Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Guildma Trojan?
Guildma is malicious software exclusively targeting Brazil and classified as a banking Trojan. While some variants of this malware have been updated to widen its range to other territories, no observations have been made of such attacks being carried out.
Furthermore, later versions had these capacities removed entirely. Guildma is the most sophisticated banking Trojan in the region of Brazil. In comparison with similar malicious programs targeting this country, Guildma uses the most advanced execution (i.e., infection) techniques.
With its various capabilities/features, this Trojan can cause especially serious issue and is, therefore, high-risk.
Guildma targets financial institutions of Brazil, however, its scope of potential targets is larger. It also attempts to exfiltrate (i.e., steal) data relating to emails, e-commerce (i.e., online stores) and streaming service accounts.
Unlike most banking Trojans operating in Brazil, Guildma has greater capacity to communicate with its C&C (Command and Control) server, which allows it more versatility in carrying out its malicious operations. Following successful infiltration, this malware checks whether it is running on a virtual machine or a "sandboxed" environment.
It also inspects the system's geolocation and other details. If the information is of no interest, Guildma terminates itself. If this data matches relevant criteria, the Trojan begins collecting system information (e.g. device name, installed software, etc.) and connects to the C&C server.
Guildma then begins monitoring pertinent activity such as when a banking website is opened. The malware can take screenshots and has keylogging capabilities as well. Therefore, it can record key strokes, which can be used to steal log-ins and passwords of various accounts.
Typically, Guildma monitors when a relevant web page is opened through Internet Explorer and forcefully logs the user out. It then gathers the log-in information when an attempt to access the account is made. Another particular area of interest for this Trojan are emails.
It can extort data from popular email clients and browsers. The malware collects email addresses and forms from sites. It can even collect email addresses and contact lists from desktop email clients (e.g. Microsoft Outlook, Thunderbird, The Bat!, etc.).
Other capabilities/features of the malicious program include emulating keyboard and mouse inputs, blocking shortcut keys (e.g. Alt + F4, which is used to closed the current activate window - by blocking this command, Guildma can prevent users from closing pop-ups that it displays, and so on).
It can also execute and exfiltrate (i.e., download) files, reboot the system, etc. In summary, Guildma can cause significant financial loss, serious privacy issues and lead to identity theft. If it is known or suspected that the Guildma banking Trojan (or other malware) has already infected the system, you are strongly advised to use anti-virus software to remove it immediately.
| Name | Guildma malware |
| Threat Type | Trojan, password-stealing virus, banking malware, spyware. |
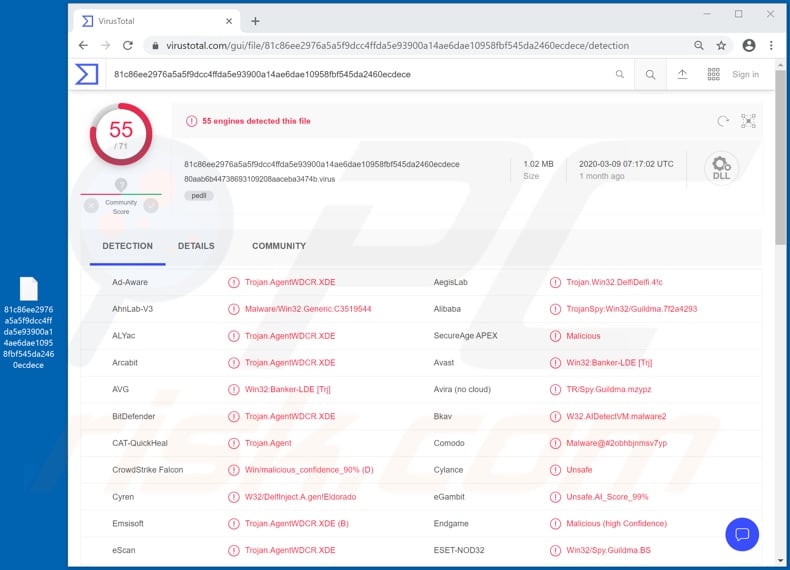
| Detection Names | Avast (Win32:Banker-LDE [Trj]), BitDefender (Trojan.AgentWDCR.XDE), ESET-NOD32 (Win32/Spy.Guildma.BS), Kaspersky (HEUR:Trojan.Win32.DelfiDelfi.gen), Full List (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Cinobi, Grandoreiro, Lampion, Mispadu and Bolik are some examples of other banking Trojans. Their functionalities differ, however, the purpose is identical: to generate revenue for the cyber criminals behind them. This malware endangers system integrity, affects its operation and can even cause data/system damage.
If such infections are not eliminated promptly, they can threaten user safety. Therefore, immediate removal is crucial.
How did Guildma infiltrate my computer?
Guildma has been observed being proliferated through spam campaigns. The term "spam campaign" defines a large scale operation, during which deceptive/scam emails are sent by the thousand.
The content of the messages used to distribute Guildma is varied, ranging from short messages intended to rouse user curiosity (e.g. requests for explanation of unspecified photographs) to fake invoices reminding users of approaching payment deadlines. Infections are caused via infectious files attached to (or linked inside) such emails.
Malicious files can be in various formats (e.g. archive and executable files, PDF and Microsoft Office documents, JavaScript, etc.). Once an infectious files is opened, the infection process is initiated (i.e., malware download/installation begins).
Other popular proliferation methods of malicious content include backdoor Trojans, illegal activation tools ("cracks"), bogus updates and untrusted download sources. Some Trojans can cause chain infections. "Cracking" tools can download/install malicious software rather than activating licensed products.
Fake updaters infect systems by exploiting weaknesses of outdated products and/or simply by installing malware rather than the promised updates.
Untrustworthy download channels (e.g. unofficial and free file-hosting websites, Peer-to-Peer sharing networks and other third party downloaders) can offer malicious programs for downloading, disguised as or bundled with normal products.
How to avoid installation of malware
Dubious and/or irrelevant emails should not be opened, especially those received from unknown/suspect senders. You are strongly advised against opening files or links present in suspicious mail, as this can lead to high-risk infection. Use only official and verified download sources.
It is also important to activate and update products with tools/functions provided by genuine developers. Illegal activation ("cracking") tools and third party updaters should not be used, as they are often employed to distribute malware. To ensure device and user safety, it is paramount to have a reputable anti-virus/anti-spyware suite installed.
It must be kept up to date, used to run regular system scans and to remove detected/potential threats. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Screenshots of malicious spam emails used to spread Guildma trojan (each contains a link leading to a malicious archive file containing Guildma malware executable);
Example 1:
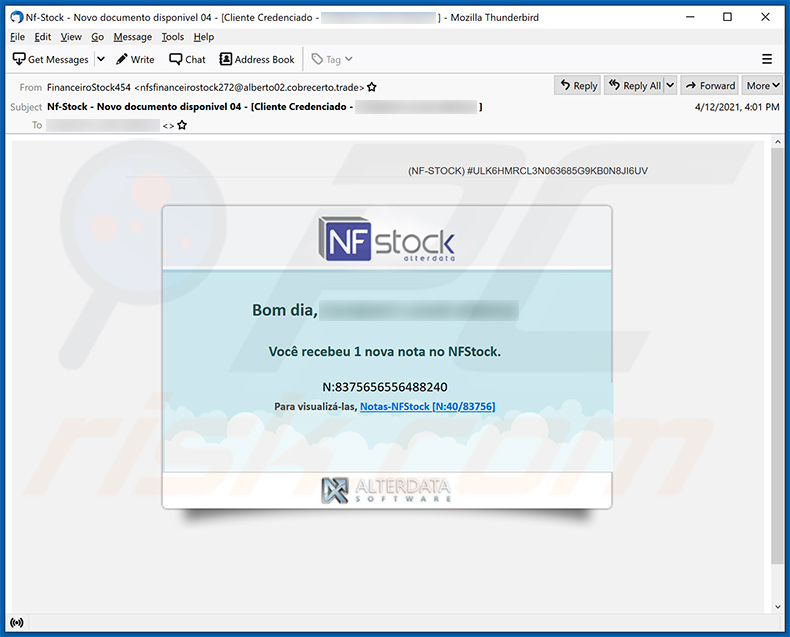
Text presented within:
Subject: Nf-Stock - Novo documento disponivel 04 - [Cliente Credenciado - ********]
(NF-Stock) #ULK6HMRCL3N063685G9KB0N8JI6UV
NF stock
alterdata
Bom dia, ********
Você recebeu 1 nova nota no NFStock.
N:8375656556488240
Para visualizá-las, Notas-NFStock [N:40/83756]
Example 2:
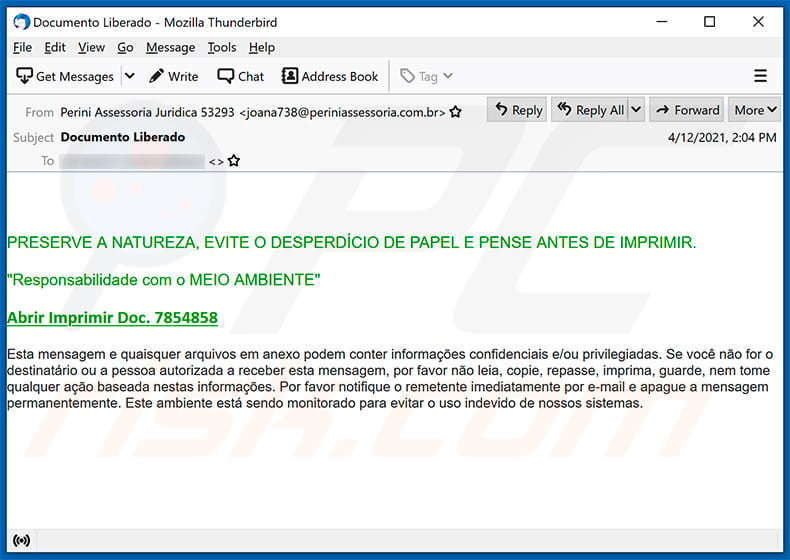
Text presented within:
Subject: Documento Liberado
PRESERVE A NATUREZA, EVITE O DESPERDÍCIO DE PAPEL E PENSE ANTES DE IMPRIMIR.
"Responsabilidade com o MEIO AMBIENTE"
Abrir Imprimir Doc. 7854858Esta mensagem e quaisquer arquivos em anexo podem conter informações confidenciais e/ou privilegiadas. Se você não for o destinatário ou a pessoa autorizada a receber esta mensagem, por favor não leia, copie, repasse, imprima, guarde, nem tome qualquer ação baseada nestas informações. Por favor notifique o remetente imediatamente por e-mail e apague a mensagem permanentemente. Este ambiente está sendo monitorado para evitar o uso indevido de nossos sistemas.
Example 3:
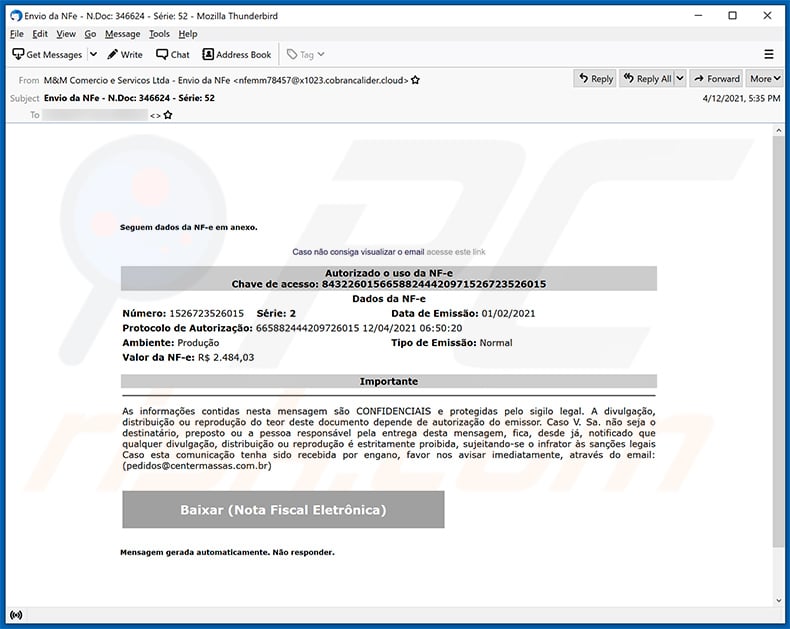
Text presented within:
Subject: Envio da NFe - N.Doc: 346624 - Série: 52
Seguem dados da NF-e em anexo.Caso não consiga visualizar o email acesse este link
Autorizado o uso da NF-e
Chave de acesso: 84322601566588244420971526723526015
Dados da NF-e
Número: 1526723526015 Série: 2 Data de Emissão: 01/02/2021
Protocolo de Autorização: 665882444209726015 12/04/2021 06:50:20
Ambiente: Produção Tipo de Emissão: Normal
Valor da NF-e: R$ 2.484,03Importante
As informações contidas nesta mensagem são CONFIDENCIAIS e protegidas pelo sigilo legal. A divulgação, distribuição ou reprodução do teor deste documento depende de autorização do emissor. Caso V. Sa. não seja o destinatário, preposto ou a pessoa responsável pela entrega desta mensagem, fica, desde já, notificado que qualquer divulgação, distribuição ou reprodução é estritamente proibida, sujeitando-se o infrator às sanções legais Caso esta comunicação tenha sido recebida por engano, favor nos avisar imediatamente, através do email: (pedidos@centermassas.com.br)
Baixar (Nota Fiscal Eletrônica)
Mensagem gerada automaticamente. Não responder.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Guildma?
- STEP 1. Manual removal of Guildma malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion