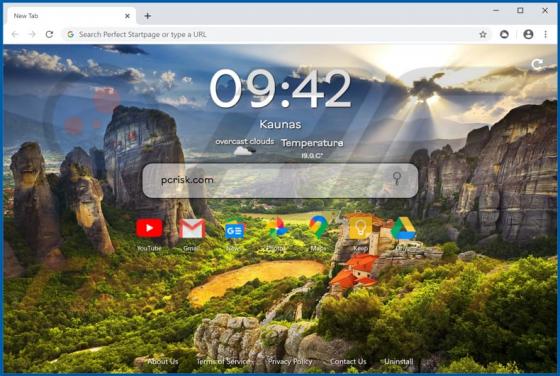
Perfect Startpage Browser Hijacker
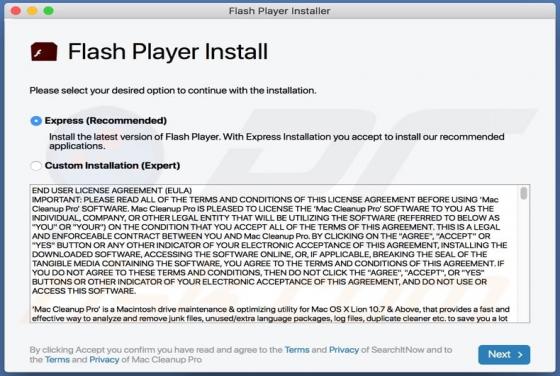
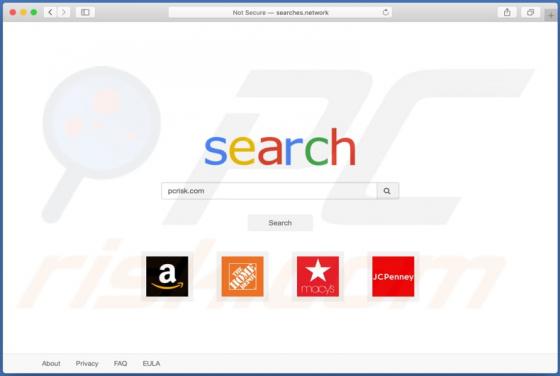
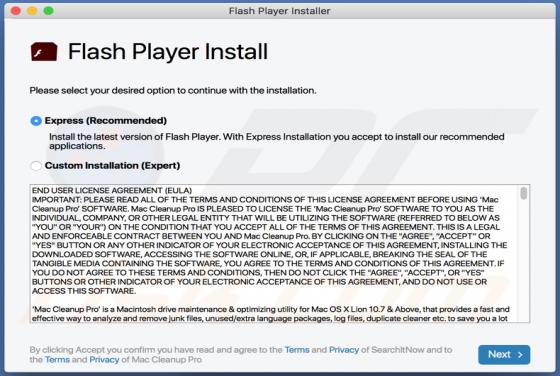
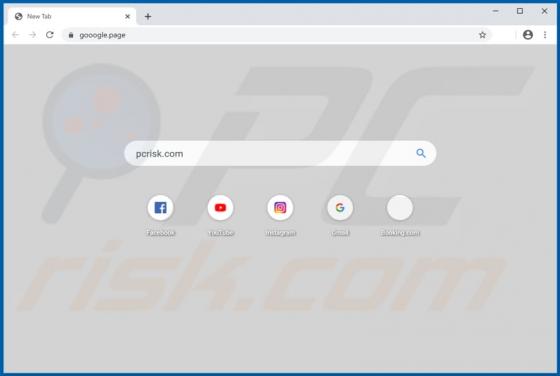
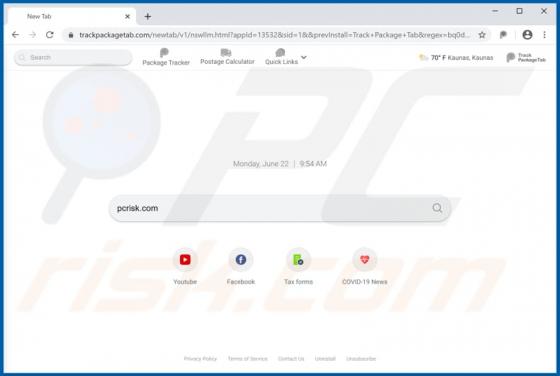
Perfect Startpage browser hijacker promotes perfectstartpage.com, a fake search engine, by modifying specific browser settings. These apps also collect information relating to users' browsing habits. People often download and install browser hijackers inadvertently and, therefore, they are categor