How to avoid falling for scams like "Investment In Your Country" email scam
Phishing/ScamAlso Known As: Investment In Your Country phishing campaign
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "Investment In Your Country"?
We have examined the email and found that it is a fraudulent attempt designed to deceive recipients into revealing their sensitive information and (or) extorting money from them. The email contains elements of deception, such as false claims or requests, with the ultimate goal of exploiting unsuspecting individuals for financial gain.
More about the "Investment In Your Country" scam email
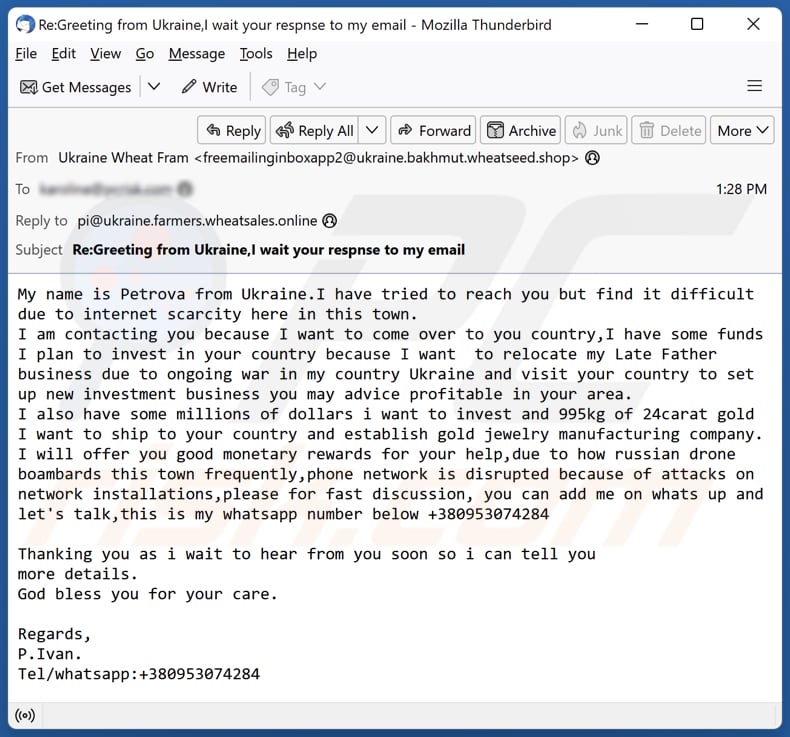
The email purports to be from someone named Petrova in Ukraine. Petrova (the scammer) claims to be experiencing difficulties in reaching the recipient due to a lack of internet access in their town. The email states that the sender intends to relocate to the recipient's country due to the ongoing conflict in Ukraine and wishes to invest in a new business there.
The letter mentions funds for investment and even a substantial amount of gold to establish a jewelry manufacturing company. The scammer offers monetary rewards in exchange for assistance. The email's urgency is emphasized by the disrupted phone network caused by attacks on network installations due to ongoing warfare.
The scammer provides a WhatsApp contact number for further communication and expresses gratitude for any help the recipient might provide. The email exhibits classic elements of a fraudulent scheme, with promises of large investments and rewards while seeking personal information or financial involvement.
| Name | Investment In Your Country Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Recipients will receive money in exchange for assistance |
| Disguise | Letter from a person named Petrova |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similar scam emails in general
Fraudulent emails, like the one described, often share common characteristics that serve as red flags. These include unsolicited and generic content, such as vague introductions or promises of substantial financial gains, an urgent or emotionally manipulative tone, and a request for personal information or financial involvement.
They frequently contain grammatical errors and inconsistencies in language use. Moreover, scammers may claim to be in a difficult or urgent situation, such as being caught in a conflict or disaster, in an attempt to elicit sympathy and quick responses. These deceptive emails typically seek to exploit recipients by extracting money, sensitive information, or both.
More examples of similar emails are "Recovered Stolen Funds And Crypto Currency", "Deceased Relative", and "Central Bank Of Nigeria". It is important to know that such emails can contain files or links used to distribute malicious software.
How do spam campaigns infect computers?
Attackers send deceptive emails that appear legitimate, often mimicking well-known organizations or individuals, and prompt users to open malicious attachments or click on malicious links. These attachments or links may contain malware, such as ransomware or keyloggers, which can compromise the recipient's system.
Cybercriminals use various types of files to trick users into infecting their computers via email, with the most common being attachments like .exe, .doc, .pdf, and .zip files.
How to avoid installation of malware?
Keep your operating system, software, and antivirus programs up to date. Exercise caution when interacting with email attachments and links, especially if they come from unknown or suspicious sources. Avoid downloading software or files from unverified websites and clicking advertisements on pages of this kind.
Do not download pirated software or tools that are supposed to activate paid software illegally. Be vigilant and stay informed about current cybersecurity threats and common tactics used by cybercriminals to better recognize and avoid potential risks.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "Investment In Your Country" email letter:
Subject: Re:Greeting from Ukraine,I wait your respnse to my email
My name is Petrova from Ukraine.I have tried to reach you but find it difficult due to internet scarcity here in this town.
I am contacting you because I want to come over to you country,I have some funds I plan to invest in your country because I want to relocate my Late Father business due to ongoing war in my country Ukraine and visit your country to set up new investment business you may advice profitable in your area.
I also have some millions of dollars i want to invest and 995kg of 24carat gold I want to ship to your country and establish gold jewelry manufacturing company.
I will offer you good monetary rewards for your help,due to how russian drone boambards this town frequently,phone network is disrupted because of attacks on network installations,please for fast discussion, you can add me on whats up and let's talk,this is my whatsapp number below +380953074284Thanking you as i wait to hear from you soon so i can tell you
more details.
God bless you for your care.Regards,
P.Ivan.
Tel/whatsapp:+380953074284
Other examples of emails from "Investment In Your Country" spam campaign:
Sample 1:
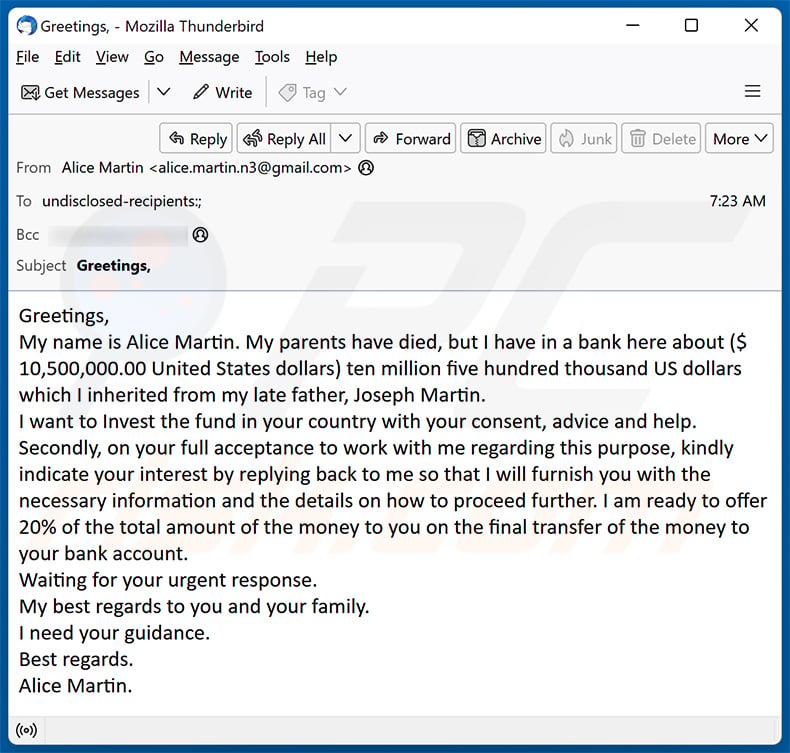
Text presented within:
Subject: Greetings,
Greetings,
My name is Alice Martin. My parents have died, but I have in a bank here about ($ 10,500,000.00 United States dollars) ten million five hundred thousand US dollars which I inherited from my late father, Joseph Martin.
I want to Invest the fund in your country with your consent, advice and help.
Secondly, on your full acceptance to work with me regarding this purpose, kindly indicate your interest by replying back to me so that I will furnish you with the necessary information and the details on how to proceed further. I am ready to offer 20% of the total amount of the money to you on the final transfer of the money to your bank account.
Waiting for your urgent response.
My best regards to you and your family.
I need your guidance.
Best regards.
Alice Martin.
Sample 2:
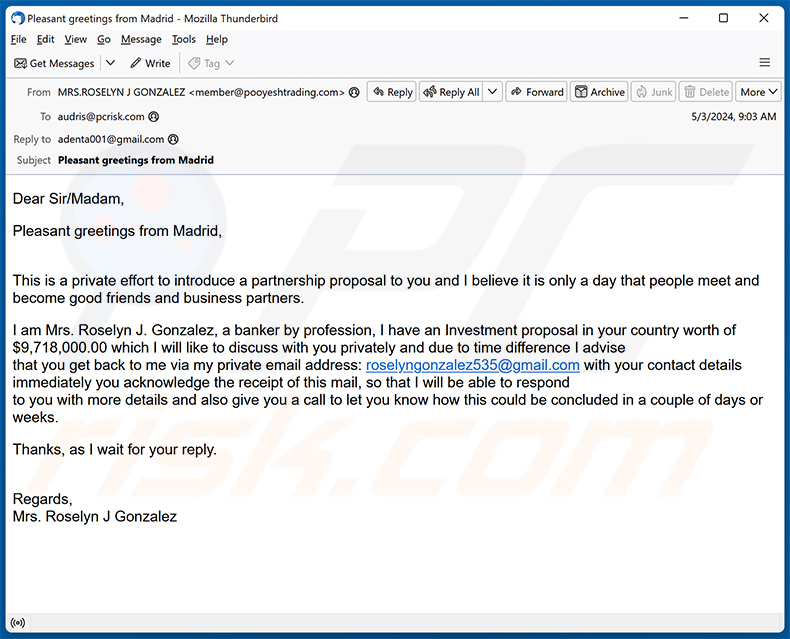
Text presented within:
Subject: Pleasant greetings from Madrid
Dear Sir/Madam,Pleasant greetings from Madrid,
This is a private effort to introduce a partnership proposal to you and I believe it is only a day that people meet and become good friends and business partners.
I am Mrs. Roselyn J. Gonzalez, a banker by profession, I have an Investment proposal in your country worth of $9,718,000.00 which I will like to discuss with you privately and due to time difference I advise
that you get back to me via my private email address: roselyngonzalez535@gmail.com with your contact details immediately you acknowledge the receipt of this mail, so that I will be able to respond
to you with more details and also give you a call to let you know how this could be concluded in a couple of days or weeks.Thanks, as I wait for your reply.
Regards,
Mrs. Roselyn J Gonzalez
Sample 3:
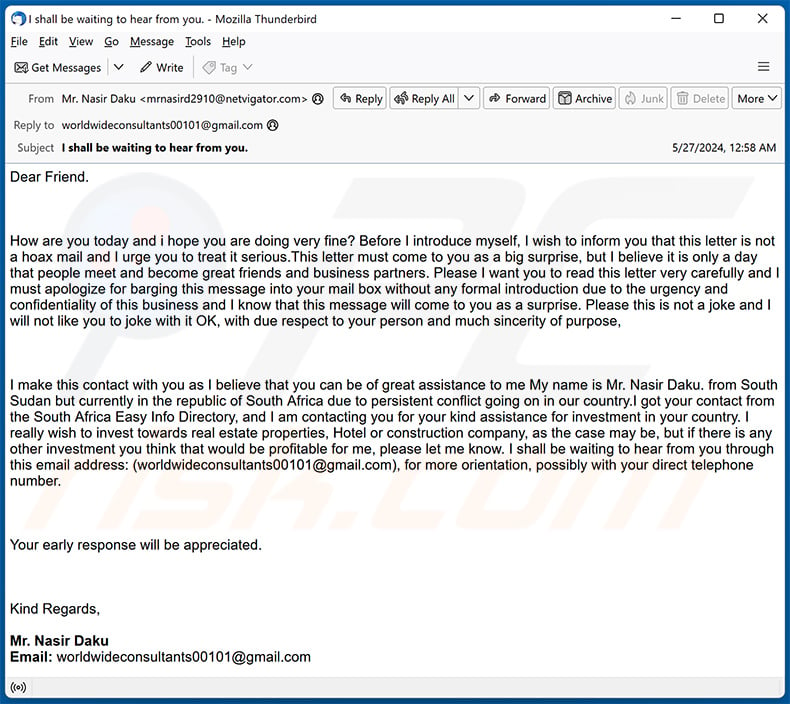
Text presented within:
Subject: I shall be waiting to hear from you.
Dear Friend.
How are you today and i hope you are doing very fine? Before I introduce myself, I wish to inform you that this letter is not a hoax mail and I urge you to treat it serious.This letter must come to you as a big surprise, but I believe it is only a day that people meet and become great friends and business partners. Please I want you to read this letter very carefully and I must apologize for barging this message into your mail box without any formal introduction due to the urgency and confidentiality of this business and I know that this message will come to you as a surprise. Please this is not a joke and I will not like you to joke with it OK, with due respect to your person and much sincerity of purpose,
I make this contact with you as I believe that you can be of great assistance to me My name is Mr. Nasir Daku. from South Sudan but currently in the republic of South Africa due to persistent conflict going on in our country.I got your contact from the South Africa Easy Info Directory, and I am contacting you for your kind assistance for investment in your country. I really wish to invest towards real estate properties, Hotel or construction company, as the case may be, but if there is any other investment you think that would be profitable for me, please let me know. I shall be waiting to hear from you through this email address: (worldwideconsultants00101@gmail.com), for more orientation, possibly with your direct telephone number.Your early response will be appreciated.
Kind Regards,
Mr. Nasir Daku
Email: worldwideconsultants00101@gmail.com
Sample 4:
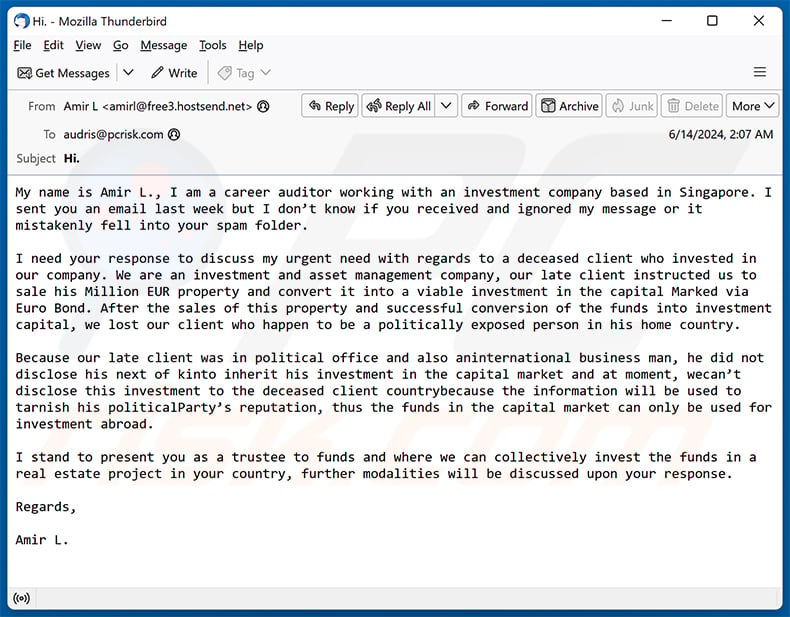
Text presented within:
Subject: Hi.
My name is Amir L., I am a career auditor working with an investment company based in Singapore. I sent you an email last week but I don’t know if you received and ignored my message or it mistakenly fell into your spam folder.
I need your response to discuss my urgent need with regards to a deceased client who invested in our company. We are an investment and asset management company, our late client instructed us to sale his Million EUR property and convert it into a viable investment in the capital Marked via Euro Bond. After the sales of this property and successful conversion of the funds into investment capital, we lost our client who happen to be a politically exposed person in his home country.
Because our late client was in political office and also aninternational business man, he did not disclose his next of kinto inherit his investment in the capital market and at moment, wecan’t disclose this investment to the deceased client countrybecause the information will be used to tarnish his politicalParty’s reputation, thus the funds in the capital market can only be used for investment abroad.
I stand to present you as a trustee to funds and where we can collectively invest the funds in a real estate project in your country, further modalities will be discussed upon your response.
Regards,
Amir L.
Sample 5:
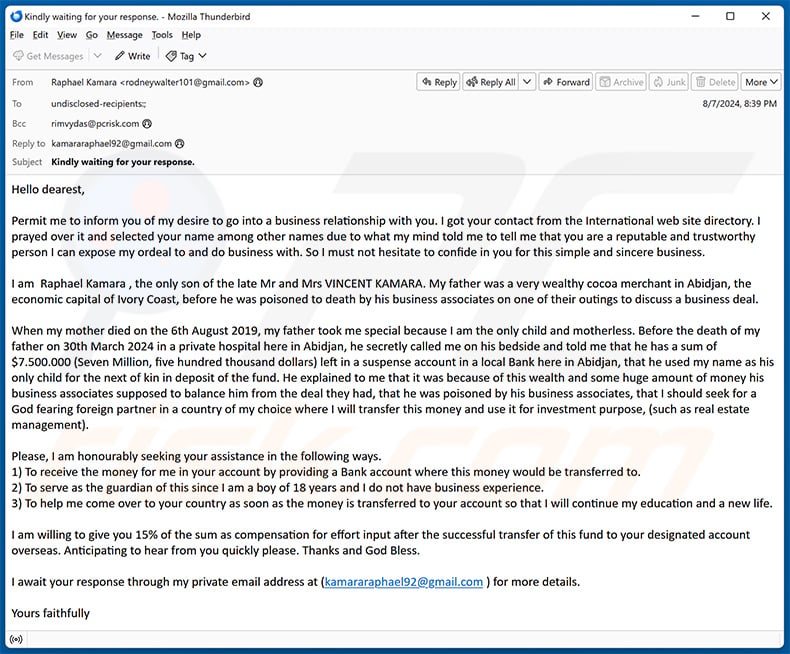
Text presented within:
Subject: Kindly waiting for your response.
Hello dearest,
Permit me to inform you of my desire to go into a business relationship with you. I got your contact from the International web site directory. I prayed over it and selected your name among other names due to what my mind told me to tell me that you are a reputable and trustworthy person I can expose my ordeal to and do business with. So I must not hesitate to confide in you for this simple and sincere business.
I am Raphael Kamara , the only son of the late Mr and Mrs VINCENT KAMARA. My father was a very wealthy cocoa merchant in Abidjan, the economic capital of Ivory Coast, before he was poisoned to death by his business associates on one of their outings to discuss a business deal.
When my mother died on the 6th August 2019, my father took me special because I am the only child and motherless. Before the death of my father on 30th March 2024 in a private hospital here in Abidjan, he secretly called me on his bedside and told me that he has a sum of $7.500.000 (Seven Million, five hundred thousand dollars) left in a suspense account in a local Bank here in Abidjan, that he used my name as his only child for the next of kin in deposit of the fund. He explained to me that it was because of this wealth and some huge amount of money his business associates supposed to balance him from the deal they had, that he was poisoned by his business associates, that I should seek for a God fearing foreign partner in a country of my choice where I will transfer this money and use it for investment purpose, (such as real estate management).
Please, I am honourably seeking your assistance in the following ways.
1) To receive the money for me in your account by providing a Bank account where this money would be transferred to.
2) To serve as the guardian of this since I am a boy of 18 years and I do not have business experience.
