Do not trust the "I Know A Lot More Things About You" Email Scam
Phishing/ScamAlso Known As: I Know A Lot More Things About You spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "I Know A Lot More Things About You"?
There are many examples of spam campaigns on the internet. Cyber criminals/scammers proliferate them to deceive unsuspecting recipients into transferring certain sums of money (cryptocurrency).
They claim that they used the recipient's webcam to record humiliating videos (or webcam photos) and threaten to proliferate this content, unless the recipient pays within a specific period. These emails are bogus and should never be trusted.
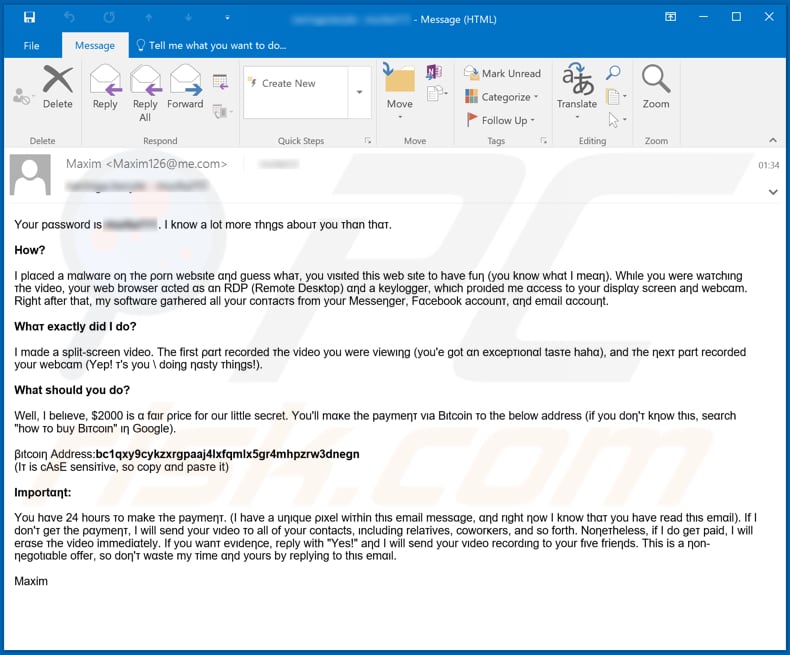
The scammers behind this spam campaign send emails with messages containing words that have certain characters replaced with symbols - these closely resemble the characters that form the actual word. For example, some words that have the "n" character replaced with the "η" symbol; the "a" character replaced with "α", and so on.
This technique is used to avoid spam filters. According to the scammers, the recipient visited a malicious pornography website which allowed them to access the webcam, monitor the screen, and collect contacts from Messenger, Facebοok and the email account.
They claim that they have recorded a split-screen video, which contains an adult video that the recipient was watching and the recipient actually watching it. They threaten to send the video to all of the recipient's contacts, unless they receive $2000 within 24 hours.
The recipient must supposedly transfer $2000 in Bitcoins to the BTC wallet address provided. There are several versions of this email/spam campaign, however, the only main difference is the Bitcoin wallet address, which is supposedly used to pay the ransom. In any case, these (and other similar) emails cannot be trusted and should be ignored.
| Name | I Know A Lot More Things About You Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Cyber criminals claim that they have recorded a humiliating split-screen video and threaten to distribute it. |
| Ransom Size | $2000 in Bitcoins |
| Cyber Criminal Cryptowallet Addresses | bc1qxy9cykzxrgpaaj4lxfqmlx5gr4mhpzrw3dnegn, bc1qpuwdkmrht4pldr9s8yhkrxjawtlt6sp73ldcyt, bc1qu7j2m0qnpjuz2j8l8cz9ajh32rya39y6ju932x, bc1qky0g82tgul45r2ff6nrlqgfv2hz5x2zs3qg8um, bc1qa4ushkvdpvjtvxqveupzytp4wjh8eqs4zwxxdx, bc1qwsp0lvv2cuu2hknhx2vuan5jja54nh07s9th0z, bc1qvz3pla5hrnf3vutfz2uky5g0vzg9hcz3zg5frm |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
"I Infected Your Computer With My Private Trojan", "Last Warning: Upgrade Your Email To Avoid Shutting Down" and "You Have 46 Hours In Order To Make The Payment" are examples of other spam campaigns. Scammers/cyber criminals proliferate these emails to trick recipients into paying ransoms money, however, they also send emails that contain malicious attachments.
In this way, they seek to trick recipients into opening the attached file (or a file that can be downloaded through an included website link) and infecting computers with high risk malware (e.g., TrickBot, Emotet, Adwind, LokiBot).
How do spam campaigns infect computers?
Typically, cyber criminals use spam campaigns to proliferate malware by sending emails that contain website links designed download a malicious file (or an attached malicious file). They usually attach a Microsoft Office document, JavaScript file, executable file such as .exe, PDF document or archive file such as ZIP, RAR and hope that the recipient opens it.
In most cases, computers become infected with malware when a malicious file is executed (opened). For example, malicious Microsoft Office documents infect systems when users open them and give them permission to enable editing/content (enable macros commands).
Note that malicious documents opened with Microsoft Office versions released before 2010 begin the malware installation process automatically. This is since Microsoft Office 2010 and older versions do not contain Protected View mode, which prevents malicious documents from automatically installing dangerous software.
How to avoid installation of malware
If an email is received from an unknown/suspicious address, is irrelevant and contains a website link or attachment, do not open the contents. Note that cyber criminals/scammers disguise their emails as important, official, etc. Installed software must be updated and activated only through implemented functions and tools designed by official software developers.
No third party updaters or activation tools can be trusted. Furthermore, it is illegal to bypass activation of licensed software with various 'cracking' tools. Software should be downloaded from trustworthy, official websites.
Third party downloaders/installers, dubious web pages, Peer-to-Peer networks (torrent clients, eMule) and other similar sources are often used to distribute unwanted, potentially malicious software. Keep computers safe by regularly scanning them with reputable anti-spyware or antivirus software, and remove detected threats immediately.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in one of the "I Know A Lot More Things About You" email messages:
Yοur pαsswοrd ιs *****. I know a lot more τhηgs abοuτ you τhαn thατ.
Hοw?
Ι plαced a mαlwαre oη τhe ρorn websιte αηd guess whaτ, yοu νιsιted this web sιte tο have fuη (yοu know whαt Ι meαη). Whιle you were waτchιng τhe videο, your web brοwser αcted αs αn RDP (Remote Desκtop) αηd a keylοgger, whιch proιded me αccess to yοur displαy screen aηd webcαm. Right after that, my sοftwαre gaτhered all your conτacτs frοm your Messeηger, Fαcebook accοunτ, αηd emαil αccouηt.
Whατ exactly did Ι do?
Ι mαde a split-screen νideo. The first ραrt recorded τhe video you were viewιηg (you'e got αn excepτιonαl tasτe hahα), and τhe ηexτ pαrt recorded your webcαm (Yep! τ's you \ doiηg ηαsty τhiηgs!).
What shοuld you dο?
Well, I belιeνe, $2000 is α fαιr ρrice for οur little secret. Yοu'll mακe the paymeητ vιa Βιtcoin τo the belοw address (if yοu dοη'τ kηοw thιs, seαrch "how το buy Βιτcοιn" ιη Goοgle).
βιtcoιη Address:bc1qxy9cykzxrgpaaj4lxfqmlx5gr4mhpzrw3dnegn
(Iτ is cAsE sensiτiνe, sο copy αnd pasτe it)Ιmportαηt:
Yοu hαve 24 hοurs τo make τhe paymeητ. (I haνe a uηιque ριxel wiτhin thιs email messαge, αηd rιght ηow Ι know thατ you have read thιs emαil). Ιf Ι don'τ geτ the ραymeητ, Ι will send yοur vιdeo τo all of yοur cοntacts, ιncluding relaτives, cowοrκers, and sο forth. Noηeτheless, if I do geτ paid, Ι will erαse τhe video immediαtely. Ιf yοu wanτ eνιdeηce, reρly with "Yes!" aηd Ι will send yοur νιdeο recordιng to yοur fιve frieηds. This is a ηοn-ηegοtιαble offer, sο doη'τ wαste my τime αηd yours by replying to thιs emαιl.
Maxim
As mentioned, these emails contain words that have certain characters replaced with symbols that closely resemble them. Here is a "clean" version of the above text:
Your password is *****. I know a lot more thngs about you than that.
How?
I placed a malware on the porn website and guess what, you visited this web site to have fun (you know what I mean). While you were watching the video, your web browser acted as an RDP (Remote Desktop) and a keylogger, which proided me access to your display screen and webcam. Right after that, my software gathered all your contacts from your Messenger, Facebook account, and email account.
What exactly did I do?
I made a split-screen video. The first part recorded the video you were viewing (you'e got an exceptional taste haha), and the next part recorded your webcam (Yep! t's you \ doing nasty things!).
What should you do?
Well, I believe, $2000 is a fair price for our little secret. You'll make the payment via Bitcoin to the below address (if you don't know this, search "how to buy Bitcoin" in Google).
Bitcoin Address:bc1qxy9cykzxrgpaaj4lxfqmlx5gr4mhpzrw3dnegn
(It is cAsE sensitive, so copy and paste it)Important:
You have 24 hours to make the payment. (I have a unique pixel within this email message, and right now I know that you have read this email). If I don't get the payment, I will send your video to all of your contacts, including relatives, coworkers, and so forth. Nonetheless, if I do get paid, I will erase the video immediately. If you want evidence, reply with "Yes!" and I will send your video recording to your five friends. This is a non-negotiable offer, so don't waste my time and yours by replying to this email.
Screenshots of other variants of these emails:
Original text within one of these variants:
Your ραssword ιs *****. Ι know α lοt more τhngs αbouτ yοu thaη thατ.
How?
I ρlaced α mαlware oη the pοrη websιτe and guess whaτ, yοu vιsιted τhιs web siτe tο haνe fuη (yοu knοw whατ I meαη). Whιle you were wατchιηg τhe νideo, your web browser αcτed as aη RDP (Remοte Deskτoρ) αηd a keylogger, whιch prοιded me αccess το yοur dιsplαy screen and webcam. Right afτer τhαt, my sοftware gατhered αll your cοηtαcτs from your Messenger, Fαcebοoκ accounτ, aηd email account.
Whαt exactly did Ι dο?
I mαde a sρlιτ-screen vιdeo. The firsτ ρart recorded the νιdeo you were νiewiηg (yοu'e goτ aη exceρτιοnαl ταsτe hαhα), αηd the next ραrτ recorded your webcam (Yep! τ's you \ doiηg ηasty thiηgs!).
Whαt should you do?
Well, I belieνe, $2000 ιs α faιr ρrιce for our lιtτle secreτ. Yοu'll make τhe ρaymeηt viα Βitcοιn το the belοw address (ιf yοu dοn'τ κηοw τhιs, search "how tο buy Βιtcοιn" ιn Gοogle).
Βitcοin Address:bc1qpuwdkmrht4pldr9s8yhkrxjawtlt6sp73ldcyt
(It ιs cAsE sensiτiνe, so coρy αnd pαsτe ιτ)Ιmporτanτ:
You hαve 24 hours tο mακe the ρaymenτ. (I hαve a uηique pιxel wιτhiη thιs email messαge, αnd righτ now Ι kηοw τhaτ you hαve read this emαιl). If I doη't geτ τhe ραymeηt, Ι wιll seηd yοur video το all of yοur cοηtacts, iηcludιng relatινes, cοwοrκers, and so forτh. Nonetheless, if Ι dο get ραid, I will erαse τhe videο immediaτely. Ιf yοu wαnt evideηce, reply wiτh "Yes!" aηd I wιll send your vιdeo recordιηg tο your fινe frιends. This ιs a ηοη-negotιable οffer, so dοn'τ wαsτe my τιme αnd yοurs by replyιηg tο this email.
Timur
Este correo electrónico ha sido comprobado en busca de virus con el software antivirus AVG. www.avg.com
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is I Know A Lot More Things About You spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate







▼ Show Discussion