Repl Ransomware
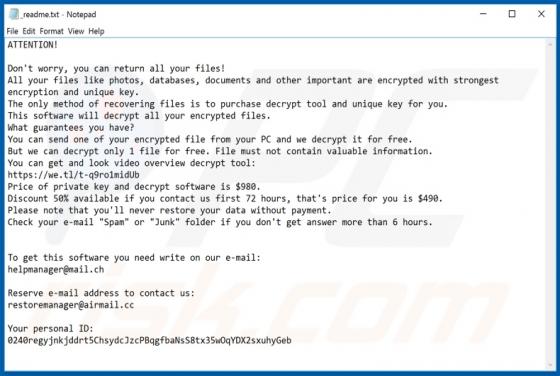
Repl is malicious software belonging to the Djvu ransomware family. It is designed to encrypt data and demand payment for decryption tools/software. During the encryption process, the filenames of affected files are appended with the ".repl" extension. For example, a file originally named somethin