Wowsearch Browser Hijacker
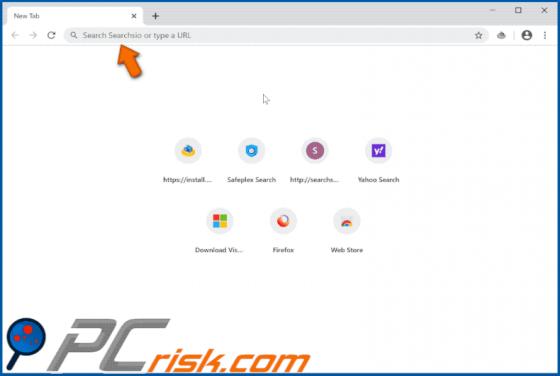
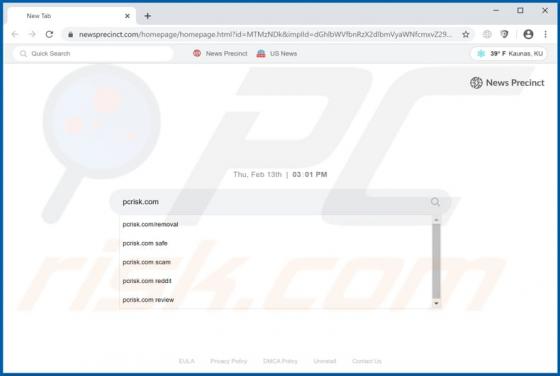
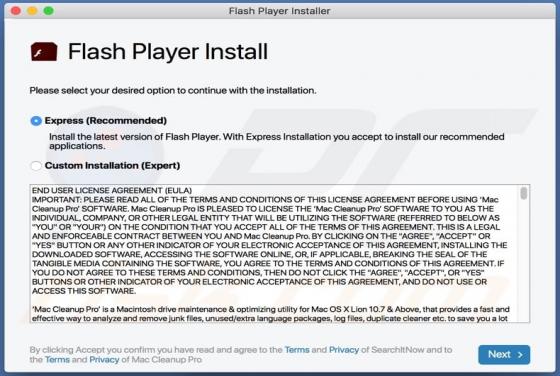
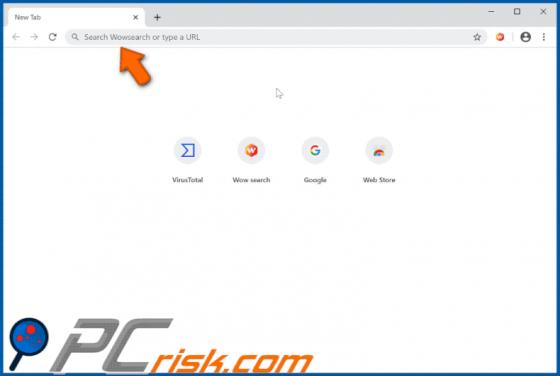
Wowsearch hijacks browsers by changing certain browser settings to search.wowsearch.net (the address of a fake search engine). Commonly, apps of this type track and record information relating to users' browsing habits, and other details. People often download and install browser hijackers inadve