LegionLocker Ransomware
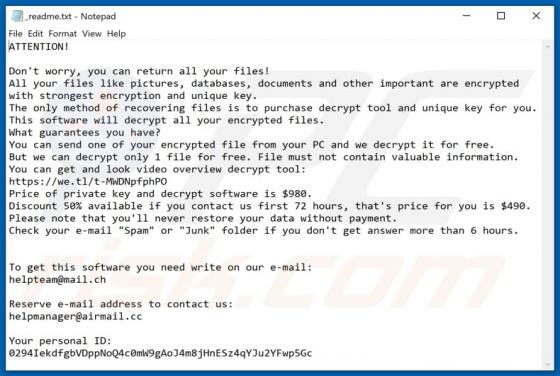
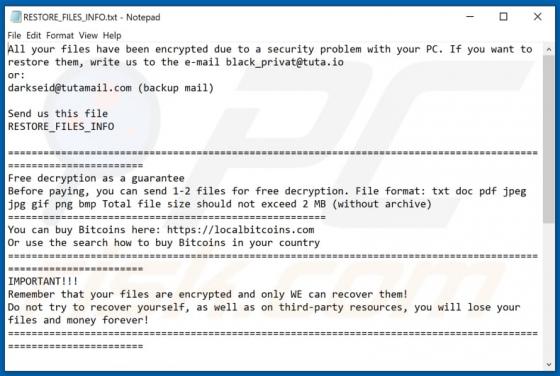
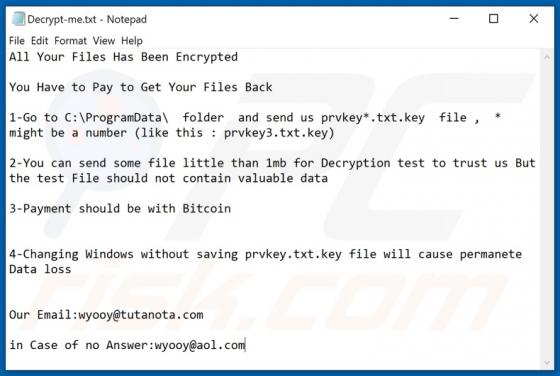
Ransomware is designed to encrypt files and demands a ransom payment. Ransomware victims cannot use encrypted files until they are decrypted with a specific decryption tool. Quite often, malware of this type not only encrypts but also renames files - it appends its extension to the filenames of a