Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Ultimate?
Ultimate is malware designed to steal information from infected macOS systems. It maintains persistence, evades detection, and securely exfiltrates stolen data to a command-and-control (C2) server controlled by cybercriminals. If a device is infected with Ultimate, the malware should be removed as soon as possible.
More about the Ultimate stealer
Before executing its main payload, the malware first collects details (hardware and system identifiers) about the device and system to create a "profile" on the infected device. It also checks for details that help it to avoid analysis environments (such as sandboxes and virtual machines) and to restrict execution based on geographic conditions.
Ultimate stealer can access saved passwords by taking the Chrome encryption key from the macOS Keychain and reading the browser's stored login database. It also tries to bypass macOS privacy protections to access sensitive data. Also, it attempts to increase its permissions and configure itself so it runs every time the system starts.
The stealer hides within the infected system by injecting itself into trusted apps so it looks normal and is harder to detect. It also sends stolen data back to the attacker in encrypted form to avoid detection. Furthermore, Ultimate can change its code and download extra components to add new features.
Lastly, the stealer can remove its own files and activity logs to cover its tracks. Generally, this malware can steal saved passwords and other sensitive data, which can lead to account takeovers, financial loss, and identity theft. The execution of additional plugins may lead to further issues.
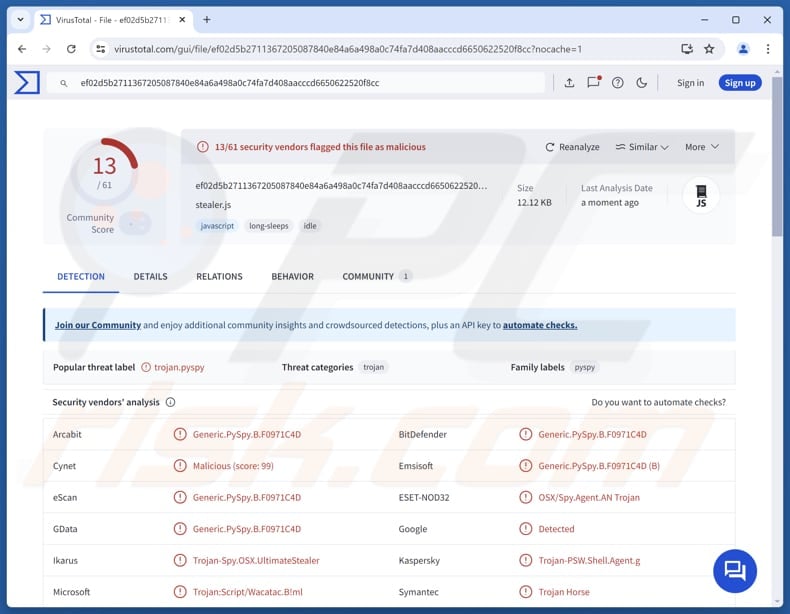
| Name | Ultimate information stealer |
| Threat Type | Information stealer |
| Detection Names | Arcabit (Generic.PySpy.B.F0971C4D), Combo Cleaner (Generic.PySpy.B.F0971C4D), ESET-NOD32 (OSX/Spy.Agent.AN Trojan), Kaspersky (Trojan-PSW.Shell.Agent.g), Symantec (Trojan Horse), Full List (VirusTotal) |
| Symptoms | Stealers are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Possible distribution methods | Infected email attachments, malicious online advertisements, social engineering, software vulnerabilities, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, financial loss, possible additional infections. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
Overall, Ultimate stealer malware is designed to quietly collect sensitive information from an infected computer. It uses multiple techniques to avoid detection and maintain long-term access to the system. Once the data is stolen, it is sent to attackers who can use it for fraud, account takeovers, or further attacks.
Some examples of information stealers are NovaStealer, DigitStealer, and FrigidStealer.
How did malware infiltrate my computer?
Malware is often distributed through a variety of infected files, including executables, compressed archives like ZIP or RAR, scripts, and documents such as PDFs or Office files. Simply opening or additionally interacting with these files can cause a system infection.
Attackers deliver malware through different channels, such as attachments and links in fraudulent emails or other messages, tech support scams, vulnerabilities in outdated or unpatched software, pirated software, unofficial activation tools, key generators, and misleading advertisements.
It can additionally spread via compromised websites, infected USB drives, peer-to-peer (P2P) sharing networks, and third-party download tools.
How to avoid malware?
Do not interact with pop-ups, ads, or links on questionable websites, and never accept notifications from unknown pages. Keep your system and applications regularly up to date so security issues are patched. Also, treat unexpected emails or messages with caution, especially if they come from unfamiliar senders, and avoid opening attachments or links that look suspicious or unrelated.
Download software from trusted sources, such as official developer websites or verified app stores, and avoid cracked programs or unauthorized activation tools. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate all threats.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
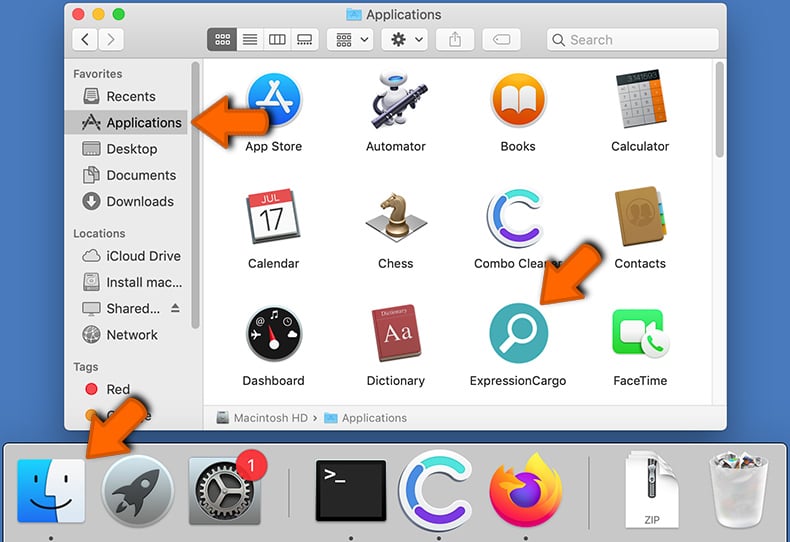
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Frequently Asked Questions (FAQ)
My computer is infected with Ultimate malware, should I format my storage device to get rid of it?
A full system format can remove Ultimate Stealer, but it will also erase all data stored on the device. Because of this, it is usually better to first attempt removal using a trusted security tool like Combo Cleaner.
What are the biggest issues that malware can cause?
Malware can damage or remove files, install other malicious programs, monitor user activity, and perform other harmful actions. It can result in serious consequences, including financial losses, stolen personal data or identities, unauthorized access to accounts, and permanent data loss.
What is the purpose of Ultimate stealer?
The purpose of Ultimate Stealer is to steal sensitive data, especially saved passwords, from a Mac and send it to attackers. It works quietly to avoid detection while collecting and exfiltrating information. Also, it can additional other plugins.
How did a malware infiltrate my computer?
Malware is often spread through harmful files such as executables, compressed archives, scripts, and documents that can infect a system once they are executed. Attackers use emails with malicious links or attachments, fake tech support schemes, compromised websites, software vulnerabilities, infected USB devices, peer-to-peer networks, unsafe third-party download sites, pirated software, deceptive online advertisements, and similar methods to deliver malware.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and remove most threats. However, more advanced threats can be well hidden in the system, so it is important to run a full scan to ensure elimination.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion