Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Mekotio?
Mekotio is malicious software, categorized as a banking Trojan. This malware specifically targets banking information. The Mekotio Trojan poses a significant threat to victims' finances and privacy. This malicious program endangers device and user safety and, therefore, it is crucial to remove Mekotio infections immediately upon detection.
More about the Mekotio Trojan
Typically, banking Trojans target online banking account credentials such as IDs, log-ins, passwords, etc. Bank account numbers, credit card details and other sensitive information are also of interest. The only purpose of malware is to generate revenue for the cyber criminals using them.
Therefore, the stolen data is often misused to make fraudulent transactions and online purchases, and is sold to third parties or otherwise misused for financial gain. Therefore, Mekotio infections can lead to significant monetary loss, serious privacy issues and even identity theft. Some Trojans of this type target other information stored in or accessed through infected devices.
Compromising or particularly vulnerable content can be used by criminals for blackmail purposes. Other accounts, which do not directly deal with financial information, yet are commonly targeted, are emails, social networking and social media.
Through such accounts, cyber criminals can ask contacts/friends for loans and/or distribute malware by sharing infectious files, all under the guise of the genuine owner. If it is suspected or known that the Mekotio Trojan (or other malware) has already infected the system, use anti-virus software to eliminate it without delay.
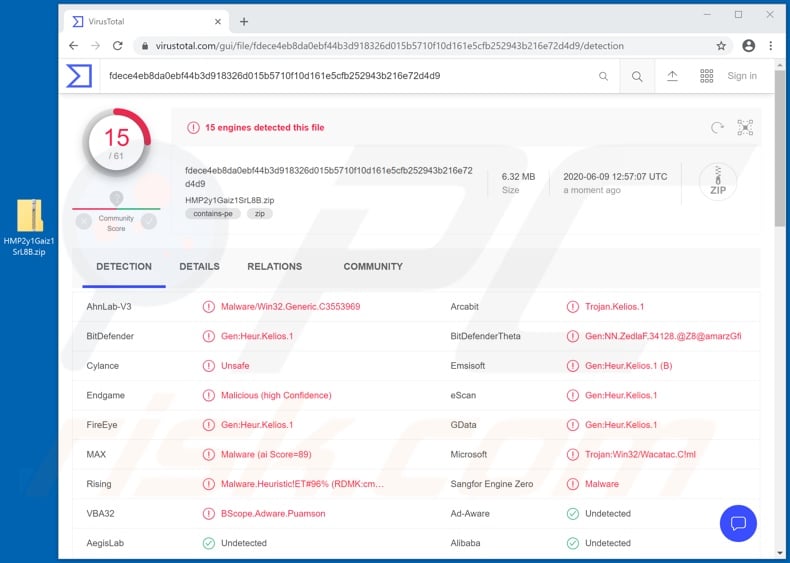
| Name | Mekotio malware |
| Threat Type | Trojan, password-stealing virus, banking malware, spyware. |
| Detection Names | BitDefender (Gen:Heur.Kelios.1), Emsisoft (Gen:Heur.Kelios.1 (B)), Endgame (Malicious (high Confidence)), Rising (Malware.Heuristic!ET#96%(RDMK:cmRtazpu5y1wRC6hqQswmBARcaZS)), Full List (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Trojans in general
Zeus Sphinx, Lucifer, Cinobi and Guildma are some examples of other banking malware, however, Trojans can have a wide variety of functionalities.
Some can enable remote access and control over the infected device, cause chain infections (i.e. download/install additional malware), exfiltrate and/or extract information, etc. Regardless of how these malicious programs operate, their purpose is identical: to generate profit for the cyber criminals behind them.
How did Mekotio infiltrate my computer?
Mekotio malware has been observed being distributed via Coronavirus/COVID-19-themed spam campaigns. The term "spam campaign" defines a large scale operation, during which thousands of deceptive/scam emails are sent.
The Mekotio-spreading messages are in Spanish and presented as judicial notifications from "Ministerio de Sanidad, Consumo y Bienestar Social" (Spain's Ministry of Health), concerning a complaint. The emails state that several complaints regarding the recipient have been received, due to alleged violations of current regulations, which were issued due to the ongoing pandemic.
Therefore, the recipients may be fined up to one hundred euros for ignoring to wear mandatory face-masks. These messages contain malicious links, which when clicked, initiate the infection chain of Mekotio. In general, spam campaigns infect systems through dangerous files distributed during these operations.
The emails can contain links to malicious websites that host such content or download links to the files. Alternatively, the files can be attached to the messages. Malicious files can be in various formats (e.g. archives, executables, PDF and Microsoft Office documents, JavaScript, etc.) and when they are executed, run or otherwise opened, download/installation of malware begins.
This malicious software is also proliferated via illegal activation tools ("cracks"), bogus updates and untrusted download channels. Rather than activating licensed products, "cracking" tools often download/install malware.
Fake updaters cause infections by abusing flaws of outdated products and/or simply by installing malicious programs rather than the promised updates. Malware is often downloaded inadvertently from dubious sources such as unofficial and free file-hosting websites, Peer-to-Peer sharing networks and other third party downloaders.
How to avoid installation of malware
Do not open suspicious and/or irrelevant emails, especially those with any links or attachments found in them, as this can lead to high-risk infection. All downloads must be done from official and verified sources. It is also important to activate and update products with tools/functions provided by legitimate developers.
Illegal activation ("cracking") tools and third party updaters must not be used, as they are often employed to proliferate malware. To protect device and user safety, it is crucial to have a reputable anti-virus/anti-spyware installed and kept updated. Use this software for regular system scans and removal of detected/potential threats.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Screenshot of the deceptive email distributing Mekotio Trojan:
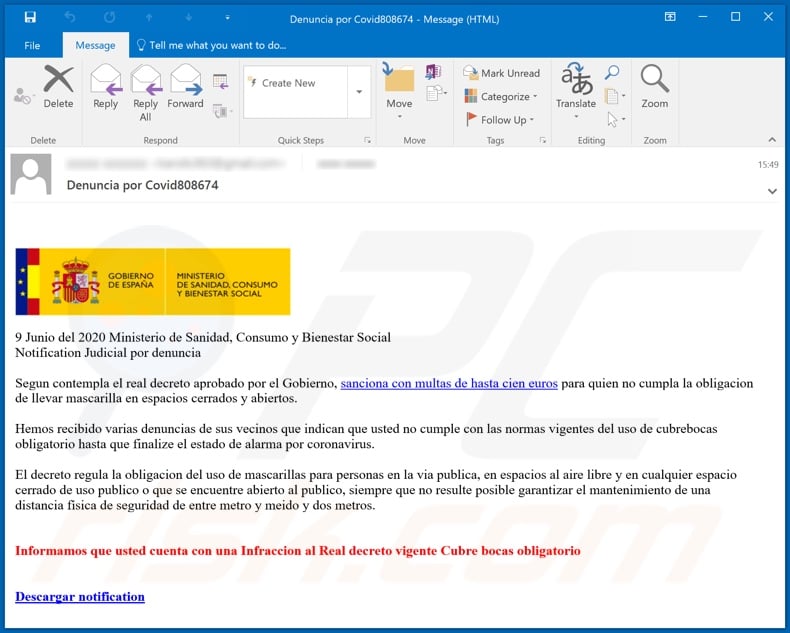
Text presented in this email message:
Subject: Denuncia por Covid808674
9 Junio del 2020 Ministerio de Sanidad, Consumo y Bienestar Social
Notification Judicial por denuncia
Segun contempla el real decreto aprobado por el Gobierno, sanciona con multas de hasta cien euros para quien no cumpla la obligacion de llevar mascarilla en espacios cerrados y abiertos.
Hemos recibido varias denuncias de sus vecinos que indican que usted no cumple con las normas vigentes del uso de cubrebocas obligatorio hasta que finalize el estado de alarma por coronavirus.
El decreto regula la obligacion del uso de mascarillas para personas en la via publica, en espacios al aire libre y en cualquier espacio cerrado de uso publico o que se encuentre abierto al publico, siempre que no resulte posible garantizar el mantenimiento de una distancia física de seguridad de entre metro y meido y dos metros.
Informamos que usted cuenta con una Infraccion al Real decreto vigente Cubre bocas obligatorio
Descargar notification
Appearance of another spam email used to spread the Mekotio Trojan:
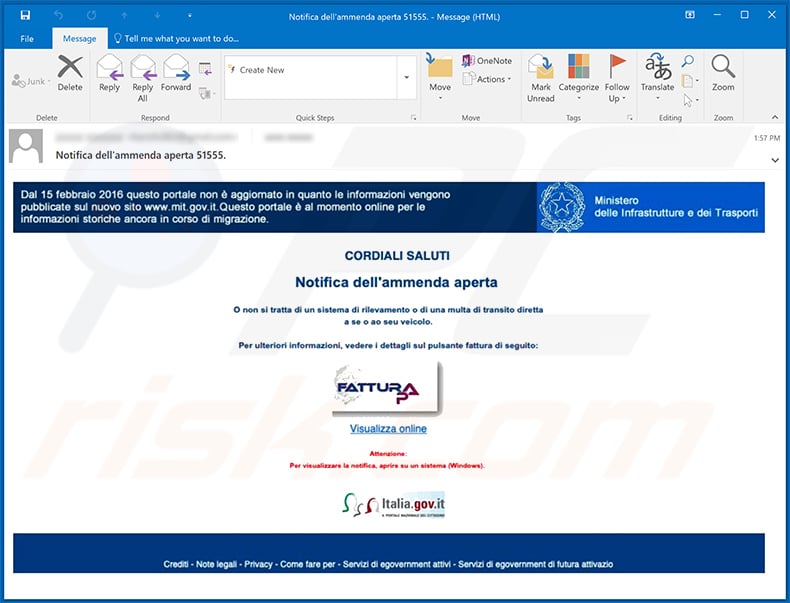
Text presented within:
Subject: Notifica dell'ammenda aperta 51555.
Dal 15 febbraio 2016 questo portale non è aggiornato in quanto le informazioni vengono pubblicate sul nuovo sito www.mit.gov.it.Questo portale è al momento online per le informazioni storiche ancora in corso di migrazione.
Ministero delle Infrastrutture e dei Trasporti
CORDIALI SALUTI
Notifica dell'ammenda apertaO non si tratta di un sistema di rilevamento o di una multa di transito diretta a se o ao seu veicolo.
Per ulteriori informazioni, vedere i dettagli sul pulsante fattura di segulto
FATTURA P
Visualizza online
Attenzione
Per visualizzare le notifica, aprire su un sistema (Windows).
Italia.gov.it
Update 24 August 2020 - Research shows that there are multiple variants of Mekotio that are being developed simultaneously. Some variants have backdoor capabilities, and can be used to steal Bitcoins by replacing the Bitcoin wallet address in the clipboard with another used by cyber criminals.
Some variants can gather information such as firewall configuration, operating system information, and list of installed antivirus solutions. They can also take screenshots, simulate mouse and keyboard actions, restart the computer, update themselves, steal passwords saved on Chrome browsers, and restrict access to various banking-related web pages.
Another example of a spam email used to spread Mekotio trojan:
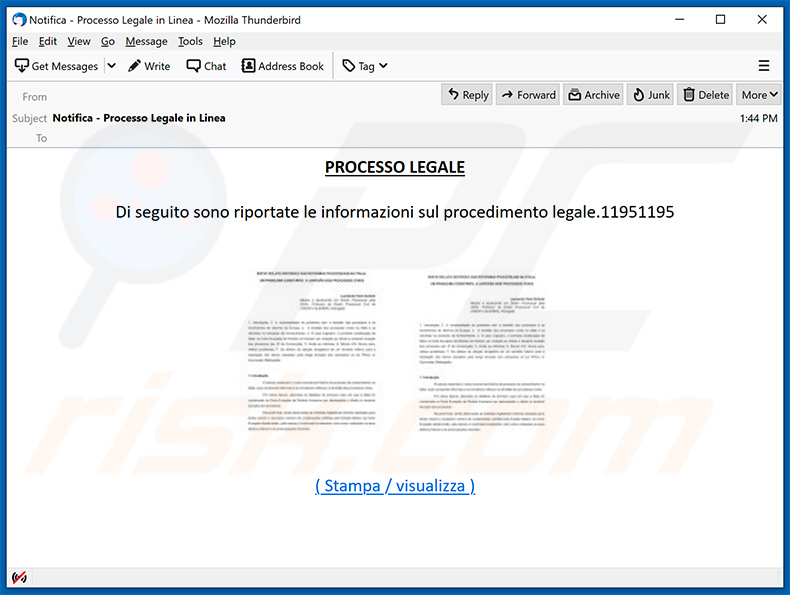
Text presented within:
Subject: Notifica - Processo Legale in Linea
PROCESSO LEGALE
Di seguito sono riportate le informazioni sul procedimento legale.11951195
( Stampa / visualizza )
Yet another example of a spam email spreading Mekotio trojan:
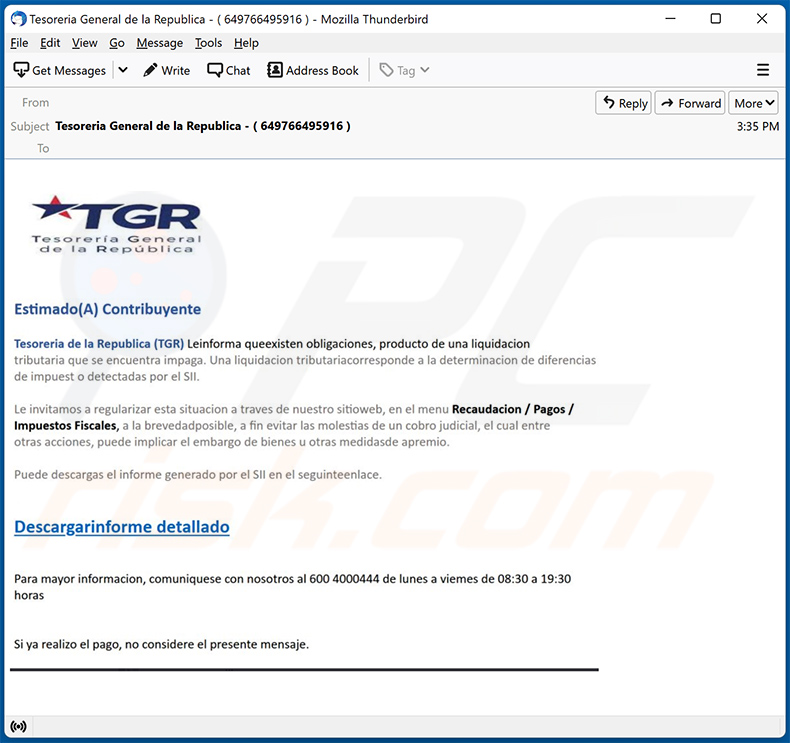
Text presented within:
Subject: Tesoreria General de la Republica - ( 649766495916 )
TGR
Tesorería General de la RepúblicaEstimado(A) Contribuyente
Tesoreria de la Republica (TGR) Leinforma queenxisten obligaciones, producto de una liquidacion tributaria que se encuentra impaga. Una liquidacion tributariacorresponde a la determinacion de diferencias de impuest o detectadas por el SII.
Le invitamos a regularizar esta situacion a traves de nuestro sitioweb, en el menu Recaudacion / Pagos / Impuestos Fiscales, a la brevedadposible, a fin evitar las molestias de un combro judicial, el cual entre otras acciones, puede implicar el embargo de bienes u otras medidasde apremio.
Puede descargas el informe generado por el SII en el seguinteenlace.
Descargarinforme detallado
Para mayor informacion, comuniquese con nosotros al 600 4000444 de lunes a viemes de 08:30 a 19:30 horas
Si ya realizo el pago, no considere el presente mensaje.
Yet another spam email spreading Mekotio trojan:
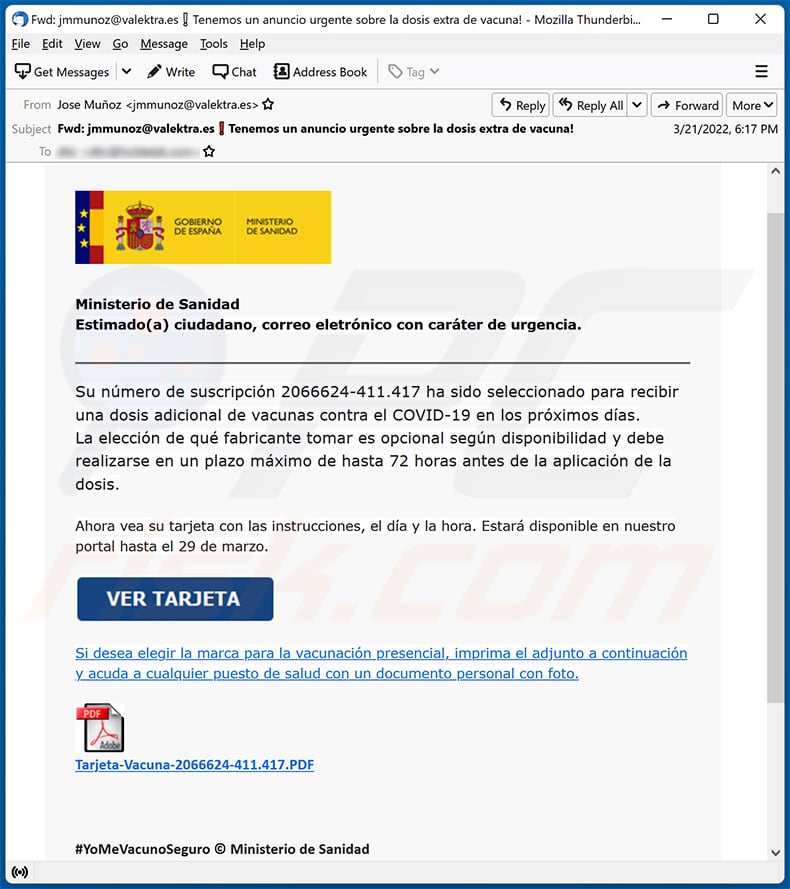
Text presented within:
Subject: Tenemos un anuncio urgente sobre la dosis extra de vacuna!
Ministerio de Sanidad
Estimado(a) ciudadano, correo eletrónico con caráter de urgencia.
Su número de suscripción 2066624-411.417 ha sido seleccionado para recibir una dosis adicional de vacunas contra el COVID-19 en los próximos días.
La elección de qué fabricante tomar es opcional según disponibilidad y debe realizarse en un plazo máximo de hasta 72 horas antes de la aplicación de la dosis.Ahora vea su tarjeta con las instrucciones, el día y la hora. Estará disponible en nuestro portal hasta el 29 de marzo.
Si desea elegir la marca para la vacunación presencial, imprima el adjunto a continuación y acuda a cualquier puesto de salud con un documento personal con foto.
Tarjeta-Vacuna-2066624-411.417.#YoMeVacunoSeguro © Ministerio de Sanidad
LATAM Airlines-themed spam email spreading Mekotion trojan:
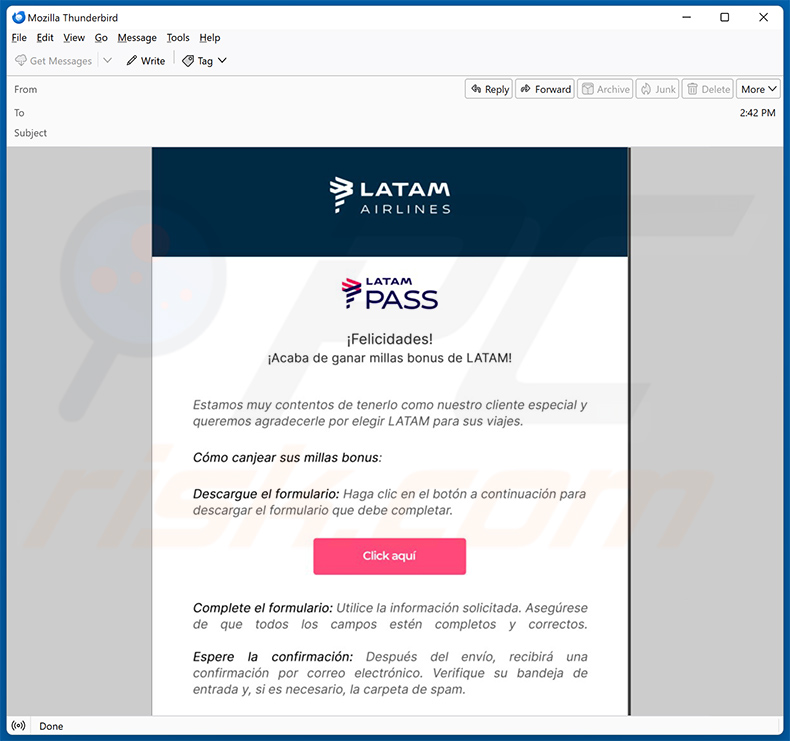
Text presented within:
LATAM Airlines
LATAM PASS
¡Felicidades!
¡Acaba de ganar millas bonus de LATAM!Estamos muy contentos de tenerlo como nuestro cliente especial y queremos agradecerle por elegir LATAM para sus viajes.
Cómo canjear sus millas bonus:
Descargue el formulario: Haga clic en el botón a continuación para descargar el formulario que debe completar.
[Click aquí]
Complete el formulario: Utilice la información solicitada. Asegúrese de que todos los campos estén completos y correctos.
Espere la confirmación: Después del envío, recibirá una confirmación por correo electrónico. Verifique su bandeja de entrada y, si es necesario, la carpeta de spam.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Mekotio?
- STEP 1. Manual removal of Mekotio malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Mekotio malware, should I format my storage device to get rid of it?
This piece of malware can be removed by following the steps provided in the removal guide above. It is not necessary to format the storage device to eliminate Mekotio.
What are the biggest issues that malware can cause?
It depends on the type of malware. The presence of malware can lead to identity theft, financial losses, decreased computer performance, hijacked personal accounts, data encryption, etc.
What is the purpose of a malware?
This malware targets banking information. It may be used to steal online banking account credentials such as usernames, IDs, passwords, etc.
How did a malware infiltrate my computer?
Computers become infected after malicious files are opened. In some cases, it is not enough to open a file to cause computer infections (for example, malicious documents require macro commands to be enabled). It is known that Mekotio is distributed via malicious email attachments. Cybercriminals also use cracked software download pages and other unreliable sources for downloading software/files, fake updaters, and similar methods to trick users into executing malware.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and eliminate almost all known malware infections. It is important to know that high-end malware can hide deep in the system. For this reason, computers infected with malware of this kind must be scanned fully (using a full scan option).
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion