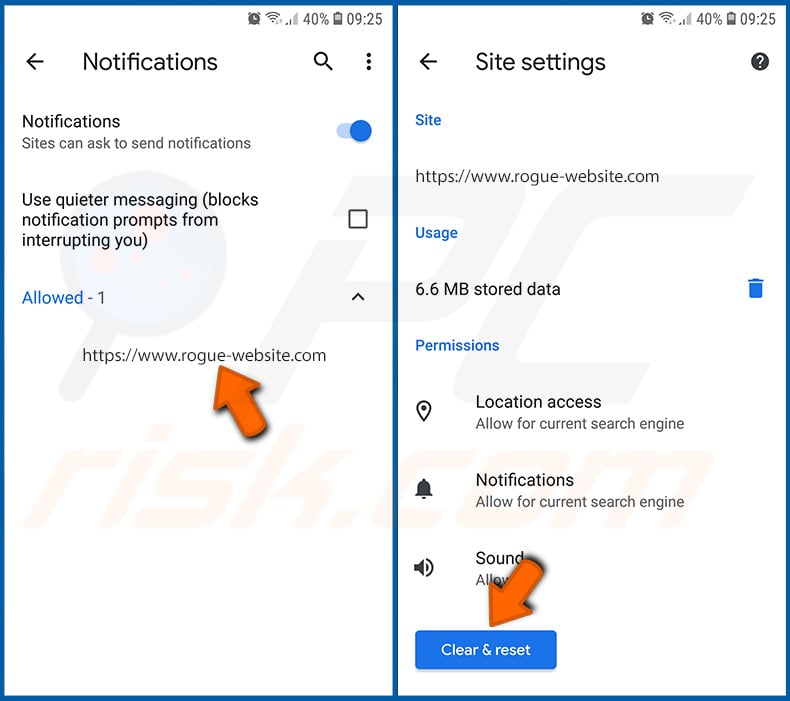
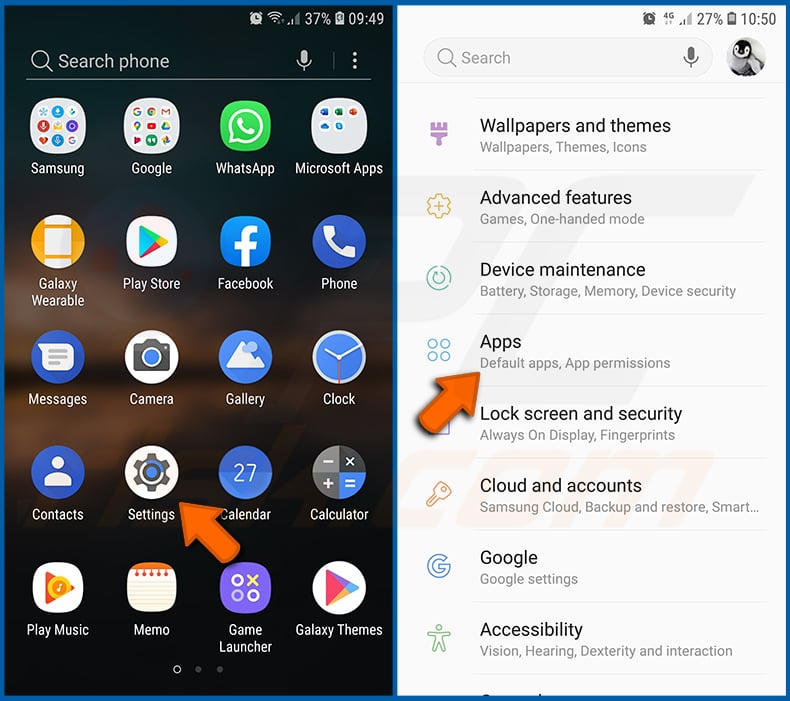
Uninstall potentially unwanted and/or malicious applications:
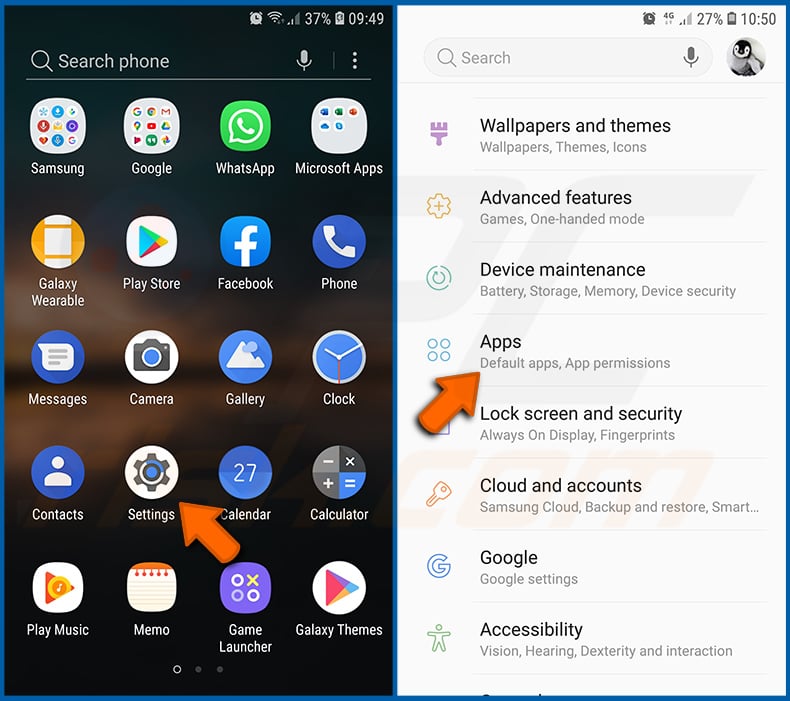
Go to "Settings", scroll down until you see "Apps" and tap it.
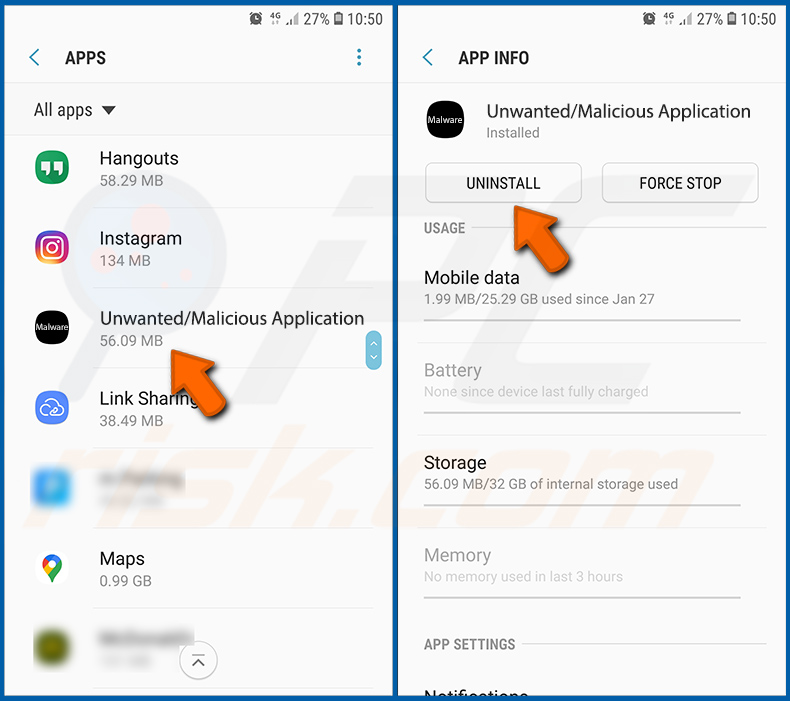
Scroll down until you see a potentially unwanted and/or malicious application, select it and tap "Uninstall". If, for some reason, you are unable to remove the selected app (e.g., you are prompted with an error message), you should try using the "Safe Mode".
Boot the Android device in "Safe Mode":
The "Safe Mode" in Android operating system temporarily disables all third-party applications from running. Using this mode is a good way to diagnose and solve various issues (e.g., remove malicious applications that prevent users you from doing so when the device is running "normally").
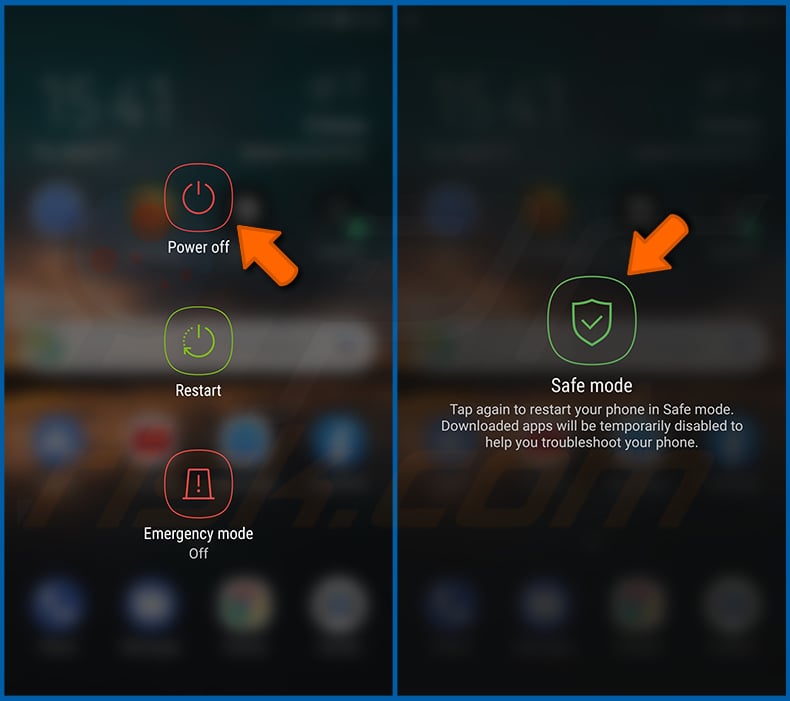
Push the "Power" button and hold it until you see the "Power off" screen. Tap the "Power off" icon and hold it. After a few seconds the "Safe Mode" option will appear and you'll be able run it by restarting the device.
