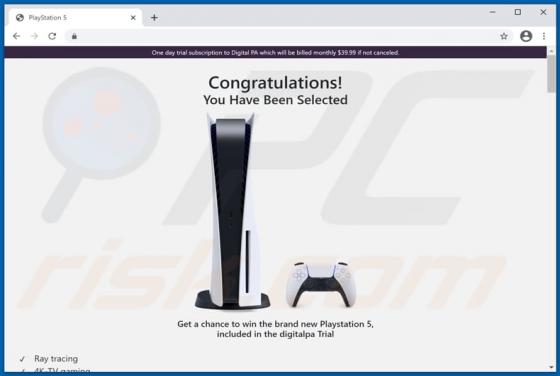
Chance To Win The Brand New Playstation 5 POP-UP Scam
It is common that phishing pages look like other pages (e.g., official pages owned by legitimate companies). Most of the times, scammers behind these pages use one or another technique to trick unsuspecting users into providing sensitive information. Usually, they attempt to extract information l