3) To help me come over to your country as soon as the money is transferred to your account so that I will continue my education and a new life.I am willing to give you 15% of the sum as compensation for effort input after the successful transfer of this fund to your designated account overseas. Anticipating to hear from you quickly please. Thanks and God Bless.
I await your response through my private email address at (kamararaphael92@gmail.com ) for more details.
Yours faithfully
Sample 6:
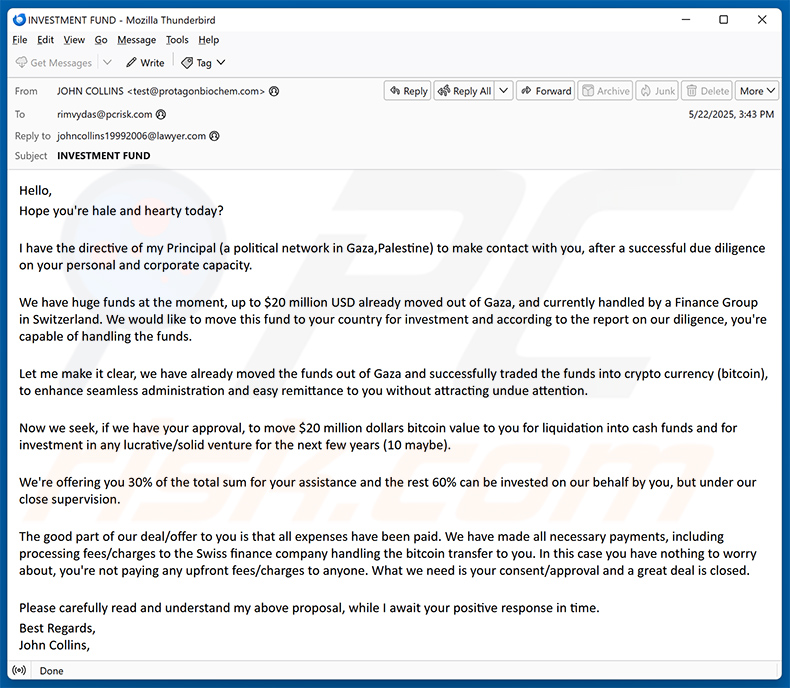
Text presented within:
Subject: INVESTMENT FUND
Hello,
Hope you're hale and hearty today?
I have the directive of my Principal (a political network in Gaza,Palestine) to make contact with you, after a successful due diligence on your personal and corporate capacity.
We have huge funds at the moment, up to $20 million USD already moved out of Gaza, and currently handled by a Finance Group in Switzerland. We would like to move this fund to your country for investment and according to the report on our diligence, you're capable of handling the funds.
Let me make it clear, we have already moved the funds out of Gaza and successfully traded the funds into crypto currency (bitcoin), to enhance seamless administration and easy remittance to you without attracting undue attention.
Now we seek, if we have your approval, to move $20 million dollars bitcoin value to you for liquidation into cash funds and for investment in any lucrative/solid venture for the next few years (10 maybe).
We're offering you 30% of the total sum for your assistance and the rest 60% can be invested on our behalf by you, but under our close supervision.
The good part of our deal/offer to you is that all expenses have been paid. We have made all necessary payments, including processing fees/charges to the Swiss finance company handling the bitcoin transfer to you. In this case you have nothing to worry about, you're not paying any upfront fees/charges to anyone. What we need is your consent/approval and a great deal is closed.
Please carefully read and understand my above proposal, while I await your positive response in time.
Best Regards,
John Collins,
Sample 7:
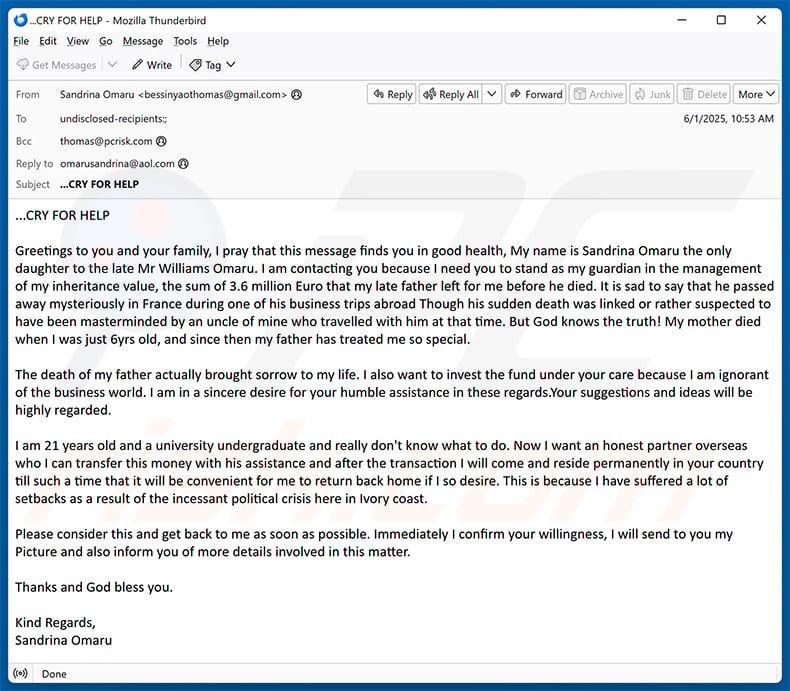
Text presented within:
...CRY FOR HELP
Greetings to you and your family, I pray that this message finds you in good health, My name is Sandrina Omaru the only daughter to the late Mr Williams Omaru. I am contacting you because I need you to stand as my guardian in the management of my inheritance value, the sum of 3.6 million Euro that my late father left for me before he died. It is sad to say that he passed away mysteriously in France during one of his business trips abroad Though his sudden death was linked or rather suspected to have been masterminded by an uncle of mine who travelled with him at that time. But God knows the truth! My mother died when I was just 6yrs old, and since then my father has treated me so special.
The death of my father actually brought sorrow to my life. I also want to invest the fund under your care because I am ignorant of the business world. I am in a sincere desire for your humble assistance in these regards.Your suggestions and ideas will be highly regarded.
I am 21 years old and a university undergraduate and really don't know what to do. Now I want an honest partner overseas who I can transfer this money with his assistance and after the transaction I will come and reside permanently in your country till such a time that it will be convenient for me to return back home if I so desire. This is because I have suffered a lot of setbacks as a result of the incessant political crisis here in Ivory coast.
Please consider this and get back to me as soon as possible. Immediately I confirm your willingness, I will send to you my Picture and also inform you of more details involved in this matter.
Thanks and God bless you.
Kind Regards,
Sandrina Omaru
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Investment In Your Country phishing campaign?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Criminals distribute identical letters to numerous recipients with the expectation that they will deceive at least one individual. These spam emails lack personalization and are mass-sent to reach a wide audience.
I have provided my personal information when tricked by this email, what should I do?
If you have shared personal information due to a deceptive email, act swiftly. Change compromised passwords, monitor accounts for suspicious activity, and report unauthorized transactions. Be cautious of further contact from the sender, and consider alerting law enforcement and running a malware scan on your computer.
I have downloaded and opened a malicious file attached to an email, is my computer infected?
For executable files, the likelihood of infection is high. However, if the file was a document like .pdf or .doc, there is a chance you may have avoided the infection, as merely opening such documents sometimes is not sufficient for malware to infect the system.
I have sent cryptocurrency to the address presented in such email, can I get my money back?
Recovering cryptocurrency sent to a fraudulent address presented in an email can be exceptionally challenging. Cryptocurrency transactions are typically irreversible, and once funds are sent to an address, they cannot be easily retrieved.
I have read the email but did not open the attachment, is my computer infected?
Merely viewing the email or its content (without opening links or attachments) does not lead to an infection.
Will Combo Cleaner remove malware infections that were present in email attachment?
Combo Cleaner possesses the capability to detect and remove the majority of malware infections. It is essential to remember that sophisticated malware often conceals itself deep within the system. Therefore, it is imperative to perform a comprehensive system scan.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion