Legion Loader Drops a Hornet’s Nest of Malware
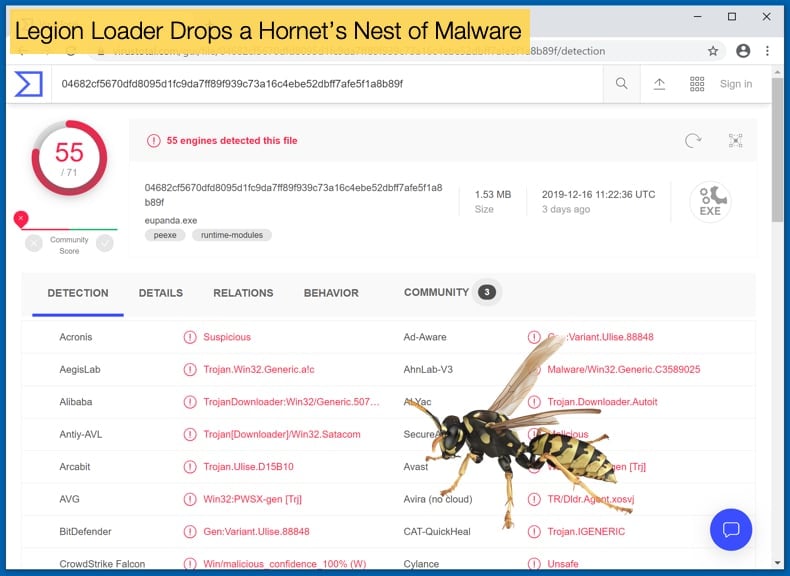
What could be worse than being infected by one piece of malware? The answer is painfully obvious, in that more than one infection is worse. What started as a lame joke may be a reality for organizations infected with Legion Loader. In a recent campaign discovered by researchers, a threat actor is attempting to infect as many machines as possible with a loader capable of dropping multiple malware strains.
Discovered by researchers at Deep Instinct who subsequently published their findings in an article, details how what various strains are dropped during the attack. Due to the number of malware strains dropped the researchers have dubbed this campaign “Hornet’s Nest.” It is not yet known how victims are infected with the initial Legion Loader but the attack is being offered as a cybercrime-as-a-service operation. Despite not knowing the initial attack and infection vectors, Legion Loader is written in C++ and still appears to be under development. Clues in the code also suggest that the loader is developed by a Russian speaker and based on the current attack pattern the operators are targeting organizations in the US and Europe.
Malware loaders, also called droppers, are generally defined as a type of trojan that is used to install or drop other varieties of malware. A famous example of such a trojan is SmokeLoader which was seen at the start of the year been used to further distribute GandCrab and Vidar. Returning to Legion Loader, once executed the malware will execute PowerShell commands that enable it to begin retrieving its malicious payloads. The loader will then deliver three different forms of trojan malware, all of which are available on underground forums. The first been Vidar which is at its core an information stealer mainly geared to steal personal information. The second trojan dropped is Predator the Thief also an information stealer but is also capable of capturing images via the infected machine’s webcam. Lastly, the third trojan dropped is Racoon Stealer which is capable of stealing passwords and cryptocurrency wallet credentials. Racoon Stealer is also widely regarded as easy to use and is incredibly customizable adding to its appeal despite the relatively new on the malware circuit.
By dropping these three different trojans enables the attacker to steal entire swathes of information. From banking information which could be used to carry out fraudulent transactions via a victim’s account to personal information. There is often a misconception regarding personal information been stolen as it is harmless. The truth of the matter is the polar opposite when personal information is combined with financial information attackers are capable of committing identity theft. This, in turn, can be used to take out loans which can be incredibly hard to reverse and prove that the victim did not apply for the loan in the first place. Personal information can also be used to blackmail and extort victims. Lastly, the information can also prove to be very valuable on the black market and simply sold off so other cybercriminals can do some of what was listed above. Further, Legion Loader also contains an RDP-based backdoor providing the attacker with entry into the compromised machine. This could allow those using Legion Loader to deploy additional attacks in the future.
Not Just Trojans
Given that Legion Loader drops a number of trojans one would be forgiven thinking that the sole aim of its operators is to steal as much information as possible. Information stealing trojans do not have a quick turnaround in terms of profit. Legion Loader has a few more tricks in order to generate funds faster. The first being, a PowerShell-based cryptocurrency stealer that allows the attacker to raid the victim's Bitcoin wallet and take whatever cryptocurrency is kept in it. Typically such malware works by exploiting a weakness in the wallet's key storage system. The malware will scan the system for “wallet.dat” or other well-known wallet software key storage locations, either by checking known file locations or by searching all hard drives for matching filenames. Typically, the file is uploaded to a remote FTP, HTTP, or SMTP server where the thief can extract the keys and steal the coins by signing a transaction, transferring the coins to the thief's Bitcoin/altcoin address. In order to get around strong passphrase protection, hackers will use such malware along with keyloggers or clipboard monitors.
That is not the only method Legion Loader employs to start generating profit from the start. The last payload delivered is a crypto miner which uses the machines CPU resources to mine cryptocurrency and is designed to siphon off a small amount of CPU power to mine coins over time. Hacker’s do not always get the siphoning off of CPU resources correct and often severe knocks to performance can be detected, and is often a tell-tale sign of infection. Researchers concluded that,
“Legion Loader is, as mentioned above, very aptly named; and is a classic case-in-point of how even a relatively low-sophistication malware can become a security nightmare for an organization, employing more advanced file-less techniques and delivering a myriad of follow-up malware ranging for info-stealers and credential harvesters to crypto-miners and backdoors.”
While the potential for damage to be caused to organizations is there Legion Loader can be defended against. If organizations adopt basic security measures and ensure all software is correctly kept up to date infections of Legion Loader and subsequent malware drops can be prevented. Further organizations are advised to apply patches upon release and secure internet-facing ports to further increase their security posture.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion