CALVO Ransomware
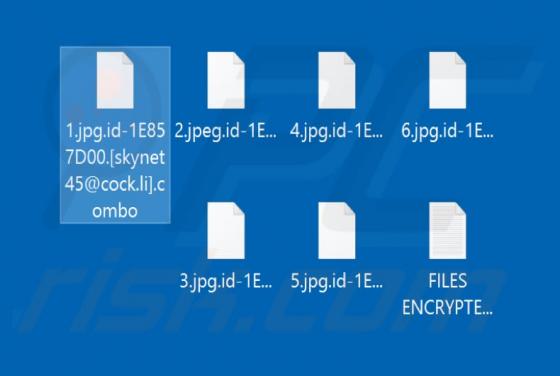
Ransomware is a type of malicious software that encrypts files (and renames them) and generates a ransom note. Typically, a ransom note generated by ransomware informs victims that they cannot access their files without the right decryption tool and provides further instructions. CALVO encrypts f