Do not trust sites claiming Pirated Windows Software detected in this Computer
Phishing/ScamAlso Known As: Pirated Windows Software detected in this Computer tech support scam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "Pirated Windows Software detected in this Computer"?
"Pirated Windows Software detected in this Computer" is a tech support scam that our researchers discovered while inspecting untrustworthy websites.
Technical support scams aim to trick users into calling fake helplines and allowing cyber criminals remote access to their devices - by claiming that their systems are infected or at risk. It must be emphasized that no website can detect threats/issues present on a visitor's computer; hence, any that make such claims are scams.
Furthermore, tech scams often include the names/graphics of real products or companies to create the impression of legitimacy; "Pirated Windows Software detected in this Computer" is not an exception. It is disguised as an alert from Windows/Microsoft - however, it is in no way associated with the Microsoft Corporation or their products.
"Pirated Windows Software detected in this Computer" scam overview
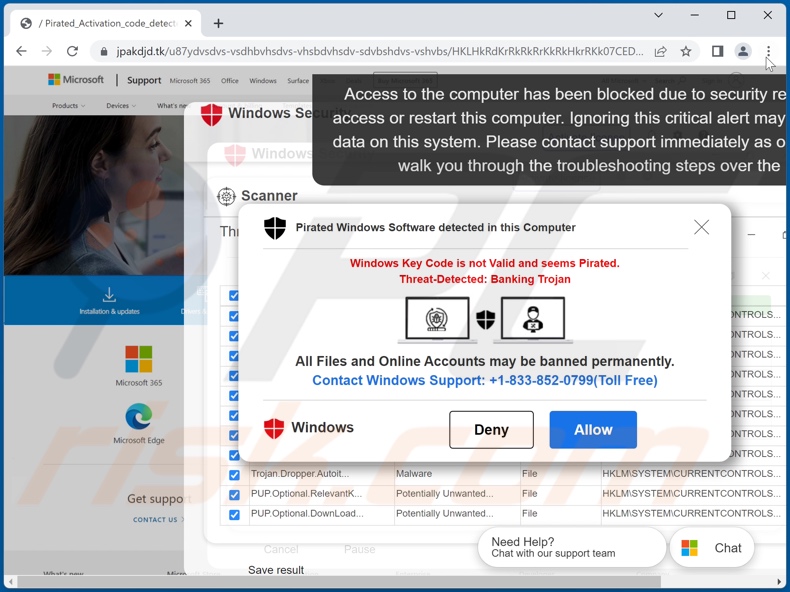
When we accessed a site running the "Pirated Windows Software detected in this Computer", we were presented with multiple pop-up windows. The background page mimics the style of Microsoft's official website's older versions. Atop it, the scam displayed a fake Windows anti-virus interface and ran a system scan (note, no website can perform system scans).
Several pop-ups were shown once the fake scan was completed. The topmost window stated that a pirated copy of Windows software was detected on the visitor's computer. Supposedly, the Windows activation key appeared invalid. Additionally, a banking trojan was found in the system. The scam urged to contact "Windows Support" in order to resolve the issues and prevent the user's files and accounts from being permanently banned.
Technical support scams aim to lure victims into calling the provided telephone number. The scammers (under the guise of "expert technicians", "customer support", etc.) instruct on how to set up remote access. What the cyber criminals do after they connect to the computer (typically via the use of legitimate remote access software) can vary.
Scammers often distract victims with bogus technobabble while performing various dubious/malicious actions on their devices. The criminals can uninstall genuine security software, install fake anti-viruses (that require purchase), download sensitive content, and even infect the system with malware.
RATs (Remote Access Trojans) are often used by tech support scammers, as this malware enables stealthy access to machines that can be potentially indefinite. However, various trojans, ransomware, cryptocurrency miners, or other malware can be used as well.
Cyber criminals also seek to acquire vulnerable information (e.g., personally identifiable details, bank account log-in credentials, credit card numbers, etc.). Users can be deceived into telling it to the scammers, typing it out (while it supposedly cannot be seen), entering it into phishing websites/files, etc.
Furthermore, the "services" of these "technicians" are usually exorbitantly priced. Difficult or impossible to trace methods are used to transfer the money, e.g., cryptocurrencies, gift cards, pre-paid vouchers, cash hidden in packages and mailed, etc. What is more, successfully scammed victims are commonly targeted repeatedly.
To summarize, by trusting scams like "Pirated Windows Software detected in this Computer" - users can experience system infections, serious privacy issues, significant financial losses, and even identity theft.
If you cannot close a deceptive website, use the Windows Task Manager to end the browser's process. Note that restoring the previous browsing session will reopen the scam page - hence, the issue will repeat itself.
And if you have allowed scammers to access your computer, immediately disconnect it from the Internet. Afterwards, uninstall the remote access software (e.g., TeamViewer, AnyDesk, etc.) the criminals used. Lastly, scan the system with a reputable anti-virus and remove all the threats detected without delay.
| Name | Pirated Windows Software detected in this Computer tech support scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud, Technical Support Scam, Tech Support Scam |
| Fake Claim | Windows activation key is invalid, pirated software suspected, trojan viruses detected, etc. |
| Disguise | Windows/Microsoft |
| Tech Support Scammer Phone Number | +1-833-852-0799, +1-877-422-9195, +1-855-743-1480, +1-808-999-9252, +1-855-796-2129, +1-833-504-2218, +1-855-332-2244, +1-855-796-2131, +1-855-677-8109, +1-855-677-8112, +1-866-822-9630, +1-833-724-0571, +1-866-499-9926, +1-844-422-4769, +1-866-801-8223, +1-888-205-3755, +1-866-522-3385, +1-(838)-300-0795, +1-844-422-4551, +1-866-662-2822, +1-866-628-5227 |
| Related Domains | jpakdjd[.]tk |
| Detection Names (jpakdjd[.]tk) | ESET (Malware), Forcepoint ThreatSeeker (Suspicious), Full List Of Detections (VirusTotal) |
| Serving IP Address (jpakdjd[.]tk) | 164.92.107.131 |
| Symptoms | Fake error messages, fake system warnings, pop-up errors, hoax computer scan. |
| Distribution methods | Compromised websites, rogue online pop-up ads, potentially unwanted applications. |
| Damage | Loss of sensitive private information, monetary loss, identity theft, possible malware infections. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Technical support scam examples
We have analyzed countless tech support scams; "DRIDEX..Malware detected - Error Code: DXRW2:#19X80XD", "Cortana - It Seems Your PC Is Locked Out", "MICROSOFT WINDOWS With Pre-installed Mcafee", and "Access to this PC has been blocked for due to illegal activities" are just some of our latest finds.
The Internet is rife with misleading, deceptive, and malicious content. Scams employ various models and disguises to gain and subsequently abuse victims' trust. Therefore, we strongly advise being careful when browsing.
How did I open a scam website?
Deceptive websites are primarily accessed via redirects caused by pages using rogue advertising networks, mistyped URLs, spam browser notifications, intrusive ads, or installed adware.
How to avoid visiting scam websites?
We advise against using sites that offer pirated programs/media or other dubious services (e.g., Torrenting, illegal streaming or downloading, etc.) - since these websites are usually monetized through rogue advertising networks. Always be careful when entering website addresses (URLs).
To avoid receiving undesirable browse notifications, do not permit questionable sites to deliver them (i.e., do not click "Allow", "Allow Notifications", etc.). Instead, ignore or deny notification delivery (i.e., click "Block", "Block Notifications", etc.).
It is crucial to download only from official and trustworthy sources. Additionally, when installing - read terms, study possible options, use the "Custom/Advanced" settings, and opt-out of all extra apps, tools, features, etc. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate all threats.
Text presented in "Pirated Windows Software detected in this Computer" scam pop-up:
Pirated Windows Software detected in this Computer
Windows Key Code is not Valid and seems Pirated.
Threat-Detected: Banking Trojan
All Files and Online Accounts may be banned permanently.
Contact Windows Support: +1-833-852-0799(TollFree)
Windows [Deny] [Allow]
The appearance of "Pirated Windows Software detected in this Computer" pop-up scam (GIF):
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Pirated Windows Software detected in this Computer tech support scam?
- How to identify a pop-up scam?
- How do pop-up scams work?
- How to remove fake pop-ups?
- How to prevent fake pop-ups?
- What to do if you fell for a pop-up scam?
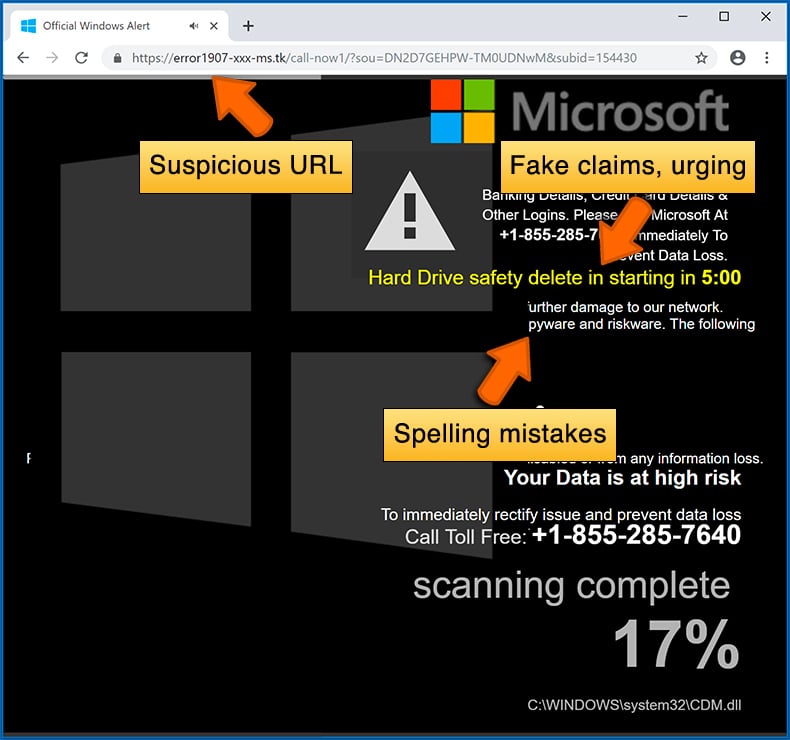
How to identify a pop-up scam?
Pop-up windows with various fake messages are a common type of lures cybercriminals use. They collect sensitive personal data, trick Internet users into calling fake tech support numbers, subscribe to useless online services, invest in shady cryptocurrency schemes, etc.
While in the majority of cases these pop-ups don't infect users' devices with malware, they can cause direct monetary loss or could result in identity theft.
Cybercriminals strive to create their rogue pop-up windows to look trustworthy, however, scams typically have the following characteristics:
- Spelling mistakes and non-professional images - Closely inspect the information displayed in a pop-up. Spelling mistakes and unprofessional images could be a sign of a scam.
- Sense of urgency - Countdown timer with a couple of minutes on it, asking you to enter your personal information or subscribe to some online service.
- Statements that you won something - If you haven't participated in a lottery, online competition, etc., and you see a pop-up window stating that you won.
- Computer or mobile device scan - A pop-up window that scans your device and informs of detected issues - is undoubtedly a scam; webpages cannot perform such actions.
- Exclusivity - Pop-up windows stating that only you are given secret access to a financial scheme that can quickly make you rich.
Example of a pop-up scam:
How do pop-up scams work?
Cybercriminals and deceptive marketers usually use various advertising networks, search engine poisoning techniques, and shady websites to generate traffic to their pop-ups. Users land on their online lures after clicking on fake download buttons, using a torrent website, or simply clicking on an Internet search engine result.
Based on users' location and device information, they are presented with a scam pop-up. Lures presented in such pop-ups range from get-rich-quick schemes to fake virus scans.
How to remove fake pop-ups?
In most cases, pop-up scams do not infect users' devices with malware. If you encountered a scam pop-up, simply closing it should be enough. In some cases scam, pop-ups may be hard to close; in such cases - close your Internet browser and restart it.
In extremely rare cases, you might need to reset your Internet browser. For this, use our instructions explaining how to reset Internet browser settings.
How to prevent fake pop-ups?
To prevent seeing pop-up scams, you should visit only reputable websites. Torrent, Crack, free online movie streaming, YouTube video download, and other websites of similar reputation commonly redirect Internet users to pop-up scams.
To minimize the risk of encountering pop-up scams, you should keep your Internet browsers up-to-date and use reputable anti-malware application. For this purpose, we recommend Combo Cleaner Antivirus for Windows.
What to do if you fell for a pop-up scam?
This depends on the type of scam that you fell for. Most commonly, pop-up scams try to trick users into sending money, giving away personal information, or giving access to one's device.
- If you sent money to scammers: You should contact your financial institution and explain that you were scammed. If informed promptly, there's a chance to get your money back.
- If you gave away your personal information: You should change your passwords and enable two-factor authentication in all online services that you use. Visit Federal Trade Commission to report identity theft and get personalized recovery steps.
- If you let scammers connect to your device: You should scan your computer with reputable anti-malware (we recommend Combo Cleaner Antivirus for Windows) - cyber criminals could have planted trojans, keyloggers, and other malware, don't use your computer until removing possible threats.
- Help other Internet users: report Internet scams to Federal Trade Commission.
Frequently Asked Questions (FAQ)
What is a pop-up scam?
Pop-up scams are deceptive messages aiming to trick users into performing specific actions. For example, victims can be deceived into calling fake support lines, allowing scammers remote access to their devices, disclosing private information, downloading/installing and/or purchasing software, making monetary transactions, and so on.
What is the purpose of a pop-up scam?
Cyber criminals use pop-up scams to generate revenue, e.g., by obtaining funds through deception, abusing or selling private data, promoting software, proliferating malware, etc.
Why do I encounter fake pop-ups?
Pop-up scams are run on rogue webpages. Users typically enter them through redirects caused by sites that use rogue advertising networks, mistyped URLs, spam browser notifications, intrusive advertisements, or installed adware.
I cannot exit a scam page, how do I close it?
Use the Windows Task Manager to end the browser's process. When opening the browser again - do not restore the previous browsing session since that will reopen the scam page.
I have allowed cyber criminals to remotely access my computer, what should I do?
If you've permitted cyber criminals to remotely access your computer - first, disconnect it from the Internet. Second, remove the software (e.g., AnyDesk, TeamViewer, etc.) the criminals used to access your device; this is important as the scammers may not need your permission to re-access the system. Lastly, perform a complete system scan with an anti-virus and eliminate all detected threats.
I have provided my personal information when tricked by a pop-up scam, what should I do?
If you have disclosed account credentials - immediately change the passwords of all potentially disclosed accounts and inform their official support. And if you've provided other personal data (e.g., ID card details, passport scans, credit card numbers, etc.) - contact the corresponding authorities without delay.
Will Combo Cleaner protect me from pop-up scams and the malware they proliferate?
Combo Cleaner can scan visited sites and detect deceptive and malicious ones. Furthermore, it can block access to such webpages. Combo Cleaner is also capable of scanning computers and eliminating most of the known malware infections. It is noteworthy that performing a full system scan is essential, as sophisticated malicious software usually hides deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion