Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Ave Maria?
Ave Maria is high-risk trojan designed to steal various information and to cause "chain infections" (spread other infections). It is typically proliferated using various spam email campaigns.
Criminals send thousands of deceptive emails that contain infectious attachments, most of which are Microsoft Office (typically Excel) files. Emails are delivered with messages encouraging users to open the attached document, however, this results in infiltration of Ave Maria.
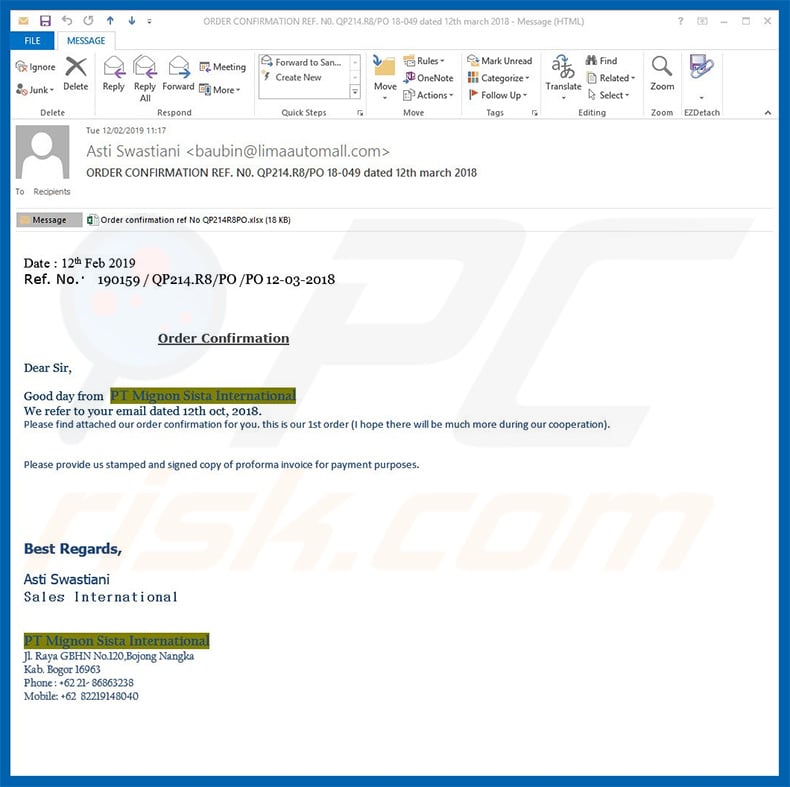
More about emails distributing Ave Maria
One of the emails we examined was an order confirmation, which contained an "invoice" attached. The message essentially states that information regarding a type of order is provided in the attached document and encourages users to review it. This, however, results in a malware infection.
This particular email was supposedly sent by an employee of the Mignon Sista International company, however, this is a deceptive tactic - cyber criminals often claim to be employees of popular companies or governmental agencies to give the impression of legitimacy, since users are much more likely to open attachments that are received from familiar names.
More about Ave Maria
Developers of this virus often target small companies/businesses, rather than regular users. Therefore, most recipients are employees/owners of various companies and businesses. This, however, does not mean that regular users are safe. The Ave Maria virus is designed to track information and record victims' keystrokes.
These infections are used to gather personal information, such as logins/passwords (of emails, social networks, etc.), credit card information, and so on. Having such information stolen is very risky. Cyber criminals aim to generate as much revenue as possible. Therefore, they are likely to misuse stolen accounts.
If they gain access to bank accounts, they can steal all funds by transfer to their accounts or via online purchases. Emails, social networks, and other accounts can be used to steal identities and perform various malicious actions (e.g., send malware to victims' contacts, ask contacts to lend money, and so on). Additionally, Ave Maria injects the system with additional malware.
At the time of research Ave Maria was used to proliferate another data-stealing trojan called LokiBot. However, the list of Ave Maria's features includes download and execution of files, which means that the situation might (and probably will) eventually change and crooks will use Ave Maria to spread some other malware.
Typically, trojans are used to proliferate ransomware and cryptominers. It is rather uncommon for trojans to spread viruses that have similar functionality (like in this case both Ave Maria and LokiBot are designed to steal data). Typically trojans spread infections that behave have different features.
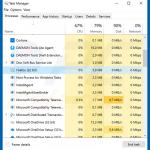
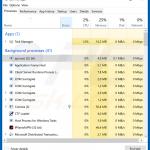
It is also worth mentioning that depending on Ave Maria's variant (executable) its process name is in Windows Task Manager is different. However, it is known that Ave Maria typically hides behind names of various genuine processes (e.g., "Firefox", "svchost.exe", etc.) in order to hide its presence.
What's interesting is that Ave Maria processes' icons are not genuine (e.g., "Firefox" process icon is some blurry square, rather than the original icon which is a fox winded around the globe). This allows to distinguish the fake processes.
Moreover, this malware is designed to alter Windows Defender's settings and prevent it from scanning the entire disk that Windows are installed in (typically its C:\ disk). That's because Ave Maria's files are hidden in Windows directory (there are few duplicates, one of them is hidden in "%APPDATA%" folder) and adds a Windows registry entry.
You can see the full list of Ave Maria's features below. In summary, having this virus on your computer can lead to various privacy issues, financial losses, and high-risk computer infections. As mentioned above, Ave Maria's process can be found in Windows Task Manager under random name.
If you find any dubious processes running, and suspect Ave Maria's presence, immediately scan your computer with a reputable anti-virus/anti-spyware suite and eliminate all detected threats.
| Name | Ave Maria malware |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Detection Names (chthonic.exe) | Avast (Win32:PWSX-gen [Trj]), BitDefender (Trojan.Agent.DSVM), ESET-NOD32 (a variant of Win32/Kryptik.GRNX), Kaspersky (Trojan-Spy.Win32.AveMaria.hl), Full List (VirusTotal) |
| Related IP Addresses | 91.192.100.61:2580 (Command & Control [C&C] server), 89.46.223.202 (Ave Maria download URL) |
| Related Domains | maxibrainz[.]warzonedns[.]com:2580 (Command & Control [C&C] server), secured[.]icbegypt[.]com (Ave Maria download URL) |
| Malicious Process Name(s) | apo.exe, Firefox, scvhost.exe - it disguises as a genuine Windows process svchost.exe (notice that second and third characters are swapped). The process name depends on Ave Maria's variant (executable). |
| Payload | LokiBot trojan. |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similarities with other trojan-type malware
Ave Maria shares many similarities with a number of other trojan-type viruses, such as TrickBot, Adwind, FormBook, and Qakbot.
Although these viruses are developed by different cyber criminals, all have the same purpose: to steal personal data. In addition, as with Ave Maria, these viruses are often distributed using spam email campaigns. They pose a significant threat to users' privacy and financial safety. Therefore, eliminating malware such as Ave Maria is paramount.
How did Ave Maria infiltrate my computer?
As mentioned above, Ave Maria is distributed using spam email campaigns that contain malicious MS Office documents attached. In most cases, the attachment format is Excel, which exploits an MS Office vulnerability (code-name CVE-2017-11882) to inject Ave Maria into the system.
This is a common method to proliferate trojans such as Ave Maria, however, the attachment is not always an MS Office document - the file type might be different (e.g., PDF, JavaScript, .exe, archive, or other).
In any case, user interaction is necessary for the malware to infiltrate the system. The user must manually run/open the attachment, otherwise the virus cannot enter the system.
How to avoid installation of malware?
To prevent this situation, be very cautious when browsing the internet. Think twice before opening email attachments. If the sender seems suspicious/unrecognizable or the attached link/file is irrelevant, do not open anything.
Bear in mind that criminals often try to abuse the recipient's curiosity by sending fraudulent messages, such as "you have received a package", "you have won a lottery", and so on. Unfortunately many users fall for these scams, hoping that they have gained something free of charge. Therefore, you should never trust such messages.
Have a reputable anti-virus/anti-spyware suite installed and running, since these programs commonly detect and eliminate malware before any damage is done. Lack of knowledge and careless behavior are the main reasons for computer infections. The key to safety is caution.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
List of Ave Maria trojan's features:
- Camera Exfiltration
- Cleanup
- Code Injection
- Download and Execution
- File Management: creation, download, exfiltration, deletion
- Info-stealer support:
Firefox
Foxmail
Google Chrome
Internet Explorer
Outlook
Thunderbird - Offline Keylogger
- Persistence
- Privilege Escalation, support from Windows 7 to Windows 10
- Processes Management: enumeration, termination
- RDP using rdpwrap
Examples of rogue processes ("apo.exe" and "Firefox") of Ave Maria in Windows Task Manager:
Examples of a malicious MS Word documents designed to inject Ave Maria trojan:
Another example of a spam email used to spread Ave Maria trojan (the attachment is a .r00 archive containing a malicious executable):
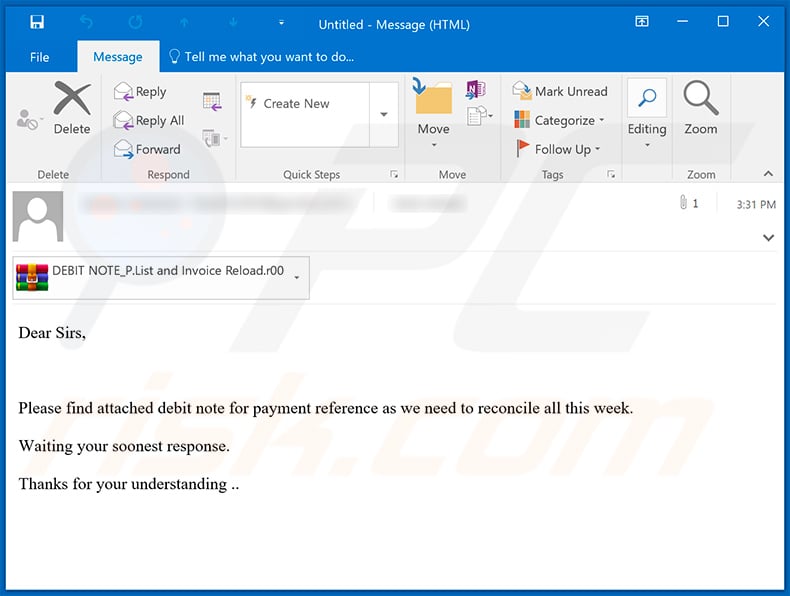
Text presented within:
Dear Sirs,
Please find attached debit note for payment reference as we need to reconcile all this week.
Waiting your soonest response.
Thanks for your understanding ..
Update September 7, 2020 - New spam campaigns proliferating the Ave Maria trojan have been detected. The scam emails (titles/subjects "Re: Consignment Notification: You have A Package With Us", "TNT ARRIVAL NOTIFICATION REPORT / INVOICE & BILL"; may vary) distributed though these campaigns are disguised as package delivery notifications from legitimate courier companies (e.g. DHL, TNT Express, etc.).
The infection chain is initiated when recipients open decoy images of fake invoices, which contain embedded URLs. Once the images are clicked on, virulent files are downloaded and automatically executed. The infectious files are hosted on Discord - instant messaging and VoIP application.
Should the Discord app be installed and/or open on the targeted device - spam filters and endpoint protection systems might be unable to detect that the URLs are malicious and simply allow all links from Discord.
Example of yet another spam email used to spread Ave Maria trojan (the attachment is a .7z archive containing a malicious executable):
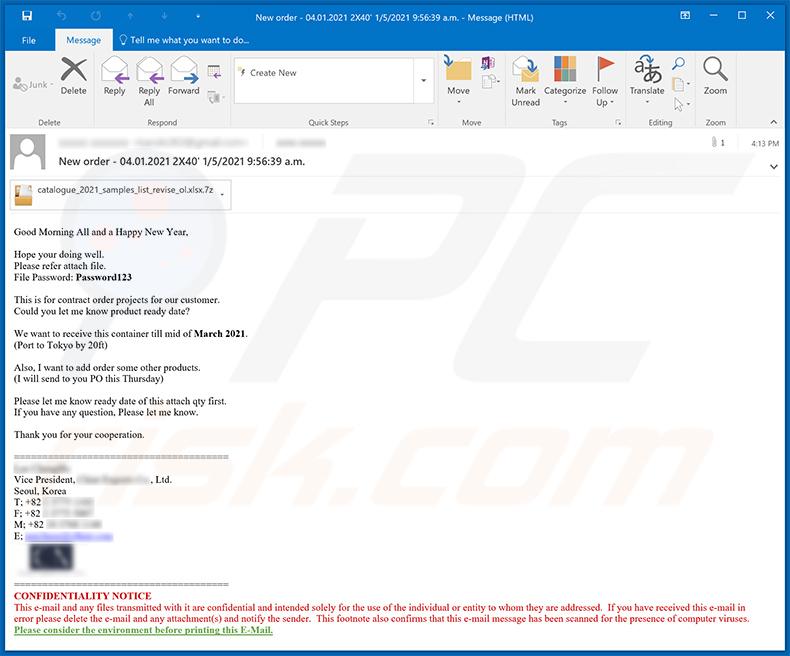
Text presented within:
Subject: New order - 04.01.2021 2X40' 1/5/2021 9:56:39 a.m.
Good Morning All and a Happy New Year,
Hope your doing well.
Please refer attach file.
File Password: Password123
This is for contract order projects for our customer.
Could you let me know product ready date?We want to receive this container till mid of March 2021.
(Port to Tokyo by 20ft)
Also, I want to add order some other products.
(I will send to you PO this Thursday)
Please let me know ready date of this attach qty first.
If you have any question, Please let me know.
Thank you for your cooperation.
======================================
- -
Vice President, - Co., Ltd.
Seoul, Korea
T; +82 -
F; +82 -
M; +82 -
E; -======================================
CONFIDENTIALITY NOTICE
This e-mail and any files transmitted with it are confidential and intended solely for the use of the individual or entity to whom they are addressed. If you have received this e-mail in error please delete the e-mail and any attachment(s) and notify the sender. This footnote also confirms that this e-mail message has been scanned for the presence of computer viruses.
Please consider the environment before printing this E-Mail.
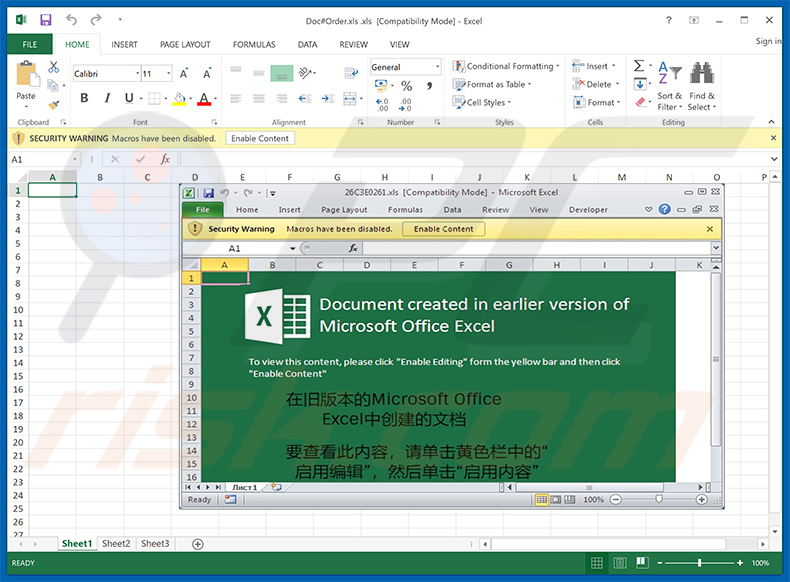
An example of a malicious MS Excel document (distributed via spam emails) designed to inject Ave Maria trojan into the system:
Another example of a spam email spreading Ave Maria trojan:
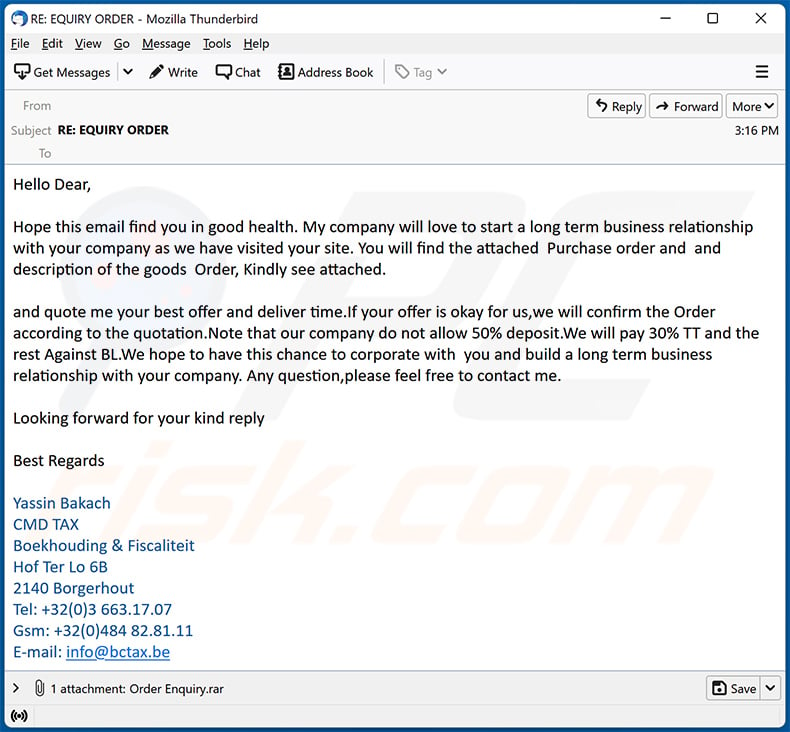
Text presented within:
Subject: RE: EQUIRY ORDER
Hello Dear,
Hope this email find you in good health. My company will love to start a long term business relationship with your company as we have visited your site. You will find the attached Purchase order and and description of the goods Order, Kindly see attached.
and quote me your best offer and deliver time.If your offer is okay for us,we will confirm the Order according to the quotation.Note that our company do not allow 50% deposit.We will pay 30% TT and the rest Against BL.We hope to have this chance to corporate with you and build a long term business relationship with your company. Any question,please feel free to contact me.
Looking forward for your kind reply
Best Regards
Yassin Bakach
CMD TAX
Boekhouding & Fiscaliteit
Hof Ter Lo 6B
2140 Borgerhout
Tel: +32(0)3 663.17.07
Gsm: +32(0)484 82.81.11
E-mail: info@bctax.be
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Ave Maria?
- STEP 1. Manual removal of Ave Maria malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Ave Maria malware, should I format my storage device to get rid of it?
No, there is no need to perform this procedure. Malware like Ave Maria can be removed without formatting the storage device.
What are the biggest issues that malware can cause?
It depends on the capabilities of the malware. Usually, cybercriminals use it to steal money, personal accounts, identities, distribute other malware, mine cryptocurrency, or encrypt files.
What is the purpose of Ave Maria malware?
Ave Maria collects sensitive information (like credit card details, login credentials, etc.). It also can infect a computer with additional malware. We found that threat actors have used Ave Maria to distribute LokiBot.
How did a malware infiltrate my computer?
It is known that Ave Maria malware is distributed via email. Threat actors send emails containing malicious attachments designed to infect computers with Ave Maria. Malicious MS Office documents infect computers after users enable macros commands (editing/content).
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and remove almost all known malware from the operating system. If a computer is infected with high-end malware, it is required to run a full system scan to remove that malware. High-end malware usually hides deep in the operating system. Thus, running a quick scan is not enough to detect and remove it.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate



▼ Show Discussion