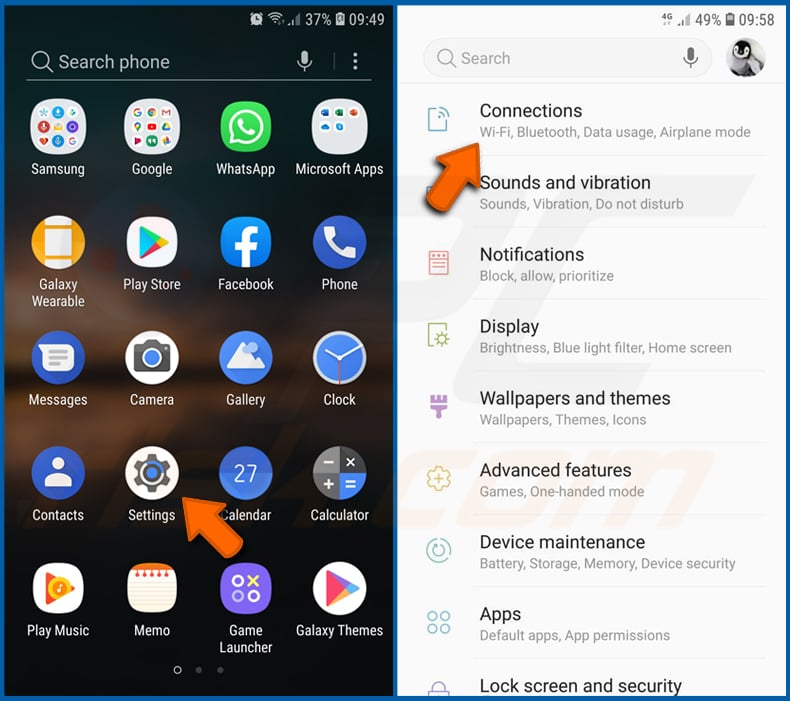
Check the battery usage of various applications:
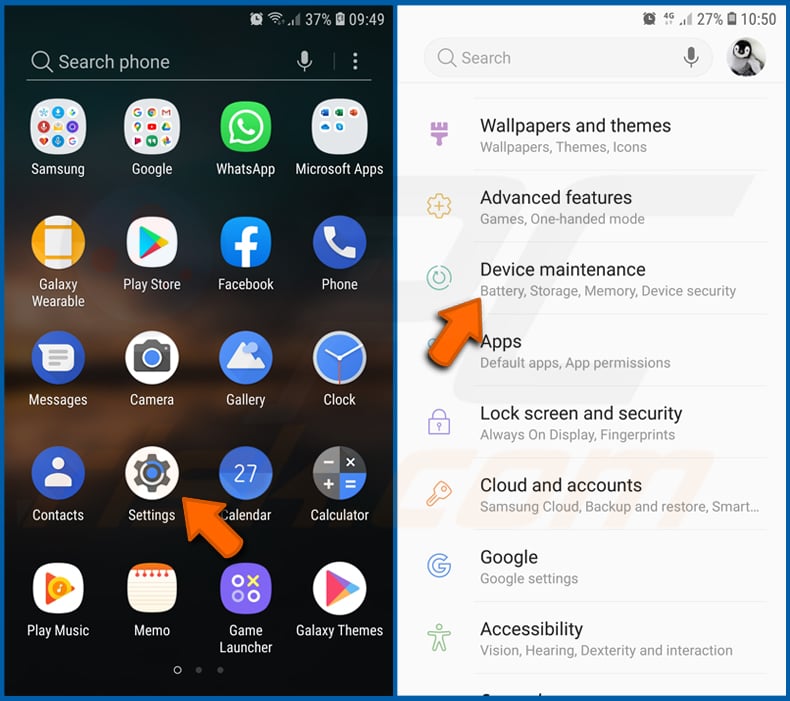
Go to "Settings", scroll down until you see "Device maintenance" and tap it.
Tap "Battery" and check the usage of each application. Legitimate/genuine applications are designed to use as little energy as possible in order to provide the best user experience and to save power. Therefore, high battery usage may indicate that the application is malicious.
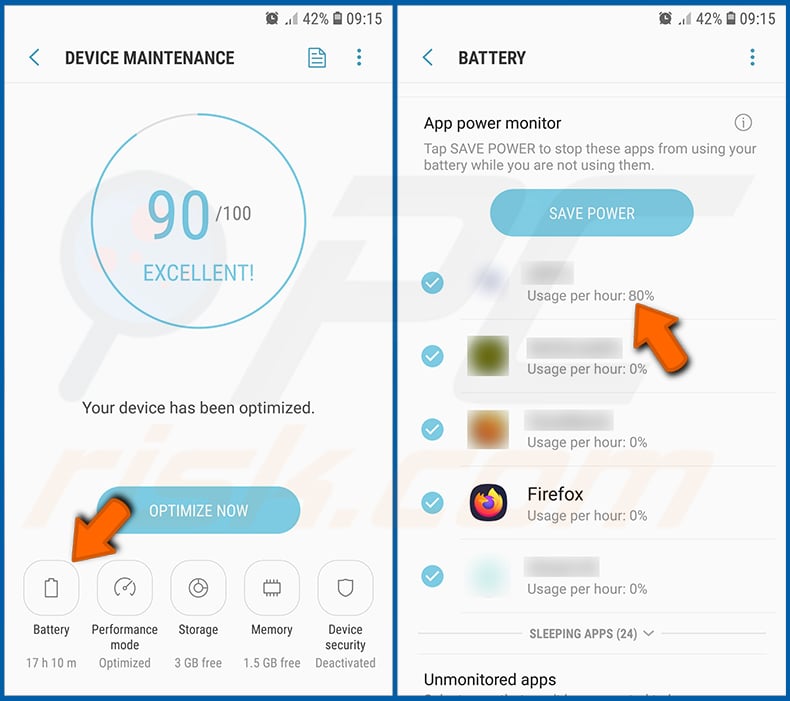
Check the data usage of various applications:
Go to "Settings", scroll down until you see "Connections" and tap it.
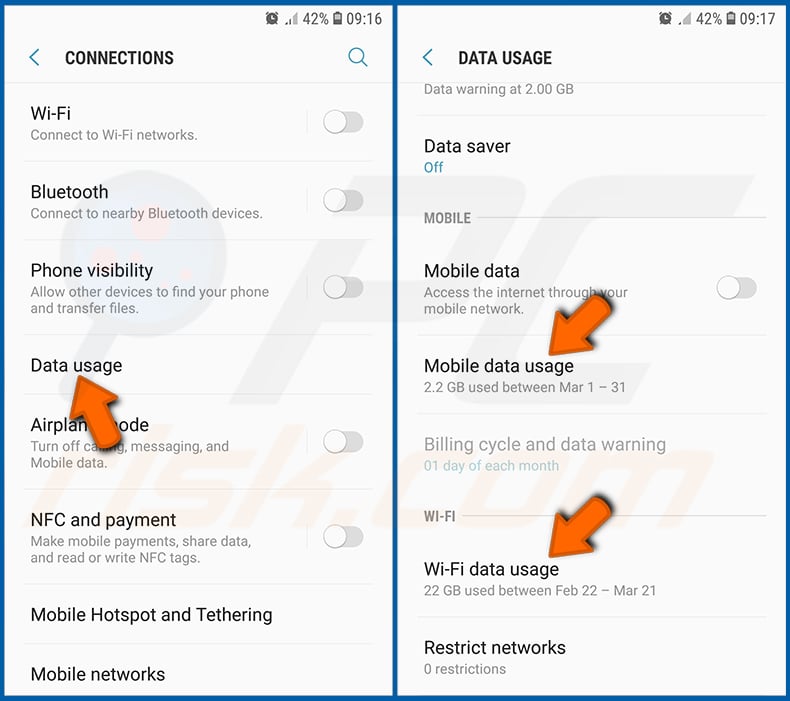
Scroll down until you see "Data usage" and select this option. As with battery, legitimate/genuine applications are designed to minimize data usage as much as possible. This means that large data usage may indicate presence of a malicious application.
Note that some malicious applications might be designed to operate when the device is connected to wireless network only. For this reason, you should check both Mobile and Wi-Fi data usage.
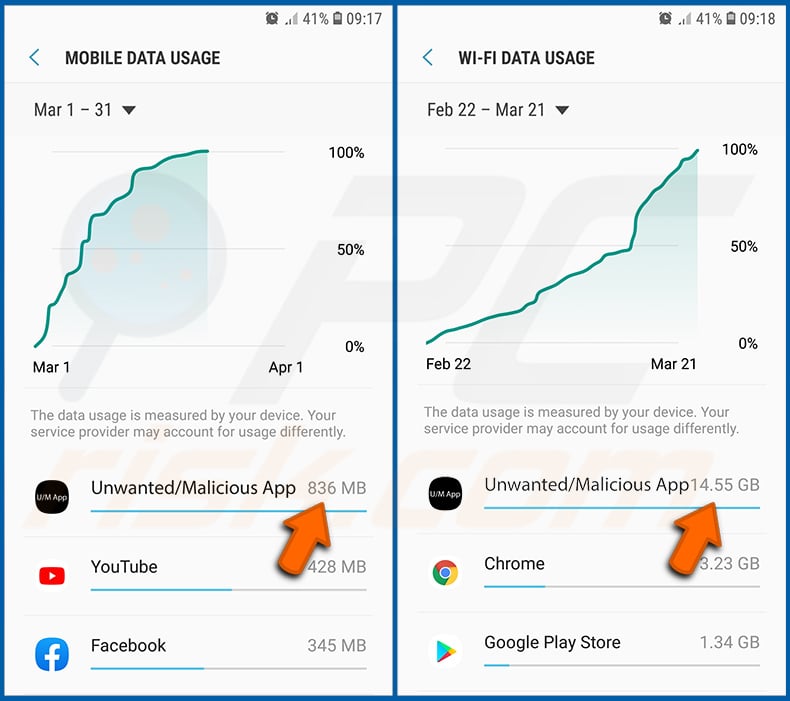
If you find an application that uses a lot of data even though you never use it, then we strongly advise you to uninstall it as soon as possible.
Install the latest software updates:
Keeping the software up-to-date is a good practice when it comes to device safety. The device manufacturers are continually releasing various security patches and Android updates in order to fix errors and bugs that can be abused by cyber criminals.
An outdated system is much more vulnerable, which is why you should always be sure that your device software is up to date.
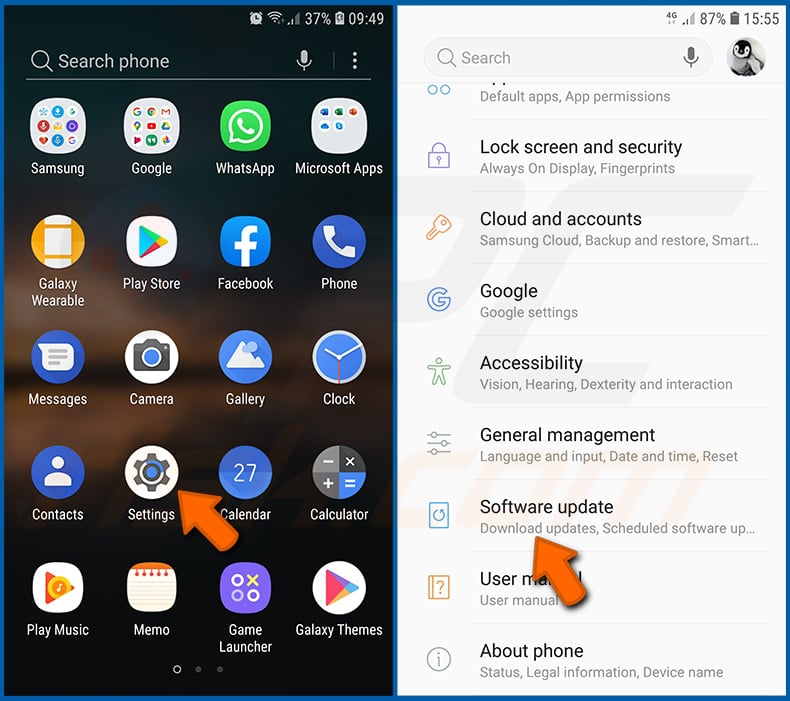
Go to "Settings", scroll down until you see "Software update" and tap it.
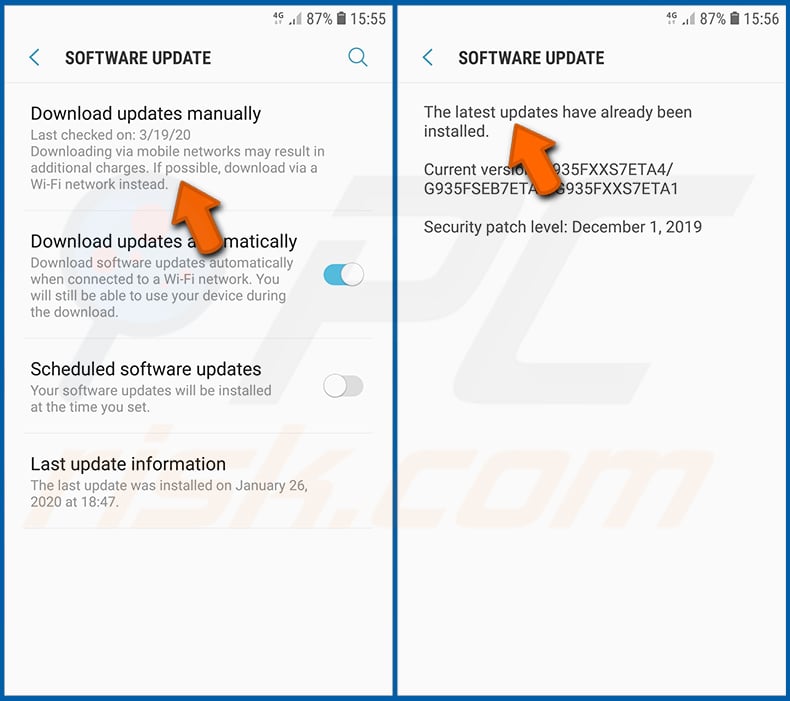
Tap "Download updates manually" and check if there are any updates available. If so, install them immediately. We also recommend to enable the "Download updates automatically" option - it will enable the system to notify you once an update is released and/or install it automatically.
Reset the system to its default state:
Performing a "Factory Reset" is a good way to remove all unwanted applications, restore system settings to default and clean the device in general, however, bear in mind that all data within the device will be deleted, including photos, video/audio files, phone numbers (stored within the device, not the SIM card), SMS messages, and so on. I.e., the device will be restored to its factory state.
You can also restore the basic system settings and/or simply network settings.
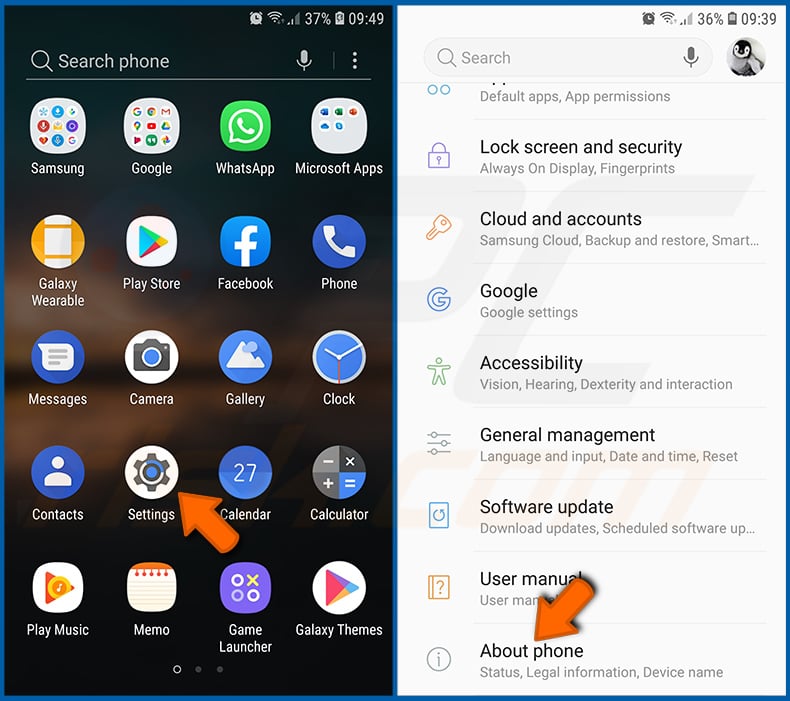
Go to "Settings", scroll down until you see "About phone" and tap it.
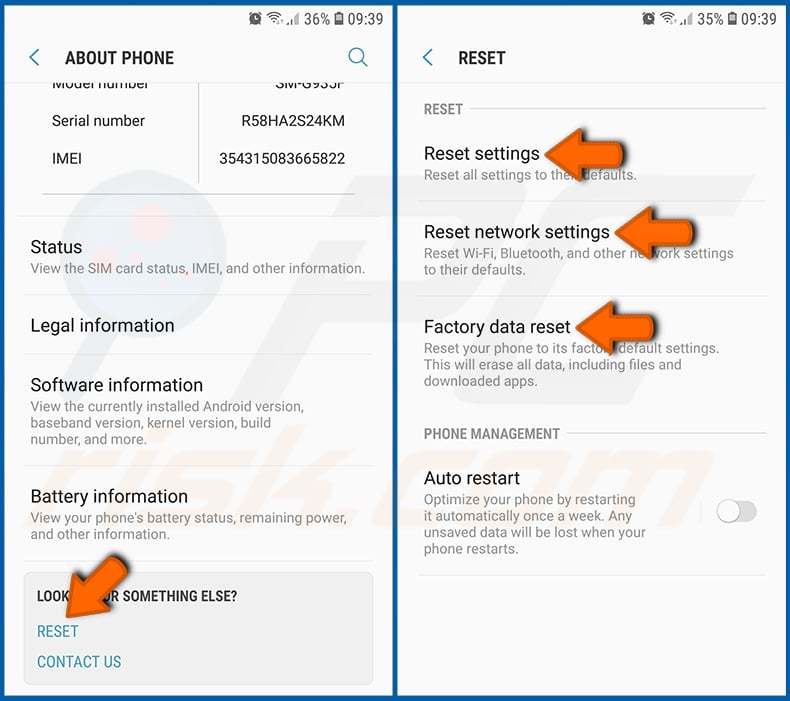
Scroll down until you see "Reset" and tap it. Now choose the action you want to perform:
"Reset settings" - restore all system settings to default;
"Reset network settings" - restore all network-related settings to default;
"Factory data reset" - reset the entire system and completely delete all stored data;
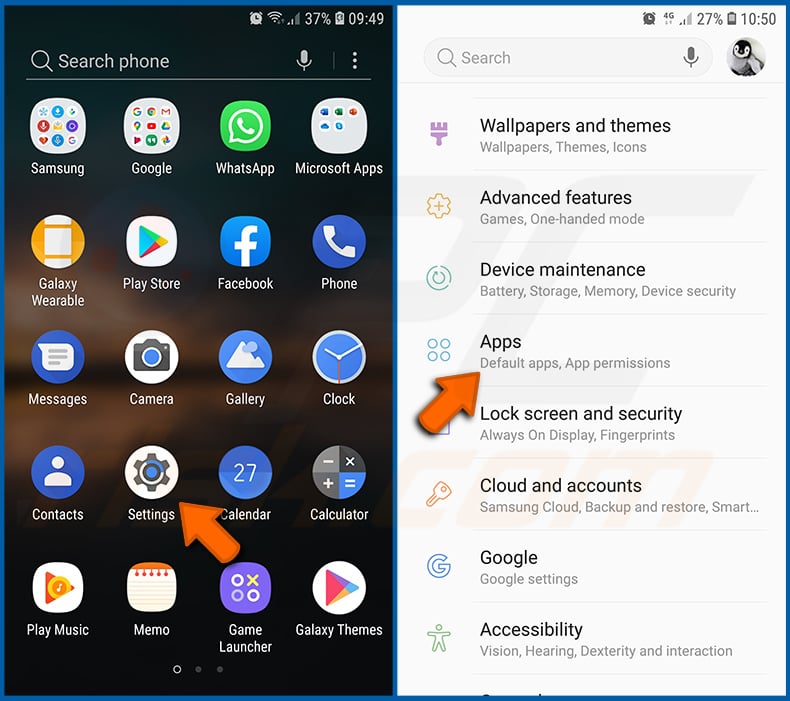
Disable applications that have administrator privileges:
If a malicious application gets administrator-level privileges it can seriously damage the system. To keep the device as safe as possible you should always check which apps have such privileges and disable the ones that should not.
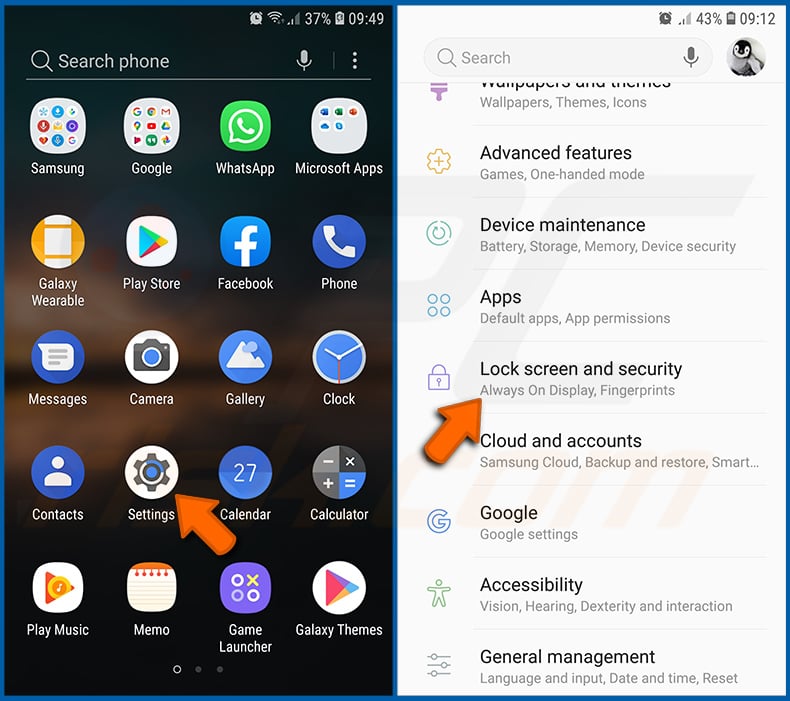
Go to "Settings", scroll down until you see "Lock screen and security" and tap it.
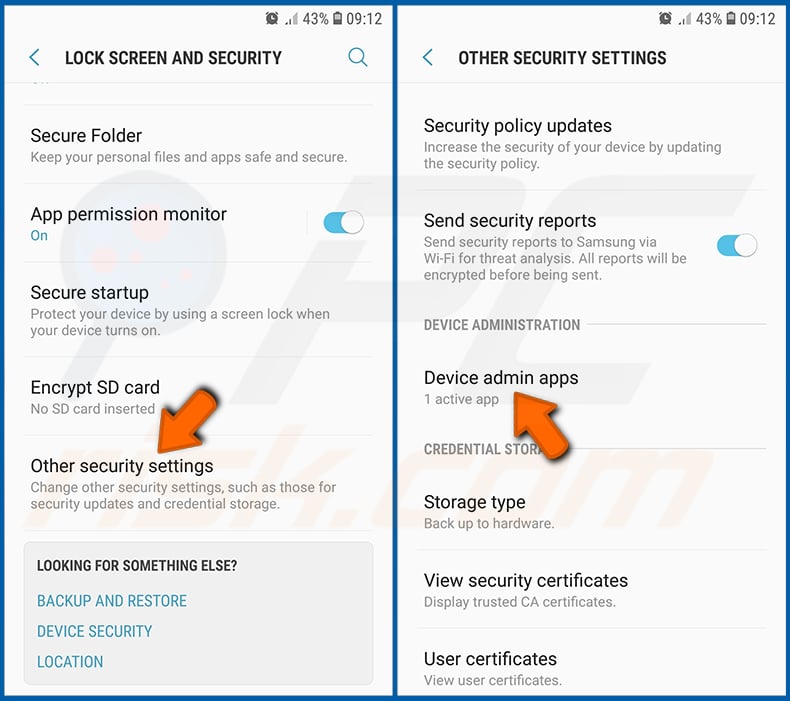
Scroll down until you see "Other security settings", tap it and then tap "Device admin apps".
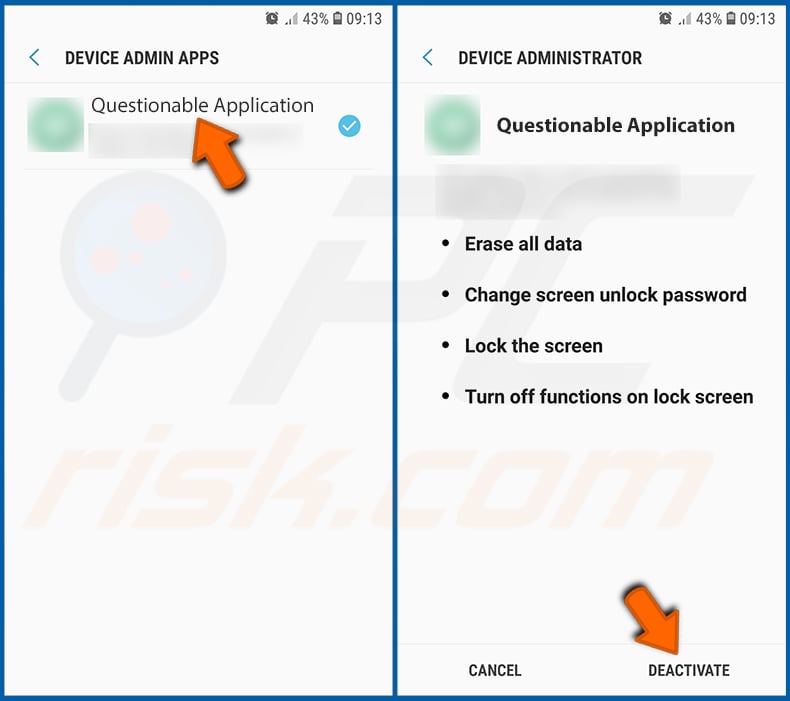
Identify applications that should not have administrator privileges, tap them and then tap "DEACTIVATE".
Frequently Asked Questions (FAQ)
What are the biggest issues that malware can cause?
Malware can cause different problems. The most common ones are data and monetary loss, hijacked online accounts, identity theft, ansd additional infections.
What is the purpose of BlackRock malware?
BlackRock can perform overlay attacks, send SMS (to specified numbers or the numbers on the infected device), retrieve text displayed on the infected device's screen (including text in notifications), run apps, and collect information about the device. Overlay attacks are used mostly to steal usernames, passwords, credit card details, and other sensitive information.
How did BlackRock malware infiltrate my device?
This malware infects devices via trojanized applications (e.g., DynamiCare and Clubhouse) downloaded from deceptive web pages. There is a high chance that BlackRock is distributed via various apps mimicking well-known legitimate apps.
Will Combo Cleaner protect me from malware?
Combo Cleaner includes an antivirus scanner that detects almost all known malware. It is common for high-end malware to be designed to hide deep in the system. Therefore, running a full system scan is a must to remove malware of this kind.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion